Marquis Software Solutions files lawsuit against SonicWall for negligence linked to ransomware attack on banks
Published on: 2026-02-25
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Marquis sues SonicWall over backup breach that led to ransomware attack
1. BLUF (Bottom Line Up Front)
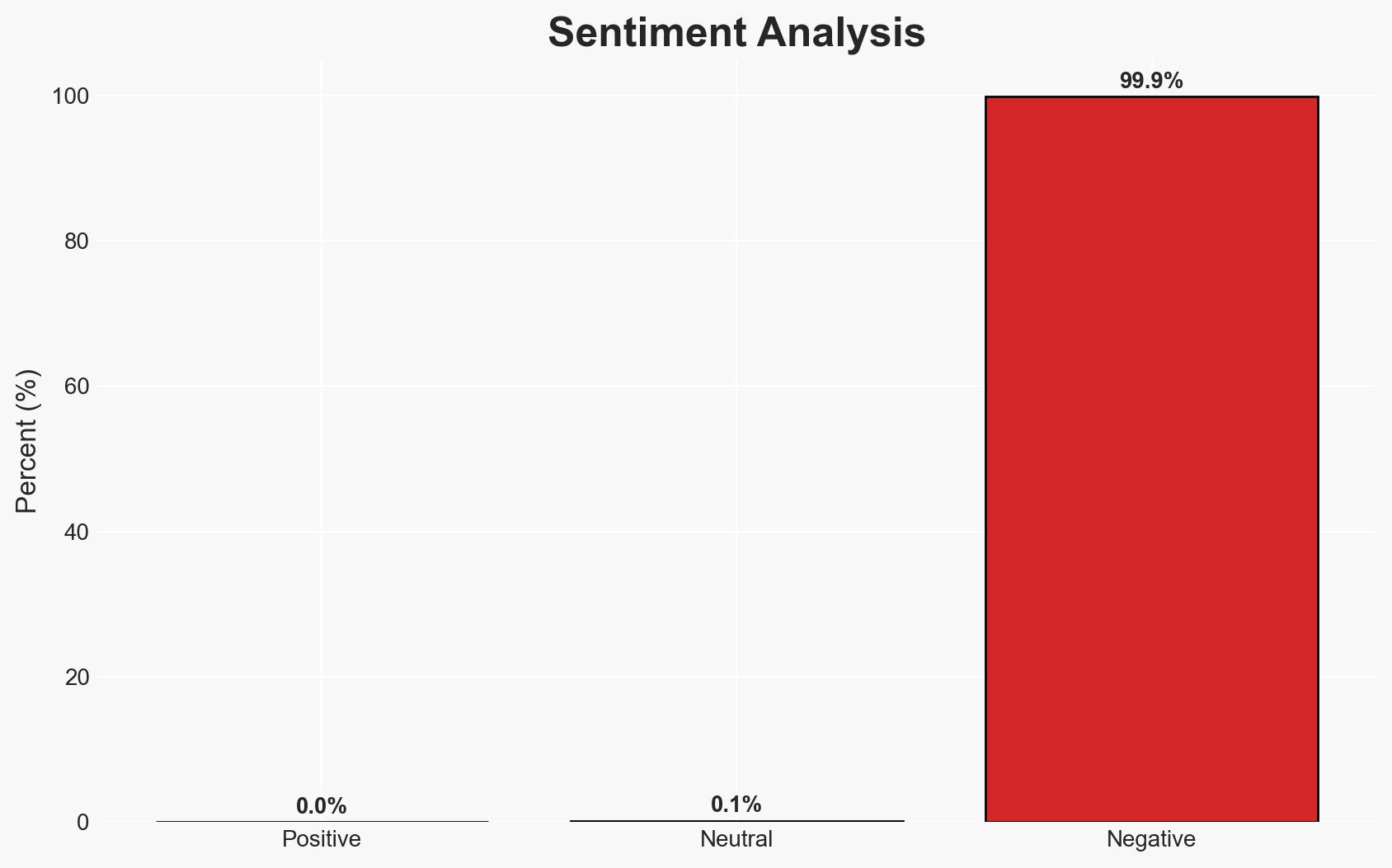
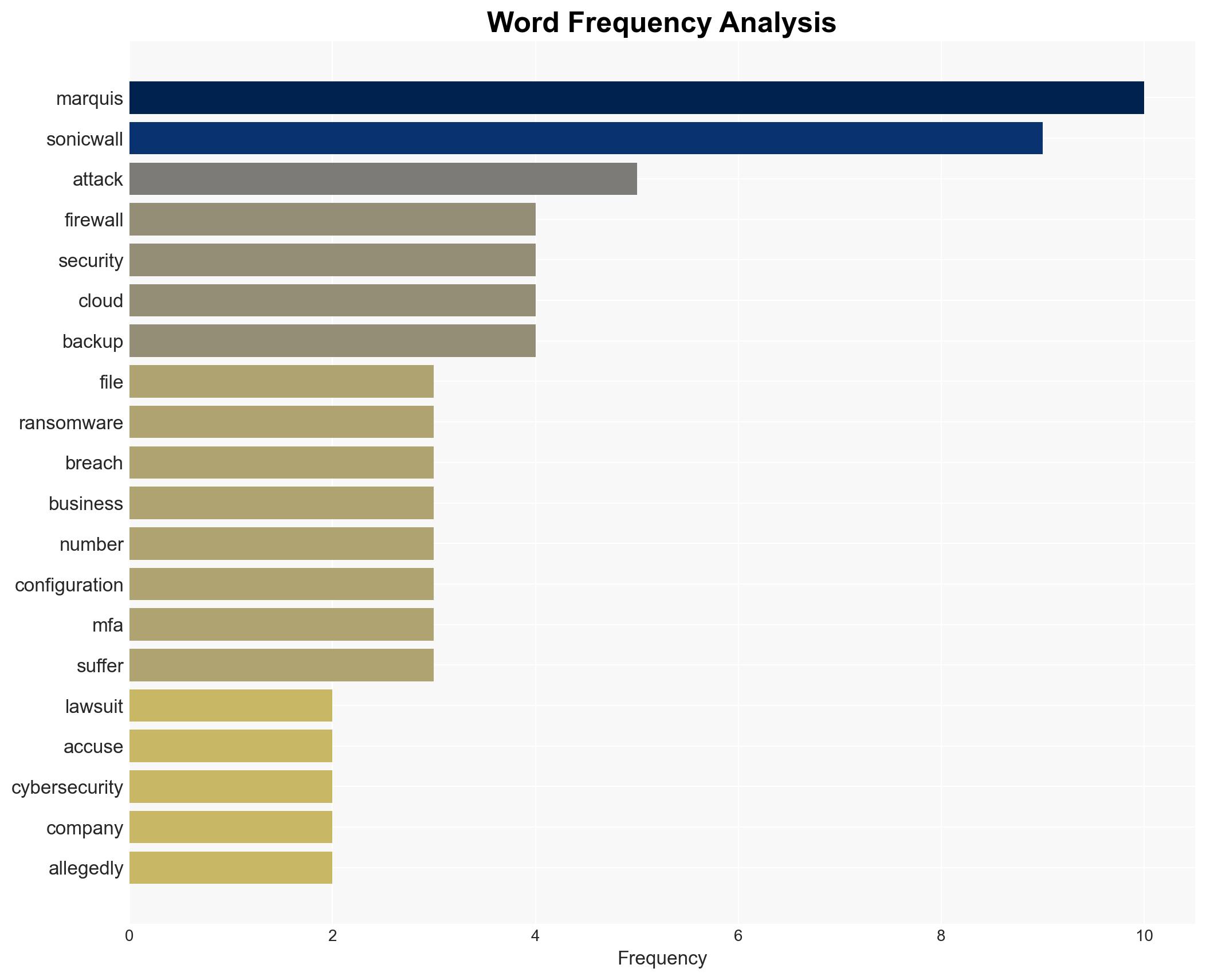
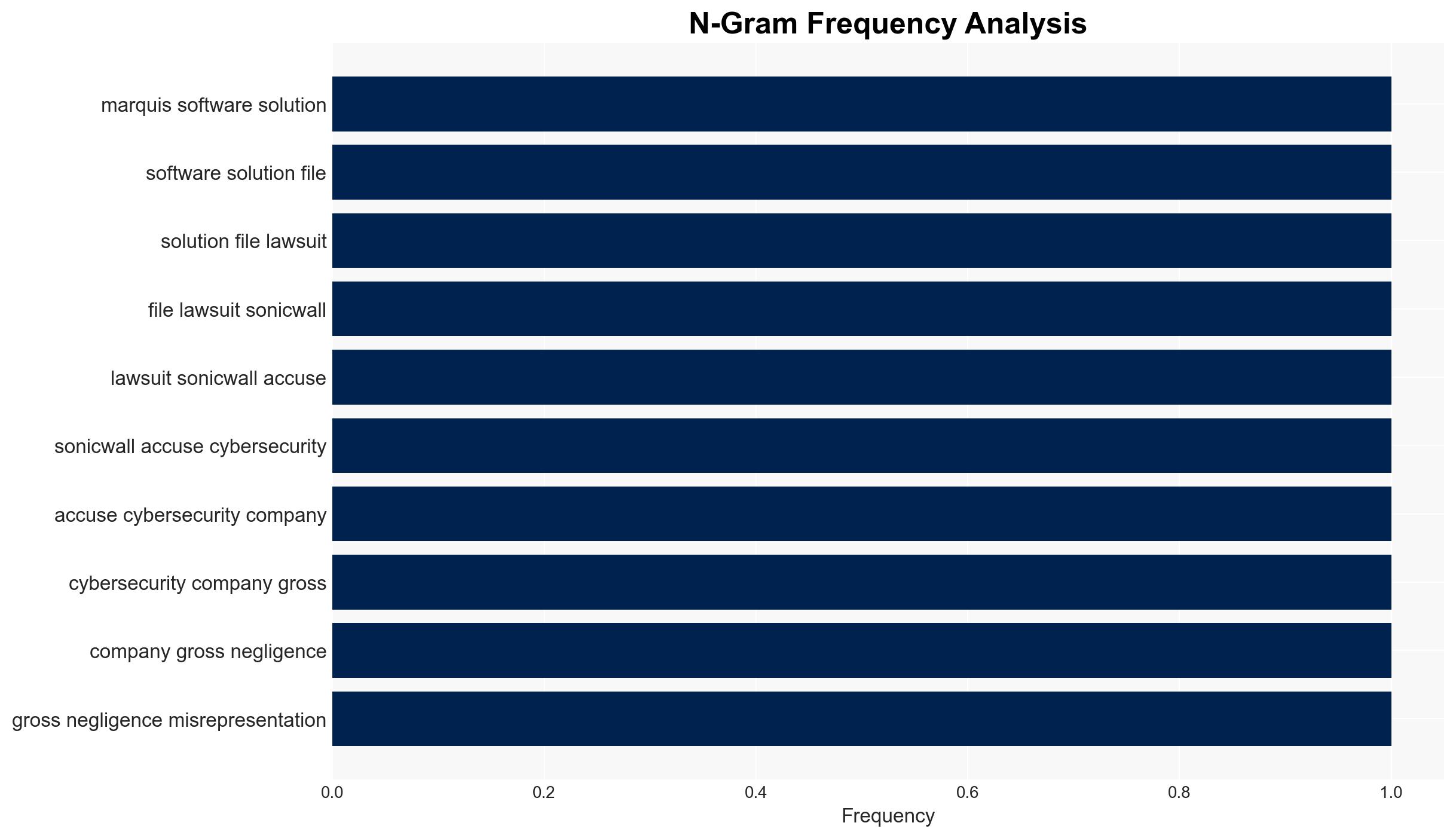
The lawsuit filed by Marquis Software Solutions against SonicWall highlights significant cybersecurity vulnerabilities and potential negligence, impacting over 700 financial institutions. The breach, attributed to state-sponsored hackers, exploited a flaw in SonicWall’s cloud backup service. This incident underscores the critical need for robust cybersecurity measures and vendor accountability. Overall confidence in this assessment is moderate due to existing information gaps and potential bias in the reporting.
2. Competing Hypotheses
- Hypothesis A: The breach was primarily due to SonicWall’s negligence in managing its cloud backup service, which introduced a vulnerability that was exploited by state-sponsored hackers. This is supported by the timeline of the API code change and the subsequent breach, but the exact nature of the negligence and its detection timeline remain uncertain.
- Hypothesis B: The breach was a result of a sophisticated attack that could have exploited multiple vulnerabilities, not solely reliant on SonicWall’s cloud backup flaw. This is less supported due to the specific identification of the API change as the breach vector, though it cannot be entirely ruled out without further technical details.
- Assessment: Hypothesis A is currently better supported due to the direct link between the API change and the breach. However, further technical analysis could shift this judgment, particularly if additional vulnerabilities are uncovered.
3. Key Assumptions and Red Flags
- Assumptions: SonicWall’s cloud backup service was the sole vector for the breach; state-sponsored actors were the primary threat actors; Marquis’s security measures were otherwise adequate.
- Information Gaps: Detailed technical analysis of the breach vector; full scope of data accessed by the attackers; SonicWall’s internal security protocols and response measures.
- Bias & Deception Risks: Potential bias from Marquis in attributing blame to SonicWall; possible underreporting or misrepresentation of the breach’s scope by SonicWall.
4. Implications and Strategic Risks
This development could lead to increased scrutiny on cybersecurity vendors and their accountability, influencing regulatory and industry standards. The breach may also embolden state-sponsored actors to exploit similar vulnerabilities in other systems.
- Political / Geopolitical: Potential diplomatic tensions if state-sponsored attribution is confirmed and linked to a specific nation-state.
- Security / Counter-Terrorism: Increased risk of similar attacks on critical infrastructure, necessitating heightened vigilance and improved defensive measures.
- Cyber / Information Space: Greater emphasis on securing cloud services and vendor-managed infrastructure; potential rise in cyber insurance claims and premiums.
- Economic / Social: Financial losses for affected institutions; potential erosion of trust in digital services, impacting customer confidence and market stability.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive audit of cloud-based security protocols; engage with cybersecurity experts to assess and mitigate vulnerabilities; enhance incident response capabilities.
- Medium-Term Posture (1–12 months): Develop stronger partnerships with cybersecurity vendors for continuous monitoring; invest in advanced threat detection technologies; advocate for industry-wide cybersecurity standards.
- Scenario Outlook:
- Best: Enhanced security measures prevent future breaches, restoring trust in digital services.
- Worst: Continued exploitation of vulnerabilities leads to widespread financial and reputational damage.
- Most-Likely: Incremental improvements in cybersecurity posture with ongoing challenges in vendor accountability.
6. Key Individuals and Entities
- Marquis Software Solutions
- SonicWall
- Mandiant (incident response company)
- State-sponsored hackers (not specifically identified)
7. Thematic Tags
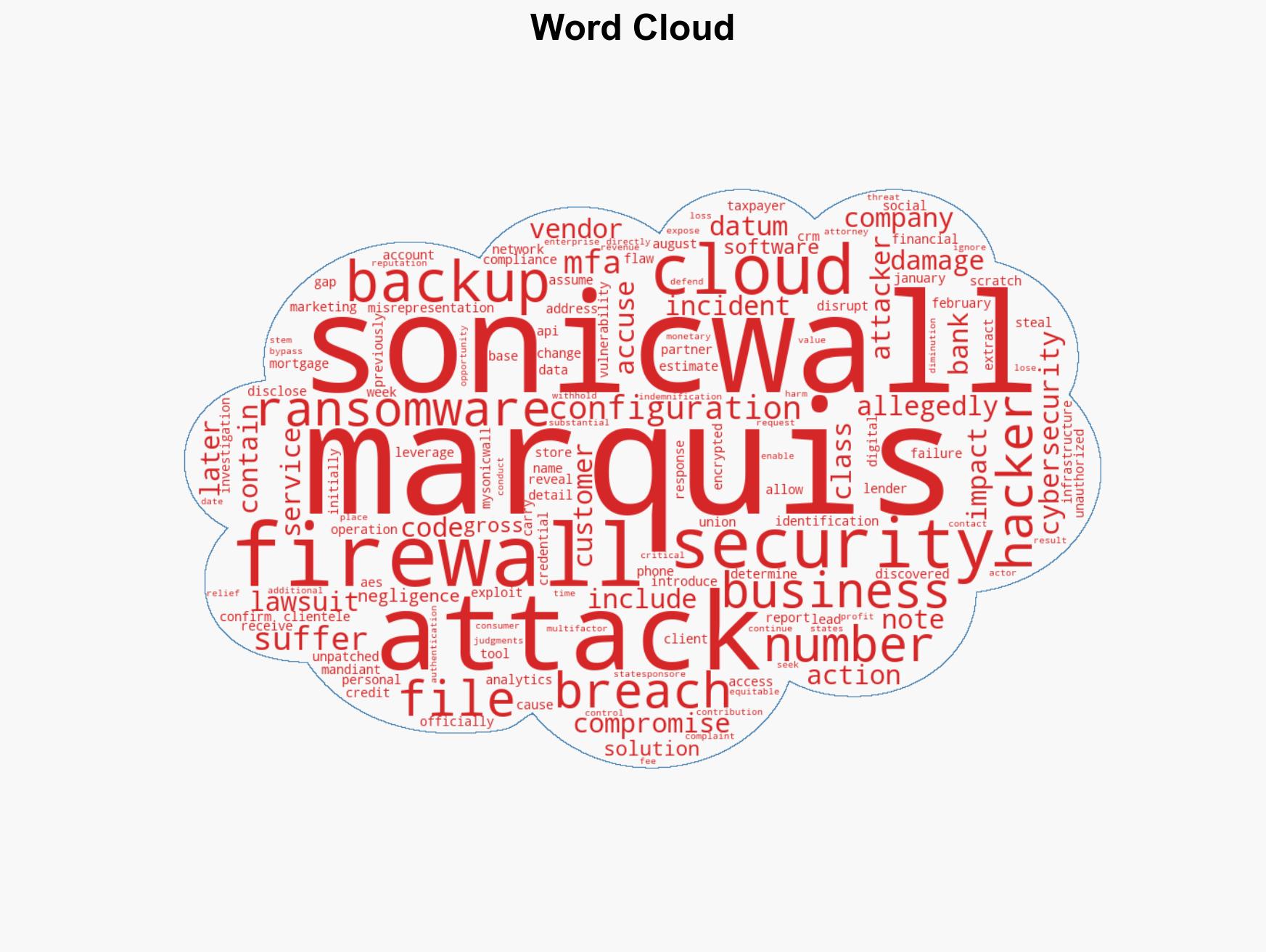
cybersecurity, state-sponsored hacking, vendor accountability, ransomware, cloud vulnerabilities, financial sector, data breach
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us