Localhost dangers CORS and DNS rebinding – Github.blog
Published on: 2025-04-02
Intelligence Report: Localhost dangers CORS and DNS rebinding – Github.blog
1. BLUF (Bottom Line Up Front)
The analysis identifies significant security vulnerabilities associated with CORS misconfigurations and DNS rebinding attacks. These vulnerabilities can lead to unauthorized access and data breaches, affecting both open-source software and commercial applications. Immediate attention is required to address these issues through improved security practices and awareness among developers.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
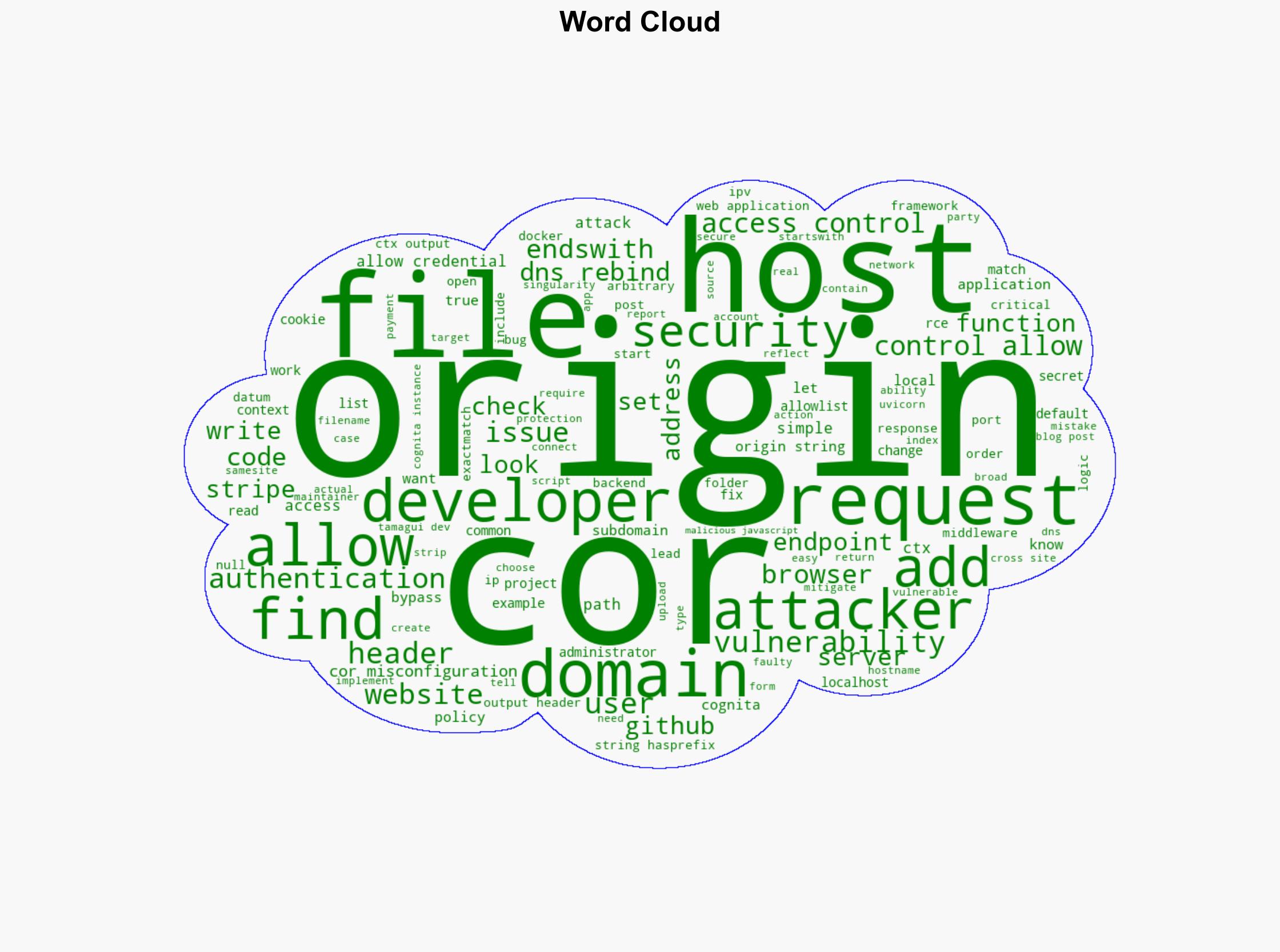
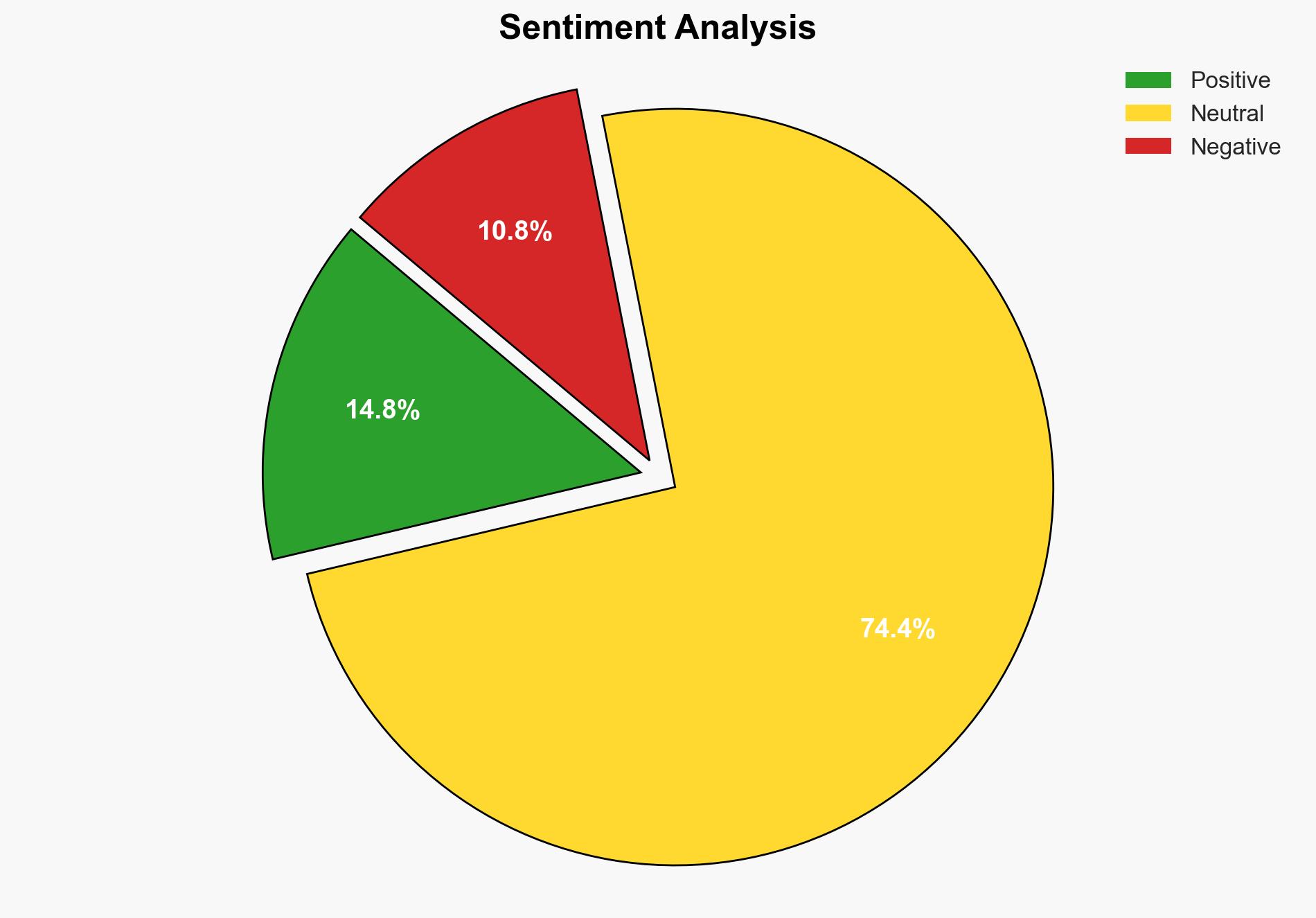
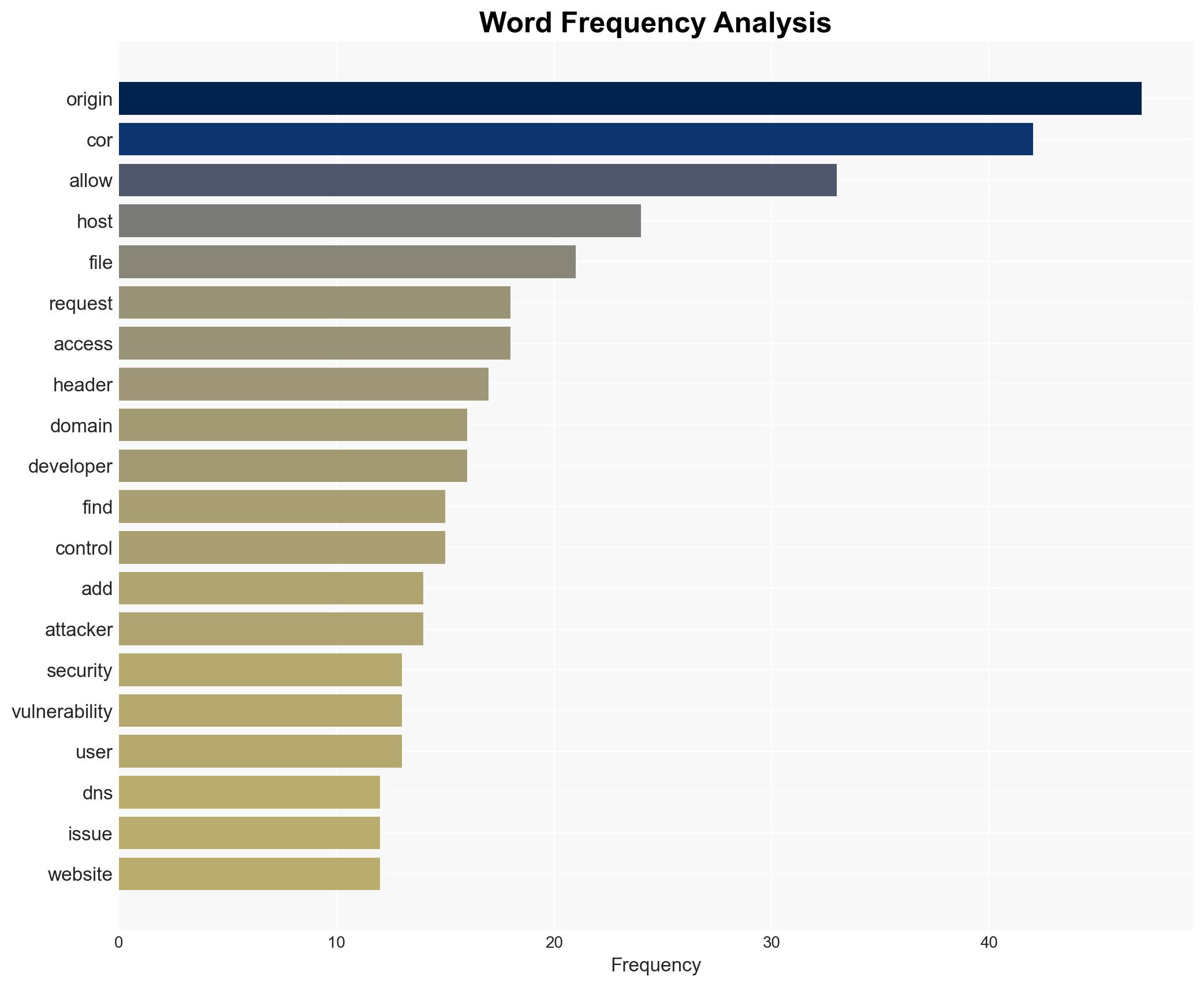
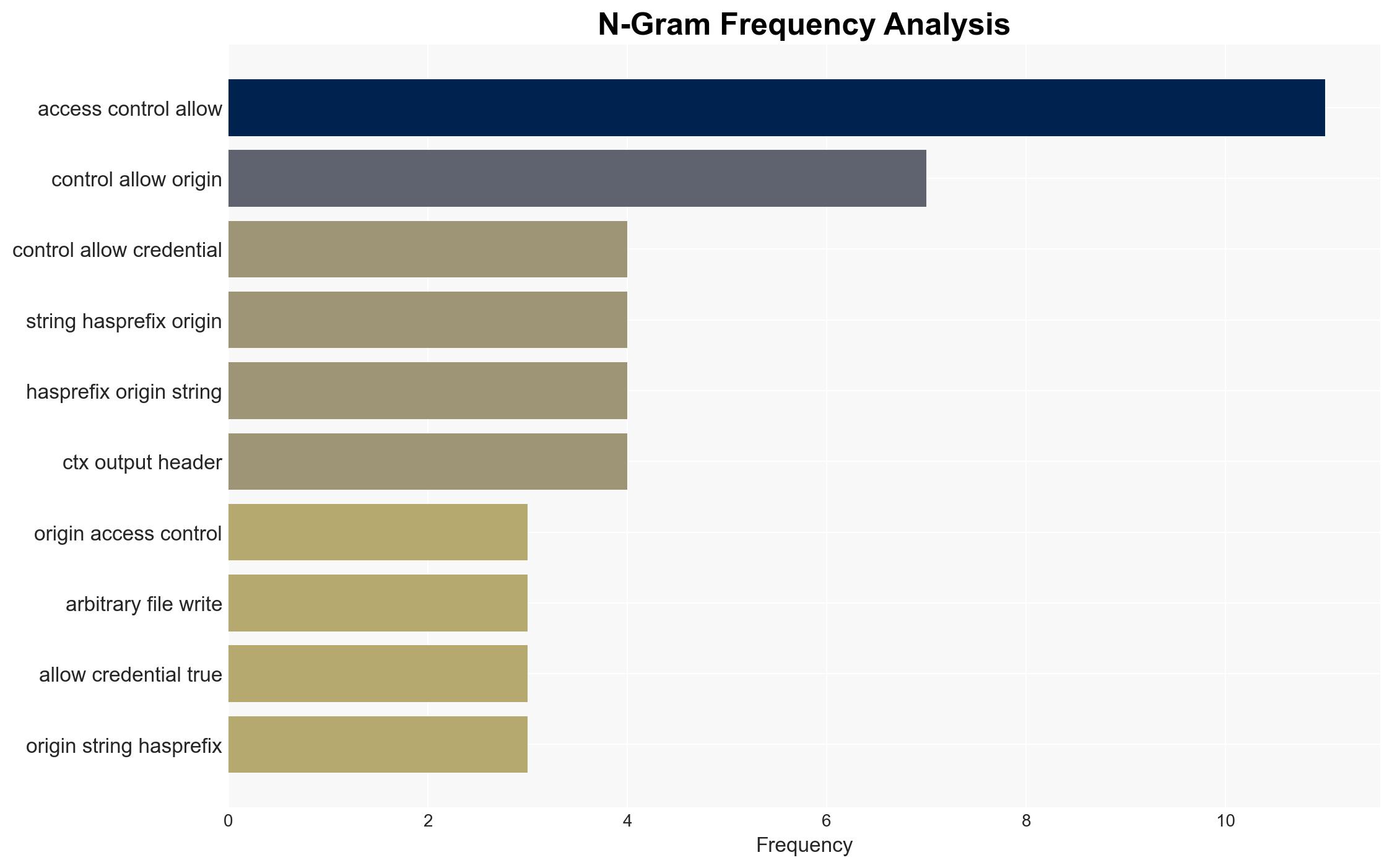
The report highlights common vulnerabilities related to Cross-Origin Resource Sharing (CORS) mechanisms. Misconfigurations often arise from developers not fully understanding the implications of altering origin policies. This can result in overly broad rules that expose applications to security threats. The analysis also covers DNS rebinding attacks, which exploit similar weaknesses to bypass origin policy restrictions, potentially leading to unauthorized data access.
Key issues include improper use of the Access-Control-Allow-Origin and Access-Control-Allow-Credentials headers, which are crucial for secure CORS implementation. Developers frequently make errors by setting these headers incorrectly, allowing malicious sites to exploit the vulnerabilities.
3. Implications and Strategic Risks
The security risks associated with CORS misconfigurations and DNS rebinding attacks have broad implications. They pose threats to national security by potentially allowing unauthorized access to sensitive data. Economically, these vulnerabilities can lead to significant financial losses for companies due to data breaches and loss of consumer trust. The widespread nature of these vulnerabilities also threatens regional stability by enabling cyber attacks that can disrupt critical infrastructure.
4. Recommendations and Outlook
Recommendations:
- Enhance developer training on CORS and DNS security to prevent misconfigurations.
- Implement stricter regulatory guidelines for secure CORS policy settings.
- Encourage the use of robust security frameworks and libraries that provide safe defaults.
- Promote regular security audits and vulnerability assessments for web applications.
Outlook:
In the best-case scenario, increased awareness and improved security practices will significantly reduce the prevalence of these vulnerabilities. The worst-case scenario involves continued exploitation of these weaknesses, leading to widespread data breaches and financial losses. The most likely outcome is a gradual improvement in security practices as awareness grows, but challenges will persist due to the complexity of securing web applications.
5. Key Individuals and Entities
The report does not mention specific individuals by name but emphasizes the role of developers and security professionals in addressing these vulnerabilities. Key entities include organizations responsible for web application development and cybersecurity.