Network Six Introduces Managed Cybersecurity Service to Enhance Business Defense Against Evolving Threats
Published on: 2026-03-09
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Network Six launched a new Managed Cybersecurity Service
1. BLUF (Bottom Line Up Front)
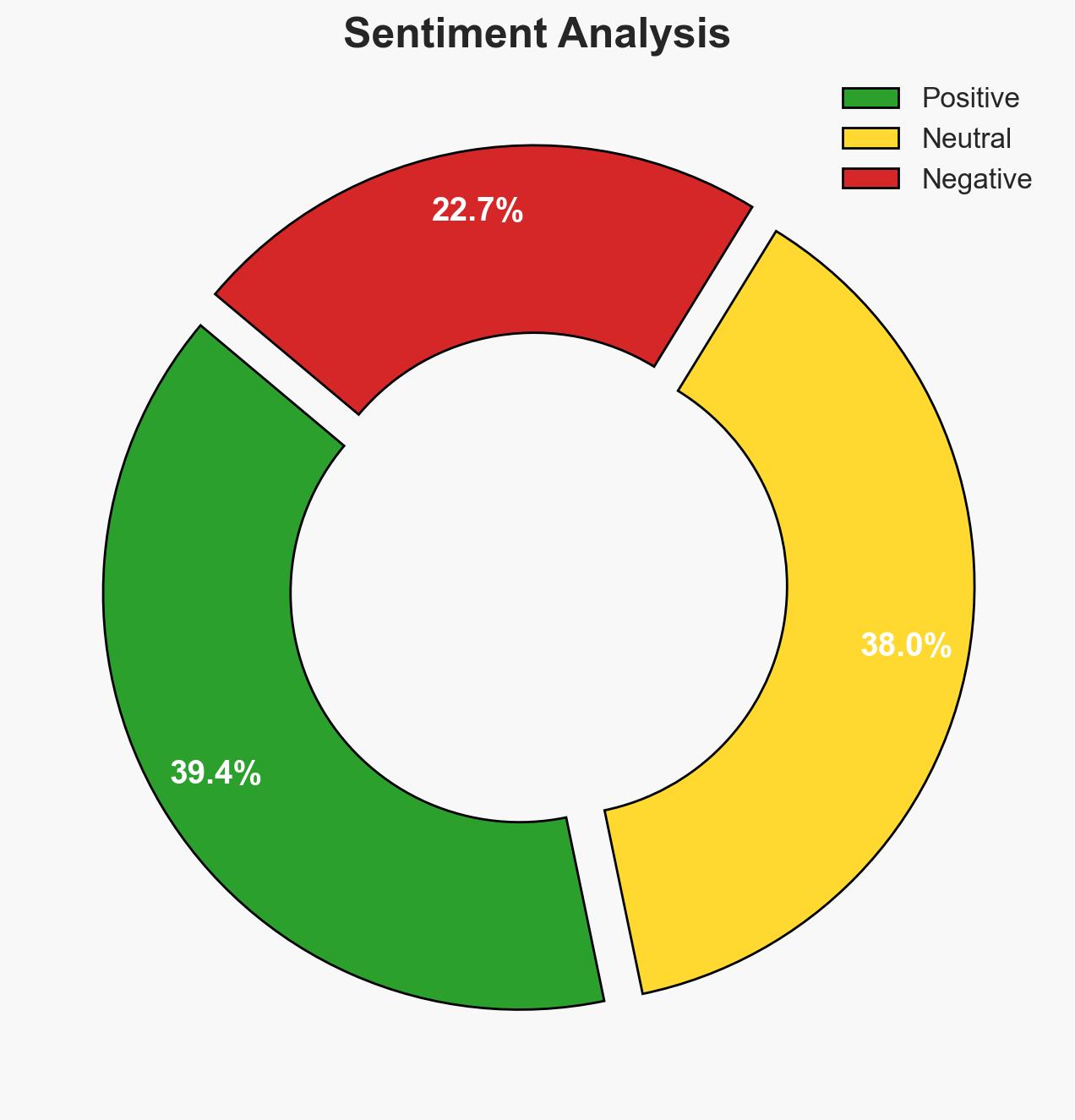
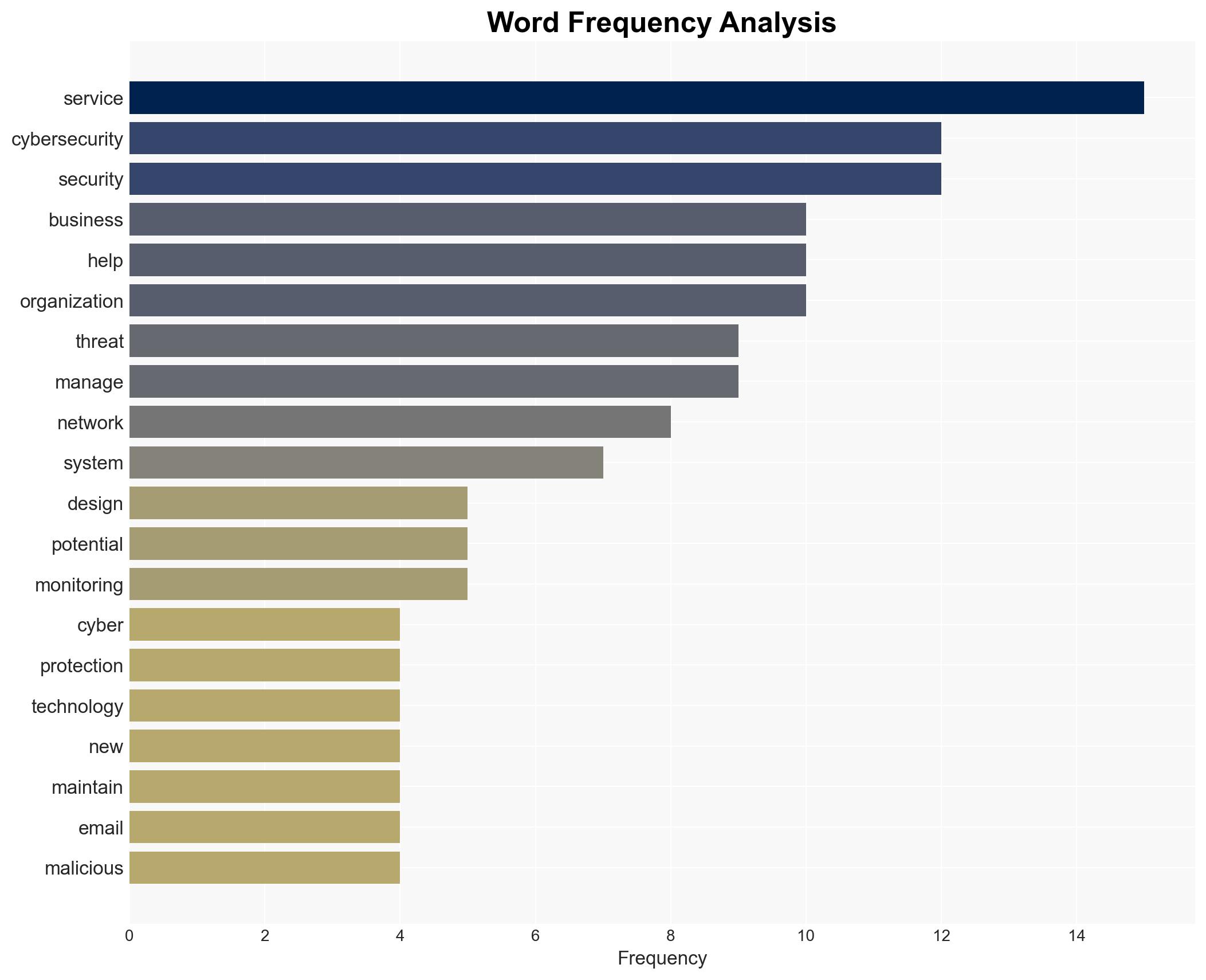
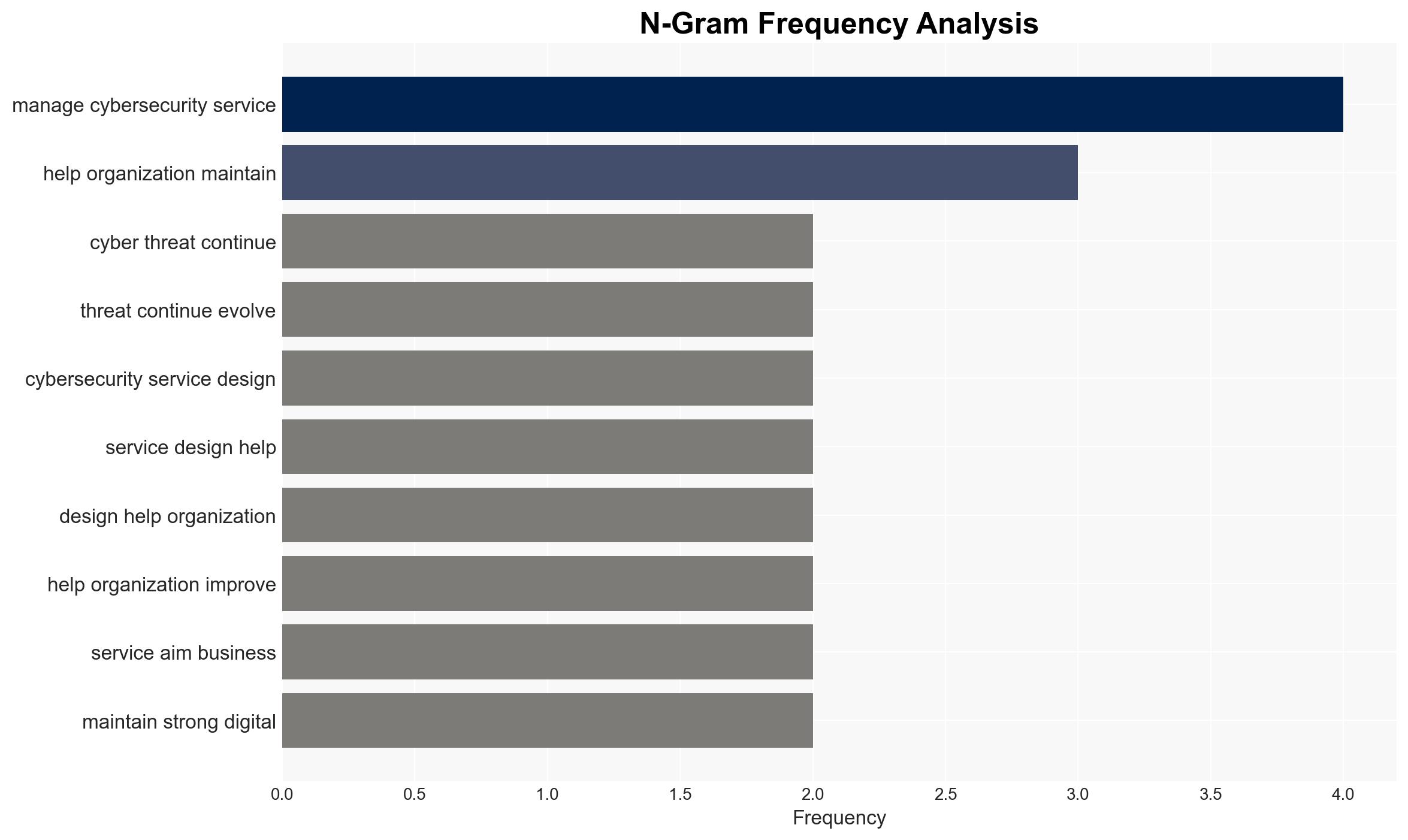
Network Six has launched a new Managed Cybersecurity Service aimed at enhancing the cybersecurity posture of small to mid-sized businesses. This initiative is likely to improve these organizations’ ability to detect and respond to cyber threats, potentially reducing their vulnerability to cybercrime. The most likely hypothesis is that this service will fill a critical gap in cybersecurity resources for smaller enterprises. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: Network Six’s service will significantly enhance the cybersecurity capabilities of small and mid-sized businesses, leading to a reduction in successful cyberattacks. This is supported by the service’s comprehensive approach, including endpoint protection and continuous monitoring. However, the effectiveness depends on the adoption rate and the actual performance of the service.
- Hypothesis B: The service may have limited impact due to potential challenges in market penetration or insufficient differentiation from existing solutions. This hypothesis is supported by the competitive nature of the cybersecurity market and potential skepticism from businesses regarding new services.
- Assessment: Hypothesis A is currently better supported due to the specific targeting of underserved small and mid-sized businesses and the comprehensive nature of the service. Key indicators that could shift this judgment include market adoption rates and customer feedback on service effectiveness.
3. Key Assumptions and Red Flags
- Assumptions: Businesses will perceive the need for enhanced cybersecurity; Network Six can effectively market and deliver its service; the service will perform as advertised.
- Information Gaps: Detailed performance metrics of the service; market adoption rates; competitor responses.
- Bias & Deception Risks: Potential bias in the promotional material from Network Six; lack of independent verification of service effectiveness.
4. Implications and Strategic Risks
This development could lead to improved cybersecurity resilience among small and mid-sized businesses, potentially decreasing their attractiveness as targets for cybercriminals. Over time, this could shift threat actors’ focus to other vulnerable sectors or lead to more sophisticated attack methods.
- Political / Geopolitical: Minimal direct implications, though improved cybersecurity could contribute to national economic stability.
- Security / Counter-Terrorism: Enhanced cybersecurity could reduce the risk of cyber-enabled terrorism targeting smaller businesses.
- Cyber / Information Space: The service might prompt competitors to innovate, potentially advancing overall cybersecurity capabilities.
- Economic / Social: Improved cybersecurity could enhance business confidence and economic stability, particularly for smaller enterprises.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor adoption rates and initial feedback from early adopters; assess competitor responses.
- Medium-Term Posture (1–12 months): Encourage partnerships with cybersecurity firms to enhance service offerings; invest in customer education on cybersecurity best practices.
- Scenario Outlook:
- Best: High adoption leads to a significant reduction in cyber incidents among small businesses.
- Worst: Service underperforms or fails to gain market traction, leading to continued vulnerabilities.
- Most-Likely: Moderate adoption with incremental improvements in cybersecurity posture.
6. Key Individuals and Entities
- Giancarlo Murtaza, Network Six
- Network Six, technology services provider
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
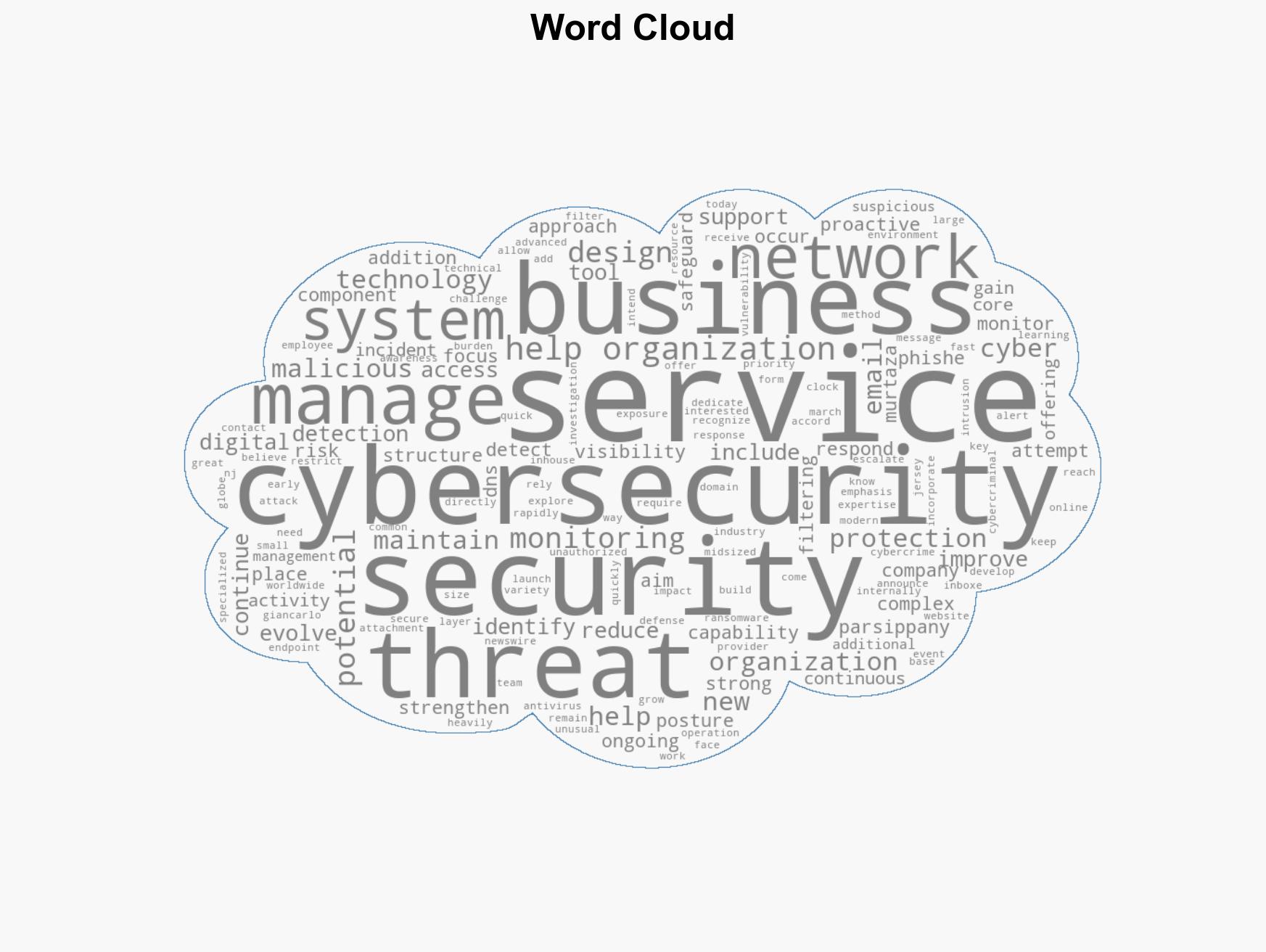
cybersecurity, small businesses, cyber threats, managed services, network security, cyber resilience, technology services
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us