Mitigating the Threat of POS Malware in an Increasingly Cashless UK Business Landscape
Published on: 2026-03-10
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Protecting your business from POS malware attacks
1. BLUF (Bottom Line Up Front)
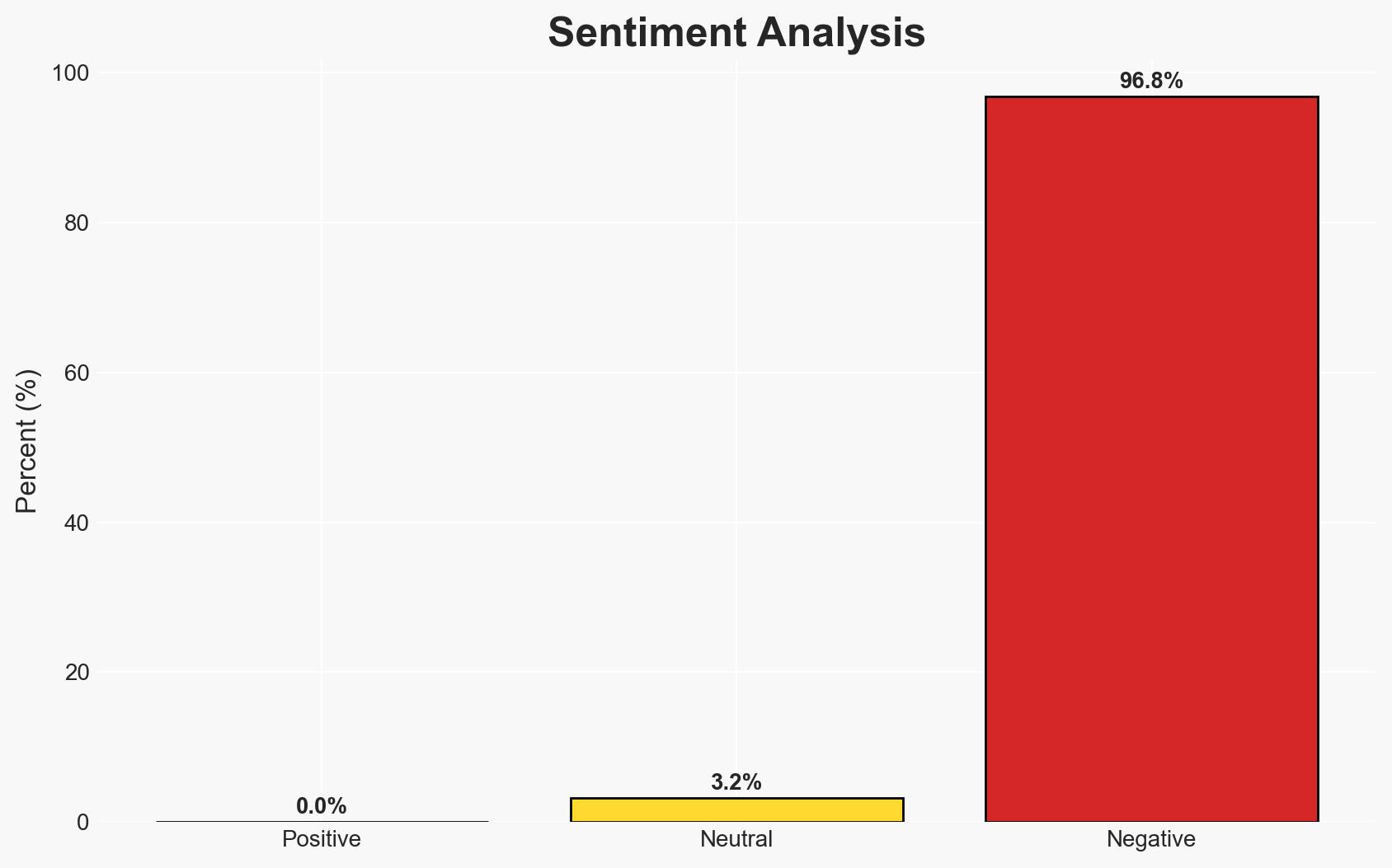
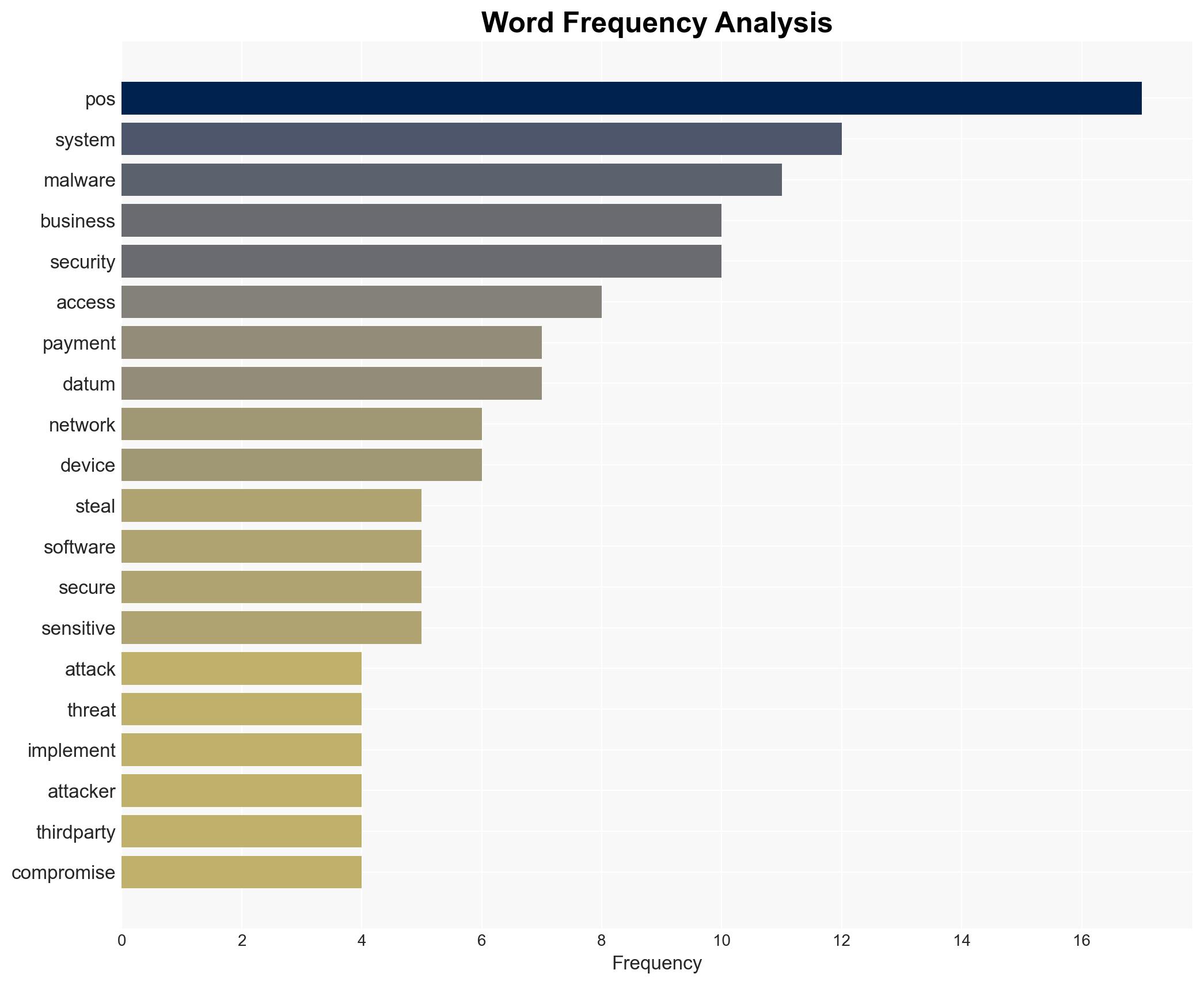
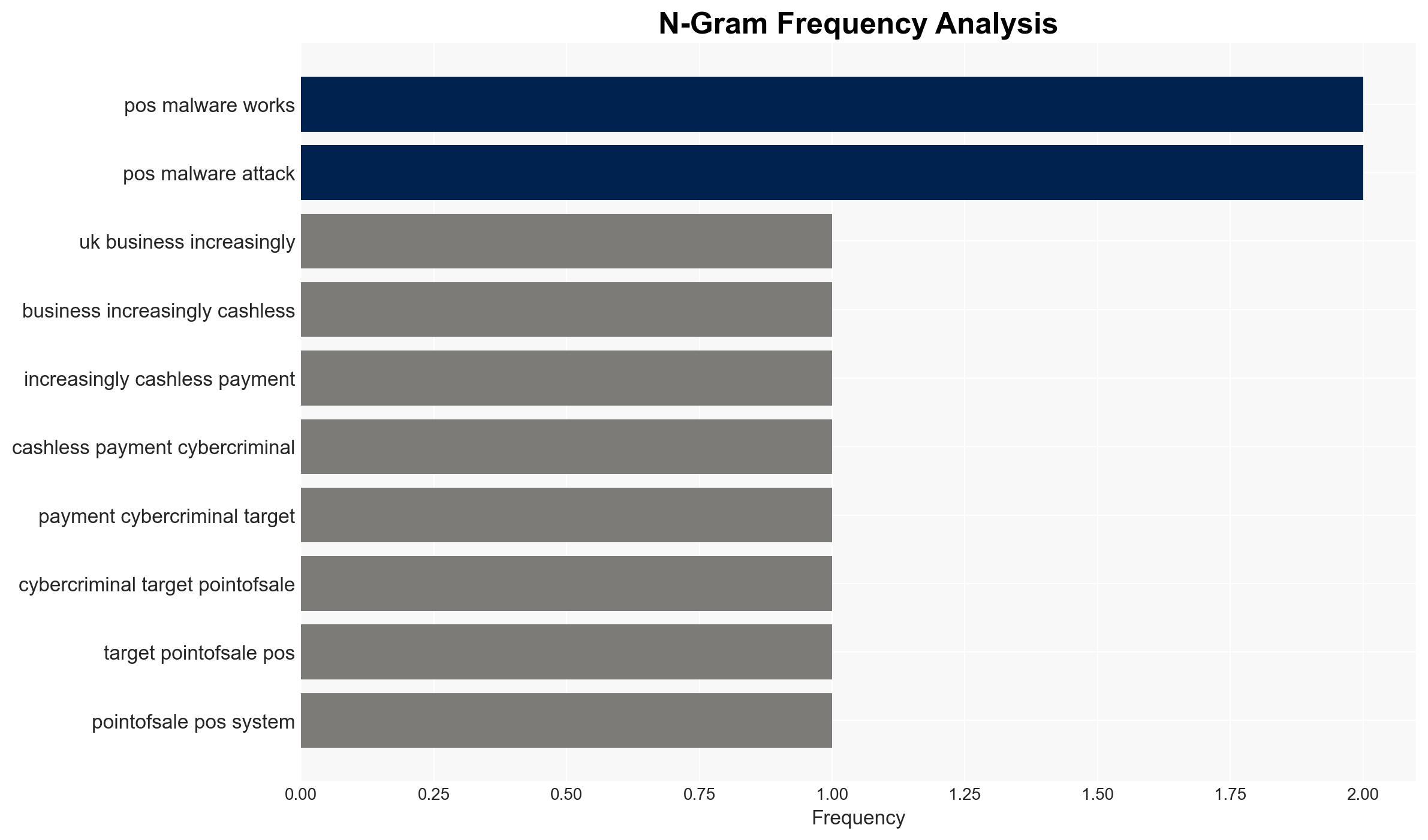
The increase in cashless transactions in the UK has led to a rise in POS malware attacks, with £600 million stolen in the first half of 2025. Small to mid-sized businesses are particularly vulnerable due to their reliance on POS systems. The most likely hypothesis is that cybercriminals will continue to exploit these systems unless robust security measures are implemented. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: Cybercriminals are primarily targeting POS systems due to their vulnerabilities and the high volume of transactions they process. This is supported by the reported increase in fraud and the variety of techniques used to exploit these systems. However, the specific motivations and capabilities of the attackers remain uncertain.
- Hypothesis B: The rise in POS malware attacks is a temporary trend driven by a surge in opportunistic attacks rather than a sustained strategic focus by cybercriminals. This is contradicted by the consistent increase in fraud and the sophistication of the malware used.
- Assessment: Hypothesis A is currently better supported due to the documented increase in fraud and the variety of sophisticated techniques employed. Key indicators that could shift this judgment include changes in attack patterns or a significant decrease in reported incidents.
3. Key Assumptions and Red Flags
- Assumptions: POS systems will remain a primary target for cybercriminals; businesses will continue to adopt cashless payment systems; current security measures are insufficient.
- Information Gaps: Detailed profiles of the attackers and their networks; specific vulnerabilities in POS systems that are being exploited.
- Bias & Deception Risks: Potential bias in reporting from businesses reluctant to disclose breaches; deception by attackers using false flags to mislead attribution efforts.
4. Implications and Strategic Risks
The ongoing exploitation of POS systems could lead to increased financial losses and reputational damage for businesses, potentially affecting consumer trust in cashless payments.
- Political / Geopolitical: Increased pressure on regulatory bodies to enforce stricter cybersecurity standards.
- Security / Counter-Terrorism: Potential for cybercriminals to collaborate with terrorist organizations, leveraging stolen data for funding.
- Cyber / Information Space: Escalation in cyber warfare tactics, with POS systems as a focal point for attacks.
- Economic / Social: Potential decline in consumer confidence in digital transactions, impacting economic growth.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct comprehensive security audits of POS systems; enhance monitoring for unusual activity; educate staff on cybersecurity best practices.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms; invest in advanced threat detection technologies; implement regular security updates and patches.
- Scenario Outlook:
- Best: Significant reduction in POS malware incidents due to improved security measures.
- Worst: Continued increase in attacks leading to widespread financial and reputational damage.
- Most-Likely: Gradual improvement in security posture with intermittent breaches as businesses adapt.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
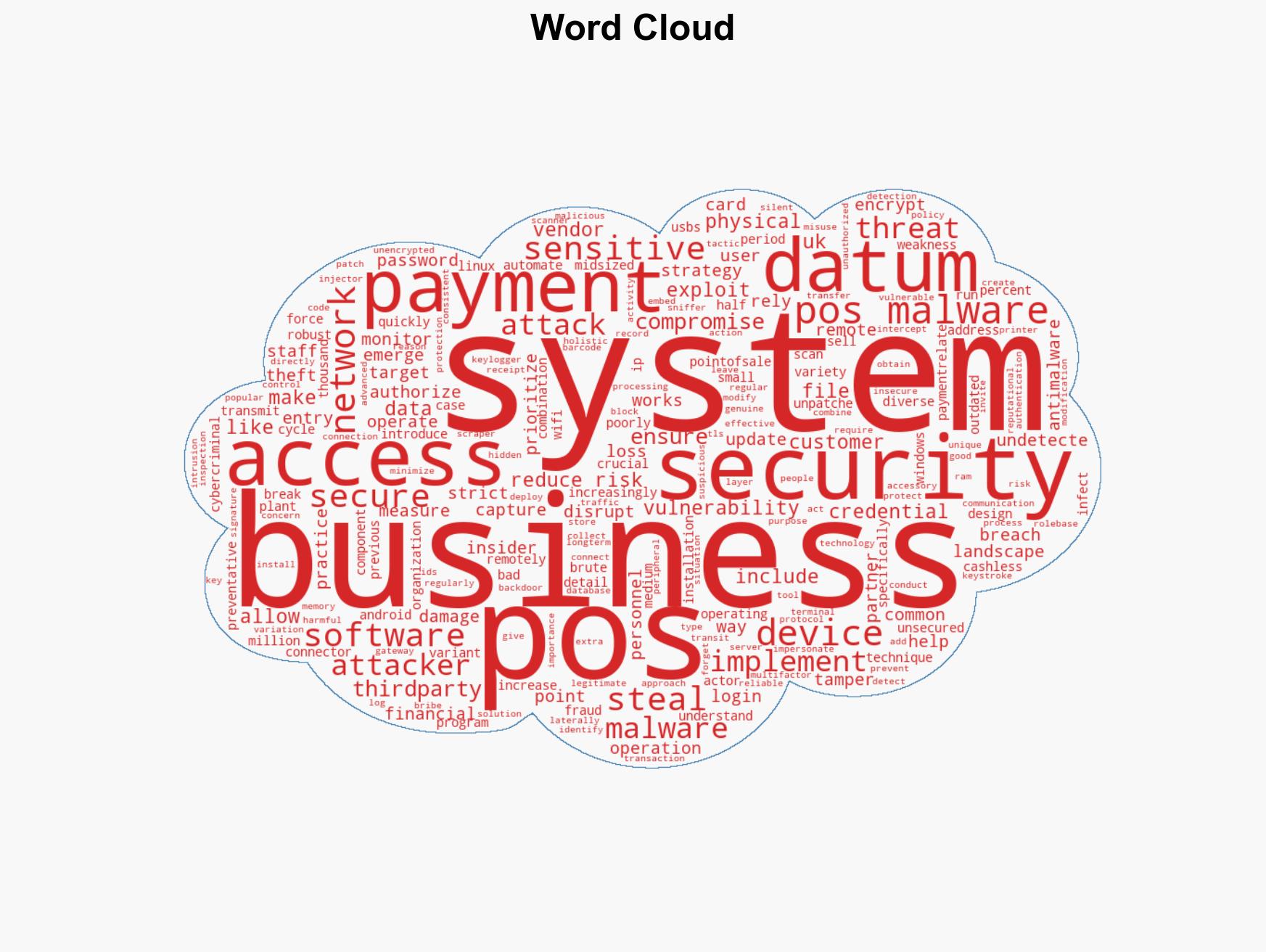
cybersecurity, POS malware, financial fraud, cashless payments, small businesses, cybercrime, data protection
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us