Microsoft Alerts Users to Fake Gaming Tools Distributing Remote Access Trojan via Legitimate Windows Processes
Published on: 2026-03-01
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Fake Xeno and Roblox Utilities Used to Install Windows RAT Microsoft Warns
1. BLUF (Bottom Line Up Front)
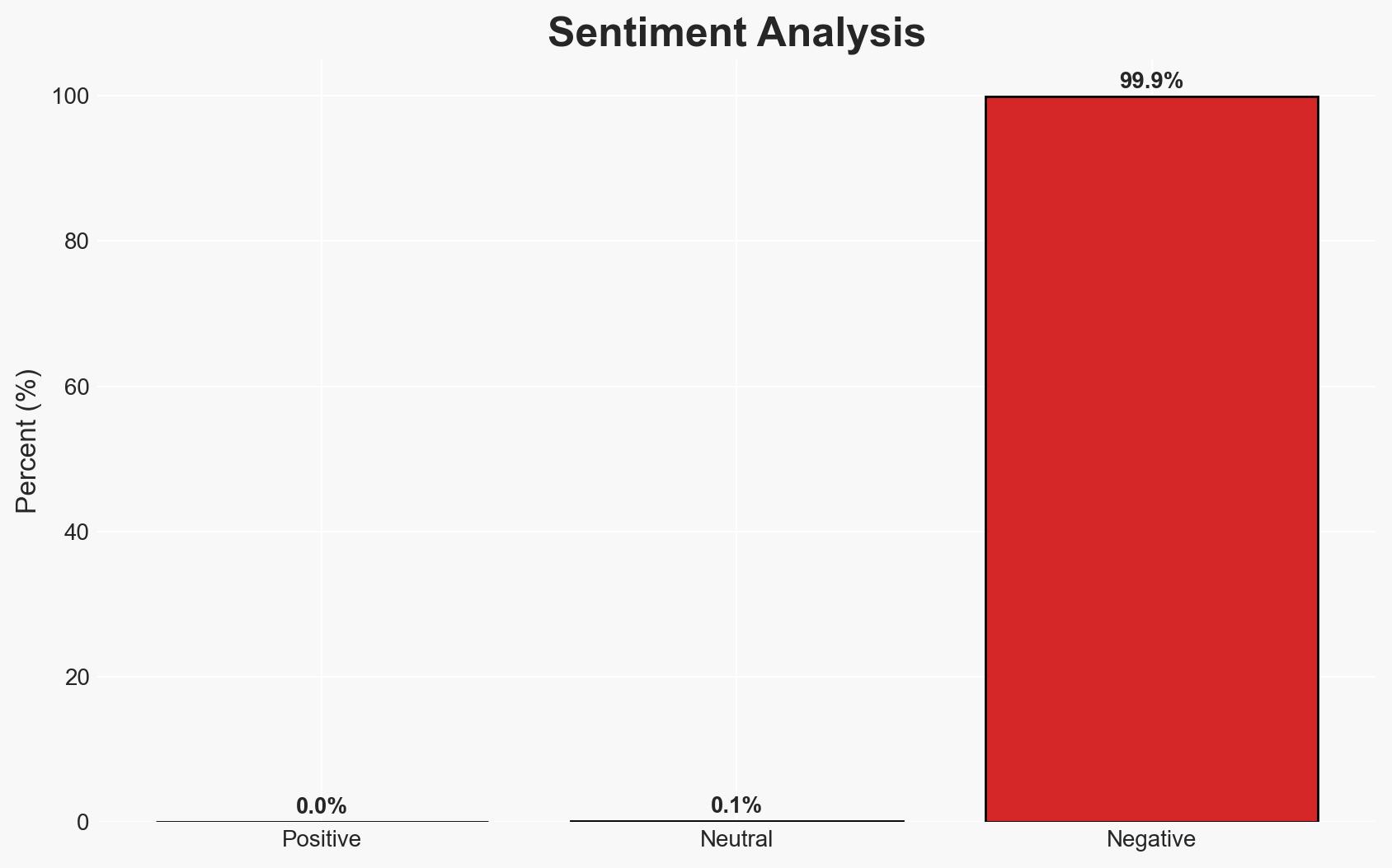
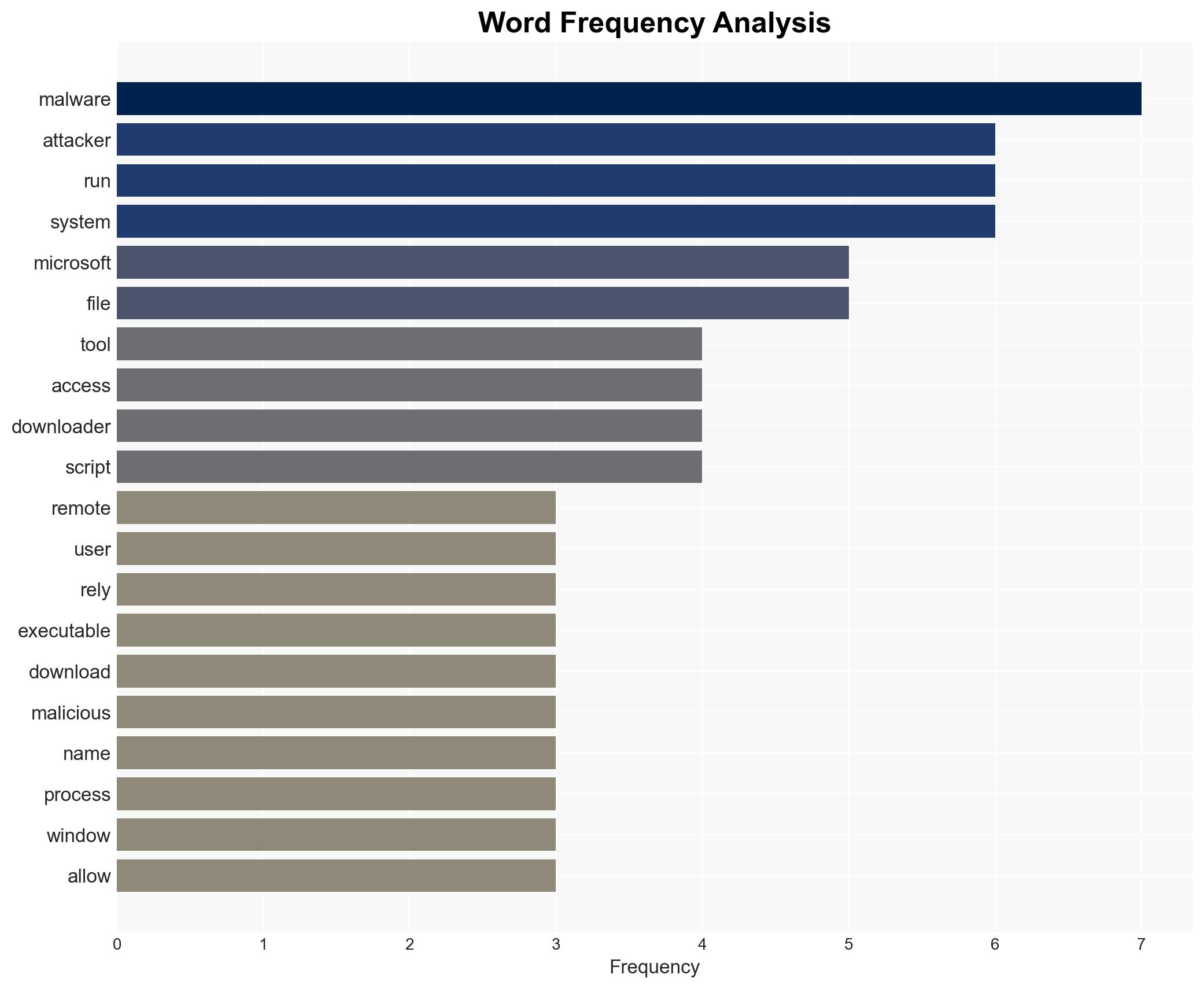
Attackers are distributing fake gaming utilities to install a remote access trojan (RAT) on Windows systems, leveraging legitimate system tools to evade detection. This campaign primarily affects users downloading gaming tools from unverified sources. The most likely hypothesis is that this is a financially motivated cybercrime operation. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The campaign is a financially motivated cybercrime operation aimed at gaining unauthorized access to systems for data theft or extortion. This is supported by the use of RATs and the focus on gaming communities, which are often targeted for financial gain. However, the specific financial mechanisms remain unclear.
- Hypothesis B: The campaign could be a state-sponsored operation aimed at gathering intelligence or conducting espionage. The use of sophisticated techniques such as LOLBins suggests a high level of expertise. However, there is no direct evidence linking this to state actors.
- Assessment: Hypothesis A is currently better supported due to the typical targeting of gaming communities for financial exploitation. Indicators such as the use of RATs and the focus on evading detection align with criminal activities. Further evidence of financial transactions or ransom demands could solidify this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The attackers are primarily motivated by financial gain; the use of LOLBins is intended to evade detection; gaming communities are the primary target.
- Information Gaps: Specific financial impacts or transactions resulting from the campaign; identification of the actors behind the operation; the full scope of affected users.
- Bias & Deception Risks: Potential bias in assuming financial motivation without direct evidence; reliance on Microsoft as the sole source may introduce bias; possibility of false flag operations by state actors.
4. Implications and Strategic Risks
This development could lead to increased targeting of gaming communities and a rise in similar cybercrime campaigns. The use of LOLBins may become more prevalent, complicating detection efforts.
- Political / Geopolitical: Limited direct impact, but potential for increased tensions if state-sponsored involvement is suspected.
- Security / Counter-Terrorism: Increased need for cybersecurity measures and awareness in gaming communities; potential for broader exploitation of LOLBins.
- Cyber / Information Space: Highlights vulnerabilities in user behavior and the effectiveness of social engineering tactics.
- Economic / Social: Potential economic impact on individuals and businesses through data theft or extortion; erosion of trust in digital platforms.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor outbound traffic for suspicious activity; block connections to identified malicious domains; review and remove suspicious Microsoft Defender exclusions and scheduled tasks.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for threat intelligence sharing; enhance user education on the risks of downloading unverified software.
- Scenario Outlook:
- Best: Effective mitigation reduces the campaign’s impact, and no further incidents occur.
- Worst: Campaign expands, affecting a broader range of users and leading to significant financial losses.
- Most-Likely: Continued targeting of gaming communities with periodic disruptions and moderate financial impacts.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
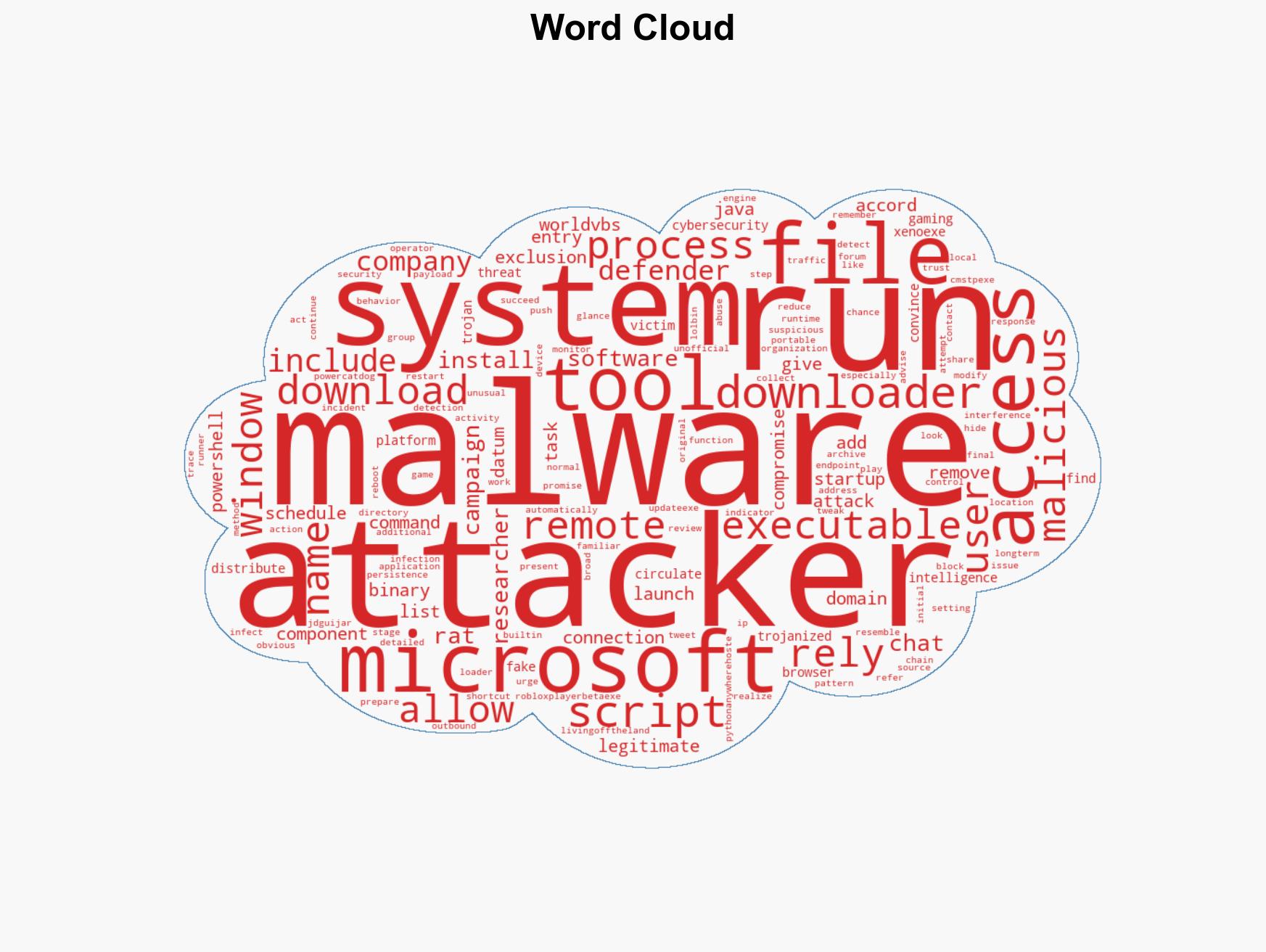
cybersecurity, remote access trojan, financial cybercrime, gaming community, LOLBins, Microsoft Defender, social engineering
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us