Meta’s Move to Remove End-to-End Encryption from Instagram DMs Raises Privacy Concerns Amid Global Surveillan…
Published on: 2026-03-20
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: The Danger Behind Metas Decision to Kill End-to-End Encrypted Instagram DMs
1. BLUF (Bottom Line Up Front)
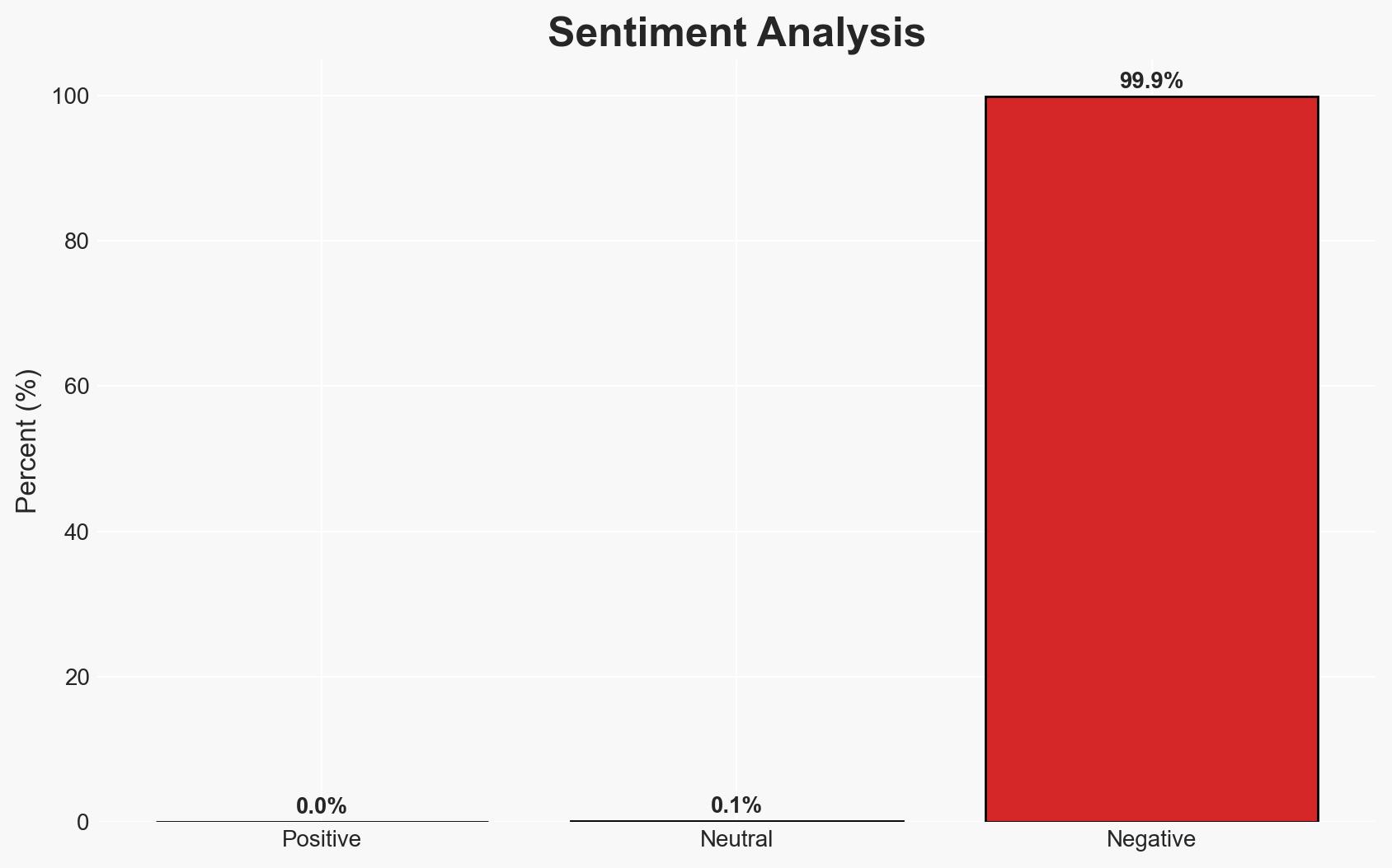
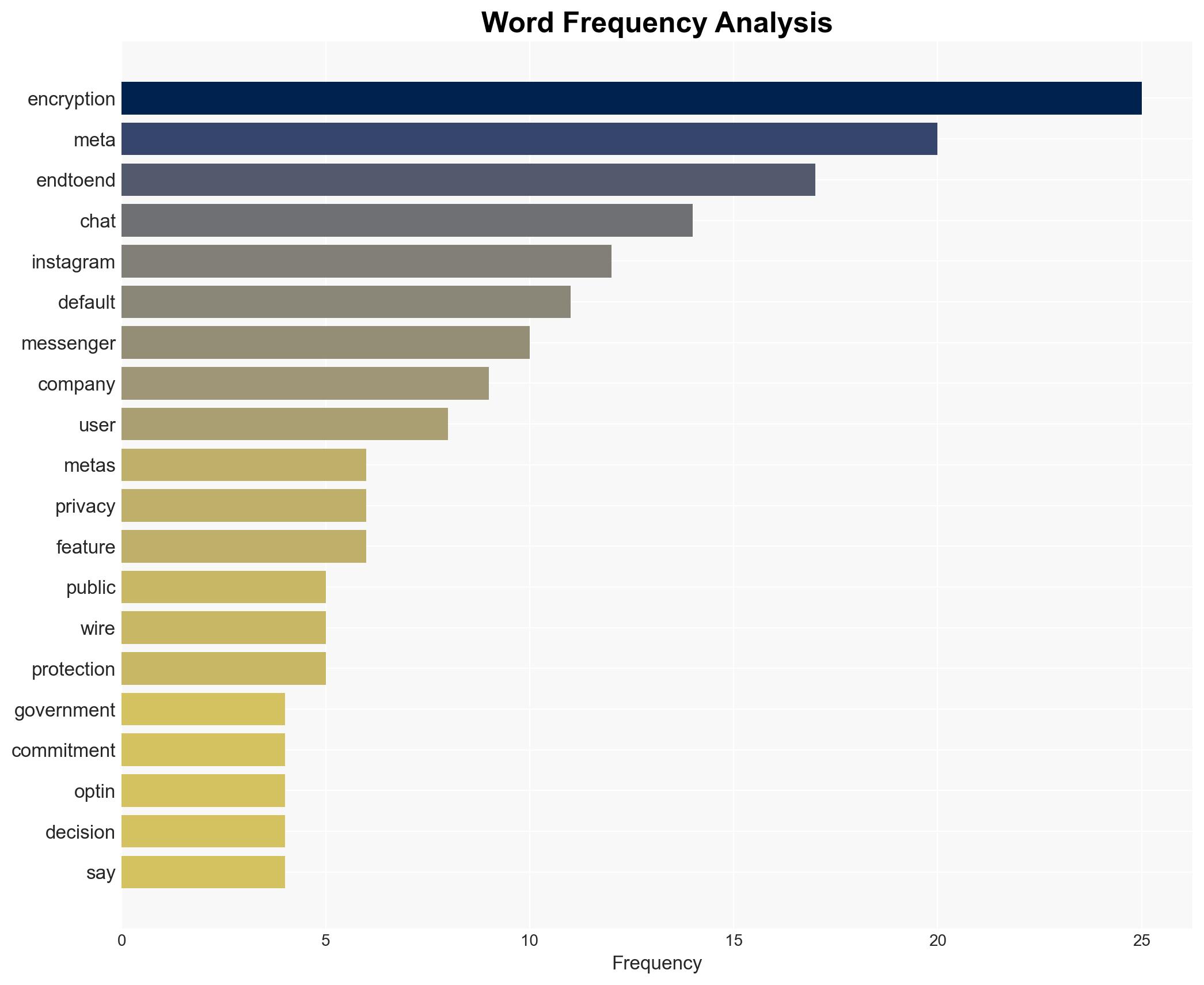
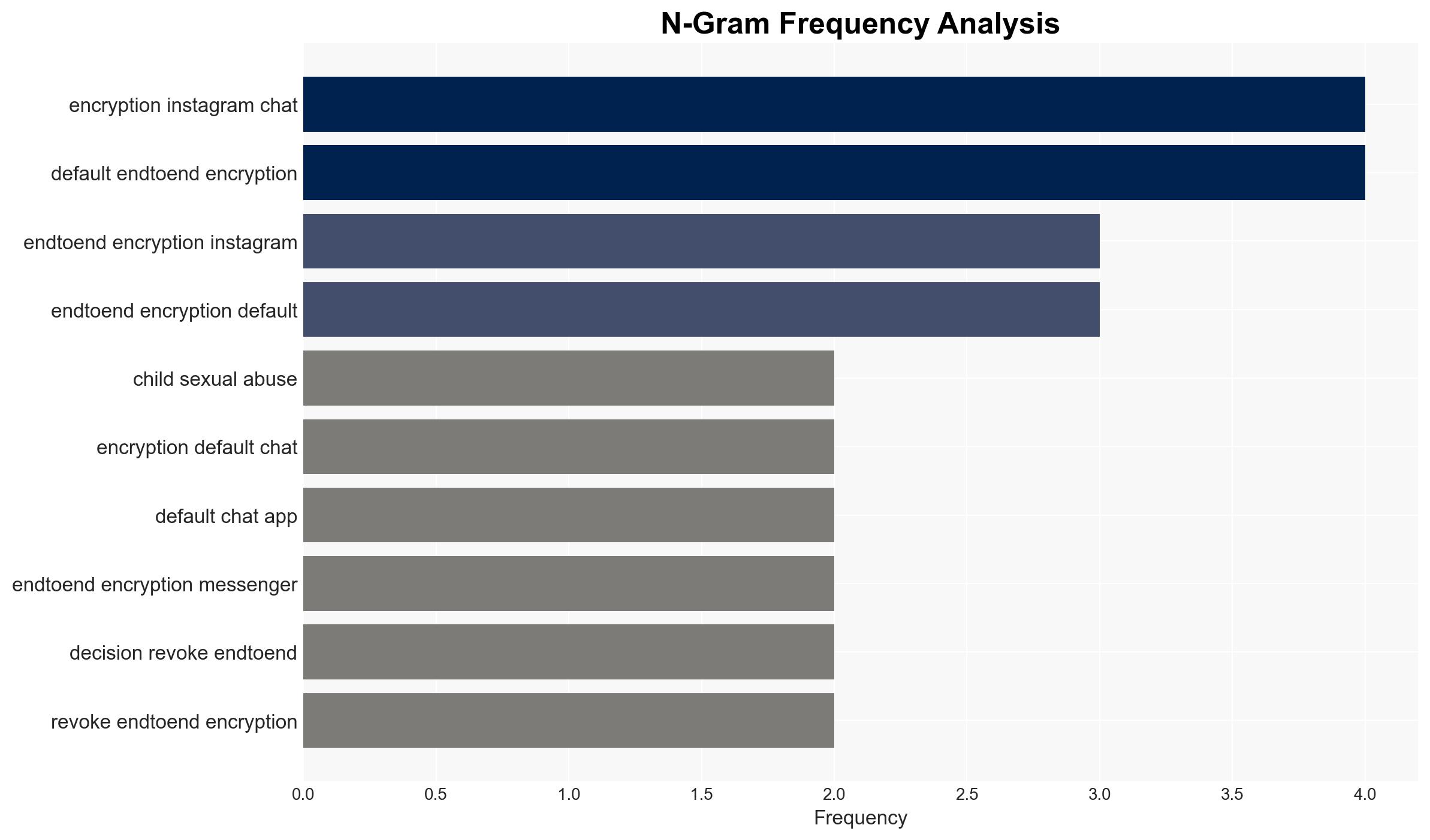
Meta’s decision to eliminate end-to-end encryption (E2EE) for Instagram Direct Messaging (DMs) could set a precedent weakening privacy commitments across the tech industry. This move may embolden governmental surveillance and erode user trust in digital privacy. The most likely hypothesis is that Meta’s decision is driven by low user adoption and external pressures, with moderate confidence in this assessment.
2. Competing Hypotheses
- Hypothesis A: Meta’s decision is primarily driven by low user adoption of the opt-in E2EE feature on Instagram DMs, as stated by the company. Supporting evidence includes Meta’s public statement on user adoption rates. However, the lack of transparency on adoption metrics raises uncertainties.
- Hypothesis B: The decision is influenced by external pressures from governments seeking to expand surveillance capabilities. This is supported by historical pressures on Meta regarding encryption. Contradicting evidence includes Meta’s longstanding public commitment to privacy, although recent actions suggest a shift.
- Assessment: Hypothesis A is currently better supported due to Meta’s explicit reasoning and the technical challenges of implementing E2EE. Future shifts in government policy or public backlash could alter this assessment.
3. Key Assumptions and Red Flags
- Assumptions: Meta’s public statements reflect its true motivations; user adoption data is accurately represented; governmental pressures are significant but not the primary driver.
- Information Gaps: Detailed user adoption statistics; internal Meta deliberations on E2EE; specific governmental pressures or communications.
- Bias & Deception Risks: Meta’s narrative may be biased to justify the decision; potential underreporting of governmental influence; cognitive bias towards assuming corporate transparency.
4. Implications and Strategic Risks
This development could weaken industry-wide commitments to privacy, increase governmental surveillance capabilities, and diminish user trust in digital platforms.
- Political / Geopolitical: Potential for increased government surveillance and pressure on other tech companies to follow suit.
- Security / Counter-Terrorism: Reduced encryption may aid law enforcement but also increase risks of misuse by repressive regimes.
- Cyber / Information Space: Potential rise in cyber threats as privacy protections weaken; increased user vulnerability to data breaches.
- Economic / Social: Possible decline in user engagement on platforms perceived as insecure; broader societal implications for privacy norms.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor Meta’s communications and user reactions; engage with privacy advocacy groups to assess impact.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies to reinforce privacy commitments; invest in public awareness campaigns on digital privacy.
- Scenario Outlook:
- Best: Meta reverses decision under public pressure, reinforcing privacy norms.
- Worst: Industry-wide rollback of E2EE, leading to increased surveillance and user distrust.
- Most-Likely: Limited rollback with increased scrutiny on privacy practices; potential regulatory responses.
6. Key Individuals and Entities
- Meta Platforms, Inc.
- Instagram (a division of Meta)
- Johns Hopkins cryptographer Matt Green
- Meta spokesperson (unnamed)
- Davi Ottenheimer, security executive
7. Thematic Tags
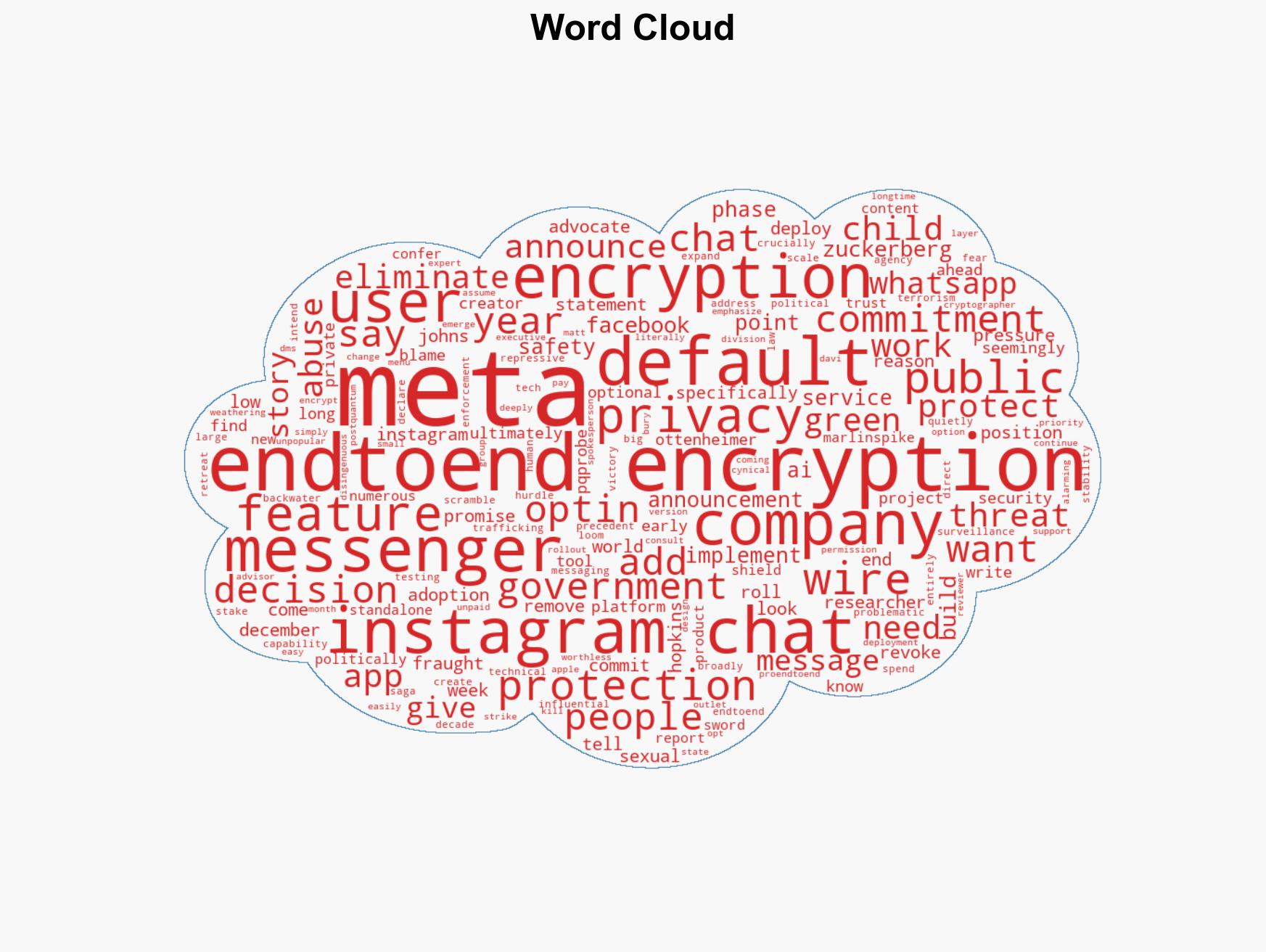
cybersecurity, digital privacy, encryption, surveillance, tech industry, user trust, government pressure
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us