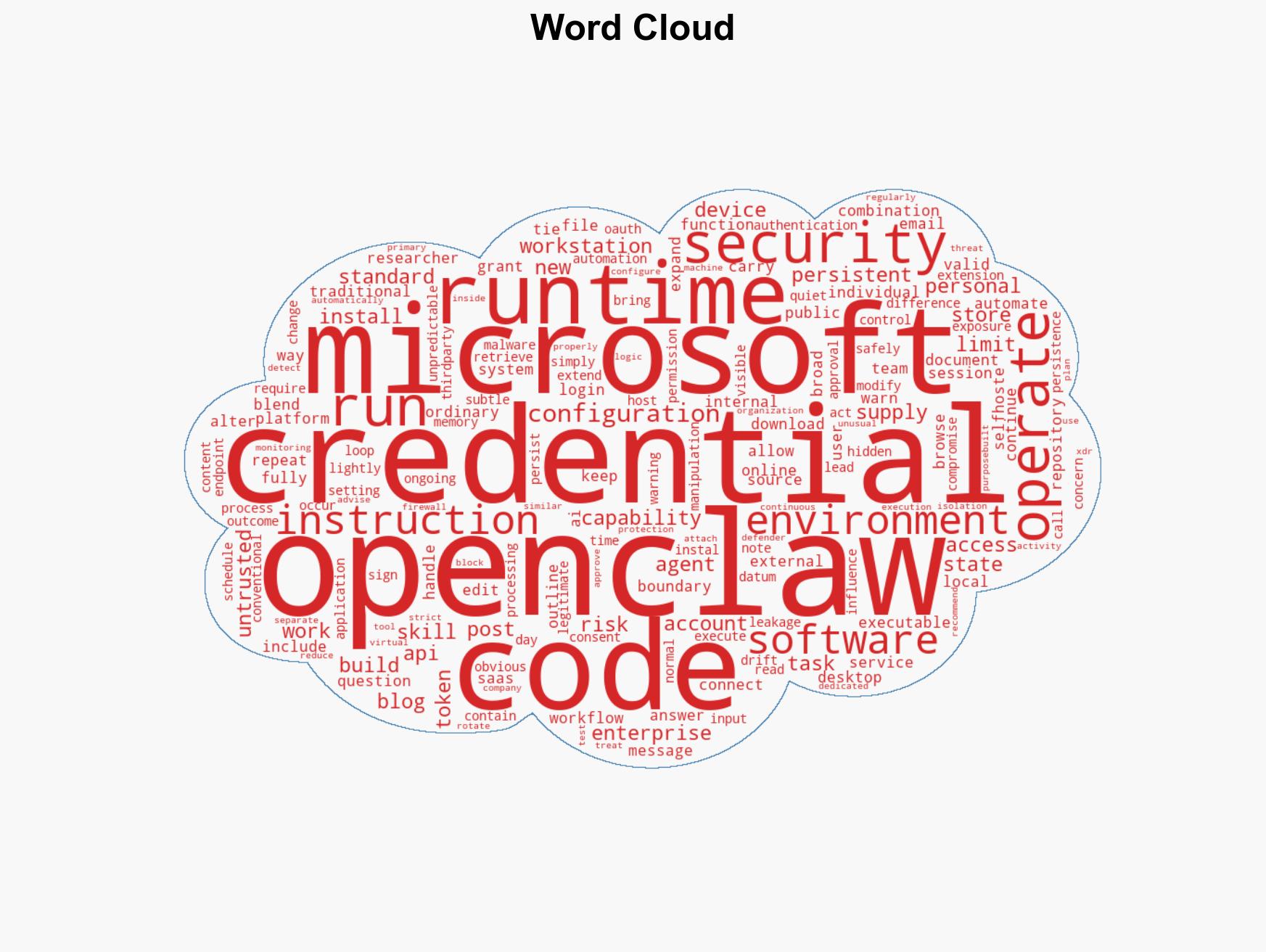
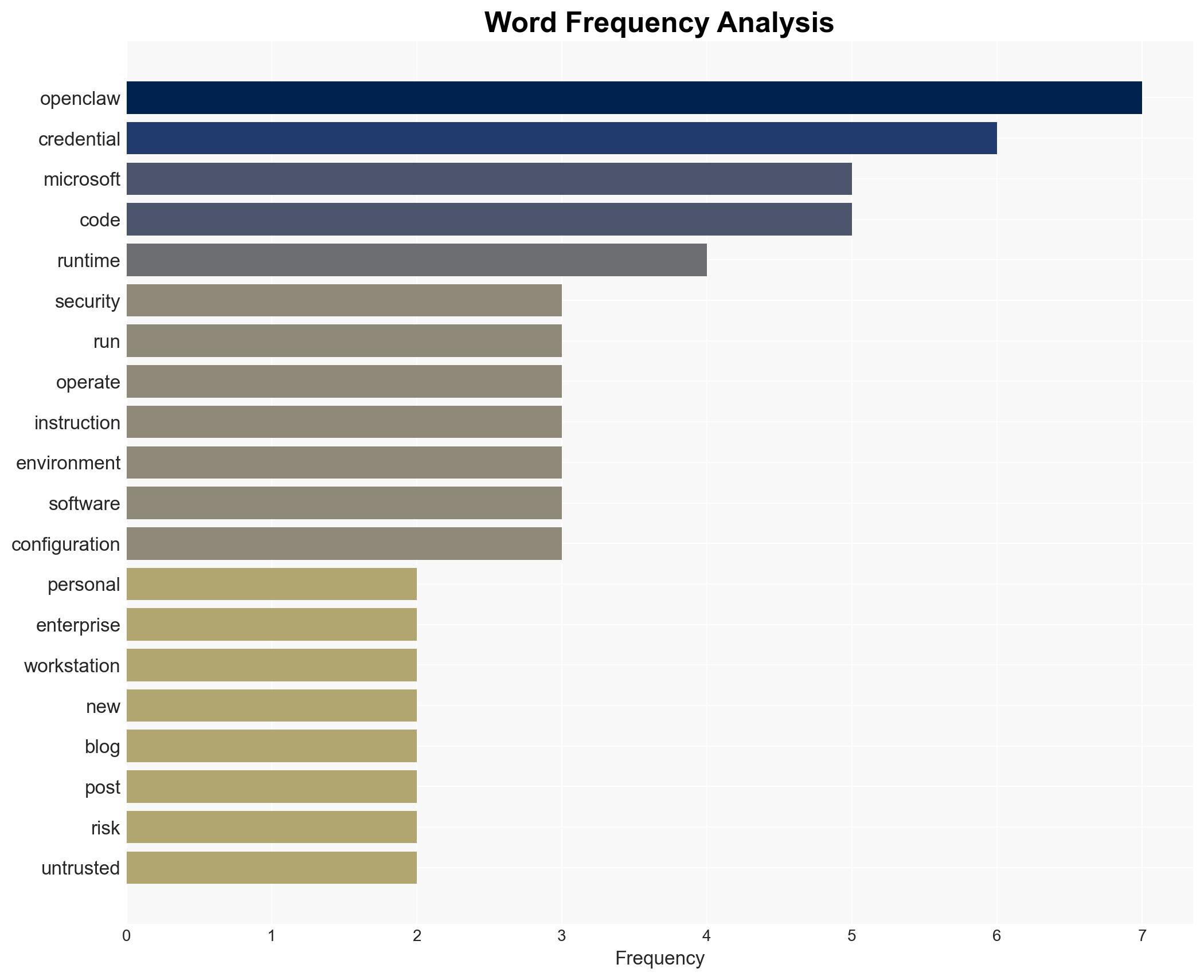
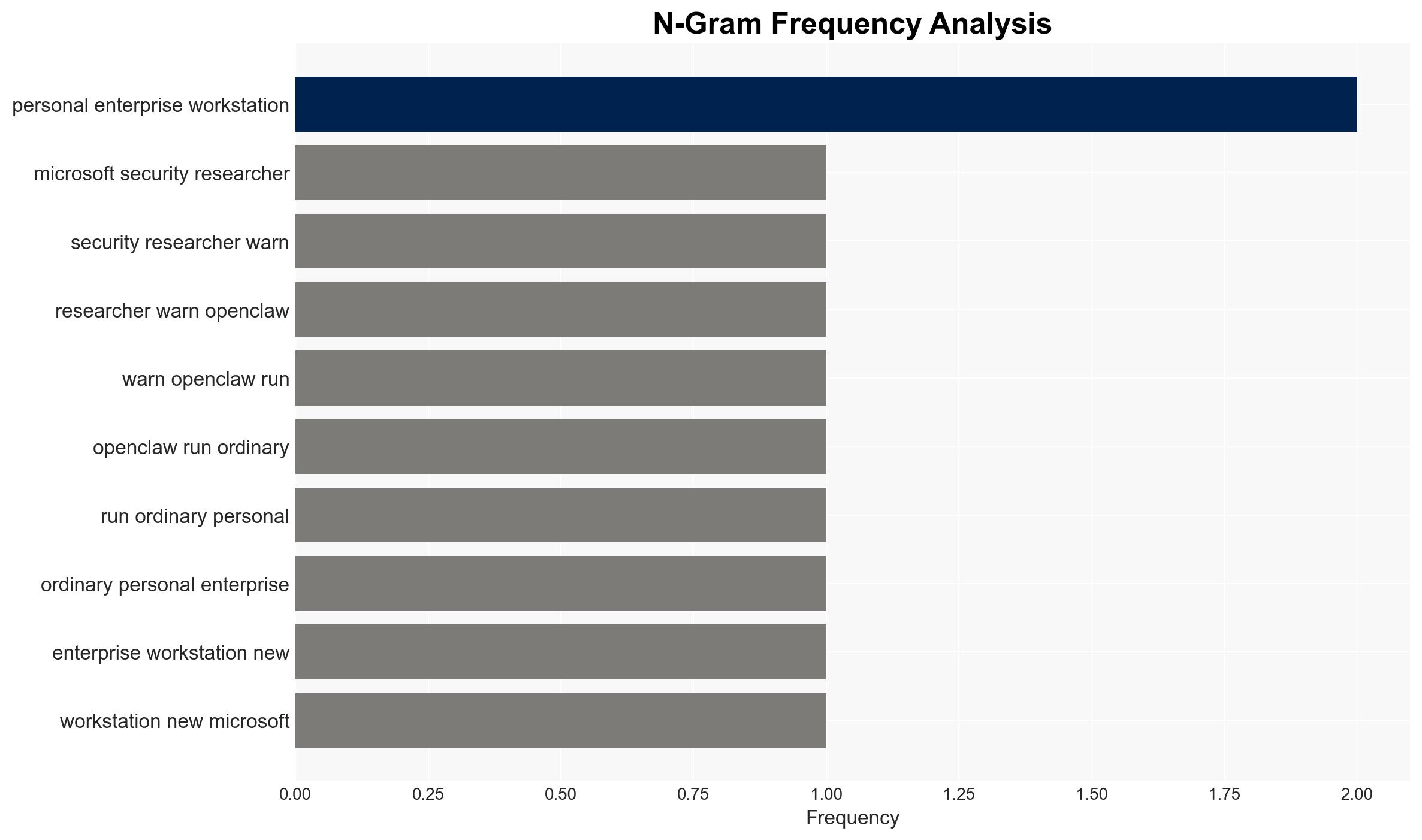
Microsoft warns against using OpenClaw on standard workstations due to significant security risks.
Published on: 2026-02-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Microsoft says OpenClaw is not appropriate to run on a standard personal or enterprise workstation so should you be worried
1. BLUF (Bottom Line Up Front)
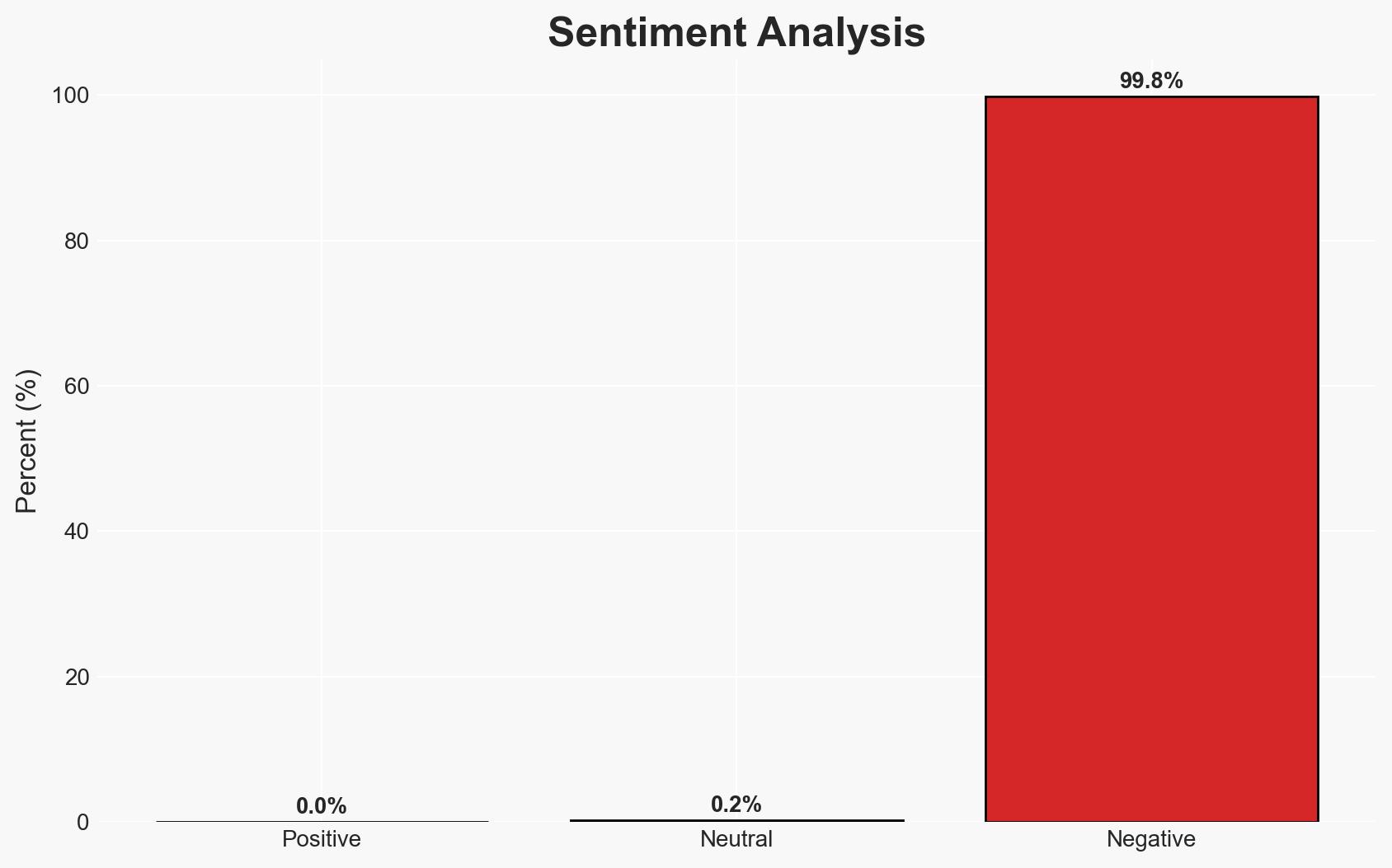
OpenClaw poses significant security risks when operated on standard personal or enterprise workstations due to its ability to execute untrusted code with persistent credentials. This risk primarily affects organizations using OpenClaw without proper isolation measures. The most likely hypothesis is that OpenClaw’s integration into standard environments could lead to data breaches and unauthorized access. Confidence in this assessment is moderate, given the potential for unknown variables in OpenClaw’s operation.
2. Competing Hypotheses
- Hypothesis A: OpenClaw’s operation on standard workstations will lead to increased security vulnerabilities due to its ability to execute untrusted code and maintain persistent credentials. Supporting evidence includes Microsoft’s warning and the inherent risks of untrusted code execution. Key uncertainties include the extent of OpenClaw’s deployment and the effectiveness of existing security measures.
- Hypothesis B: OpenClaw can be safely integrated into standard workstations if appropriate isolation and security measures are implemented. This hypothesis is supported by Microsoft’s recommendations for strict isolation and credential management. Contradicting evidence includes the complexity and potential cost of implementing these measures effectively.
- Assessment: Hypothesis A is currently better supported due to the inherent risks and challenges in implementing effective isolation and security measures. Indicators that could shift this judgment include widespread successful implementation of Microsoft’s recommended security practices.
3. Key Assumptions and Red Flags
- Assumptions: OpenClaw’s current operational model remains unchanged; organizations may not fully implement recommended security measures; existing endpoint protections are insufficient against OpenClaw’s capabilities.
- Information Gaps: Detailed data on OpenClaw’s deployment scale and specific incidents of security breaches caused by its operation.
- Bias & Deception Risks: Potential bias in Microsoft’s assessment due to vested interests in promoting alternative solutions; lack of independent verification of OpenClaw’s risks.
4. Implications and Strategic Risks
The integration of OpenClaw into standard workstations could lead to significant security challenges, necessitating a reevaluation of current cybersecurity frameworks.
- Political / Geopolitical: Increased regulatory scrutiny on AI-driven automation tools and potential international collaboration on cybersecurity standards.
- Security / Counter-Terrorism: Potential exploitation by malicious actors to gain unauthorized access to sensitive information.
- Cyber / Information Space: Heightened risk of data breaches and information manipulation through compromised systems.
- Economic / Social: Increased costs for organizations to implement necessary security measures; potential reputational damage from breaches.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a risk assessment of OpenClaw deployment; implement isolation measures as recommended by Microsoft; monitor for unusual activity.
- Medium-Term Posture (1–12 months): Develop and enforce comprehensive security policies for AI tool integration; invest in training for cybersecurity personnel.
- Scenario Outlook:
- Best: Successful implementation of security measures mitigates risks.
- Worst: Widespread breaches lead to significant data loss and regulatory action.
- Most-Likely: Gradual improvement in security practices with occasional incidents.
6. Key Individuals and Entities
- Microsoft Security Researchers
- OpenClaw Development Team
- Organizations deploying OpenClaw
- Cybersecurity Regulatory Bodies
7. Thematic Tags
cybersecurity, AI integration, data protection, risk management, enterprise security, automation risks
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us