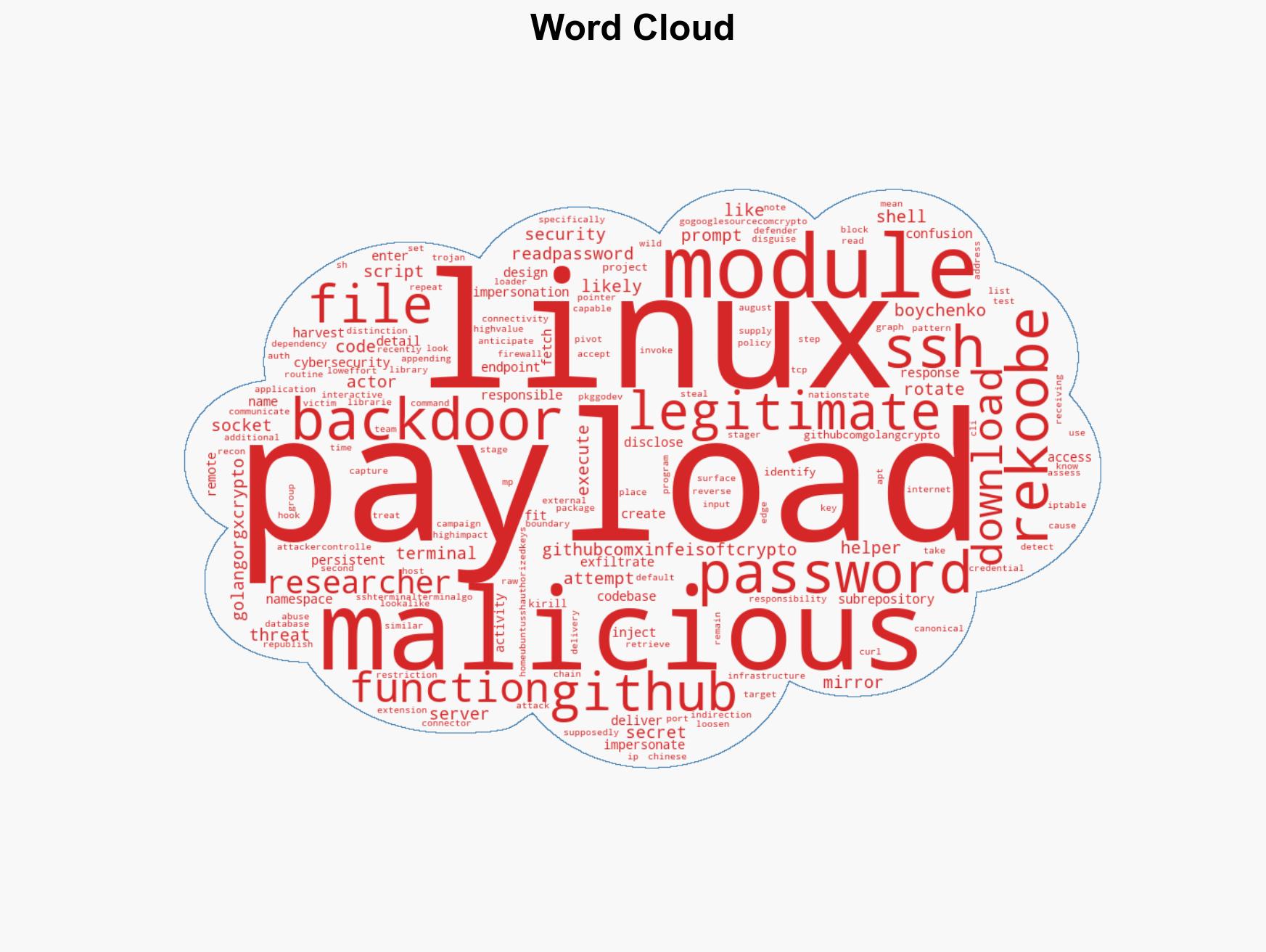
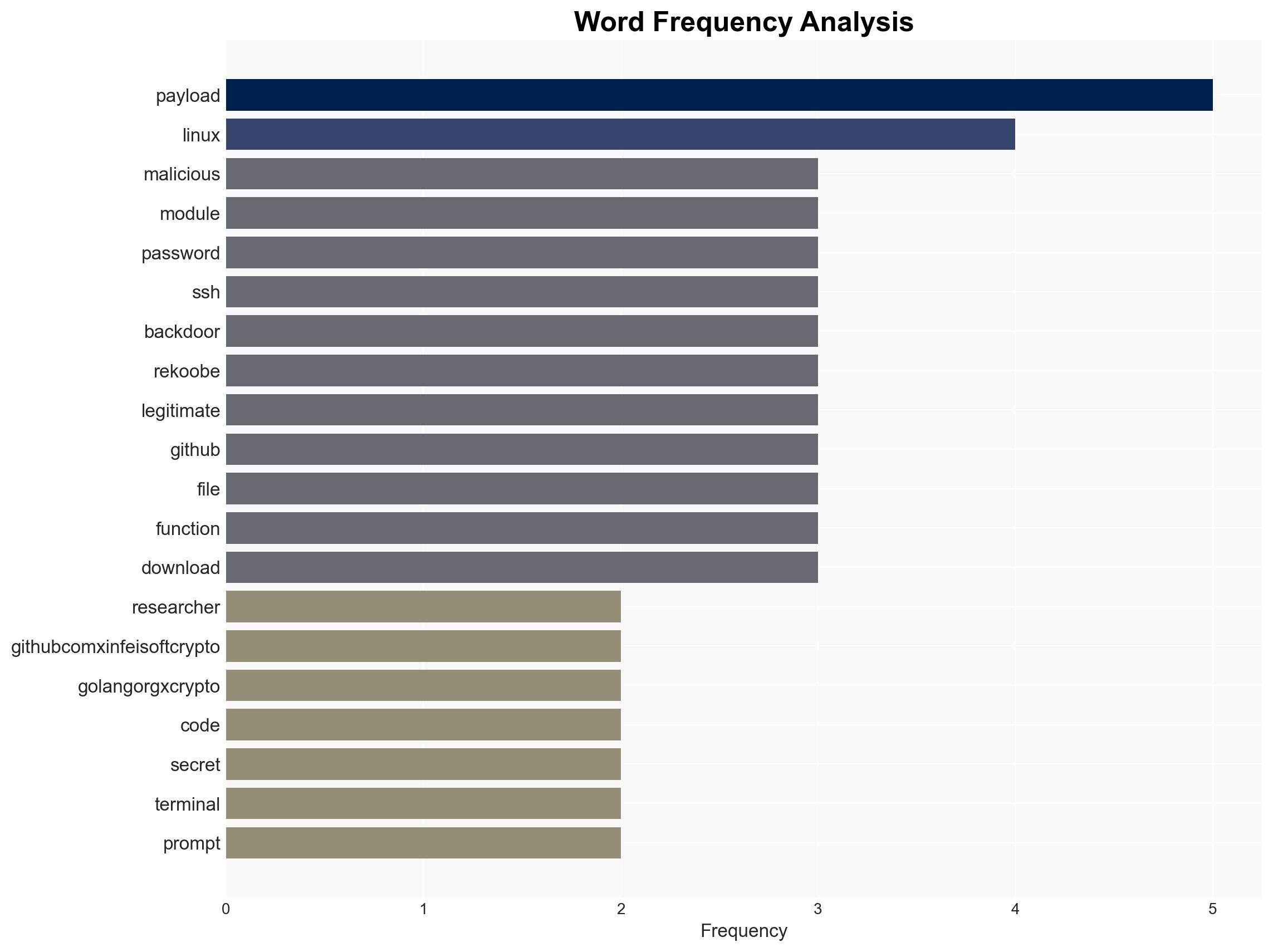
Malicious Go Module Harvests Passwords and Deploys Rekoobe Backdoor via SSH Access
Published on: 2026-02-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Malicious Go Crypto Module Steals Passwords Deploys Rekoobe Backdoor
1. BLUF (Bottom Line Up Front)
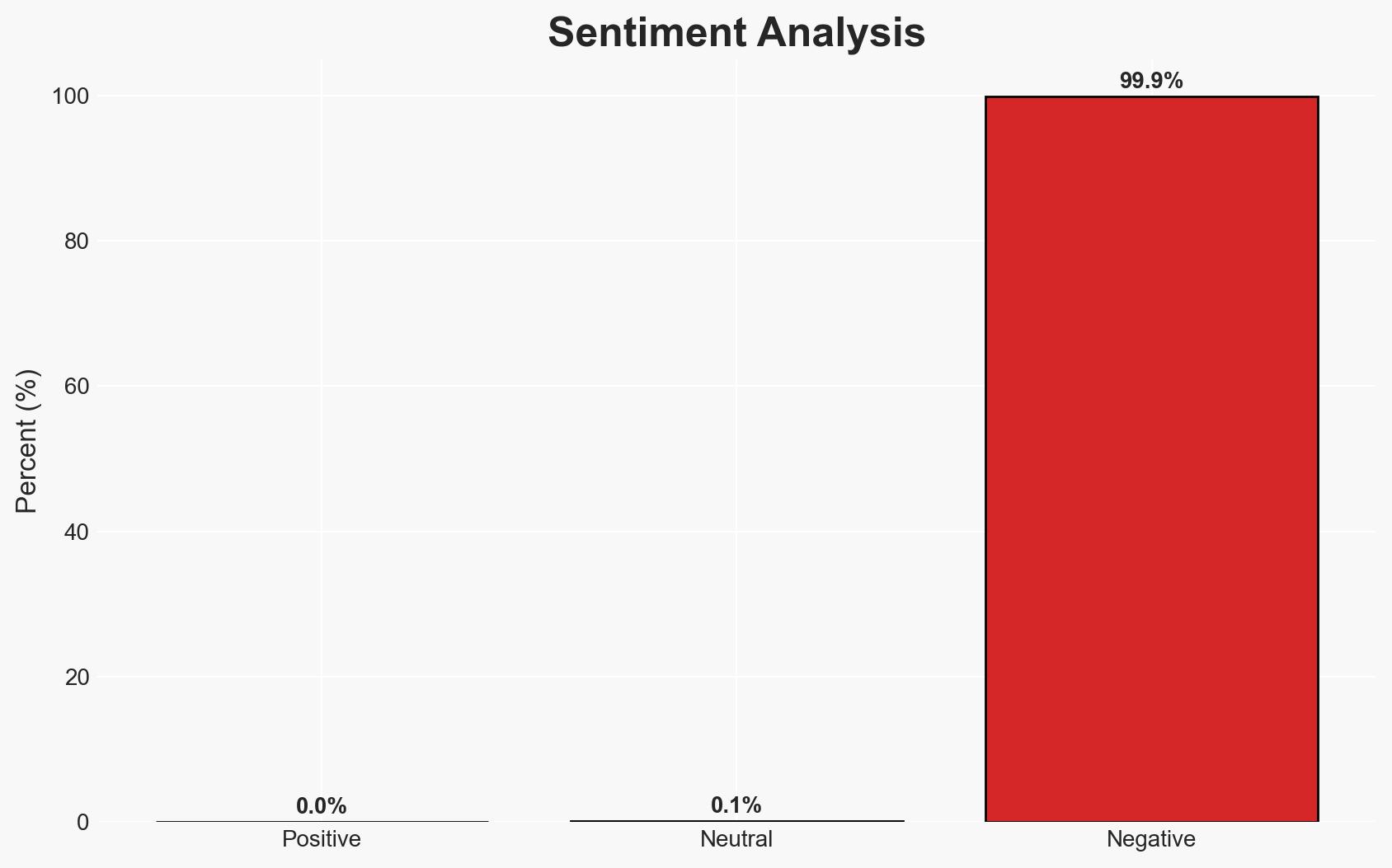
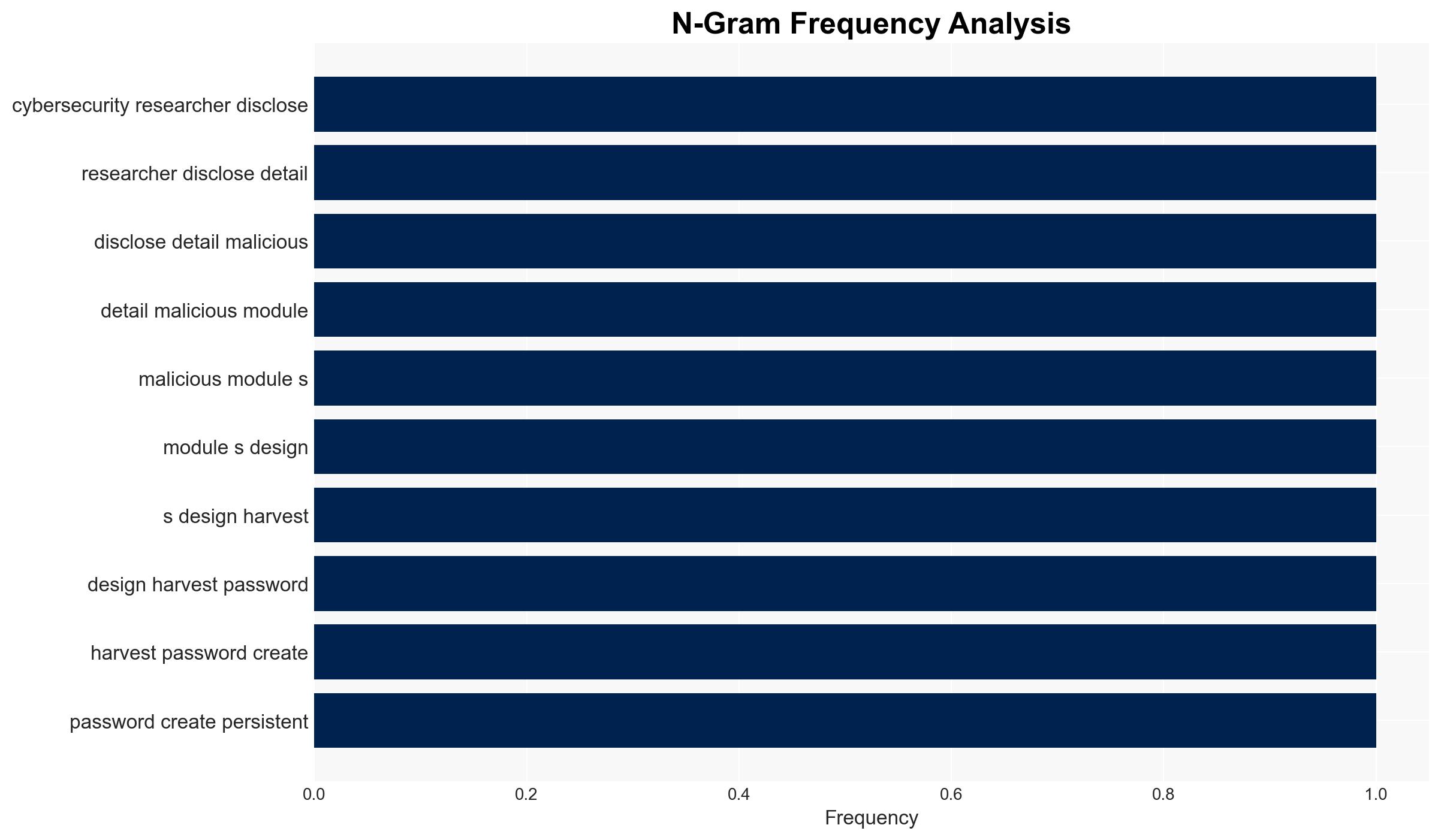
The malicious Go module, masquerading as a legitimate crypto library, poses a significant threat by stealing passwords and deploying the Rekoobe backdoor. This activity primarily affects Linux systems and is linked to Chinese nation-state actors. The campaign’s low-effort, high-impact nature suggests a high likelihood of recurrence. Overall confidence in this assessment is moderate due to the existing evidence and known actor patterns.
2. Competing Hypotheses
- Hypothesis A: The malicious Go module is part of a targeted campaign by Chinese nation-state actors, specifically APT31, to compromise Linux systems for espionage purposes. Evidence includes the use of Rekoobe, previously associated with Chinese actors, and the sophisticated nature of the attack. However, the exact attribution remains uncertain.
- Hypothesis B: The module is the work of independent cybercriminals exploiting namespace confusion for financial gain through credential theft and system compromise. While the attack’s sophistication suggests nation-state involvement, the lack of direct attribution evidence leaves room for alternative explanations.
- Assessment: Hypothesis A is currently better supported due to the historical use of Rekoobe by Chinese actors and the strategic targeting of high-value systems. Indicators such as further attribution evidence or changes in attack patterns could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The module’s primary goal is espionage; Chinese nation-state actors are involved; the attack leverages GitHub’s infrastructure for distribution.
- Information Gaps: Definitive attribution to specific actors; full scope of affected systems; details on command and control infrastructure.
- Bias & Deception Risks: Attribution bias towards known actors; potential for false flag operations; reliance on open-source reporting.
4. Implications and Strategic Risks
This development could lead to increased targeting of open-source repositories and supply chain vulnerabilities, impacting trust in software dependencies and open-source projects.
- Political / Geopolitical: Potential escalation in cyber tensions between China and affected nations, leading to diplomatic strains.
- Security / Counter-Terrorism: Increased risk of similar attacks targeting critical infrastructure and sensitive data repositories.
- Cyber / Information Space: Heightened awareness and scrutiny of open-source projects; potential for increased cyber defense measures.
- Economic / Social: Potential economic impact on organizations reliant on compromised systems; erosion of trust in open-source software.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor for similar namespace confusion attacks; enhance security measures for open-source dependencies; engage with GitHub for rapid response.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for threat intelligence sharing; invest in supply chain security tools; conduct regular audits of software dependencies.
- Scenario Outlook: Best: Improved defenses deter future attacks; Worst: Widespread exploitation of similar vulnerabilities; Most-Likely: Continued targeting with incremental improvements in attack sophistication.
6. Key Individuals and Entities
- APT31 (Chinese nation-state group)
- Kirill Boychenko (Socket security researcher)
- Go security team
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, nation-state actors, supply chain attacks, open-source vulnerabilities, Linux backdoor, espionage, namespace confusion
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us