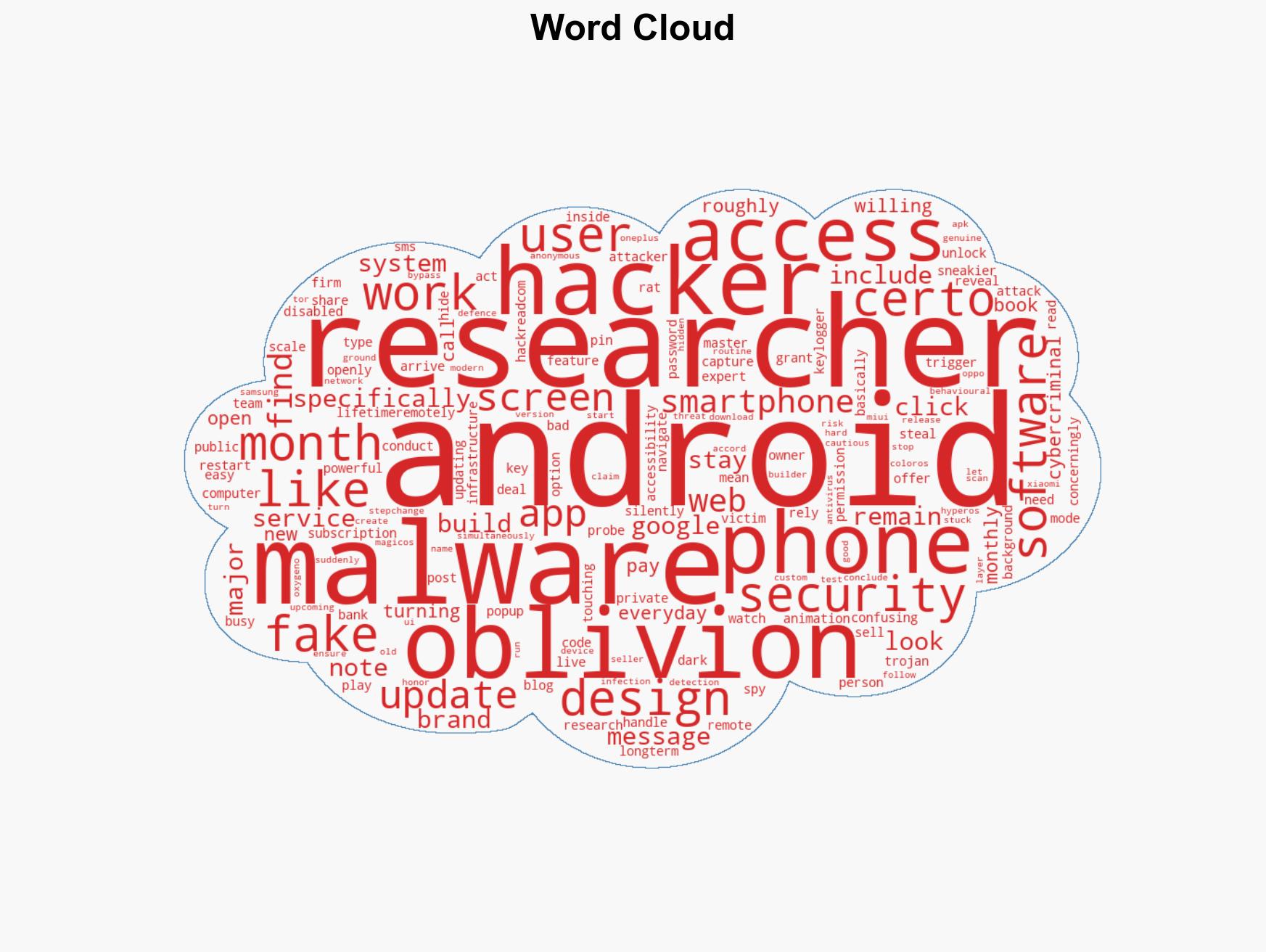
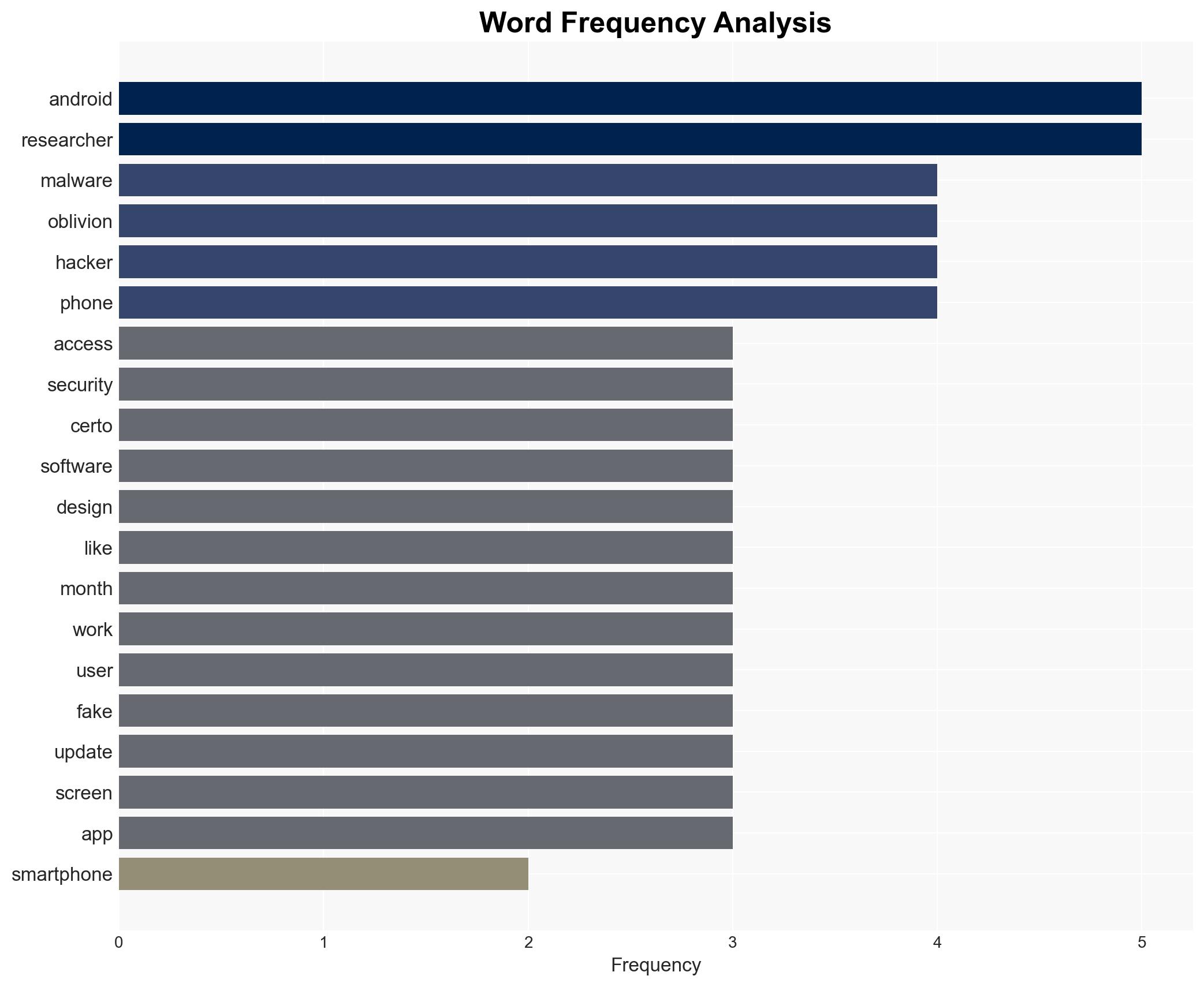
New Android Malware Oblivion Leverages Fake Updates to Exploit Smartphones for $300 Monthly Subscription
Published on: 2026-02-25
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: 300 a Month Android Malware Oblivion Uses Fake Updates to Hijack Phones
1. BLUF (Bottom Line Up Front)
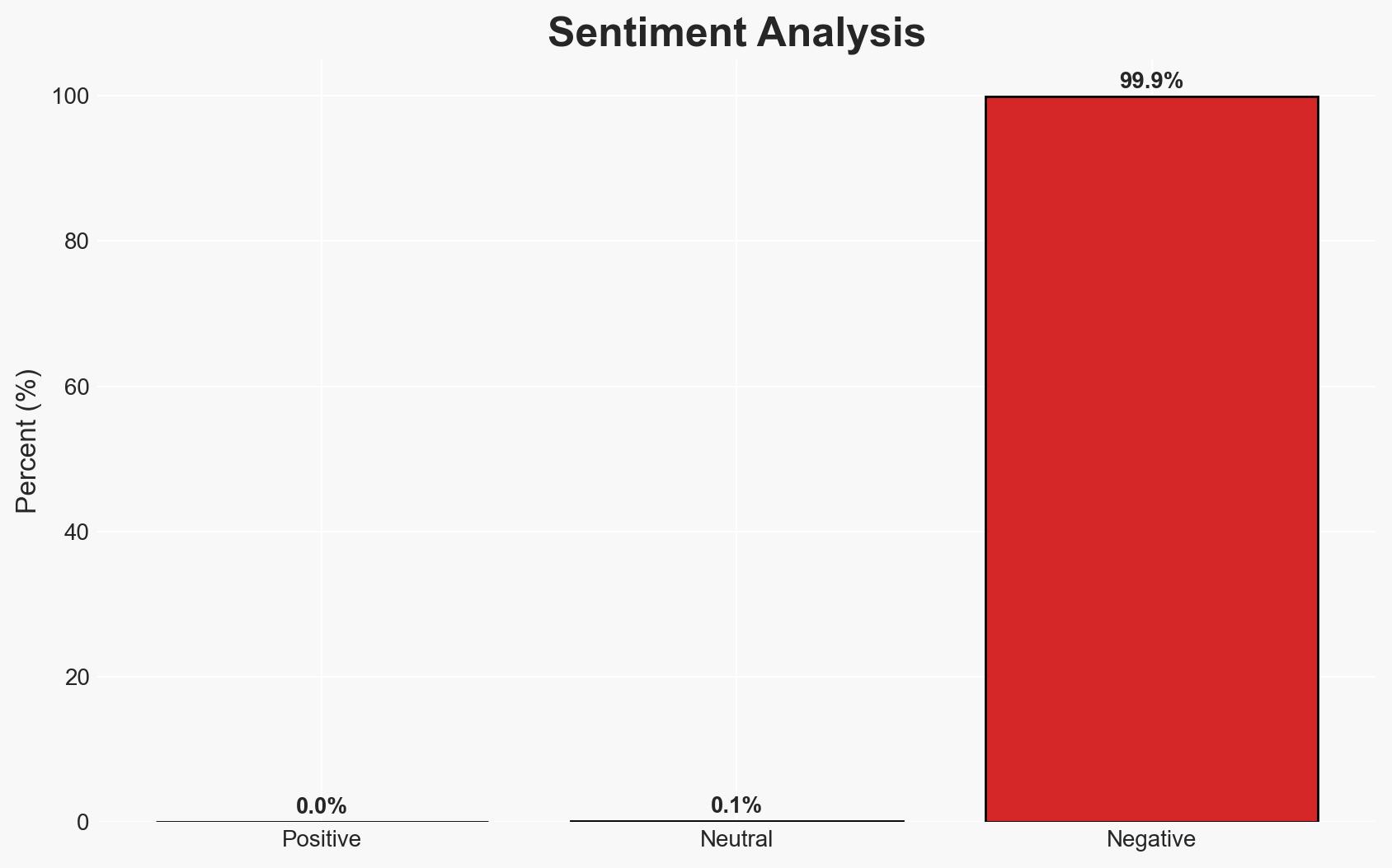
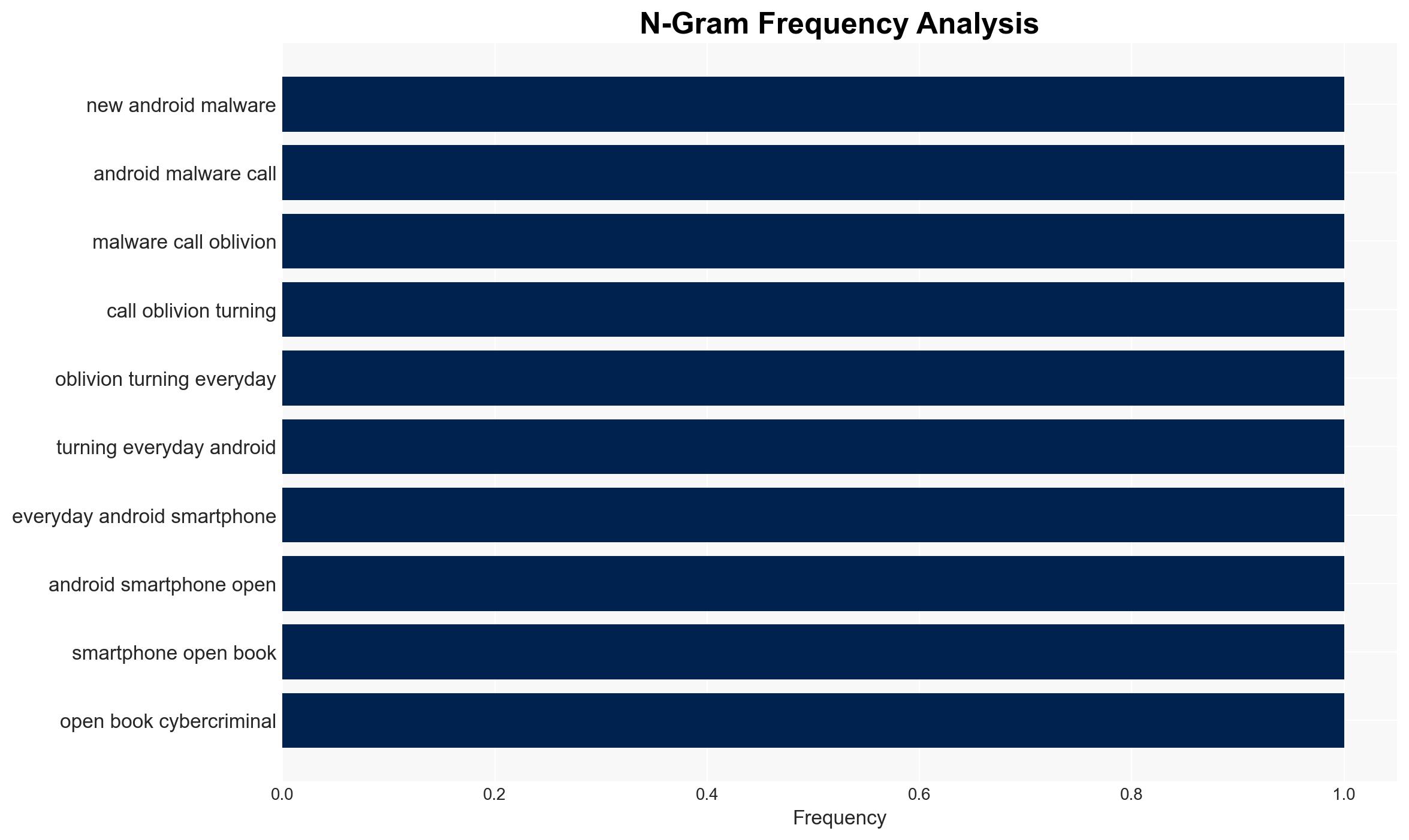
The Oblivion malware represents a significant threat to Android users by exploiting fake updates to gain unauthorized access to devices. This malware is notable for its ease of use and availability on the public web, posing risks to both individuals and organizations using Android devices. The most likely hypothesis is that the malware’s developers are leveraging its accessibility to expand their user base rapidly. Overall confidence in this assessment is moderate due to existing information gaps regarding the malware’s full capabilities and distribution mechanisms.
2. Competing Hypotheses
- Hypothesis A: The Oblivion malware is primarily designed to target individual users for financial gain through unauthorized access to personal data. Supporting evidence includes its ability to capture sensitive information like bank codes and passwords. However, the extent of its targeting scope remains uncertain.
- Hypothesis B: Oblivion is part of a broader campaign aimed at corporate espionage, exploiting Android devices within organizational environments. This hypothesis is less supported due to the malware’s public availability and pricing model, which suggests a focus on individual rather than corporate targets.
- Assessment: Hypothesis A is currently better supported, given the malware’s features and pricing model that appeal to individual users seeking unauthorized access to personal data. Indicators such as targeted attacks on corporate networks could shift this assessment.
3. Key Assumptions and Red Flags
- Assumptions: The malware’s primary distribution method is through fake update notifications; the malware’s capabilities are accurately described by Certo researchers; the pricing model reflects the intended user base.
- Information Gaps: Details on the malware’s distribution network, the exact number of affected devices, and the identity of the developers remain unclear.
- Bias & Deception Risks: Potential bias in the source’s analysis due to commercial interests; possible deception by malware developers regarding the malware’s full capabilities or intended targets.
4. Implications and Strategic Risks
The proliferation of the Oblivion malware could lead to increased cybercrime activities and heightened security risks for Android users. Its accessibility may encourage more individuals to engage in unauthorized surveillance, impacting privacy and security.
- Political / Geopolitical: Potential for international tensions if state actors exploit the malware for espionage.
- Security / Counter-Terrorism: Increased risk of data breaches and unauthorized surveillance impacting national security.
- Cyber / Information Space: Potential for widespread data theft and disruption of digital ecosystems.
- Economic / Social: Potential economic impact due to increased cybersecurity costs and loss of consumer trust in Android devices.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase monitoring of Android app stores for fake updates, enhance public awareness campaigns about the risks of unauthorized app downloads.
- Medium-Term Posture (1–12 months): Develop partnerships with Android device manufacturers to improve security features, invest in research to identify and mitigate emerging malware threats.
- Scenario Outlook:
- Best: Rapid identification and patching of vulnerabilities, reducing the malware’s effectiveness.
- Worst: Widespread adoption of the malware leading to significant data breaches and financial losses.
- Most-Likely: Gradual increase in malware incidents with periodic disruptions as security measures catch up.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, malware, Android, data privacy, cybercrime, mobile security, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us