Microsoft uses AI to find flaws in GRUB2 U-Boot Barebox bootloaders – BleepingComputer
Published on: 2025-03-31
Intelligence Report: Microsoft uses AI to find flaws in GRUB2 U-Boot Barebox bootloaders – BleepingComputer
1. BLUF (Bottom Line Up Front)
Microsoft has utilized its AI-powered Security Copilot to identify vulnerabilities in GRUB2, U-Boot, and Barebox bootloaders. These vulnerabilities include buffer overflows and cryptographic flaws that could potentially allow attackers to bypass security mechanisms such as UEFI Secure Boot. The discovery underscores the importance of AI in accelerating vulnerability detection and highlights the need for timely security updates to mitigate these risks.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
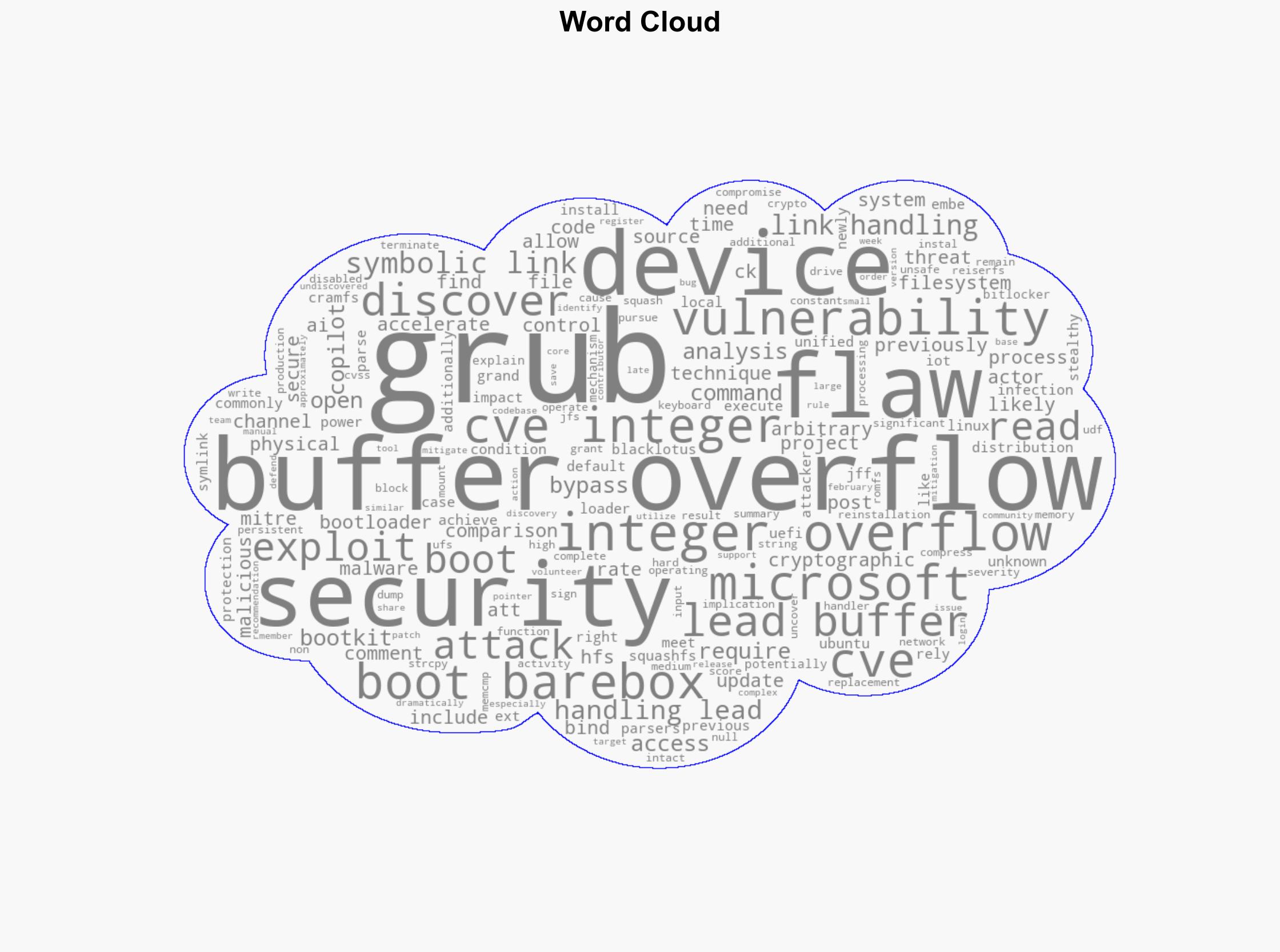
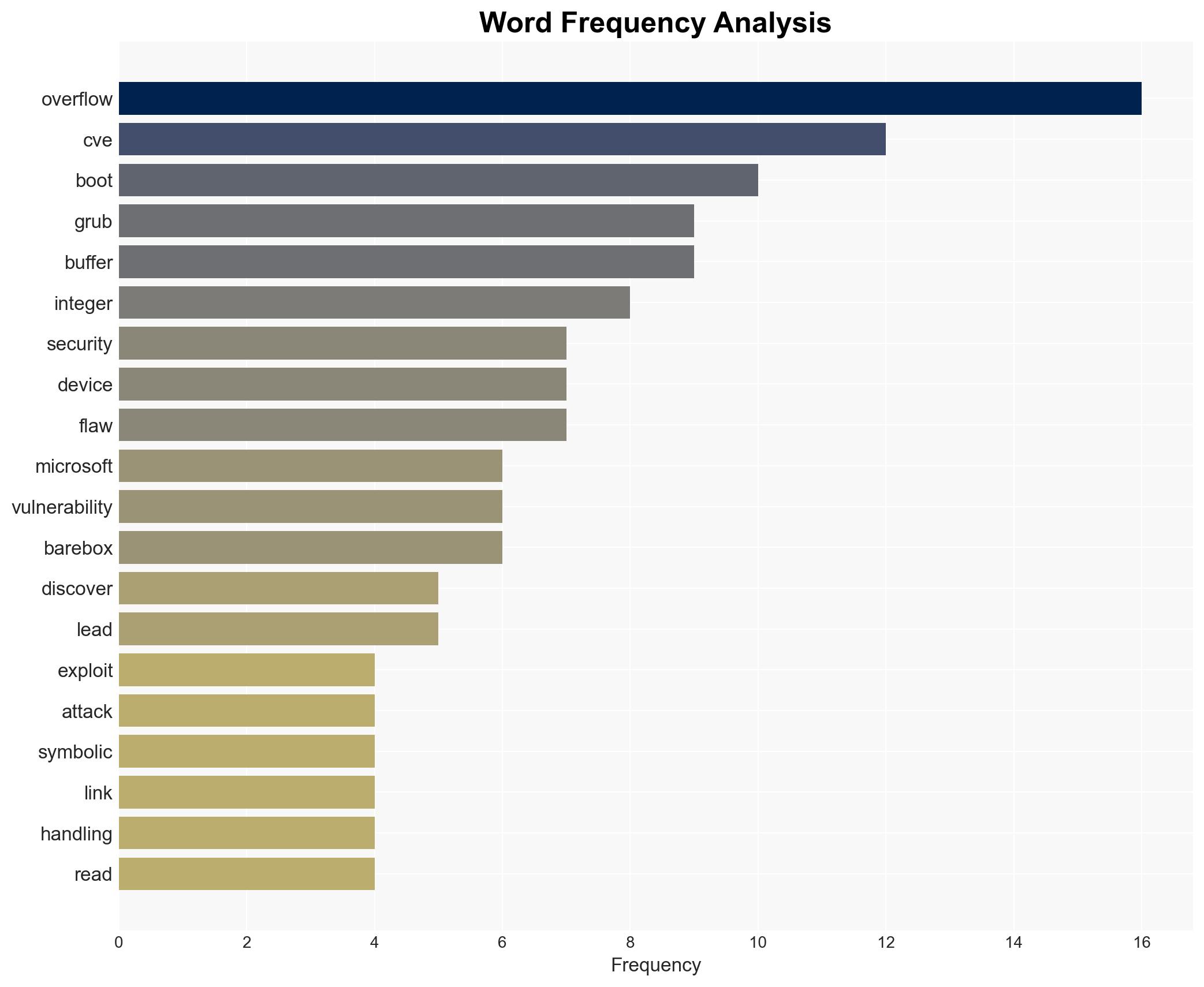
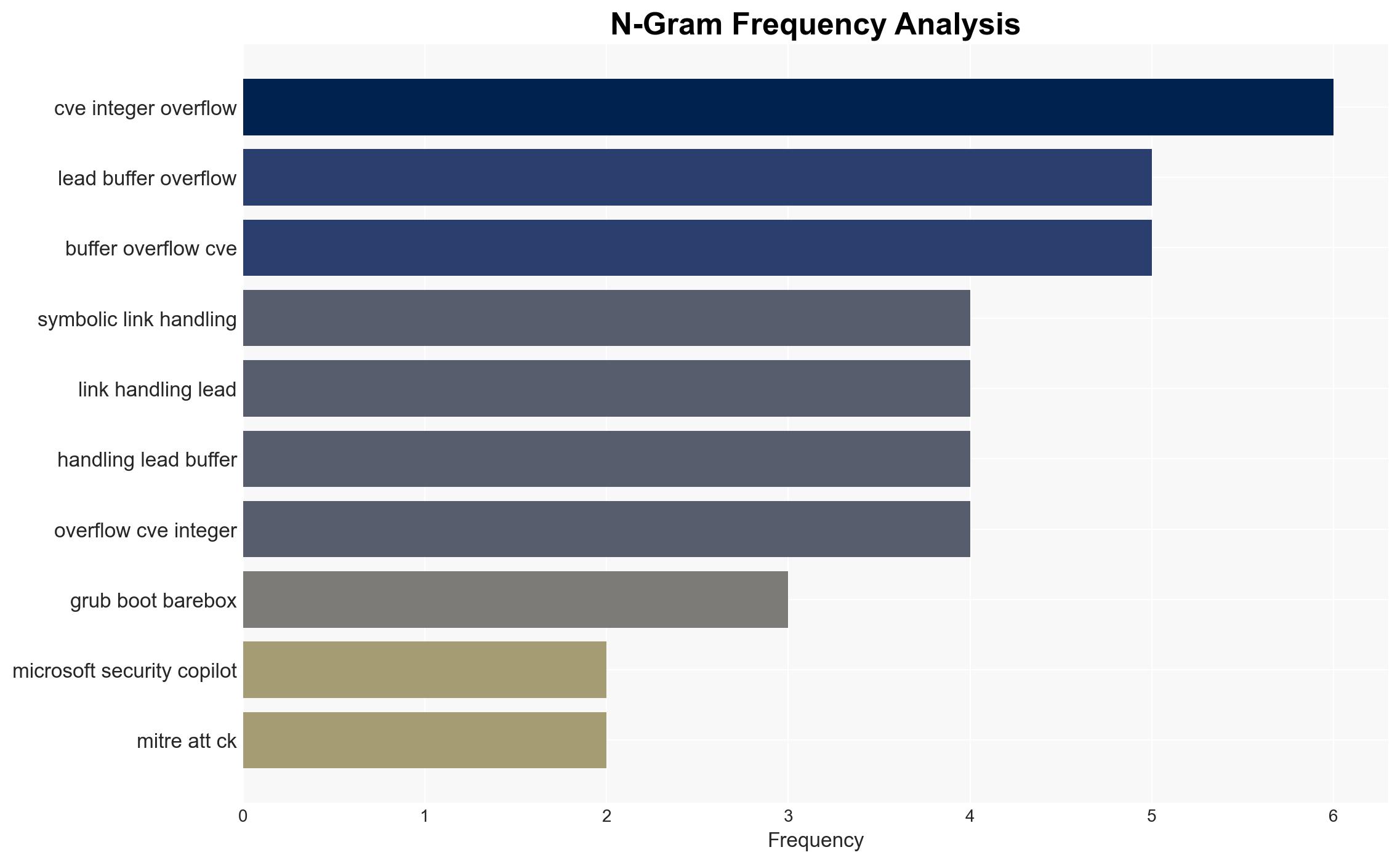
Microsoft’s AI identified several vulnerabilities in open-source bootloaders, including GRUB2 and Barebox. Key vulnerabilities include:
- Buffer overflow in filesystem parsers and command channels.
- Cryptographic comparison flaws in GRUB’s cryptographic functions.
- Multiple integer overflows affecting symbolic link handling and file reading.
These vulnerabilities could allow attackers with physical access to devices to execute arbitrary code, potentially installing stealthy bootkits that bypass security mechanisms like BitLocker.
3. Implications and Strategic Risks
The identified vulnerabilities pose significant risks to devices relying on UEFI Secure Boot, particularly in IoT environments. Exploitation could lead to persistent malware infections, compromising entire networks. The vulnerabilities’ presence in widely used open-source projects increases the risk of widespread exploitation, affecting national security, regional stability, and economic interests.
4. Recommendations and Outlook
Recommendations:
- Accelerate the deployment of security patches for affected bootloaders, prioritizing systems with high exposure.
- Enhance collaboration between open-source communities and security experts to improve vulnerability management.
- Implement advanced monitoring and response mechanisms to detect and mitigate exploitation attempts.
Outlook:
Best-case scenario: Rapid patch deployment mitigates risks, and increased collaboration strengthens open-source security.
Worst-case scenario: Delayed patching leads to widespread exploitation, resulting in significant security breaches.
Most likely outcome: Gradual patch adoption reduces immediate risks, but ongoing vigilance is required to address emerging threats.
5. Key Individuals and Entities
The report mentions significant individuals and organizations but does not provide any roles or affiliations. Key entities include:
- Microsoft
- GRUB2
- Barebox
- U-Boot