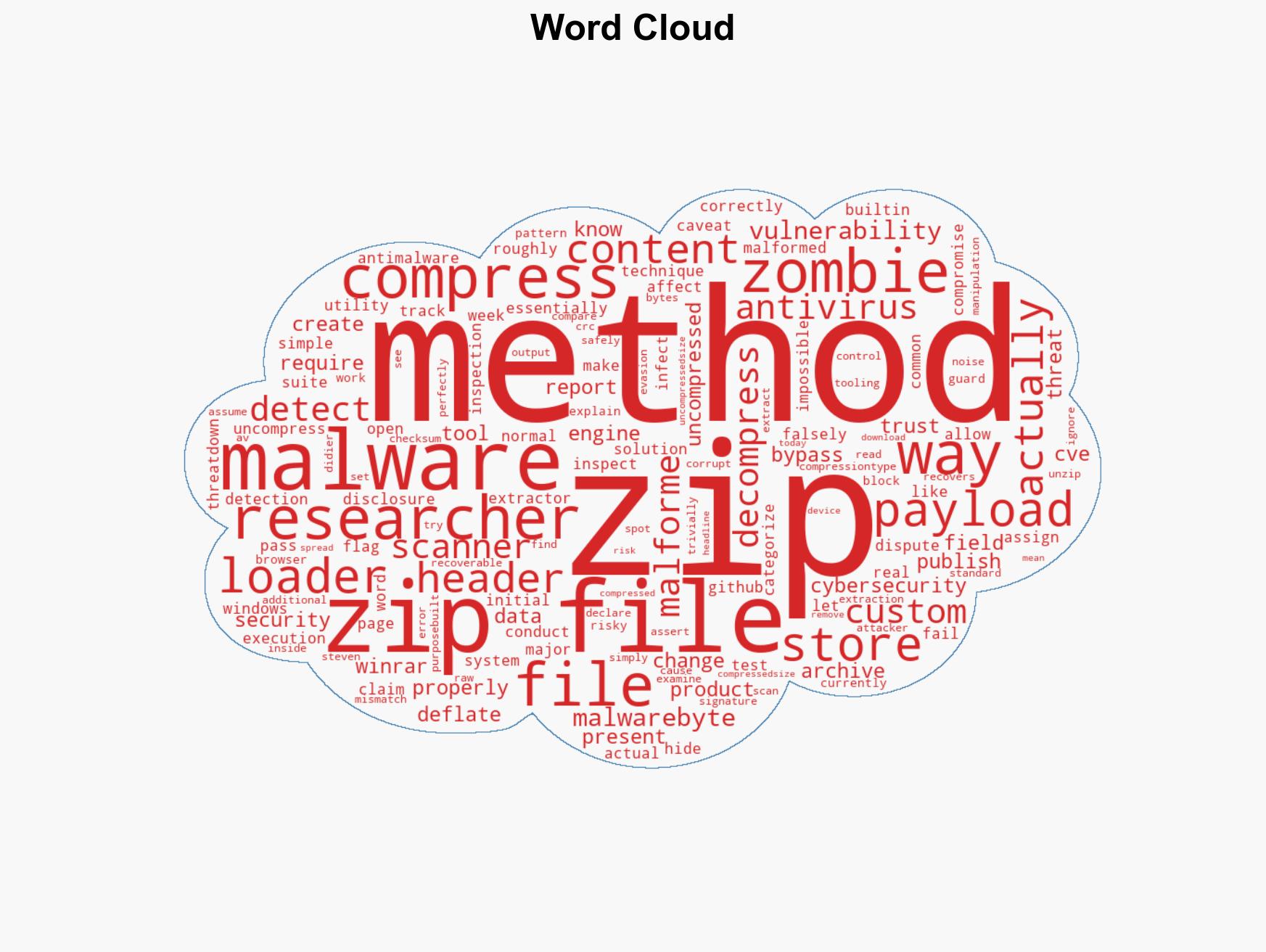
Malicious ZIP technique evades detection by most antivirus software during initial scans
Published on: 2026-03-16
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Zombie ZIP method can fool antivirus during the first scan
1. BLUF (Bottom Line Up Front)
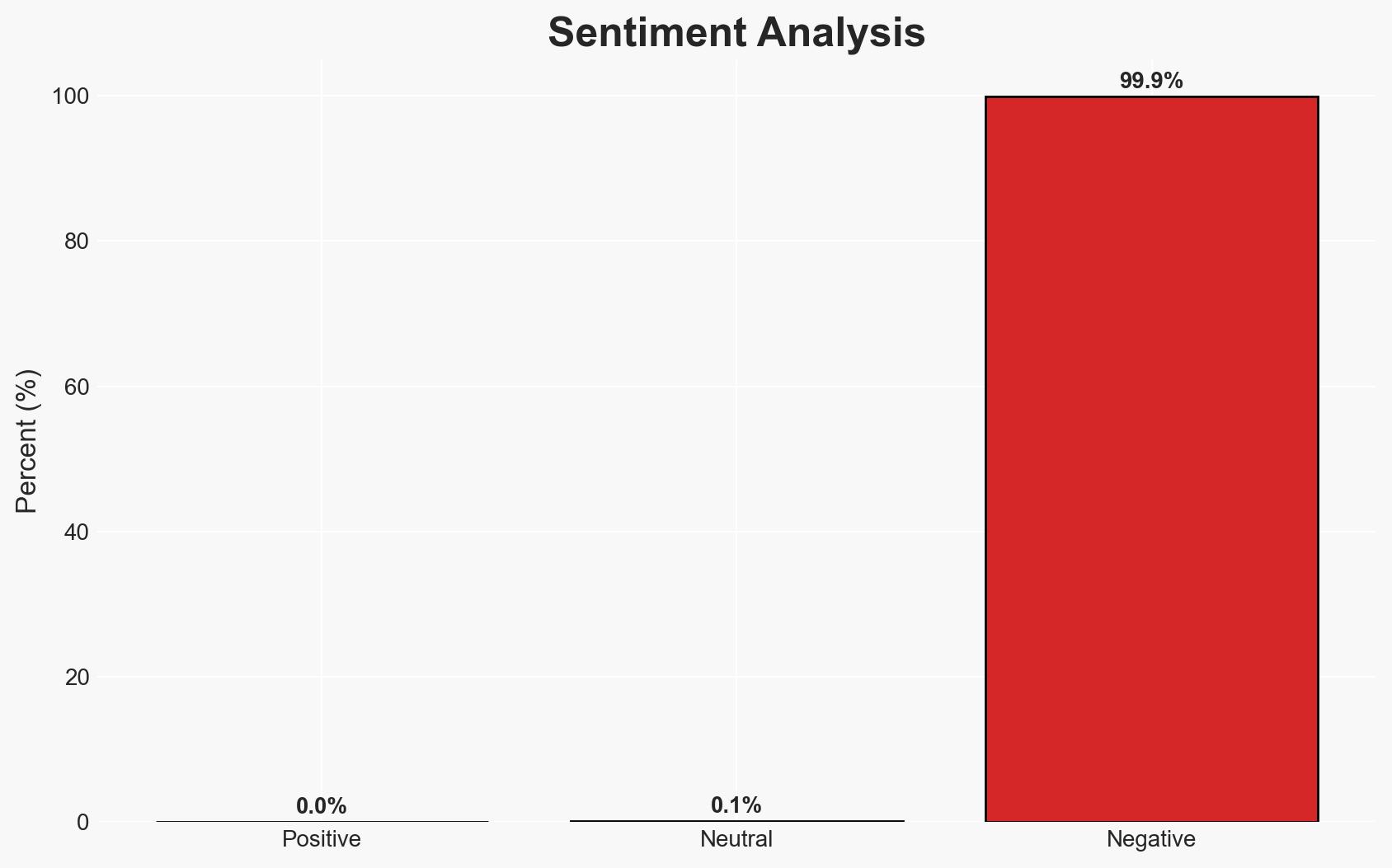
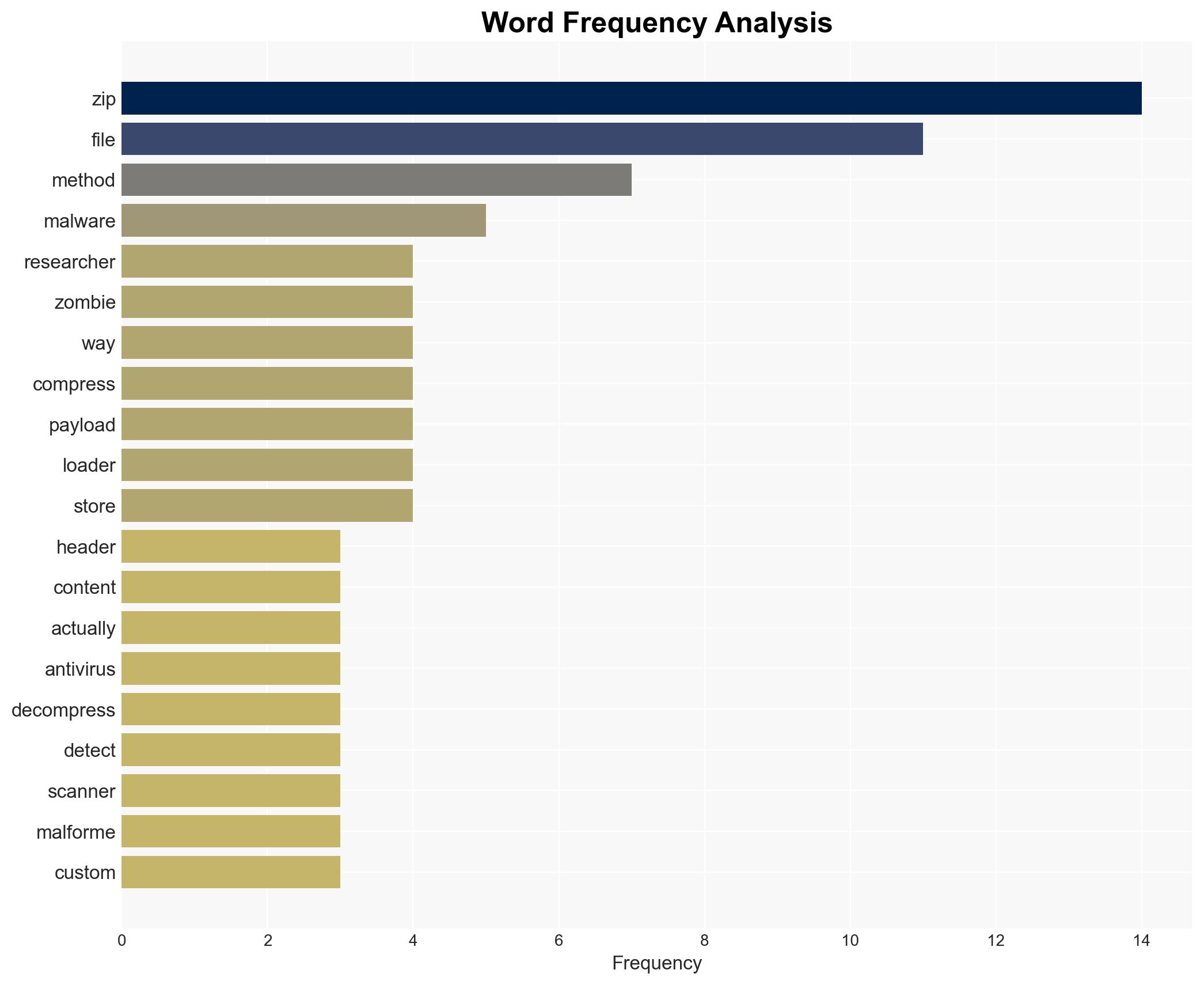
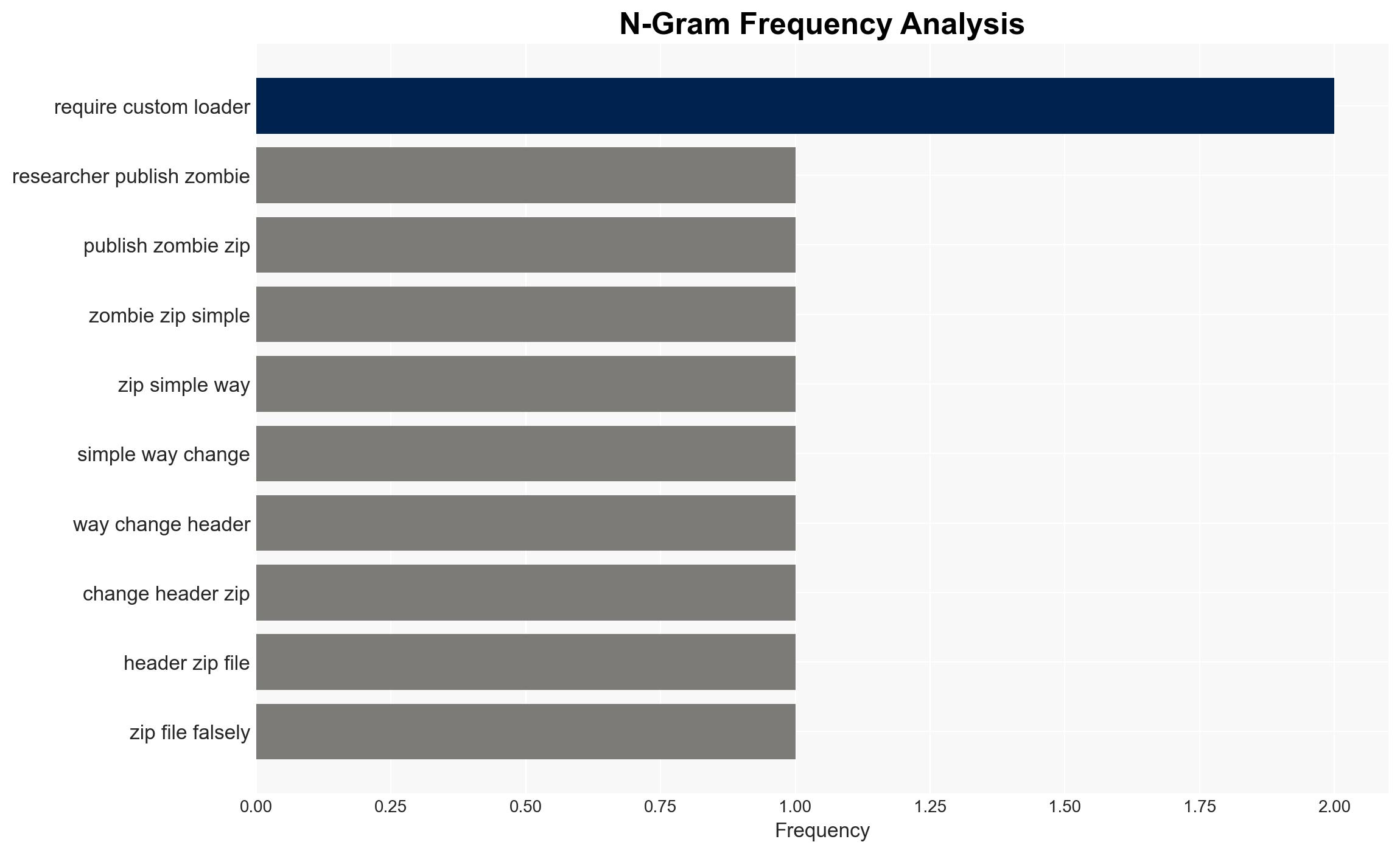
The “Zombie ZIP” method exploits a vulnerability in antivirus software, allowing malware to bypass initial scans by altering ZIP file headers. This technique affects antivirus vendors and potentially compromised systems. The overall confidence level in this assessment is moderate, given the requirement for a custom loader to execute the payload.
2. Competing Hypotheses
- Hypothesis A: The Zombie ZIP method poses a significant threat to cybersecurity by enabling widespread malware distribution. Supporting evidence includes the high failure rate of antivirus engines during initial scans. Contradicting evidence is the necessity of a custom loader, limiting its impact to already compromised systems.
- Hypothesis B: The Zombie ZIP method is a limited threat, primarily affecting systems with existing vulnerabilities. Supporting evidence includes the requirement for a custom loader and the ability of some antivirus solutions to detect the payload post-decompression. Contradicting evidence is the initial bypass of most antivirus engines.
- Assessment: Hypothesis B is currently better supported due to the requirement for a custom loader, which restricts the method’s applicability to systems already compromised or targeted by sophisticated attackers. Indicators such as widespread adoption of the method or development of more sophisticated loaders could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Antivirus vendors will update their engines to detect malformed ZIP headers; the custom loader requirement limits the method’s applicability; cybersecurity researchers will continue to develop countermeasures.
- Information Gaps: Detailed data on the prevalence of the Zombie ZIP method in active cyber campaigns; effectiveness of antivirus updates in addressing this vulnerability.
- Bias & Deception Risks: Potential bias from cybersecurity vendors in downplaying the threat; risk of manipulation by actors promoting the method as more effective than it is.
4. Implications and Strategic Risks
The Zombie ZIP method could lead to temporary increases in malware infections until antivirus solutions adapt. Its impact is likely limited to targeted attacks rather than widespread campaigns.
- Political / Geopolitical: Limited direct implications, but potential for state actors to exploit the method in targeted cyber operations.
- Security / Counter-Terrorism: Increased risk of targeted cyber attacks on critical infrastructure if leveraged by sophisticated threat actors.
- Cyber / Information Space: Possible short-term disruption in cybersecurity operations as vendors update detection capabilities.
- Economic / Social: Minimal economic impact unless the method is leveraged in large-scale ransomware or data theft campaigns.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Encourage antivirus vendors to update detection algorithms; monitor for signs of the method’s use in active campaigns.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity researchers to enhance detection methods; invest in training for identifying and mitigating similar threats.
- Scenario Outlook: Best: Antivirus solutions effectively mitigate the threat. Worst: Sophisticated actors develop more effective loaders, increasing the method’s impact. Most-Likely: Limited impact with gradual mitigation by cybersecurity vendors.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, antivirus evasion, malware, cyber threat, information security, vulnerability management
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us