Nasscom advises tech firms to enhance cybersecurity amid escalating West Asia tensions and potential disrupti…
Published on: 2026-03-09
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
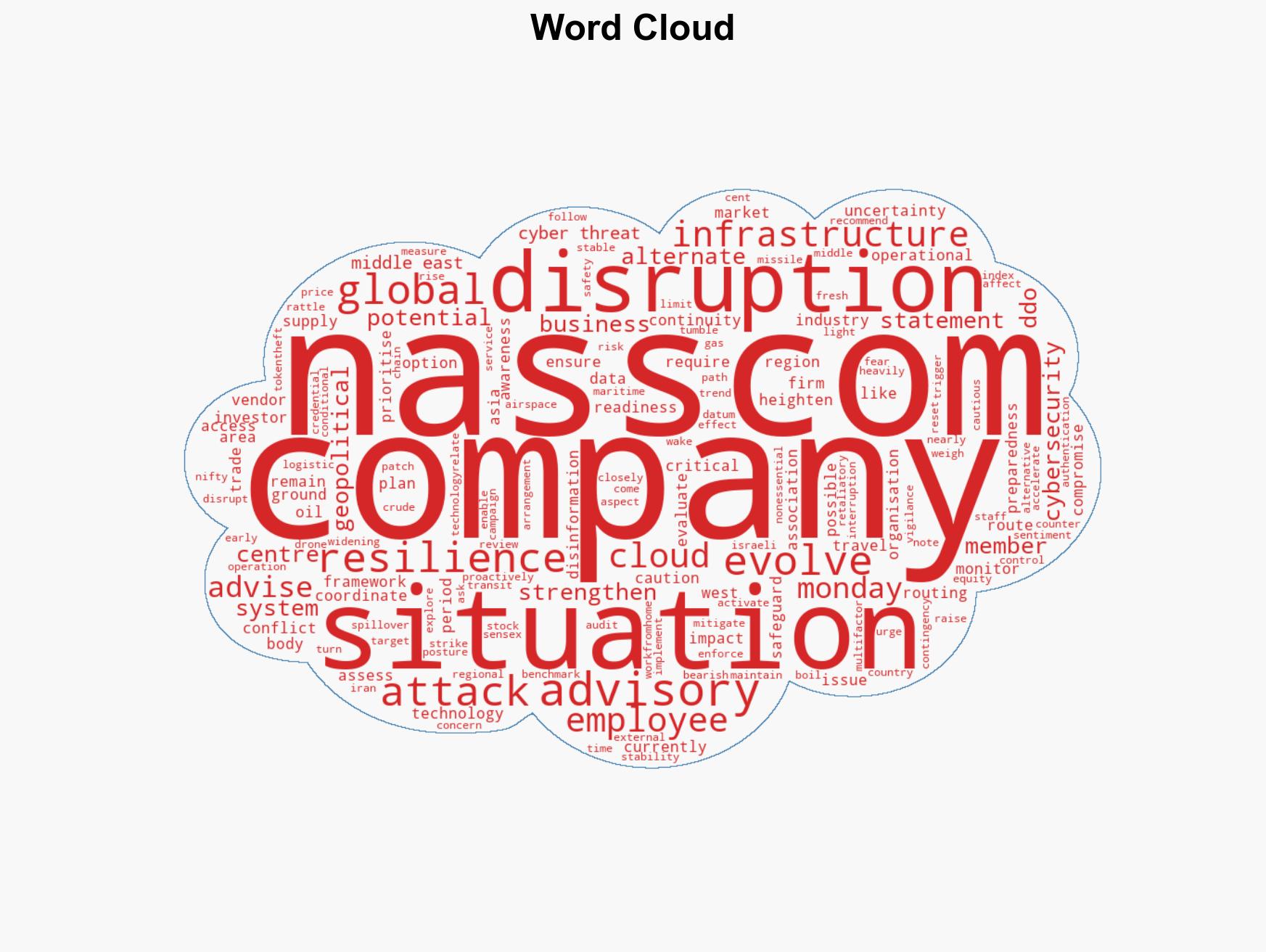
Intelligence Report: West Asia conflict Nasscom urges member firms to step up vigilance cyber resilience
1. BLUF (Bottom Line Up Front)
The ongoing geopolitical conflict in West Asia, particularly involving US and Israeli actions against Iran, has prompted Nasscom to advise technology firms to enhance cybersecurity and operational readiness. This advisory highlights potential cyber threats and disruptions to global technology infrastructure. The situation affects technology companies globally, with moderate confidence in the assessment that heightened vigilance is necessary given the evolving threat landscape.
2. Competing Hypotheses
- Hypothesis A: The conflict in West Asia will lead to increased cyber threats and disruptions to global technology infrastructure, necessitating immediate action by technology firms. This is supported by Nasscom’s advisory and the historical precedent of cyber activities during geopolitical tensions. However, the extent of the threat remains uncertain.
- Hypothesis B: The current geopolitical tensions will not significantly impact global technology infrastructure or lead to substantial cyber threats. This hypothesis is less supported given the proactive measures advised by Nasscom and the potential for escalation in cyber activities during such conflicts.
- Assessment: Hypothesis A is currently better supported due to the advisory from Nasscom and the historical correlation between geopolitical conflicts and increased cyber threats. Indicators such as further escalation in the conflict or reports of cyber incidents could reinforce this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The conflict will continue to escalate; technology firms have the capacity to enhance cybersecurity measures; cyber threats are a likely vector of conflict spillover.
- Information Gaps: Specific details on the nature and scope of potential cyber threats; real-time intelligence on cyber activities linked to the conflict.
- Bias & Deception Risks: Potential bias in reporting from involved parties; risk of underestimating the capability of state or non-state actors to conduct cyber operations.
4. Implications and Strategic Risks
The conflict in West Asia could lead to prolonged instability, affecting multiple domains. The potential for cyber operations targeting global technology infrastructure is a significant concern.
- Political / Geopolitical: Escalation could draw in additional regional actors, complicating diplomatic resolutions.
- Security / Counter-Terrorism: Increased risk of asymmetric warfare tactics, including cyber attacks.
- Cyber / Information Space: Potential rise in cyber espionage and infrastructure attacks targeting technology firms.
- Economic / Social: Disruptions in oil supply and global markets could lead to economic instability and social unrest.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cyber threats, implement robust cybersecurity measures, and activate business continuity plans.
- Medium-Term Posture (1–12 months): Develop partnerships for intelligence sharing, invest in cybersecurity infrastructure, and conduct regular threat assessments.
- Scenario Outlook:
- Best: De-escalation leads to stabilization, reducing cyber threat levels.
- Worst: Conflict escalates, resulting in widespread cyber attacks and infrastructure disruptions.
- Most-Likely: Continued tensions with intermittent cyber threats targeting technology infrastructure.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, geopolitical conflict, technology infrastructure, Nasscom advisory, West Asia tensions, cyber threats, business continuity
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us