NCSC Advises Urgent Patching of Critical F5 BIG-IP Vulnerability Amid Active Exploitation
Published on: 2026-03-31
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: NCSC Urges Immediate Patching of F5 BIG-IP Bug
1. BLUF (Bottom Line Up Front)
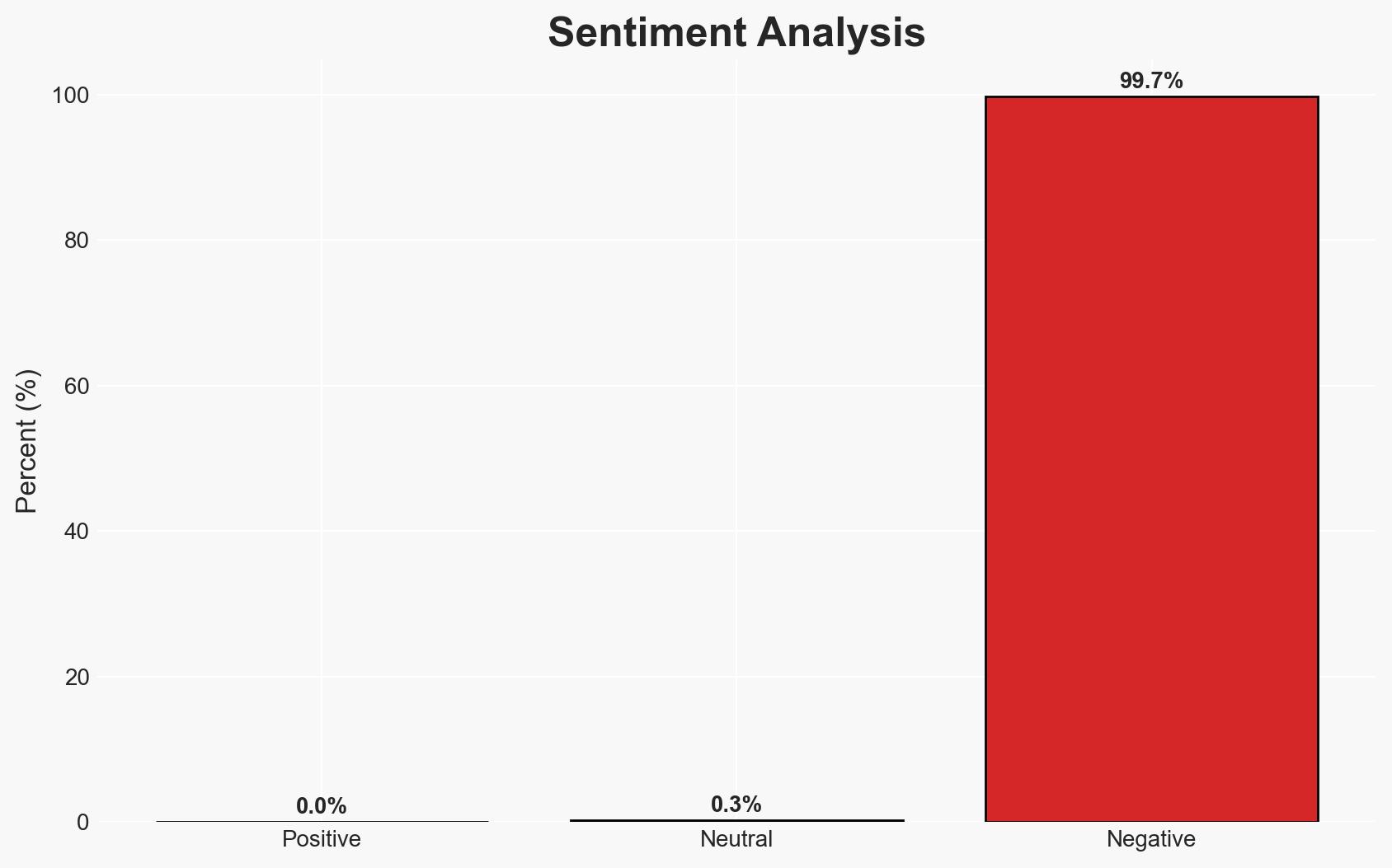
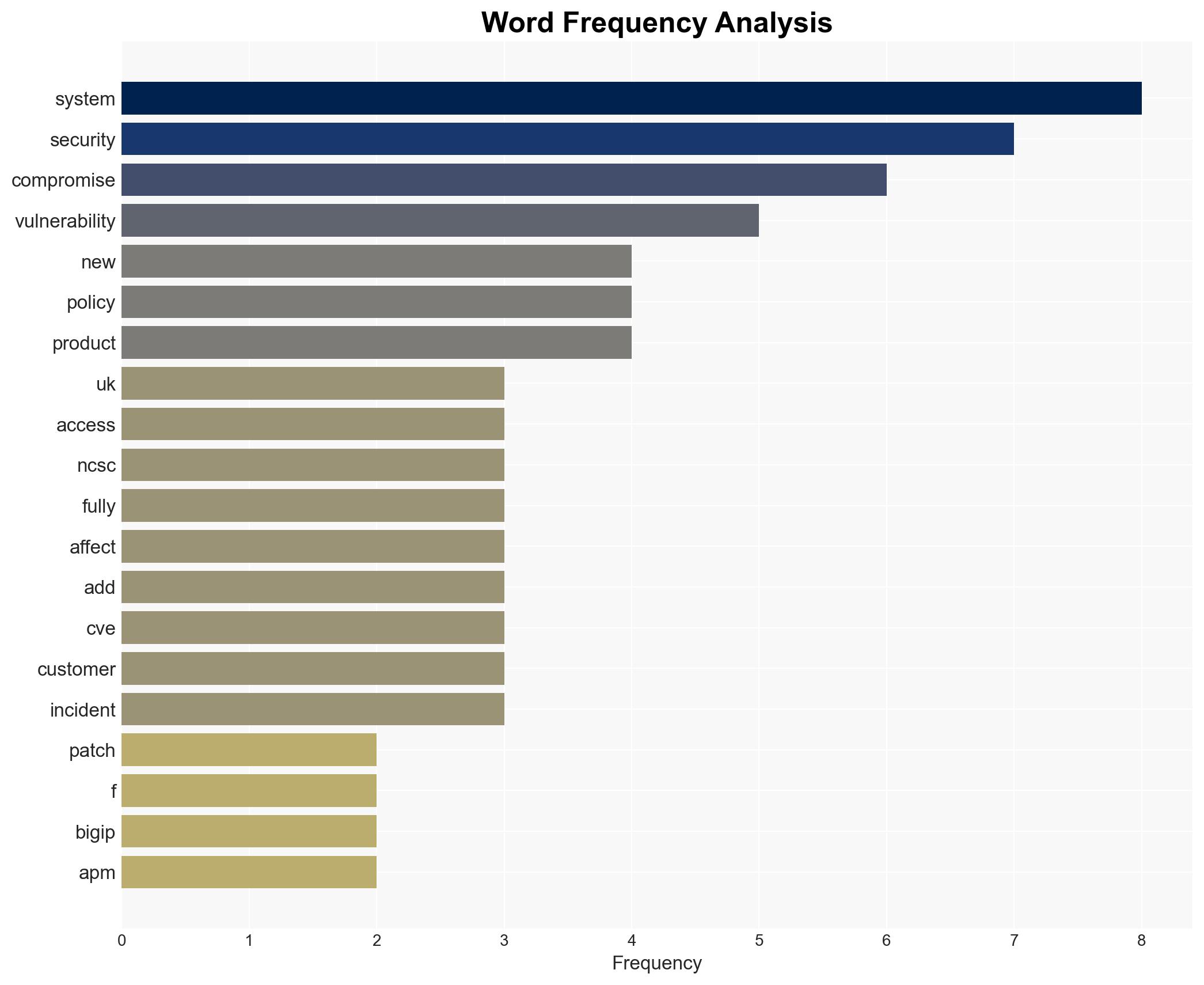
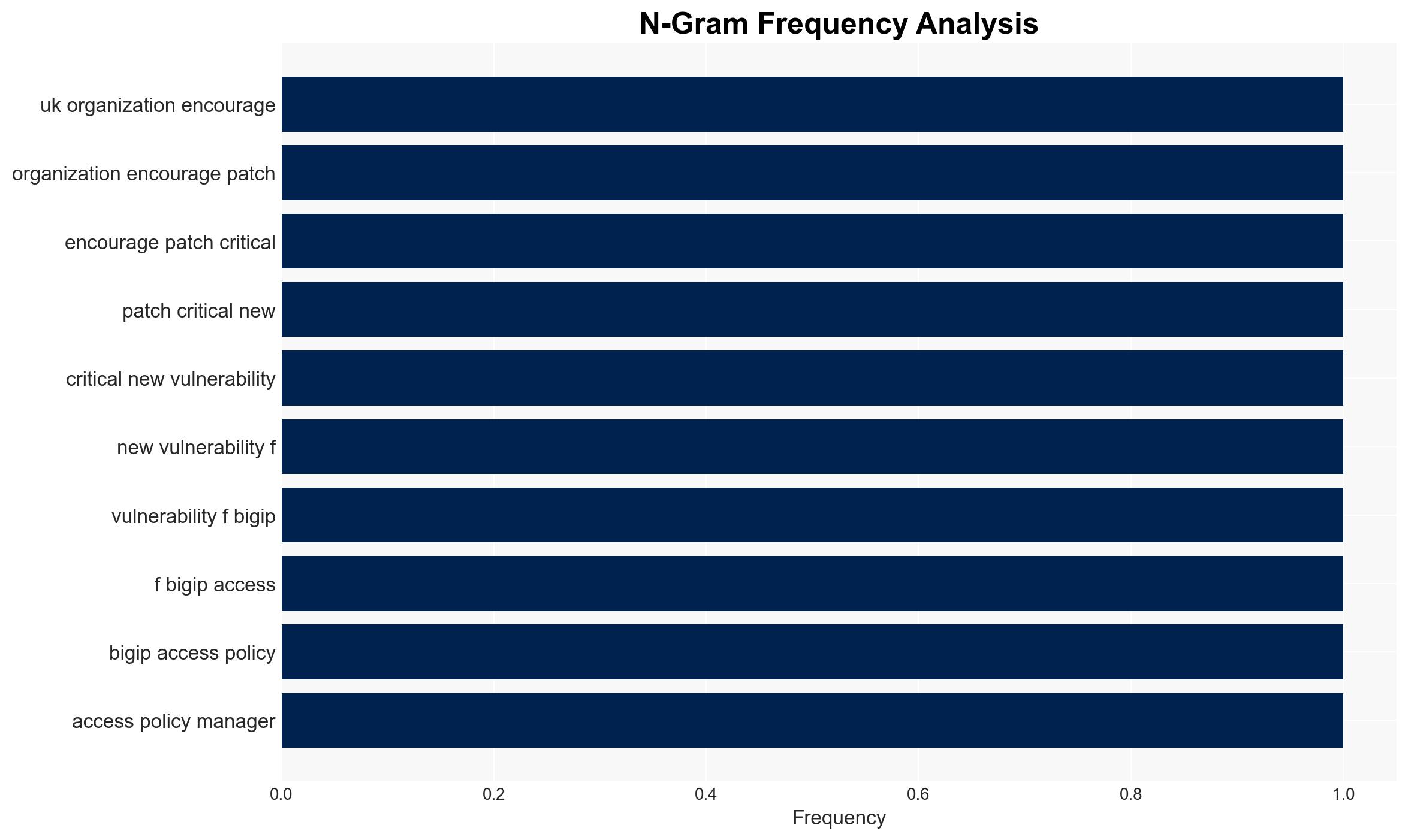
The National Cyber Security Centre (NCSC) has issued an urgent advisory for UK organizations to patch a critical vulnerability in F5’s BIG-IP Access Policy Manager, which is under active exploitation. The vulnerability, CVE-2025-53521, allows remote code execution and poses a significant threat to network security. This assessment is made with moderate confidence due to ongoing investigations into the extent of exploitation within UK networks.
2. Competing Hypotheses
- Hypothesis A: The vulnerability is being actively exploited by state-backed actors to gain persistent access to critical infrastructure networks. This is supported by the reclassification of the vulnerability’s severity and historical targeting patterns of F5 products by sophisticated threat actors. However, the full scope of exploitation in the UK remains unclear.
- Hypothesis B: The exploitation is primarily opportunistic by non-state actors seeking to exploit the vulnerability for financial gain through ransomware or data theft. This is supported by the high CVSS score indicating attractiveness to a wide range of cybercriminals. Contradictory evidence includes the specific targeting of F5 products by state actors in the past.
- Assessment: Hypothesis A is currently better supported due to the strategic value of F5 products in critical infrastructure and the historical precedent of state-backed exploitation. Indicators that could shift this judgment include evidence of widespread financial-motivated attacks or attribution to specific non-state groups.
3. Key Assumptions and Red Flags
- Assumptions: The vulnerability is being actively exploited; State-backed actors have the capability and intent to exploit this vulnerability; F5’s security advisory accurately reflects the threat landscape; Organizations will follow NCSC and F5 guidance promptly.
- Information Gaps: Specific details on the extent of exploitation within UK networks; Attribution of current exploitation activities; Effectiveness of mitigation measures implemented by affected organizations.
- Bias & Deception Risks: Potential over-reliance on vendor-provided information; Confirmation bias towards state-backed actor involvement; Possible underestimation of non-state actor capabilities.
4. Implications and Strategic Risks
The exploitation of this vulnerability could lead to significant disruptions in critical infrastructure and sensitive data breaches, potentially affecting national security. The situation may evolve as more information becomes available about the actors involved and the extent of the compromise.
- Political / Geopolitical: Increased tensions between states if attribution to a nation-state actor is confirmed; Potential for retaliatory cyber operations.
- Security / Counter-Terrorism: Heightened alert for critical infrastructure sectors; Possible need for increased cybersecurity measures and collaboration.
- Cyber / Information Space: Potential for further exploitation by other threat actors; Increased scrutiny on F5 and similar technology vendors.
- Economic / Social: Potential economic impact due to service disruptions; Erosion of public trust in digital infrastructure security.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urgently patch affected systems; Conduct thorough investigations for signs of compromise; Report incidents to NCSC; Enhance monitoring and threat hunting activities.
- Medium-Term Posture (1–12 months): Develop resilience measures including regular security assessments; Strengthen partnerships with cybersecurity agencies; Invest in cybersecurity training and awareness programs.
- Scenario Outlook:
- Best Case: Rapid patching and mitigation prevent widespread exploitation, with minimal impact.
- Worst Case: Extensive exploitation leads to significant disruptions and data breaches, with geopolitical ramifications.
- Most-Likely: Mixed outcomes with some successful mitigations but ongoing exploitation attempts, requiring sustained vigilance.
6. Key Individuals and Entities
- National Cyber Security Centre (NCSC)
- F5 Networks
- US Cybersecurity and Infrastructure Security Agency (CISA)
- State-backed threat actors (not specifically identified)
7. Thematic Tags
cybersecurity, vulnerability management, state-sponsored threats, critical infrastructure, cyber-espionage, network security, digital resilience
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us