Mixed Signals – The New Yorker
Published on: 2025-03-31
Intelligence Report: Mixed Signals – The New Yorker
1. BLUF (Bottom Line Up Front)
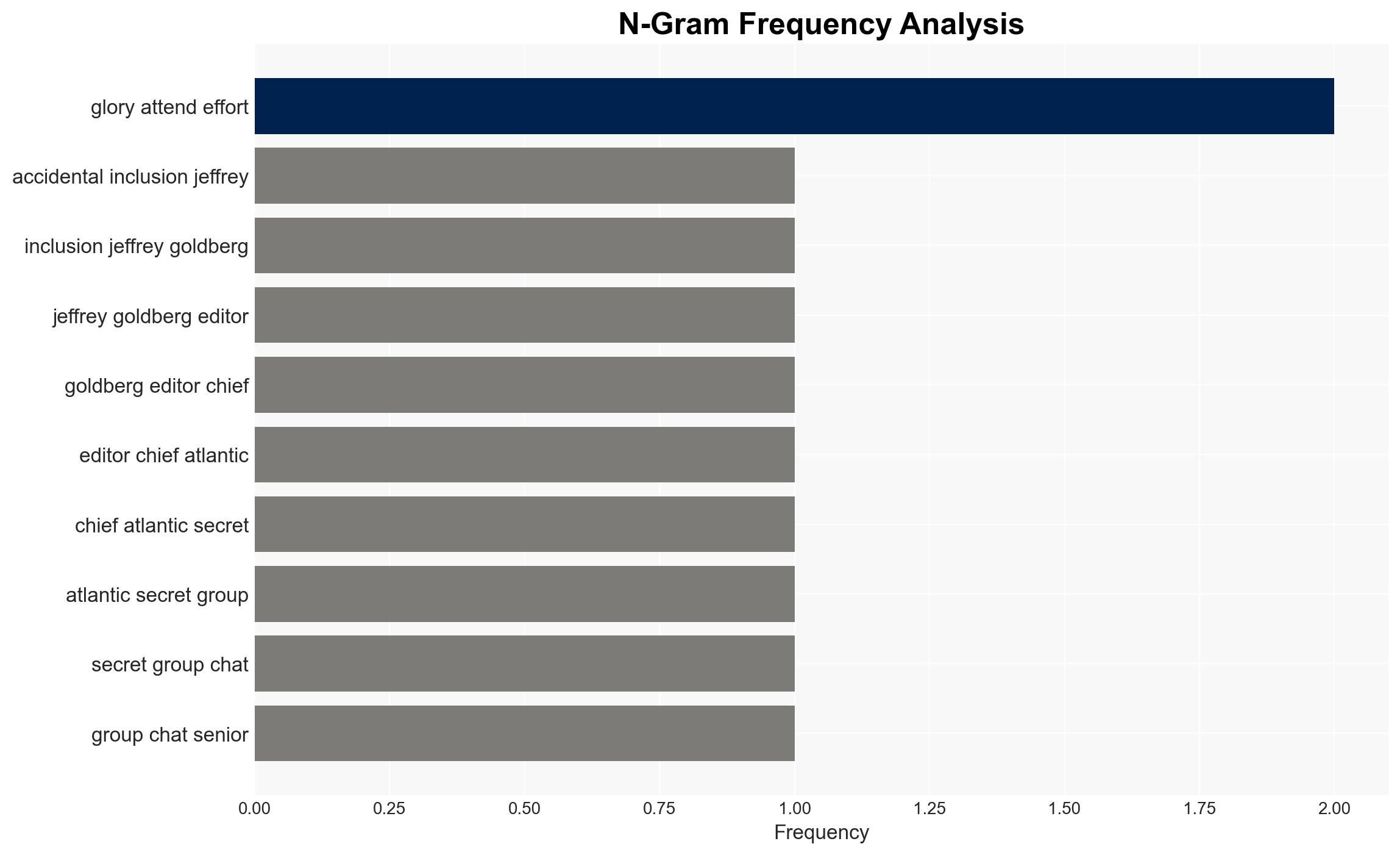
The report highlights a breach of national security involving a secret group chat among senior officials. The incident draws historical parallels to strategic military deceptions, suggesting potential vulnerabilities in communication protocols. Immediate attention is required to assess the breach’s impact and prevent future occurrences.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
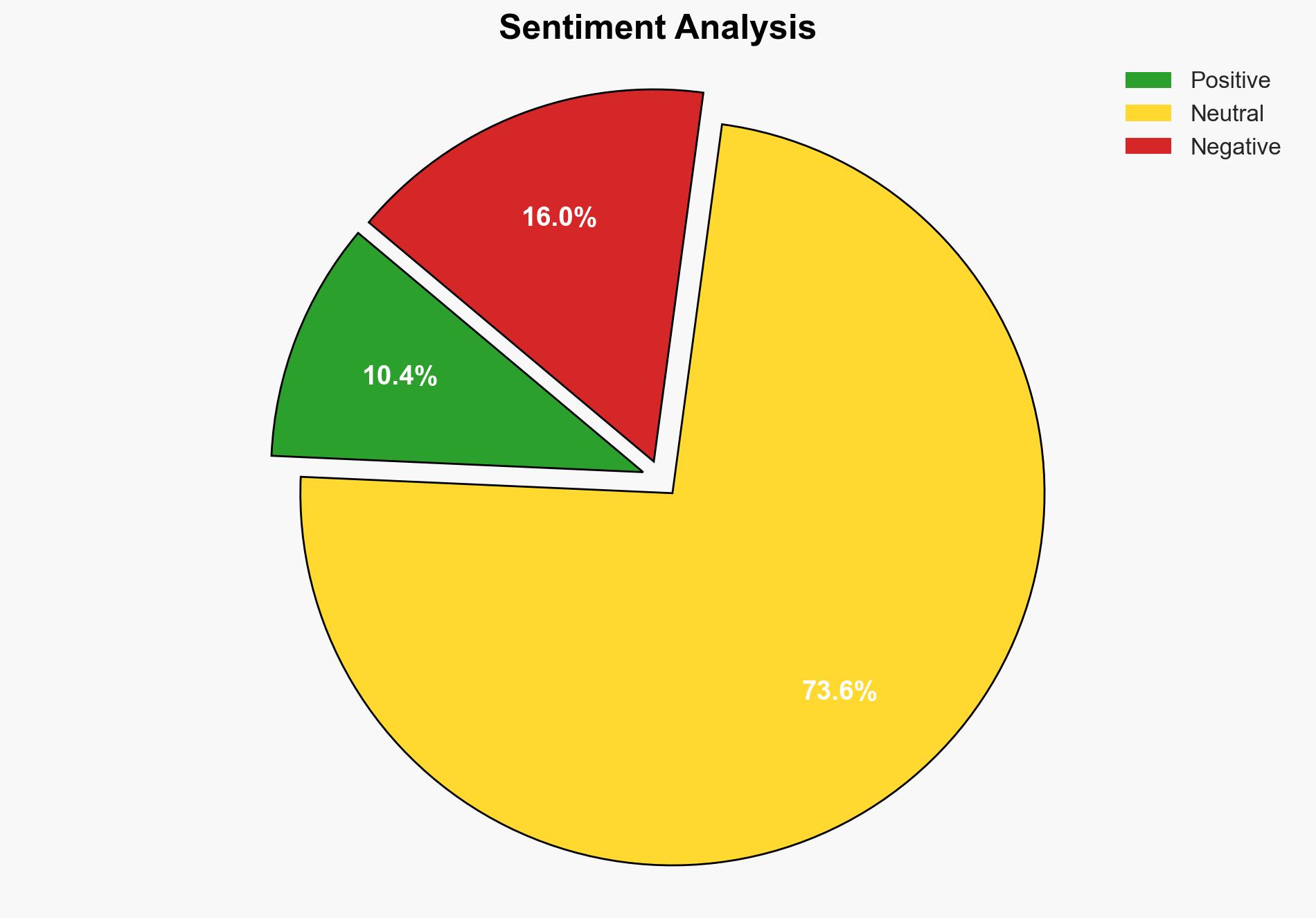
General Analysis
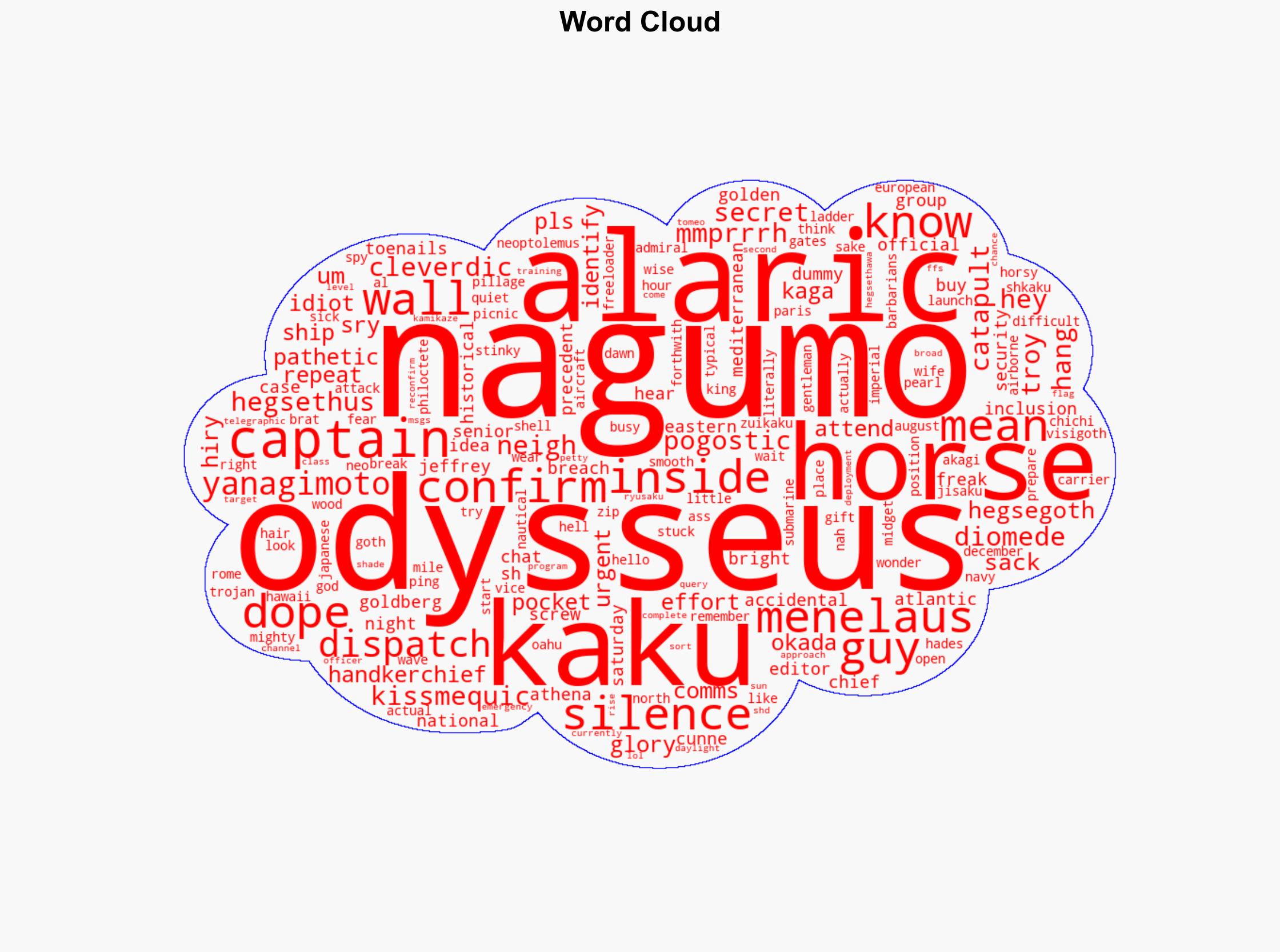
The breach in communication among senior officials, as evidenced by the accidental inclusion of sensitive information in a group chat, underscores the need for robust security measures. Historical references to military strategies, such as the Trojan Horse and Alaric’s sack of Rome, suggest the potential for strategic deception and infiltration. The narrative draws parallels to contemporary security risks, emphasizing the importance of vigilance and secure communication channels.
3. Implications and Strategic Risks
The breach poses significant risks to national security, potentially exposing sensitive information to unauthorized parties. The incident highlights vulnerabilities in digital communication systems, which could be exploited by adversaries. The historical references suggest a pattern of strategic deception that could inform future threats. The implications extend to regional stability and economic interests, as compromised communication could lead to miscalculations or escalations in geopolitical tensions.
4. Recommendations and Outlook
Recommendations:
- Implement enhanced security protocols for digital communications among senior officials to prevent unauthorized access.
- Conduct regular security audits and training to ensure compliance with best practices in information security.
- Explore technological solutions, such as encryption and secure messaging platforms, to safeguard sensitive communications.
Outlook:
Best-case scenario: Implementation of robust security measures prevents future breaches, maintaining national security integrity.
Worst-case scenario: Continued vulnerabilities lead to further breaches, compromising strategic interests and national security.
Most likely scenario: Incremental improvements in security protocols reduce the risk of breaches, but ongoing vigilance is required to address evolving threats.
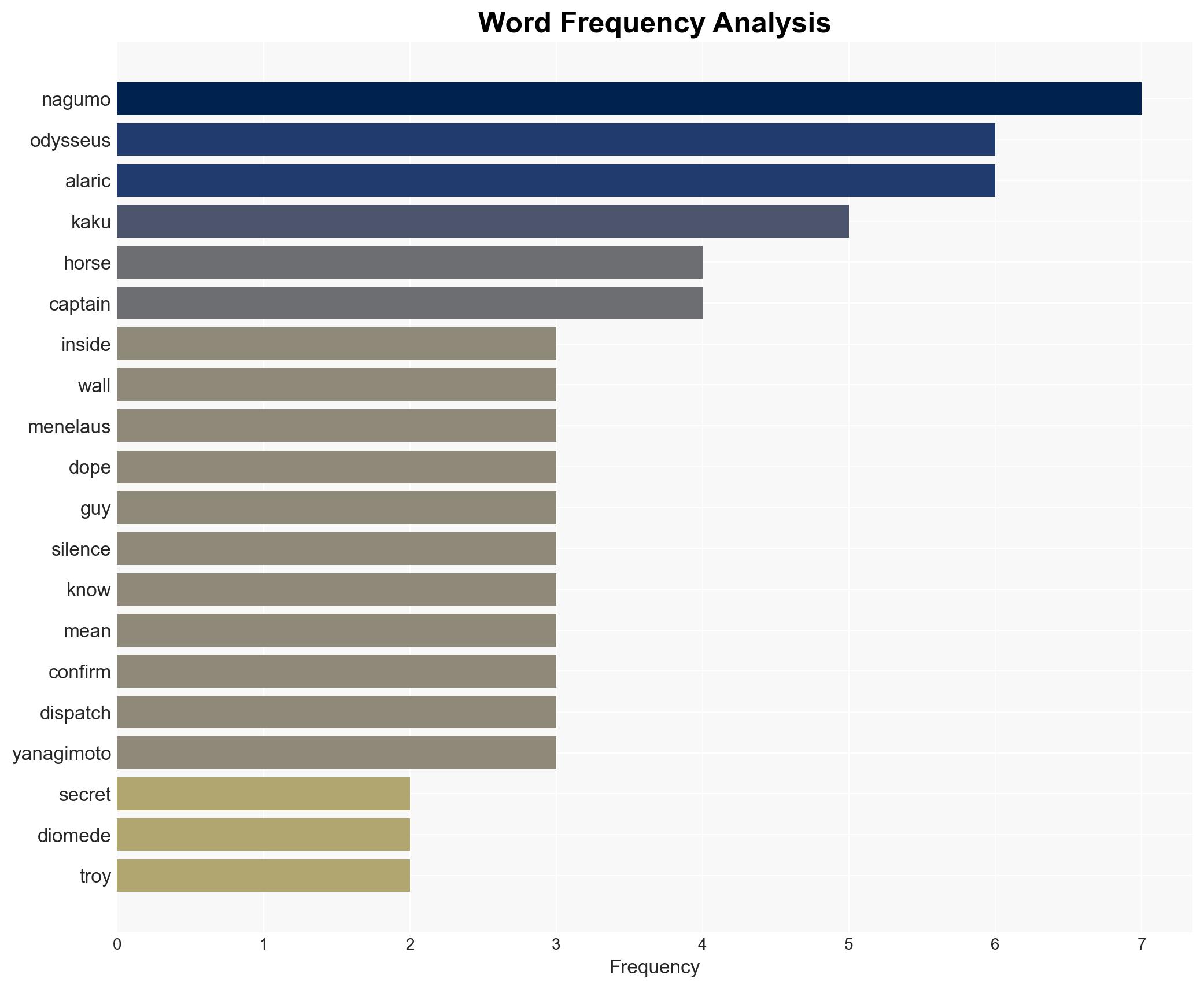
5. Key Individuals and Entities
The report mentions the following individuals involved in the communication breach and historical references:
- Jeffrey Goldberg
- Odysseus
- Diomede
- Menelaus
- Neoptolemus
- Philoctete
- Hegsethus
- Alaric
- Chichi Nagumo
- Jisaku Okada
- Ryusaku Yanagimoto
- Tomeo Kaku
These individuals are referenced in the context of historical and contemporary strategic scenarios, emphasizing the importance of secure communication and strategic foresight.