Navigating Advanced Persistent Threats: Identification and Prevention Strategies
Published on: 2026-02-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: How to understand and avoid Advanced Persistent Threats
1. BLUF (Bottom Line Up Front)
Advanced Persistent Threats (APTs) represent a significant and ongoing risk to a wide range of sectors beyond traditional government and military targets, including healthcare, telecoms, and finance. The most likely hypothesis is that APTs will continue to evolve in sophistication and target diversity, posing a persistent threat to national and economic security. Overall confidence in this assessment is moderate, given the dynamic nature of cyber threats and the evolving tactics of threat actors.
2. Competing Hypotheses
- Hypothesis A: APTs are primarily state-sponsored and continue to focus on strategic targets such as government and military. This is supported by historical patterns but contradicted by the recent diversification of targets to include commercial sectors.
- Hypothesis B: APTs have diversified and now include non-state actors targeting a broader range of sectors, including commercial and critical infrastructure. This is supported by the increasing number of attacks on non-traditional targets, though it lacks direct attribution evidence.
- Assessment: Hypothesis B is currently better supported due to the observed expansion of APT targets beyond traditional state interests. Key indicators that could shift this judgment include evidence of state sponsorship in recent attacks or a return to predominantly government-focused targeting.
3. Key Assumptions and Red Flags
- Assumptions: APTs will continue to evolve in sophistication; state and non-state actors will both engage in APT activities; current detection and defense mechanisms are insufficient to fully mitigate APT risks.
- Information Gaps: Lack of specific attribution data for recent APT incidents; limited visibility into the full scope of APT capabilities and intentions.
- Bias & Deception Risks: Potential bias in attributing APTs predominantly to state actors; risk of deception by threat actors using false flags to mislead attribution efforts.
4. Implications and Strategic Risks
The evolution of APTs could lead to increased geopolitical tensions, particularly if state-sponsored activities are confirmed. The diversification of targets suggests a broadening threat landscape that could strain cybersecurity resources and defenses.
- Political / Geopolitical: Potential for increased international tensions and retaliatory actions if state sponsorship is confirmed.
- Security / Counter-Terrorism: Heightened threat environment requiring enhanced cybersecurity measures and international cooperation.
- Cyber / Information Space: Increased demand for advanced cybersecurity solutions and threat intelligence sharing.
- Economic / Social: Potential economic disruptions and loss of public trust in affected sectors, particularly if critical infrastructure is targeted.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of critical infrastructure sectors; increase information sharing among cybersecurity stakeholders; conduct vulnerability assessments.
- Medium-Term Posture (1–12 months): Develop resilience measures, including regular training and simulation exercises; strengthen international partnerships for intelligence sharing and joint response capabilities.
- Scenario Outlook:
- Best Case: Improved detection and response capabilities reduce APT effectiveness, leading to a decline in successful attacks.
- Worst Case: APTs successfully compromise critical infrastructure, causing significant economic and social disruption.
- Most-Likely: Continued evolution of APT tactics with periodic successful breaches, necessitating ongoing adaptation of defense strategies.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
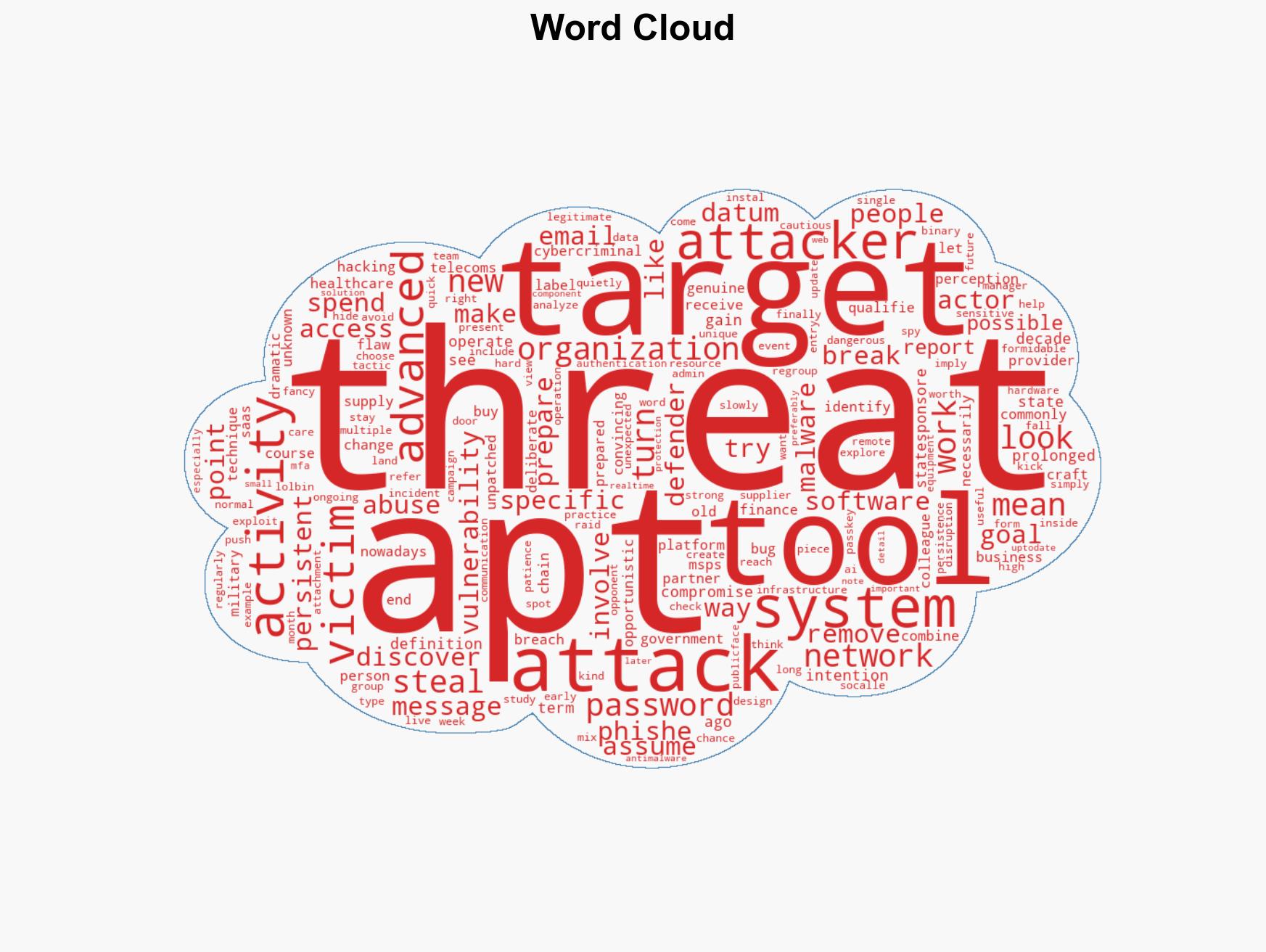
cybersecurity, advanced persistent threats, state-sponsored actors, critical infrastructure, cyber-espionage, information security, threat intelligence
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us