Mitigating Zero-Day Risks: Strategies for Effective Attack Surface Management
Published on: 2026-03-10
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: The Zero-Day Scramble is Avoidable A Guide to Attack Surface Reduction
1. BLUF (Bottom Line Up Front)
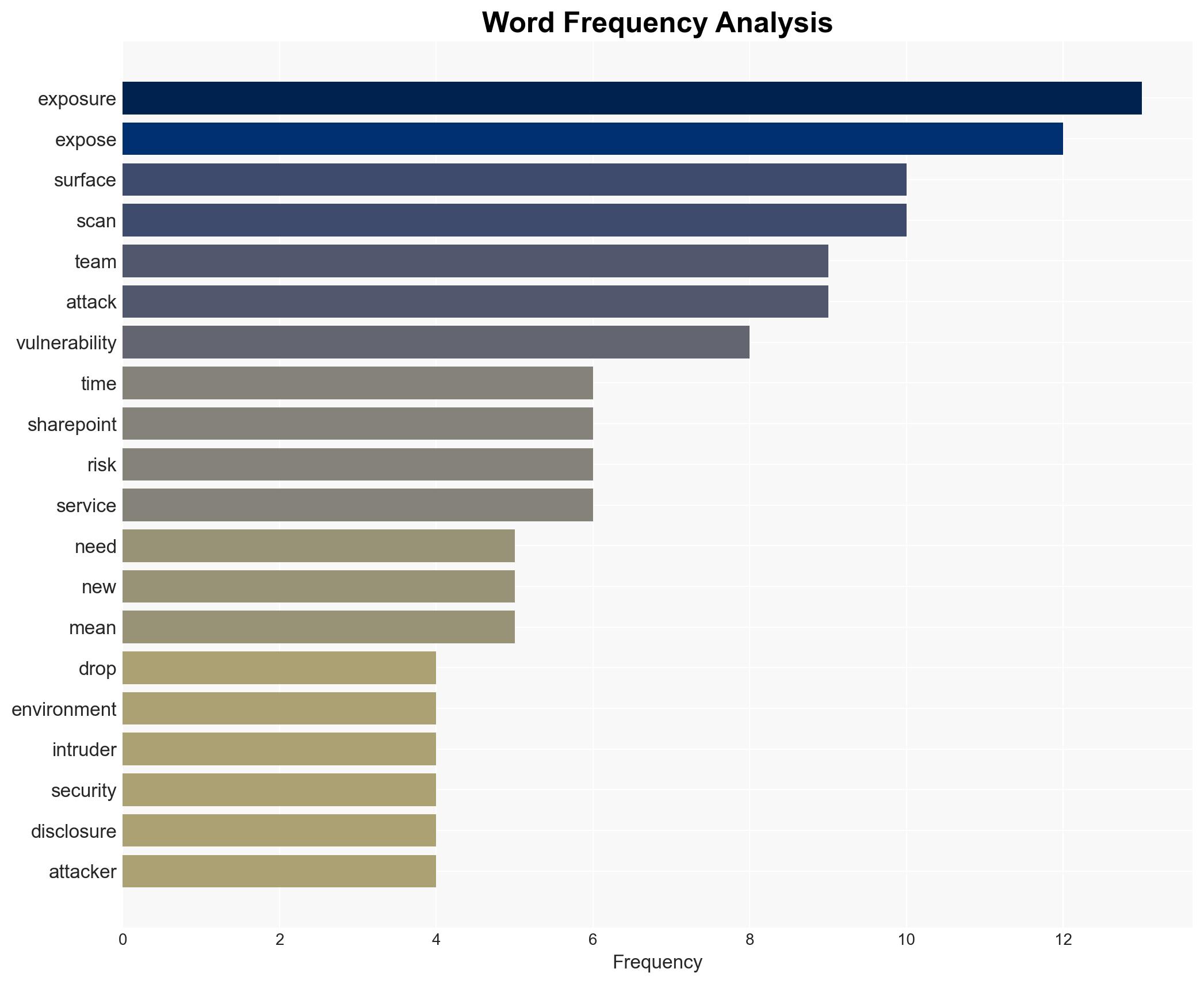
The rapid exploitation of zero-day vulnerabilities poses a significant threat to cybersecurity, particularly when organizations have excessive internet-facing exposure. The most supported hypothesis is that reducing unnecessary exposure can mitigate these risks. This affects IT security teams and organizations globally. Overall confidence in this assessment is moderate due to existing information gaps.
2. Competing Hypotheses
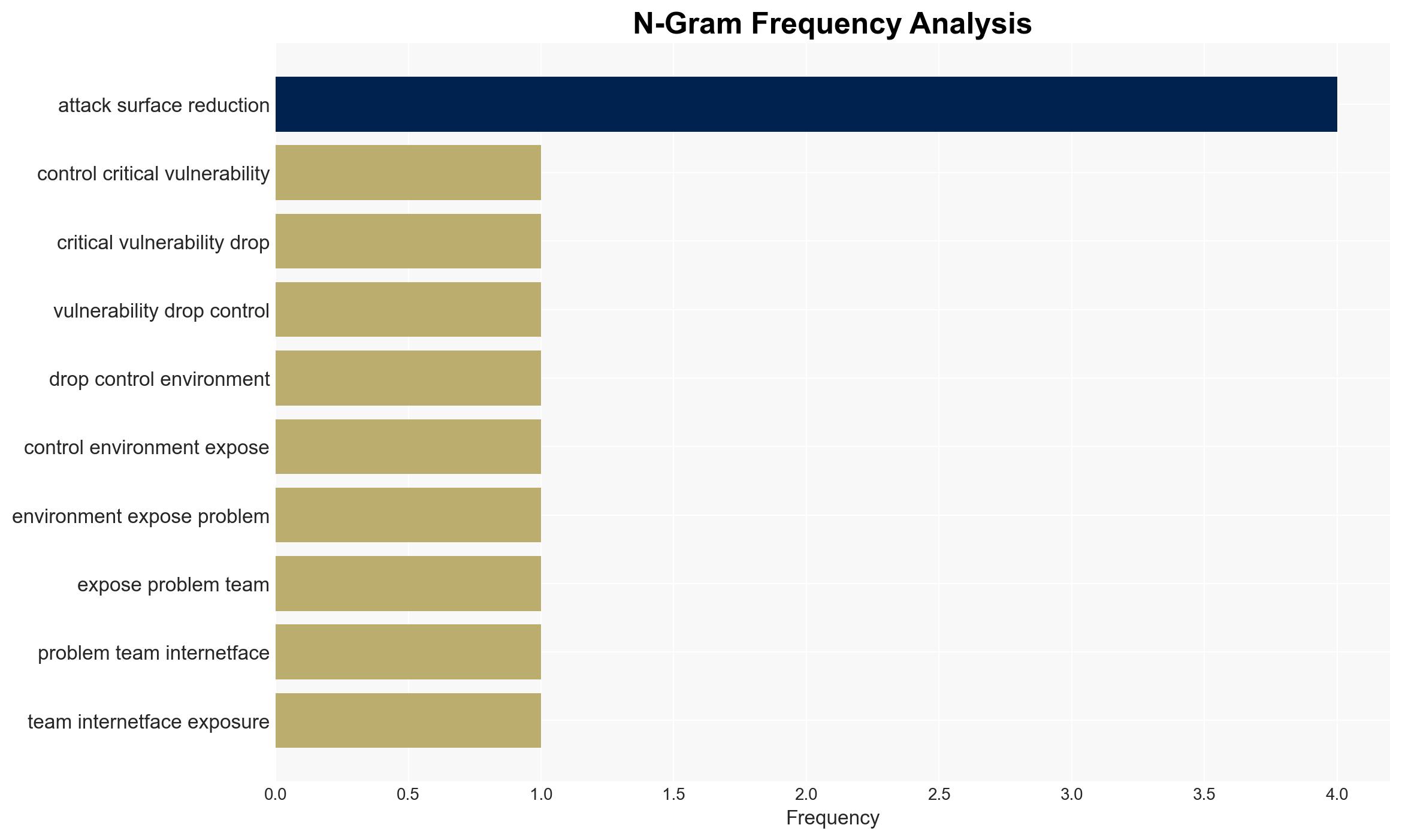
- Hypothesis A: Organizations can significantly reduce the risk of zero-day exploits by minimizing unnecessary internet-facing exposure. Evidence includes the unnecessary exposure of SharePoint servers and the rapid exploitation timeline. Key uncertainties include the effectiveness of current exposure management practices.
- Hypothesis B: The rapid pace of zero-day exploitation is inevitable, and mitigation efforts will have limited impact. This is supported by the shrinking time-to-exploit window and the complexity of patch management. Contradicting evidence includes successful cases of exposure reduction.
- Assessment: Hypothesis A is currently better supported due to evidence of unnecessary exposure contributing to vulnerabilities. Indicators that could shift this judgment include new data on the effectiveness of exposure reduction strategies or changes in exploitation timelines.
3. Key Assumptions and Red Flags
- Assumptions: Organizations have the capability to identify and reduce unnecessary exposure; zero-day exploitation timelines will continue to shrink; current security practices are insufficient.
- Information Gaps: Detailed data on the effectiveness of specific exposure reduction strategies; comprehensive statistics on zero-day exploit timelines across different sectors.
- Bias & Deception Risks: Potential bias from security vendors promoting their solutions; lack of independent verification of vulnerability management practices.
4. Implications and Strategic Risks
The ongoing trend of rapid zero-day exploitation could lead to increased cyber incidents, impacting national security and economic stability. Effective exposure management could mitigate these risks.
- Political / Geopolitical: Potential for increased tensions between nations due to state-sponsored cyber activities.
- Security / Counter-Terrorism: Heightened threat environment as cyber vulnerabilities are exploited for malicious purposes.
- Cyber / Information Space: Increased focus on cybersecurity measures and potential regulatory changes.
- Economic / Social: Potential economic disruptions due to cyber incidents affecting critical infrastructure.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct comprehensive scans to identify and reduce unnecessary internet-facing exposure; prioritize patch management processes.
- Medium-Term Posture (1–12 months): Develop partnerships for threat intelligence sharing; invest in cybersecurity training and awareness programs.
- Scenario Outlook: Best: Effective exposure management reduces incidents. Worst: Continued rapid exploitation leads to significant breaches. Most-Likely: Incremental improvements in exposure management with periodic breaches.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, zero-day vulnerabilities, attack surface management, state-sponsored cyber activity, vulnerability management, cyber threat intelligence
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us