Maryland Resident Faces Charges for $53 Million Uranium Finance Crypto Exchange Hack and Laundering
Published on: 2026-03-31
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Maryland Man Charged Over 53m Uranium Finance Crypto Hack
1. BLUF (Bottom Line Up Front)
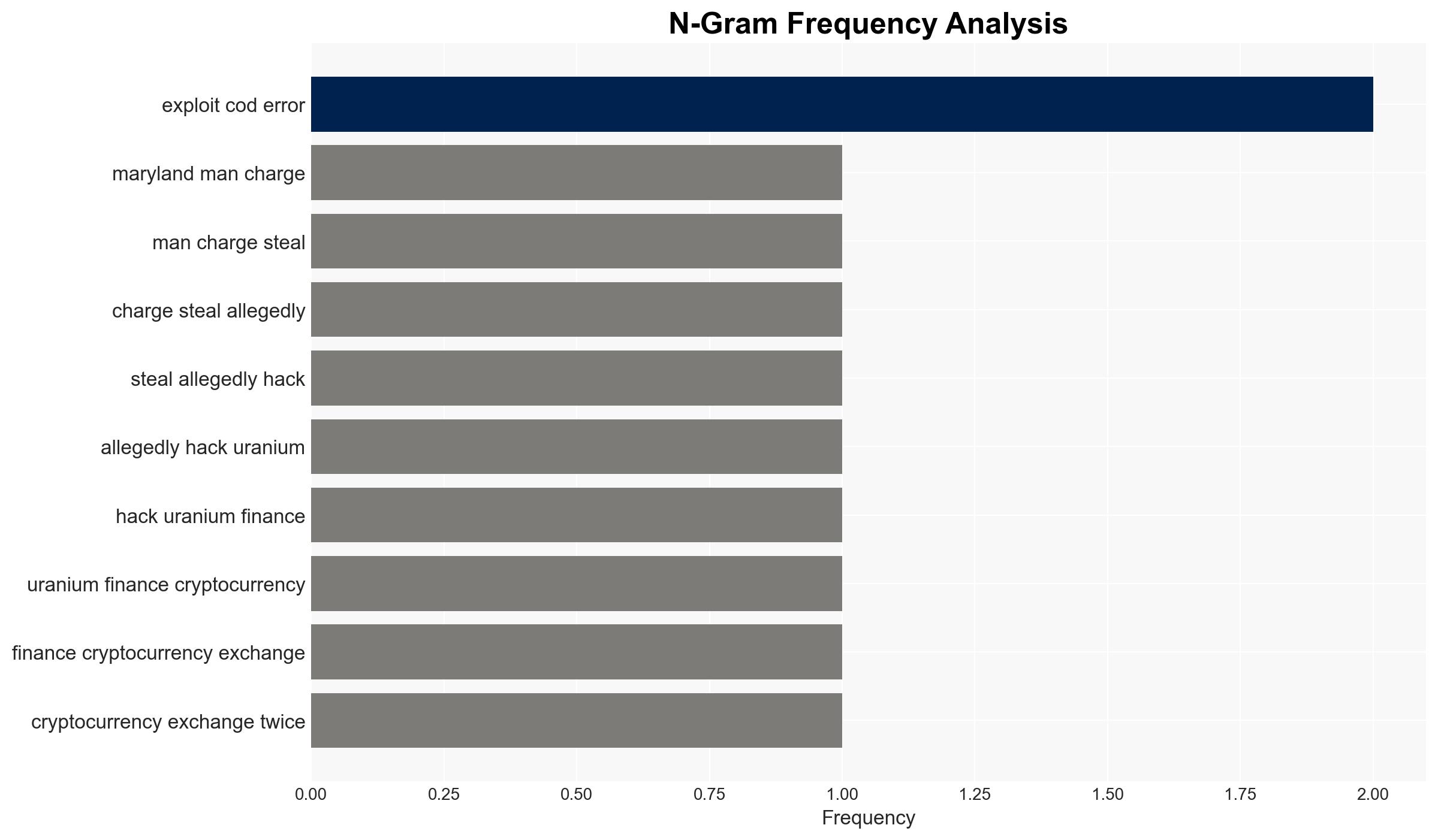
A Maryland man, Jonathan Spalletta, has been charged with hacking the Uranium Finance cryptocurrency exchange, resulting in over $53 million in losses and the platform’s shutdown. The case underscores vulnerabilities in decentralized finance platforms. The most likely hypothesis is that Spalletta exploited technical flaws for personal gain, with moderate confidence in this assessment due to limited information on potential accomplices or broader network involvement.
2. Competing Hypotheses
- Hypothesis A: Spalletta acted alone in exploiting technical vulnerabilities in Uranium Finance’s smart contracts to steal funds. Evidence includes the specific technical methods used and the lack of mention of accomplices. However, uncertainties remain regarding the potential involvement of others in planning or executing the attacks.
- Hypothesis B: Spalletta was part of a larger network or received external assistance in executing the hacks. This is supported by the complexity of laundering large sums through decentralized exchanges and mixers, which may require additional expertise. Contradicting evidence includes the current focus on Spalletta as the sole perpetrator.
- Assessment: Hypothesis A is currently better supported due to the detailed charges against Spalletta and the absence of evidence pointing to other individuals. Indicators that could shift this judgment include the discovery of communications or financial links to other actors.
3. Key Assumptions and Red Flags
- Assumptions: The technical flaws were not widely known prior to the attacks; Spalletta had the necessary skills to exploit these vulnerabilities; law enforcement has identified all major participants.
- Information Gaps: Details on whether Spalletta had any accomplices or if there were prior warnings about the vulnerabilities; the full extent of financial transactions involved in laundering the funds.
- Bias & Deception Risks: Potential bias in focusing solely on Spalletta without exploring broader network connections; risk of deception if Spalletta is concealing the involvement of others.
4. Implications and Strategic Risks
This development highlights the persistent vulnerabilities in decentralized finance platforms and may lead to increased regulatory scrutiny. The case could influence future cybersecurity measures and legal frameworks.
- Political / Geopolitical: Potential for increased international cooperation on cryptocurrency regulation and cybercrime.
- Security / Counter-Terrorism: Heightened awareness of cryptocurrency platforms as potential targets for criminal activities.
- Cyber / Information Space: Likely to prompt enhanced security protocols and audits in the cryptocurrency sector.
- Economic / Social: Possible erosion of trust in decentralized finance platforms, impacting user engagement and investment.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase monitoring of cryptocurrency exchanges for unusual activities; engage with cybersecurity firms to assess vulnerabilities in smart contracts.
- Medium-Term Posture (1–12 months): Develop partnerships with international law enforcement to enhance tracking of illicit cryptocurrency transactions; invest in public-private initiatives to improve blockchain security.
- Scenario Outlook:
- Best: Enhanced security measures prevent future breaches, restoring confidence in decentralized finance.
- Worst: Continued exploitation of vulnerabilities leads to significant financial losses and regulatory crackdowns.
- Most-Likely: Gradual improvements in security and regulatory frameworks, with ongoing challenges in enforcement.
6. Key Individuals and Entities
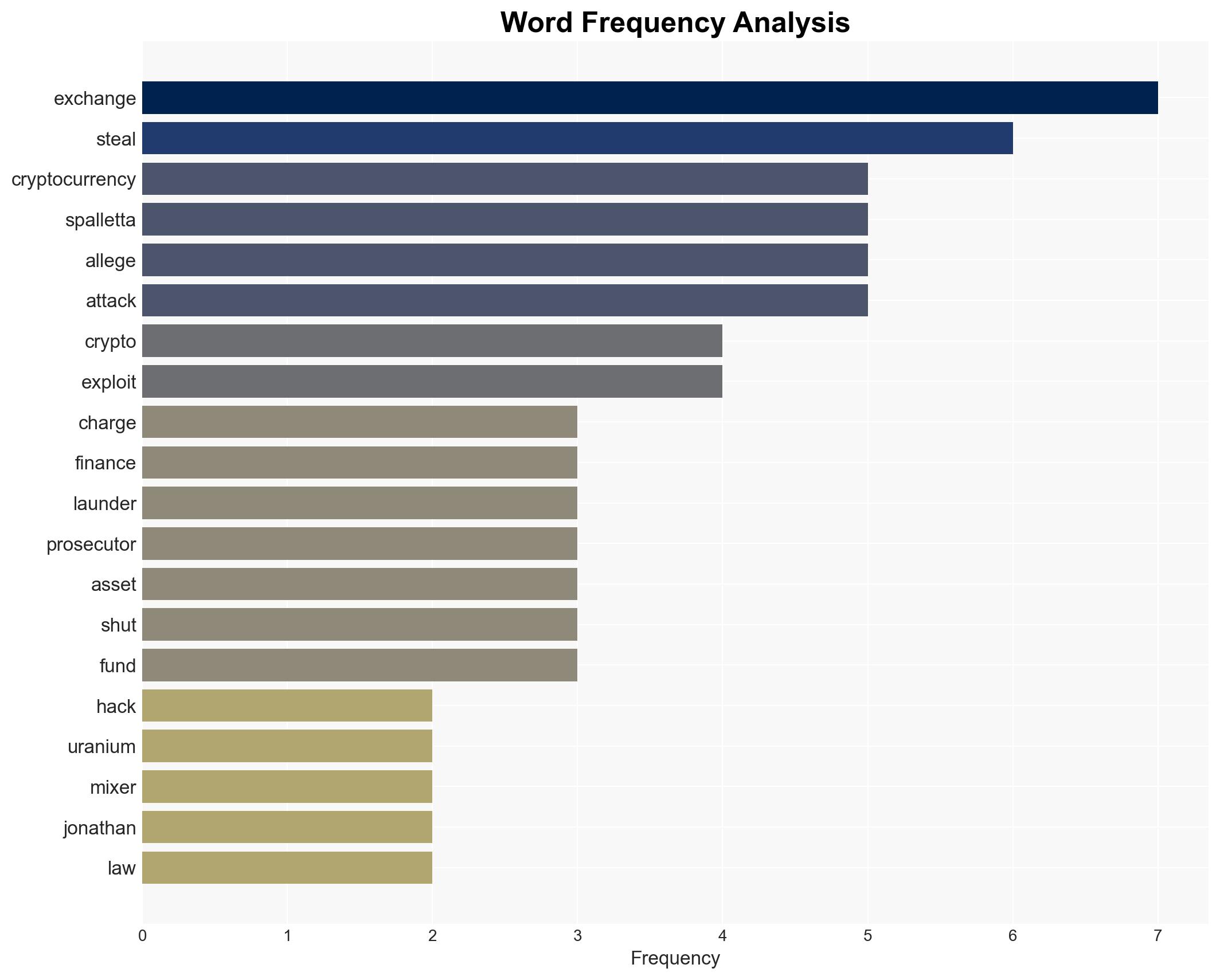
- Jonathan Spalletta – Alleged perpetrator
- Uranium Finance – Targeted cryptocurrency exchange
- Tornado Cash – Cryptocurrency mixer used for laundering
7. Thematic Tags
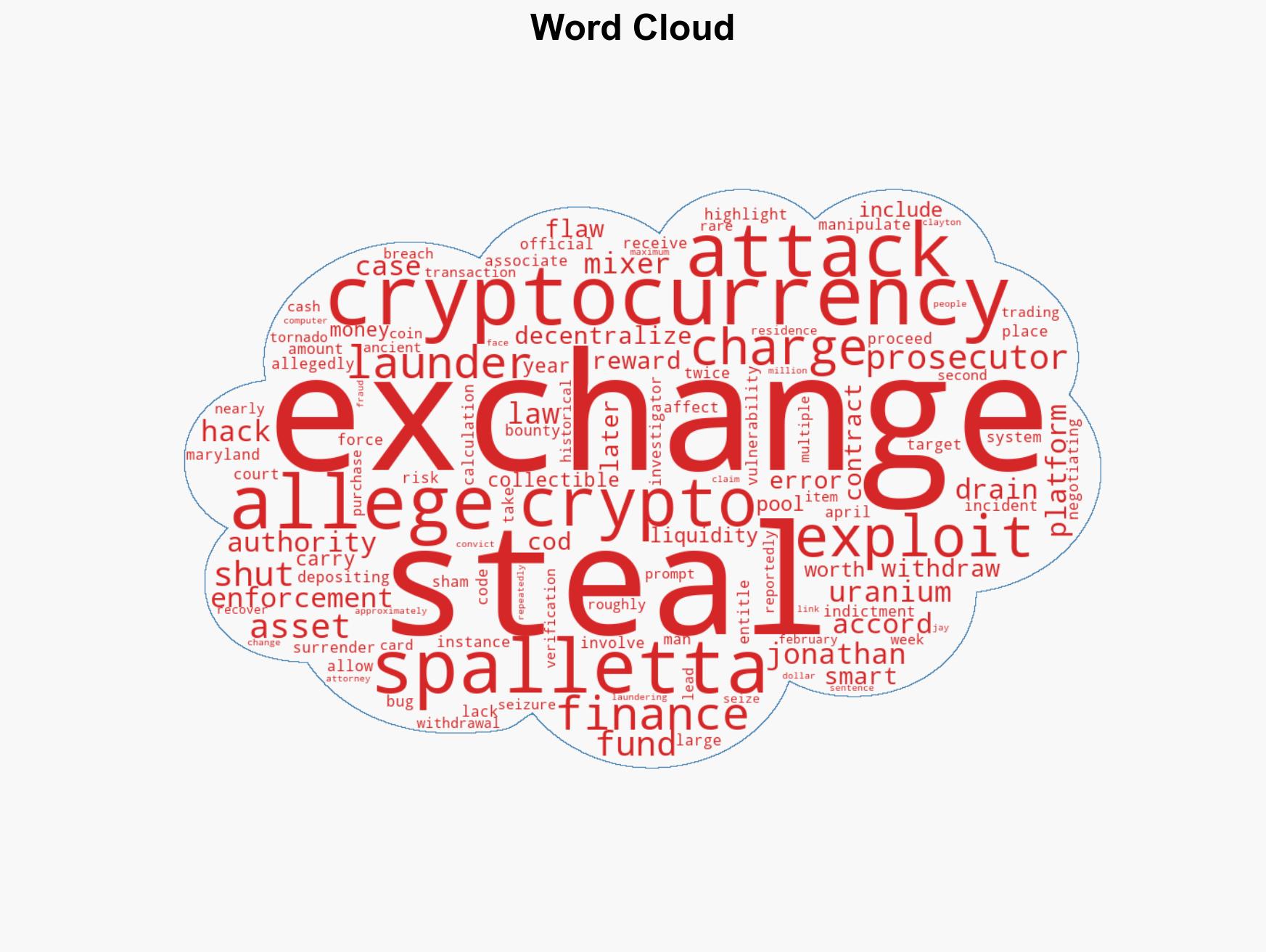
cybersecurity, cybercrime, cryptocurrency, decentralized finance, smart contract vulnerabilities, financial regulation, cyber security, money laundering
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us