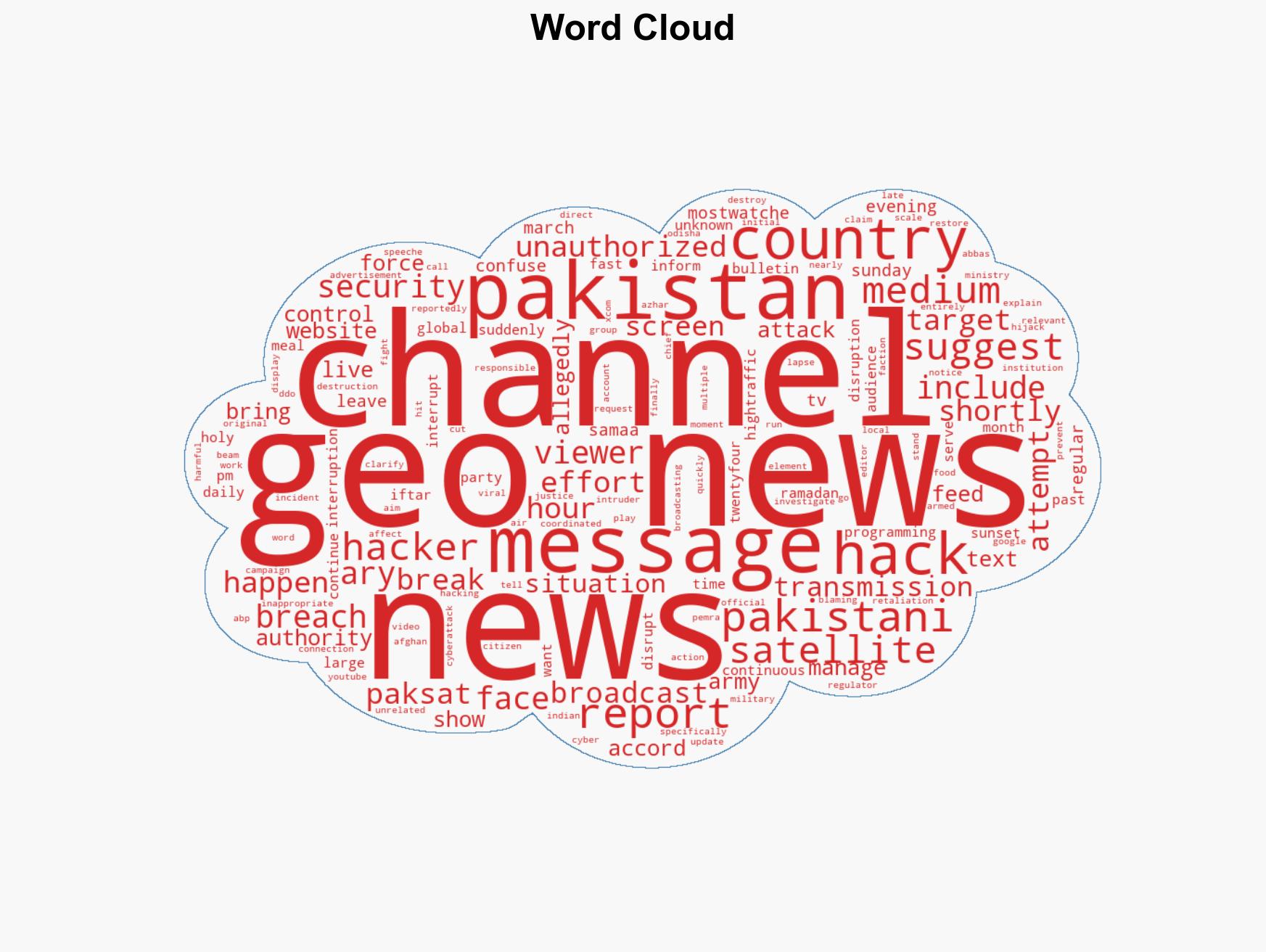
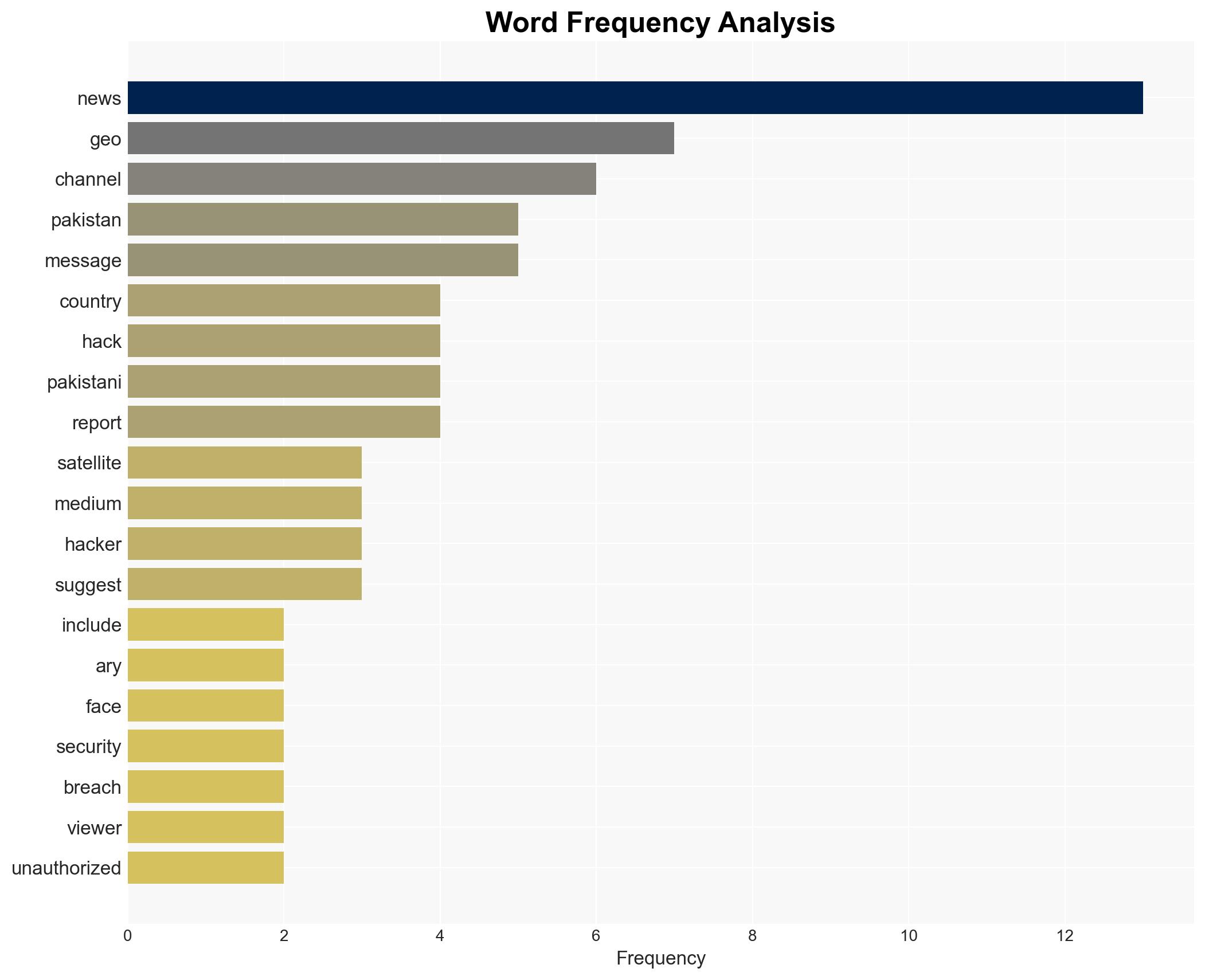
Major Pakistani News Networks Compromised by Hackers Broadcasting Anti-Military Content
Published on: 2026-03-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Pakistans Top News Channels Hacked and Hijacked With Anti-Military Messages
1. BLUF (Bottom Line Up Front)
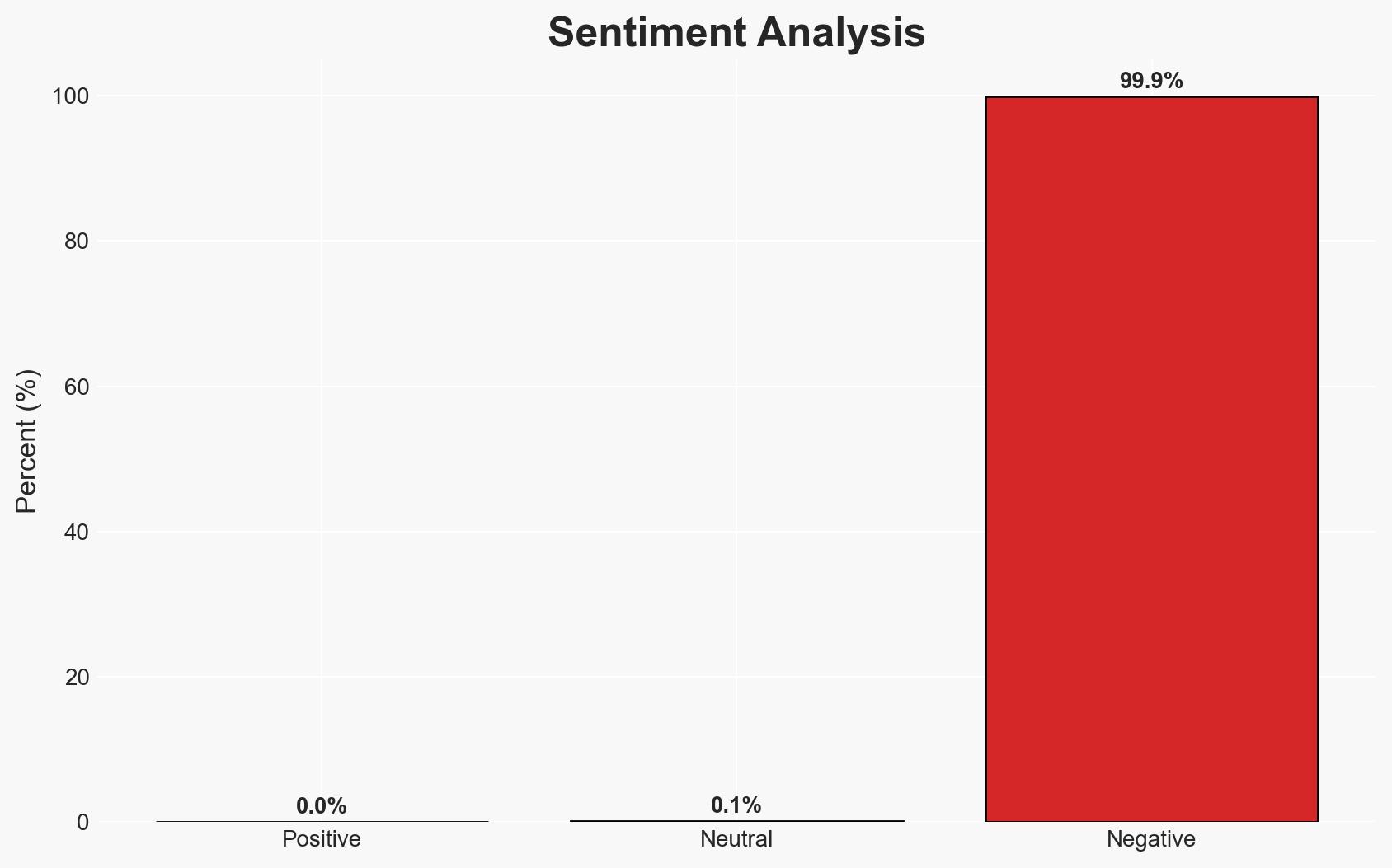
The hacking of Pakistan’s major news channels, displaying anti-military messages, suggests a coordinated cyber operation possibly aimed at destabilizing the country’s internal security and public trust in the military. The incident has triggered retaliatory cyberattacks by Pakistani entities. The most likely hypothesis is that a non-state actor, possibly with regional interests, orchestrated the attack. Overall confidence in this assessment is moderate due to limited attribution evidence.
2. Competing Hypotheses
- Hypothesis A: A non-state actor, potentially with regional interests, conducted the cyberattacks to destabilize Pakistan’s internal security and undermine the military’s public image. Supporting evidence includes the coordinated nature of the attack and the specific anti-military messaging. However, the lack of concrete attribution and official statements from Pakistani authorities introduces uncertainty.
- Hypothesis B: A state-sponsored actor, possibly from a neighboring country, orchestrated the attack to exploit existing tensions within Pakistan and provoke retaliatory actions. This is supported by the scale of the attack and subsequent retaliatory cyberattacks. Contradicting evidence includes the absence of direct claims of responsibility by any state actor.
- Assessment: Hypothesis A is currently better supported due to the absence of direct evidence linking a state actor and the nature of the messages, which align more with non-state actor motivations. Key indicators that could shift this judgment include credible attribution evidence or official statements from involved states.
3. Key Assumptions and Red Flags
- Assumptions: The attack was technically sophisticated, requiring significant resources; the messages were intended to incite public dissent against the military; retaliatory cyberattacks were conducted by Pakistani entities.
- Information Gaps: Definitive attribution of the attackers; the exact methods used to breach the satellite feeds; official responses from the Pakistani government and military.
- Bias & Deception Risks: Potential bias in media reporting due to nationalistic sentiments; risk of deception by the attackers to mislead attribution efforts.
4. Implications and Strategic Risks
This development could exacerbate internal tensions within Pakistan, leading to increased public distrust in the military and government. It may also trigger further cyber conflicts in the region.
- Political / Geopolitical: Potential escalation of regional cyber tensions, particularly between Pakistan and neighboring countries.
- Security / Counter-Terrorism: Increased risk of internal unrest and potential exploitation by extremist groups.
- Cyber / Information Space: Highlighted vulnerabilities in national cyber infrastructure and potential for further attacks.
- Economic / Social: Possible impacts on investor confidence and social cohesion due to perceived instability.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cyber activities targeting media outlets; engage in diplomatic channels to de-escalate potential regional tensions.
- Medium-Term Posture (1–12 months): Develop resilience measures for critical media infrastructure; strengthen regional cybersecurity partnerships.
- Scenario Outlook:
- Best: Strengthened cybersecurity leads to reduced vulnerability and improved regional cooperation.
- Worst: Escalation of cyber conflicts leads to broader geopolitical tensions.
- Most-Likely: Continued low-level cyber skirmishes with periodic escalations.
6. Key Individuals and Entities
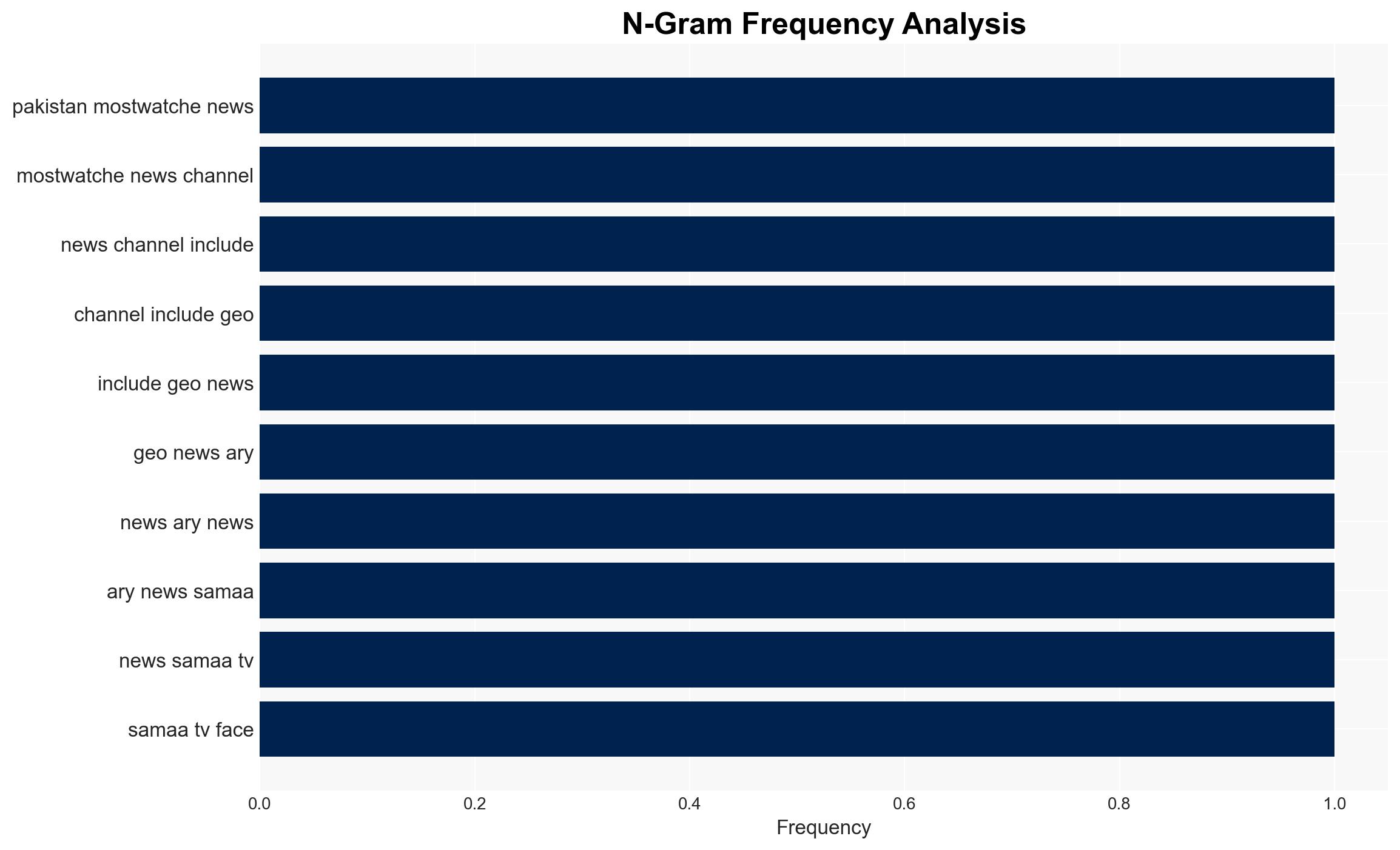
- Geo News, ARY News, Samaa TV, Pakistan Armed Forces, Pakistan Cyber Force, Ministry of Information and Broadcasting (Pakistan), PEMRA (Pakistan Electronic Media Regulatory Authority)
7. Thematic Tags
cybersecurity, media manipulation, regional tensions, information warfare, military relations, cyber retaliation, public trust
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us