ManoMano Alerts Users to Data Breach Linked to Cyberattack on Customer Support Subcontractor
Published on: 2026-02-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: French DIY etailer ManoMano admits customer data stolen
1. BLUF (Bottom Line Up Front)
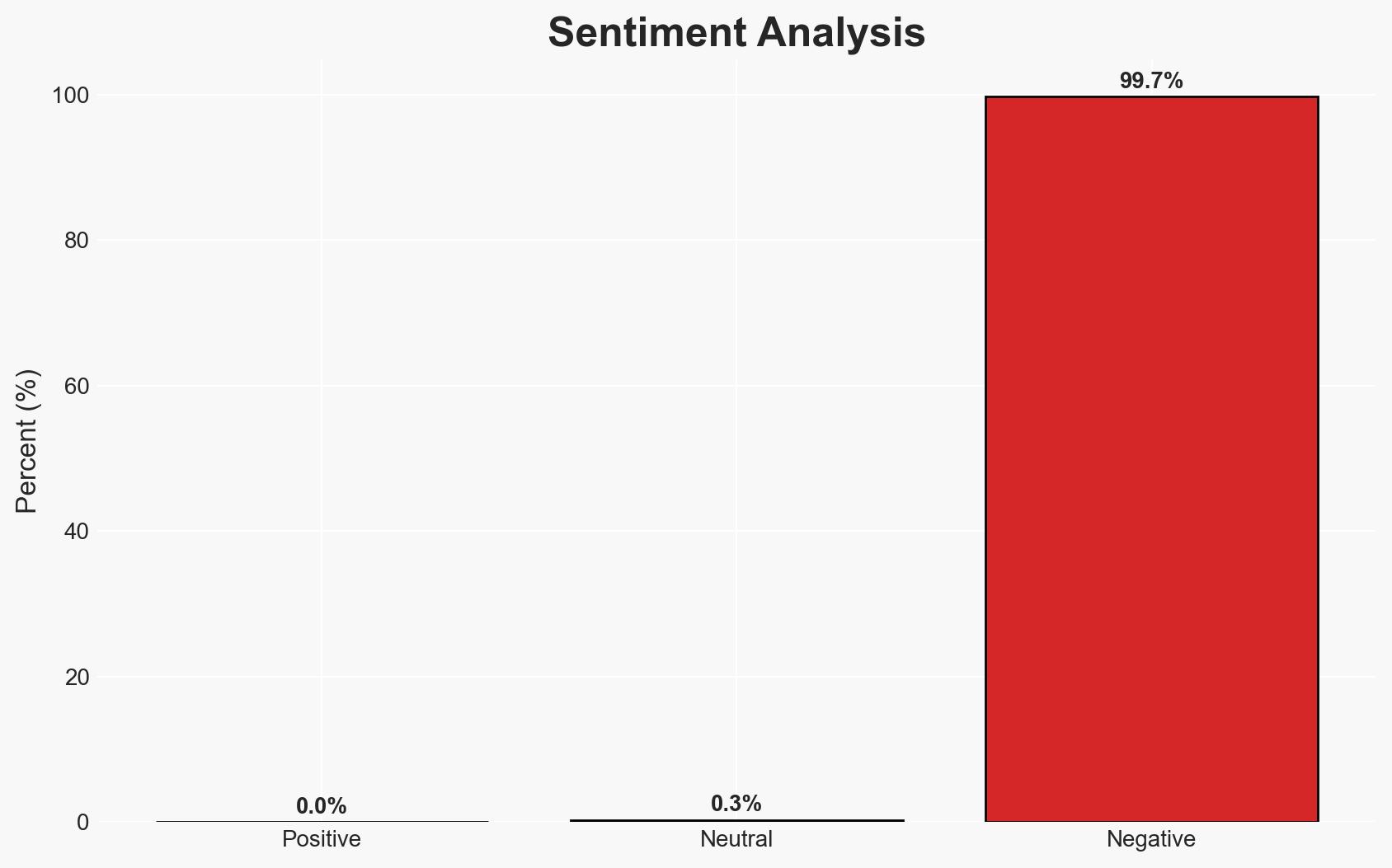
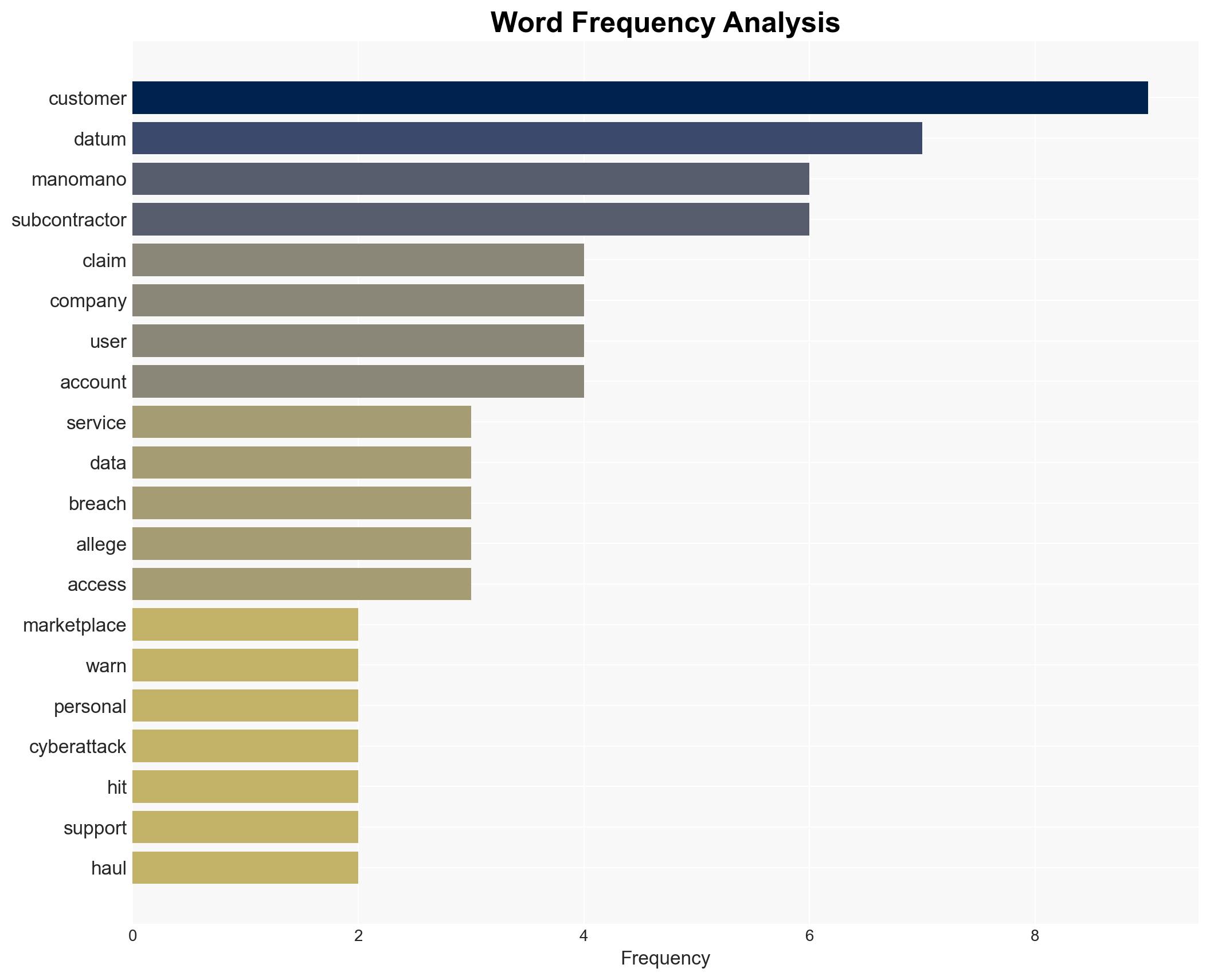
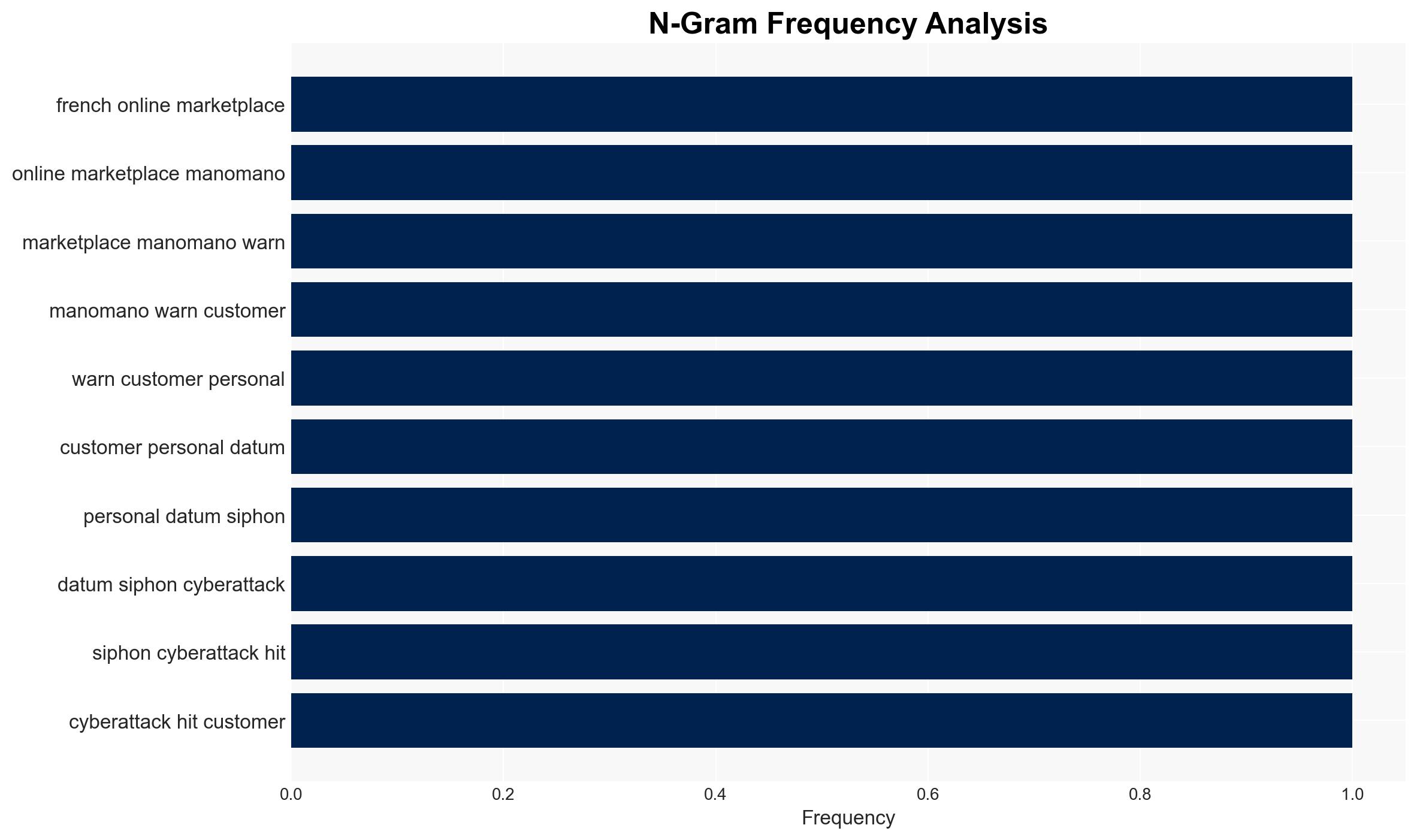
The cyberattack on ManoMano’s customer support subcontractor resulted in the unauthorized extraction of customer data, potentially affecting millions across Europe. The breach, claimed by an actor named “Indra,” suggests a larger data compromise than publicly acknowledged by ManoMano. This incident poses significant risks for phishing and impersonation. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The breach was limited to the data ManoMano has publicly acknowledged, and the claims by “Indra” are exaggerated. Supporting evidence includes ManoMano’s official statements and immediate actions to mitigate the breach. Contradicting evidence includes “Indra’s” claims of a larger dataset.
- Hypothesis B: The breach is as extensive as claimed by “Indra,” affecting tens of millions of user accounts. Supporting evidence includes the detailed claims made by “Indra” on BreachForums. Contradicting evidence includes the lack of corroboration from other sources and the company’s official stance.
- Assessment: Hypothesis B is currently better supported due to the detailed nature of “Indra’s” claims and the potential underreporting by ManoMano. Key indicators that could shift this judgment include independent verification of the data volume and further disclosures by ManoMano or third-party investigators.
3. Key Assumptions and Red Flags
- Assumptions: The subcontractor had extensive access to customer data; “Indra” is a credible actor; ManoMano’s public disclosures are accurate to their knowledge.
- Information Gaps: The identity and security posture of the subcontractor; independent verification of the breach’s scale; the exact method of data extraction.
- Bias & Deception Risks: Potential bias in ManoMano’s reporting to minimize reputational damage; possible exaggeration by “Indra” for notoriety or financial gain.
4. Implications and Strategic Risks
This breach could lead to increased scrutiny on subcontractor data security practices and impact ManoMano’s reputation and customer trust. The incident may also encourage similar attacks on other platforms.
- Political / Geopolitical: Potential regulatory responses in the EU regarding data protection and subcontractor oversight.
- Security / Counter-Terrorism: Increased risk of phishing and impersonation attacks leveraging the stolen data.
- Cyber / Information Space: Potential for further exploitation of vulnerabilities in widely used platforms like Zendesk.
- Economic / Social: Possible loss of consumer confidence in online marketplaces, affecting sales and market dynamics.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring for phishing attempts, verify the breach’s scale, and engage with cybersecurity experts for mitigation strategies.
- Medium-Term Posture (1–12 months): Strengthen subcontractor vetting and security protocols, and consider partnerships for improved cyber resilience.
- Scenario Outlook:
- Best: Breach impact is contained, and ManoMano strengthens security measures, restoring customer trust.
- Worst: Additional breaches occur, leading to significant financial and reputational damage.
- Most-Likely: ManoMano faces regulatory scrutiny and moderate reputational impact, prompting industry-wide security enhancements.
6. Key Individuals and Entities
- ManoMano
- Indra (alleged threat actor)
- Zendesk (unconfirmed subcontractor)
- CNIL (French data protection authority)
- ANSSI (French national cybersecurity agency)
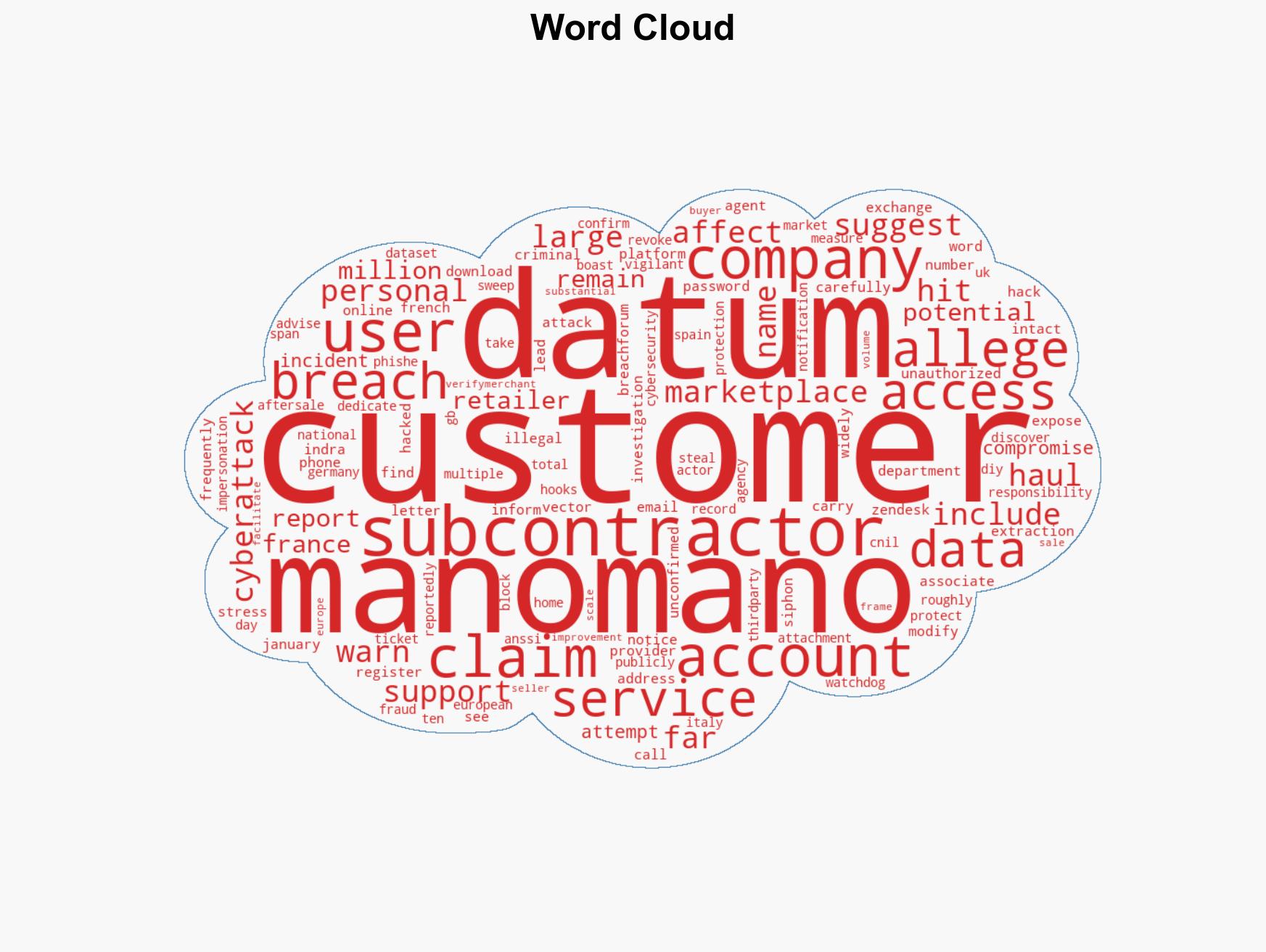
7. Thematic Tags
cybersecurity, data breach, phishing, subcontractor risk, European markets, regulatory response, online marketplaces
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us