Microsoft Alerts Windows Users to WhatsApp Attachment Exploit in New Social Engineering Campaign
Published on: 2026-04-01
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: WhatsApp on Windows users targeted in new campaign warns Microsoft
1. BLUF (Bottom Line Up Front)
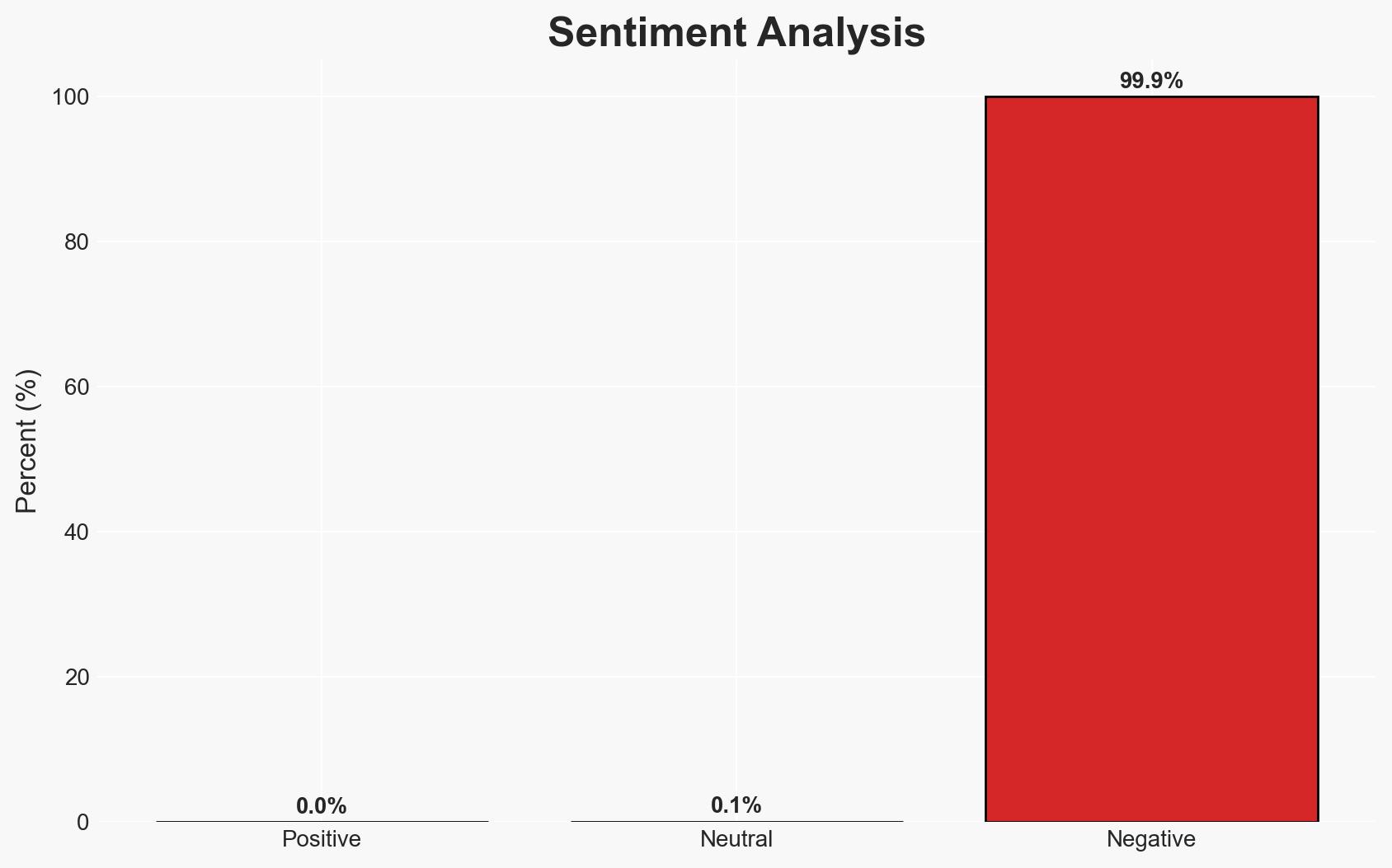
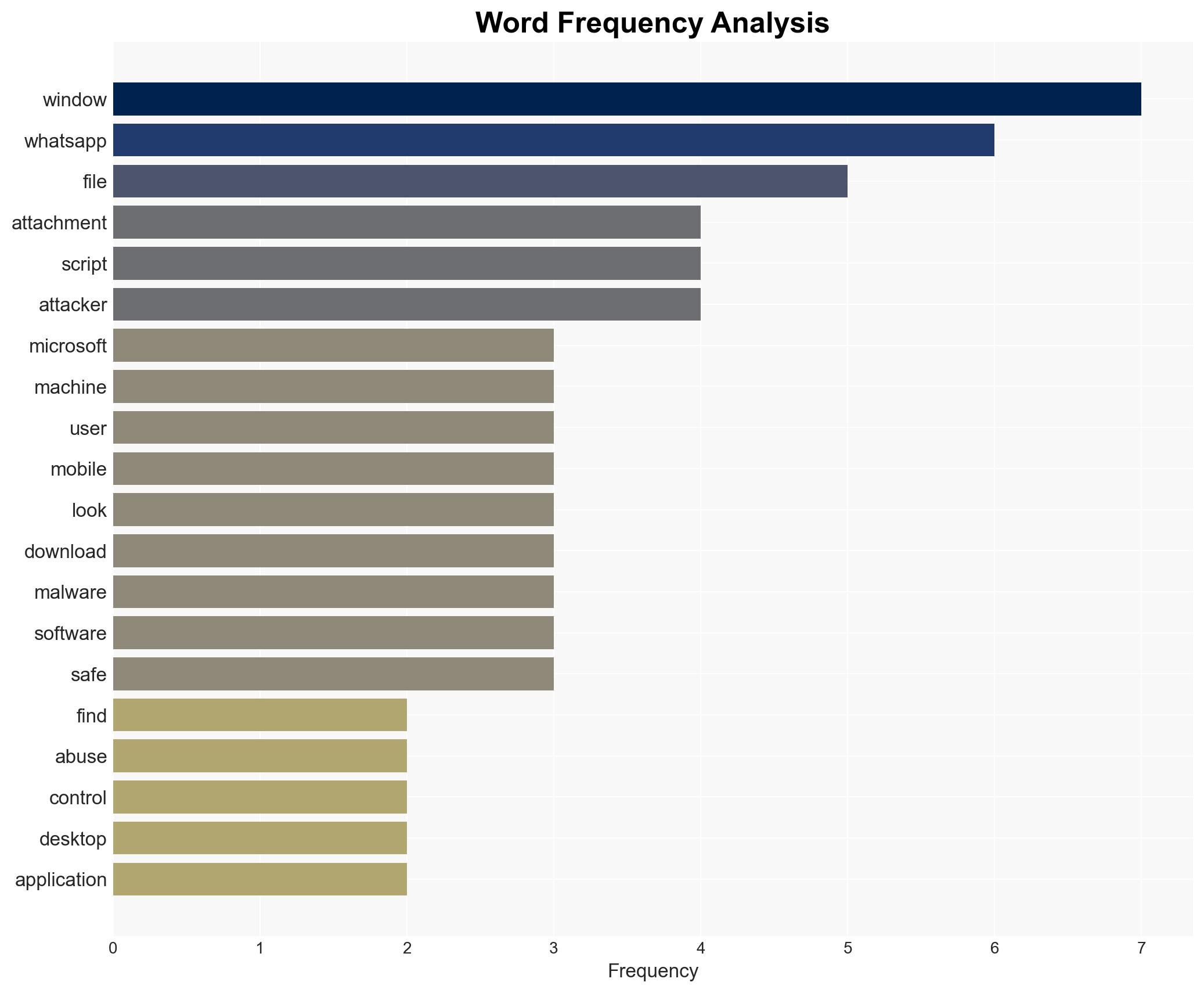
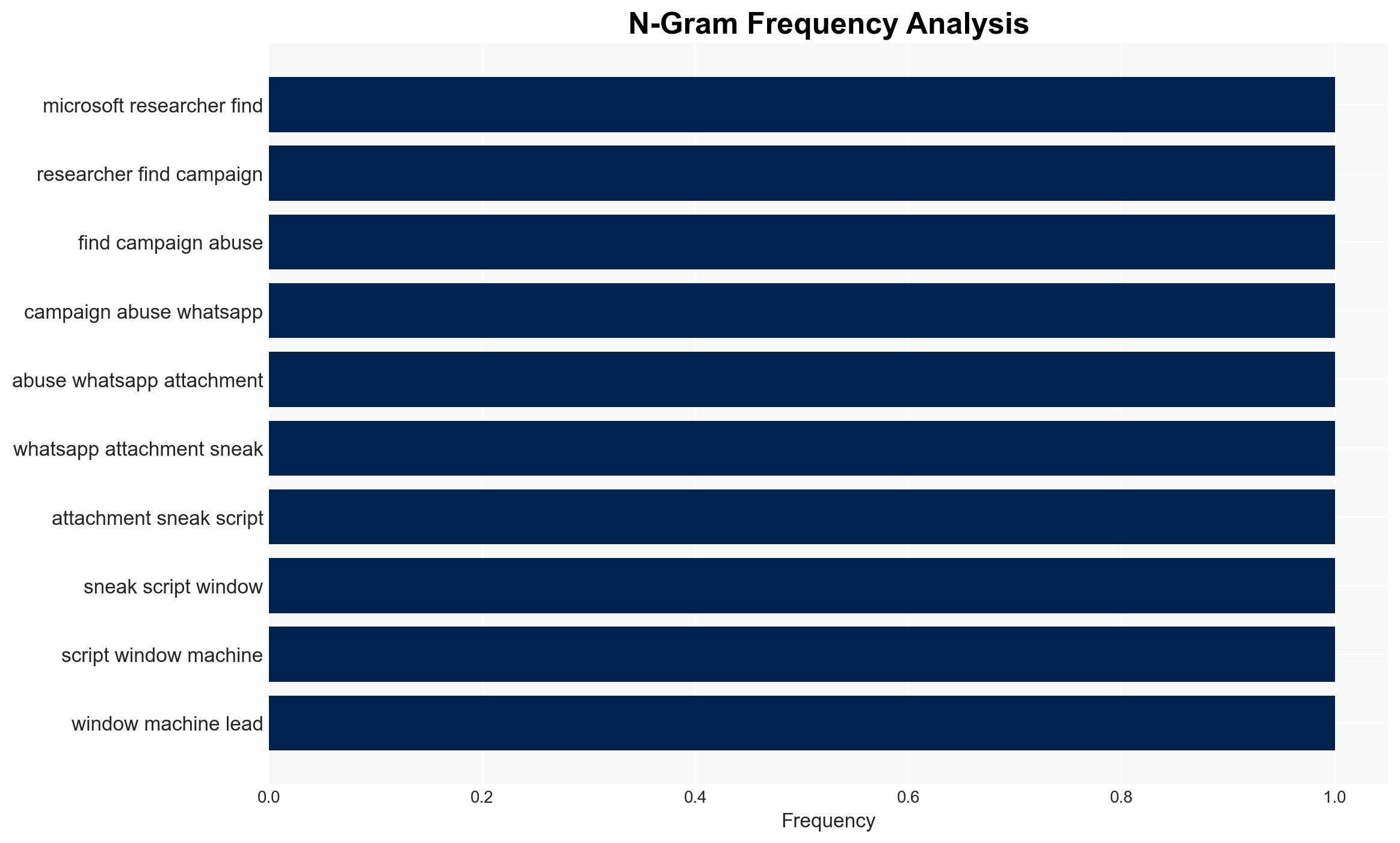
Microsoft has identified a cyber campaign targeting WhatsApp users on Windows, exploiting social engineering to gain remote control over systems. The campaign utilizes legitimate tools in a “living off the land” technique, complicating detection. This threat predominantly affects users of WhatsApp’s desktop application on Windows. Overall confidence in this assessment is moderate, given the reliance on social engineering and existing security measures.
2. Competing Hypotheses
- Hypothesis A: The campaign is primarily opportunistic, targeting a wide range of users indiscriminately to maximize potential control over systems. This is supported by the use of common cloud services to mask malicious activity. However, the specific targeting of WhatsApp desktop users suggests a more focused approach, which contradicts a purely opportunistic strategy.
- Hypothesis B: The campaign is a targeted operation aimed at specific individuals or organizations, leveraging WhatsApp’s desktop application as a vector due to its lower adoption rate and potentially less stringent security practices. This hypothesis is supported by the sophistication of the attack and the use of social engineering, which typically requires more effort and planning.
- Assessment: Hypothesis B is currently better supported, as the complexity and targeted nature of the attack suggest a deliberate operation rather than a broad, indiscriminate campaign. Indicators that could shift this judgment include evidence of widespread, random targeting or a significant increase in attack volume.
3. Key Assumptions and Red Flags
- Assumptions: The attackers have a moderate to high level of technical capability. WhatsApp desktop users are less vigilant about security compared to mobile users. The use of legitimate tools will continue to evade detection by standard security measures.
- Information Gaps: Specific identities or motivations of the attackers remain unknown. The full scope and scale of the campaign are unclear, including the number of affected users.
- Bias & Deception Risks: There is a risk of confirmation bias in assuming targeted attacks without broader data. The use of legitimate cloud services could be a deliberate deception tactic to obscure the attack’s origin.
4. Implications and Strategic Risks
This development could lead to increased scrutiny of WhatsApp’s desktop application security and broader concerns about the security of desktop applications synchronized with mobile devices.
- Political / Geopolitical: Potential for increased regulatory pressure on Meta and similar tech companies to enhance desktop application security.
- Security / Counter-Terrorism: The campaign could inspire similar tactics in other cyber operations, increasing the threat landscape.
- Cyber / Information Space: Highlights the vulnerability of using legitimate tools for malicious purposes, complicating threat detection and response.
- Economic / Social: Could lead to decreased trust in desktop applications, impacting user engagement and potentially affecting Meta’s market position.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of WhatsApp desktop application activity, particularly focusing on unusual network traffic patterns. Educate users on recognizing and avoiding social engineering tactics.
- Medium-Term Posture (1–12 months): Develop partnerships with cloud service providers to identify and mitigate misuse of their platforms. Invest in advanced detection capabilities for LOTL techniques.
- Scenario Outlook:
- Best Case: Increased awareness and improved security measures significantly reduce the effectiveness of such campaigns.
- Worst Case: Attackers adapt and scale operations, leading to widespread compromise of sensitive systems.
- Most-Likely: Continued targeted attacks with moderate success, prompting ongoing security enhancements and user education.
6. Key Individuals and Entities
- Microsoft (researchers and security teams)
- Meta (WhatsApp developers and security teams)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
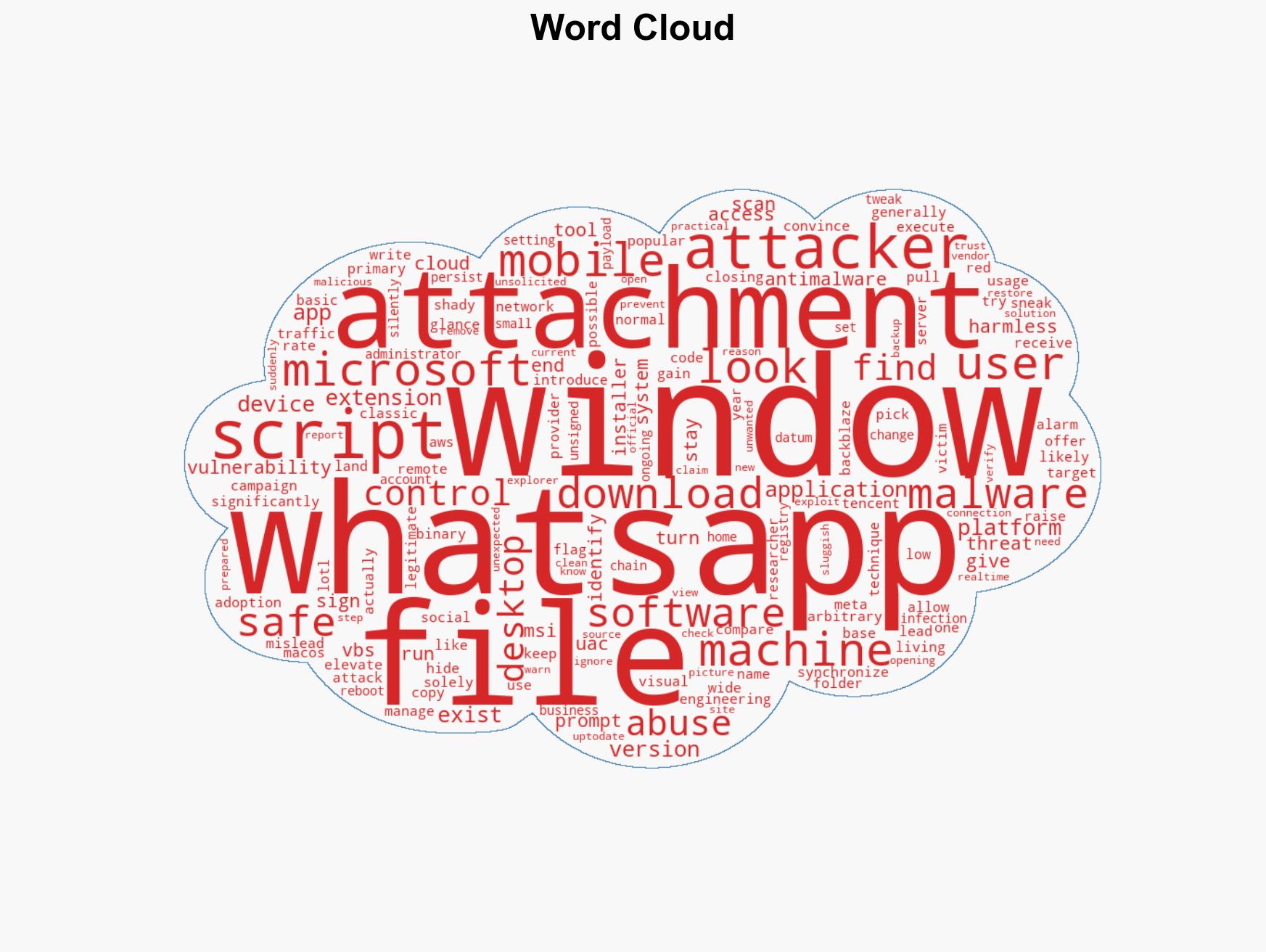
cybersecurity, social engineering, living off the land, WhatsApp, Windows security, cloud services, remote access
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us