New DarkSword Toolkit Exposes iPhone Users to Data Theft via Infected Websites, Experts Warn
Published on: 2026-03-19
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: There’s an Easy Way to Stay Safe From the New ‘DarkSword’ iPhone Hackers
1. BLUF (Bottom Line Up Front)
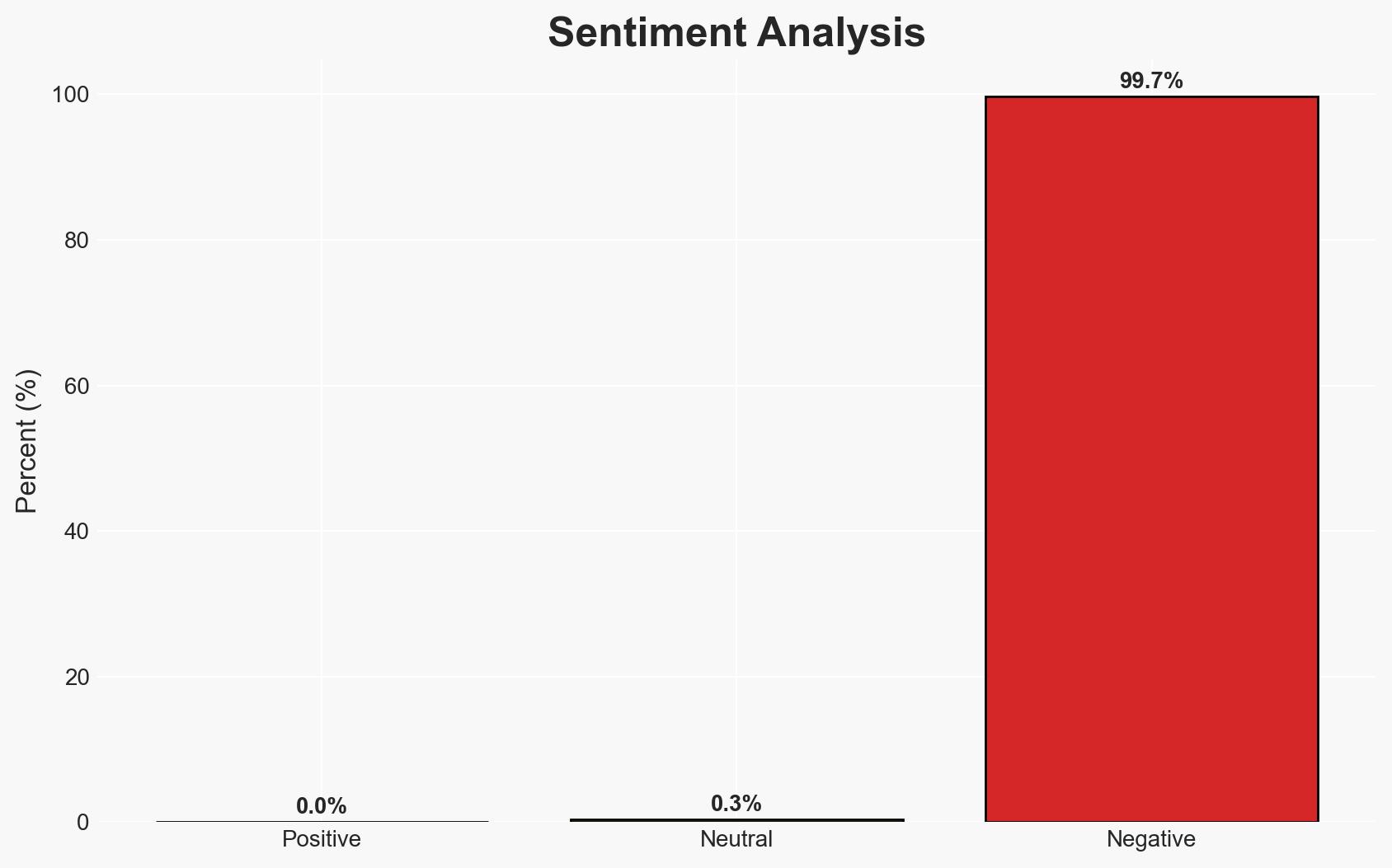
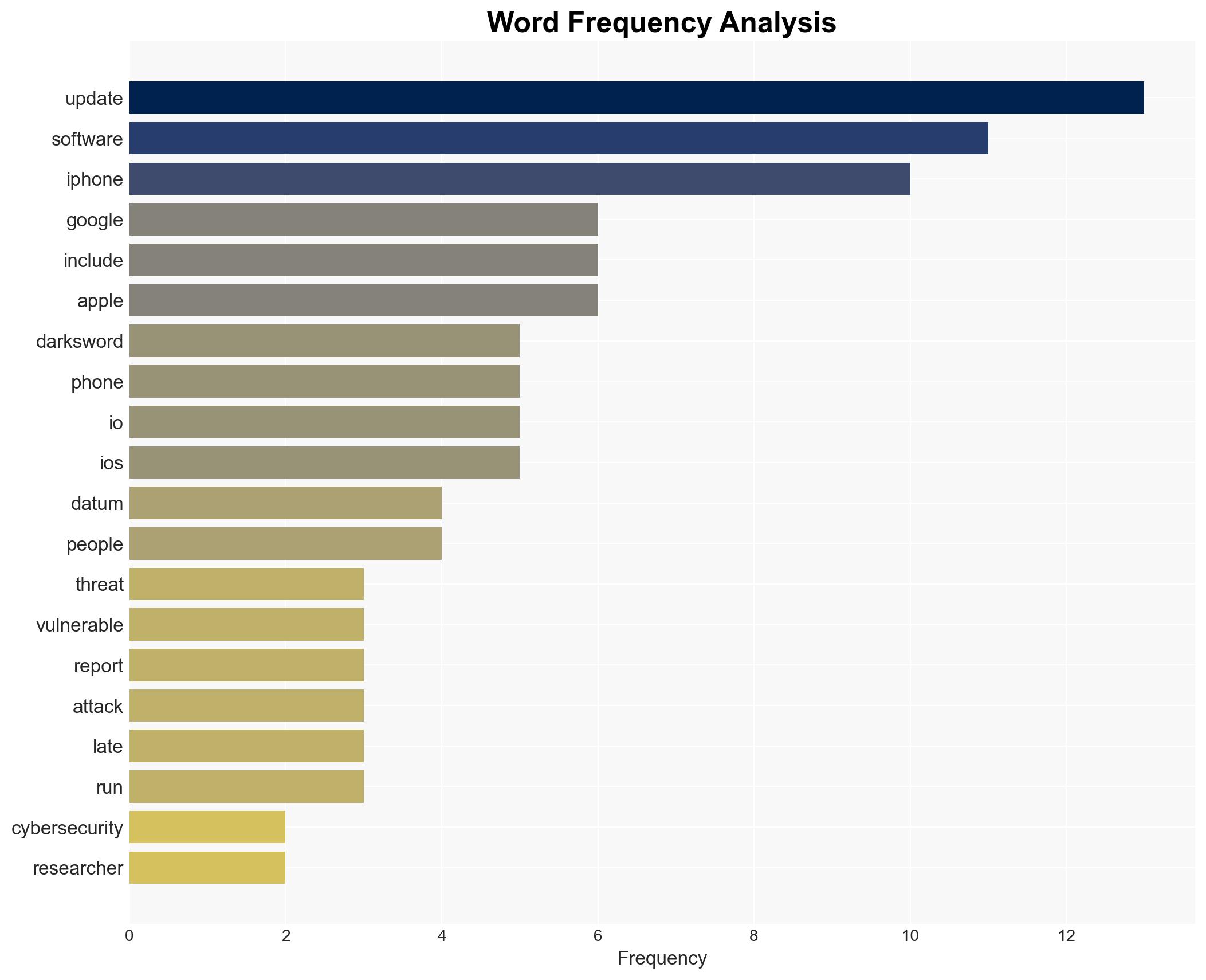
The DarkSword hacking toolkit poses a significant cybersecurity threat to iPhone users, particularly those running outdated software versions. The toolkit is sophisticated, targeting users through infected websites and is linked to both commercial surveillance vendors and suspected state-sponsored actors. The primary mitigation strategy is to ensure iOS software is updated. Overall confidence in this assessment is moderate due to limited geographical impact data and potential source biases.
2. Competing Hypotheses
- Hypothesis A: DarkSword is primarily a tool used by state-sponsored actors to target specific geopolitical regions. This is supported by its deployment in countries like Saudi Arabia, Turkey, Malaysia, and Ukraine, and its sophisticated nature. However, the involvement of commercial surveillance vendors introduces uncertainty about the primary actors.
- Hypothesis B: DarkSword is a commercially developed tool used broadly by various actors, including private entities, for financial or espionage purposes. The involvement of multiple surveillance vendors supports this, but the targeting of specific regions suggests a potential state-sponsored agenda.
- Assessment: Hypothesis A is currently better supported due to the geopolitical significance of the targeted countries and the sophisticated nature of the toolkit. Indicators such as broader geographical deployment or evidence of financial motivations could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The toolkit’s sophistication implies state-level involvement; updating iOS effectively mitigates the threat; the current geographical impact is limited to reported regions.
- Information Gaps: Lack of detailed attribution to specific state actors; unclear motivations behind targeting specific countries; potential underreporting of affected regions.
- Bias & Deception Risks: Source bias from cybersecurity firms with commercial interests; potential deception by state actors to obscure true origins or intentions.
4. Implications and Strategic Risks
The development of DarkSword could lead to increased geopolitical tensions, particularly if state-sponsored involvement is confirmed. The toolkit’s sophistication may prompt other actors to develop similar capabilities, escalating the cyber threat landscape.
- Political / Geopolitical: Potential diplomatic strains if state-sponsored involvement is confirmed; increased scrutiny on countries implicated in the toolkit’s use.
- Security / Counter-Terrorism: Heightened cybersecurity measures may be necessary; potential for increased cyber espionage activities.
- Cyber / Information Space: Risk of similar toolkits emerging; increased demand for cybersecurity solutions and updates.
- Economic / Social: Potential economic impact on affected regions; increased public concern over digital privacy and security.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Encourage rapid iOS updates; enhance monitoring of affected regions; engage with Apple and cybersecurity firms for intelligence sharing.
- Medium-Term Posture (1–12 months): Develop partnerships with international cybersecurity agencies; invest in research for detecting and mitigating similar threats; enhance public awareness campaigns.
- Scenario Outlook:
- Best: Effective mitigation through updates and international cooperation reduces threat.
- Worst: Expanded use of DarkSword leads to widespread data breaches and geopolitical tensions.
- Most-Likely: Continued targeted attacks with gradual improvements in detection and response capabilities.
6. Key Individuals and Entities
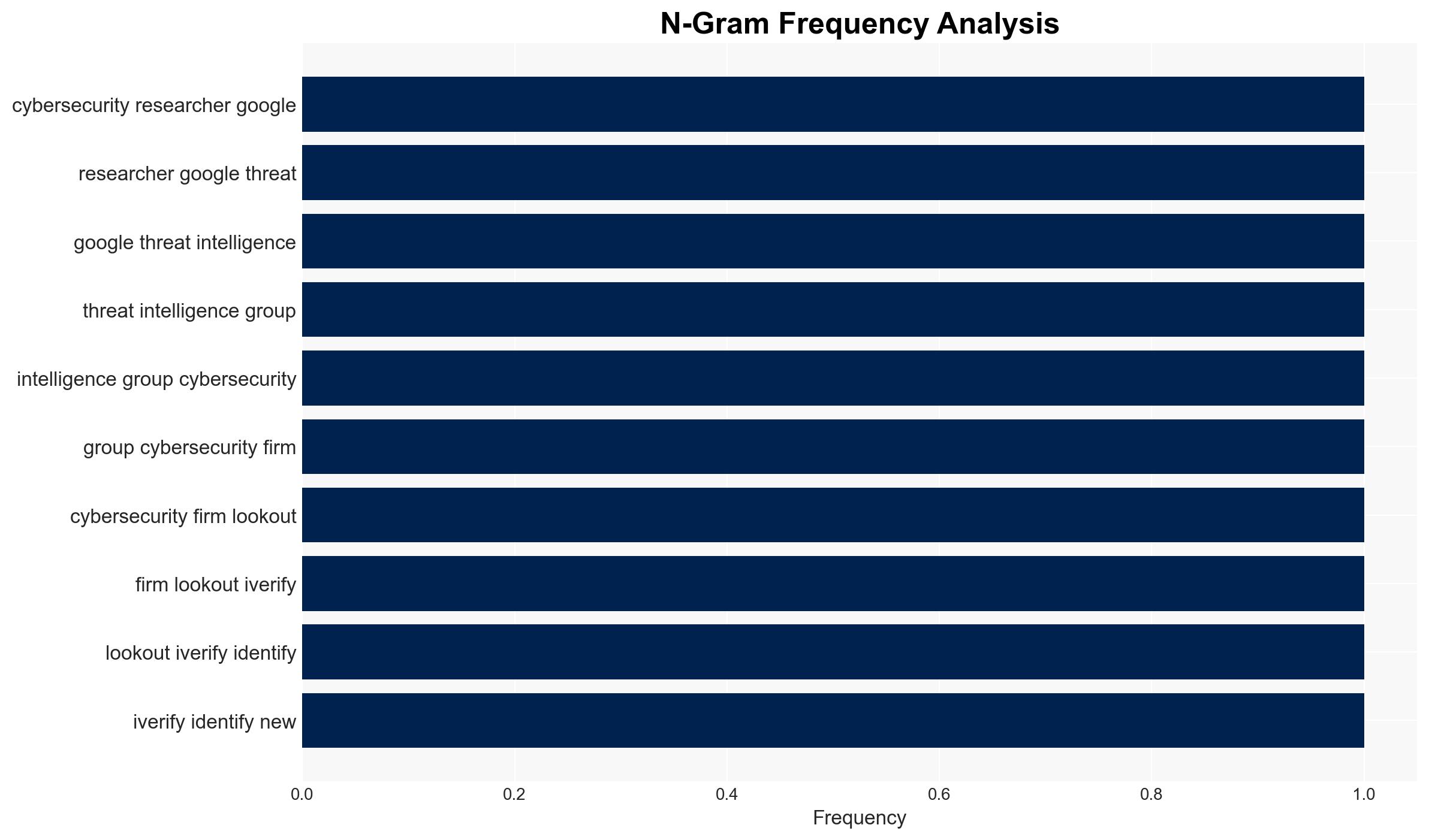
- Google’s Threat Intelligence Group
- Lookout
- iVerify
- Apple
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
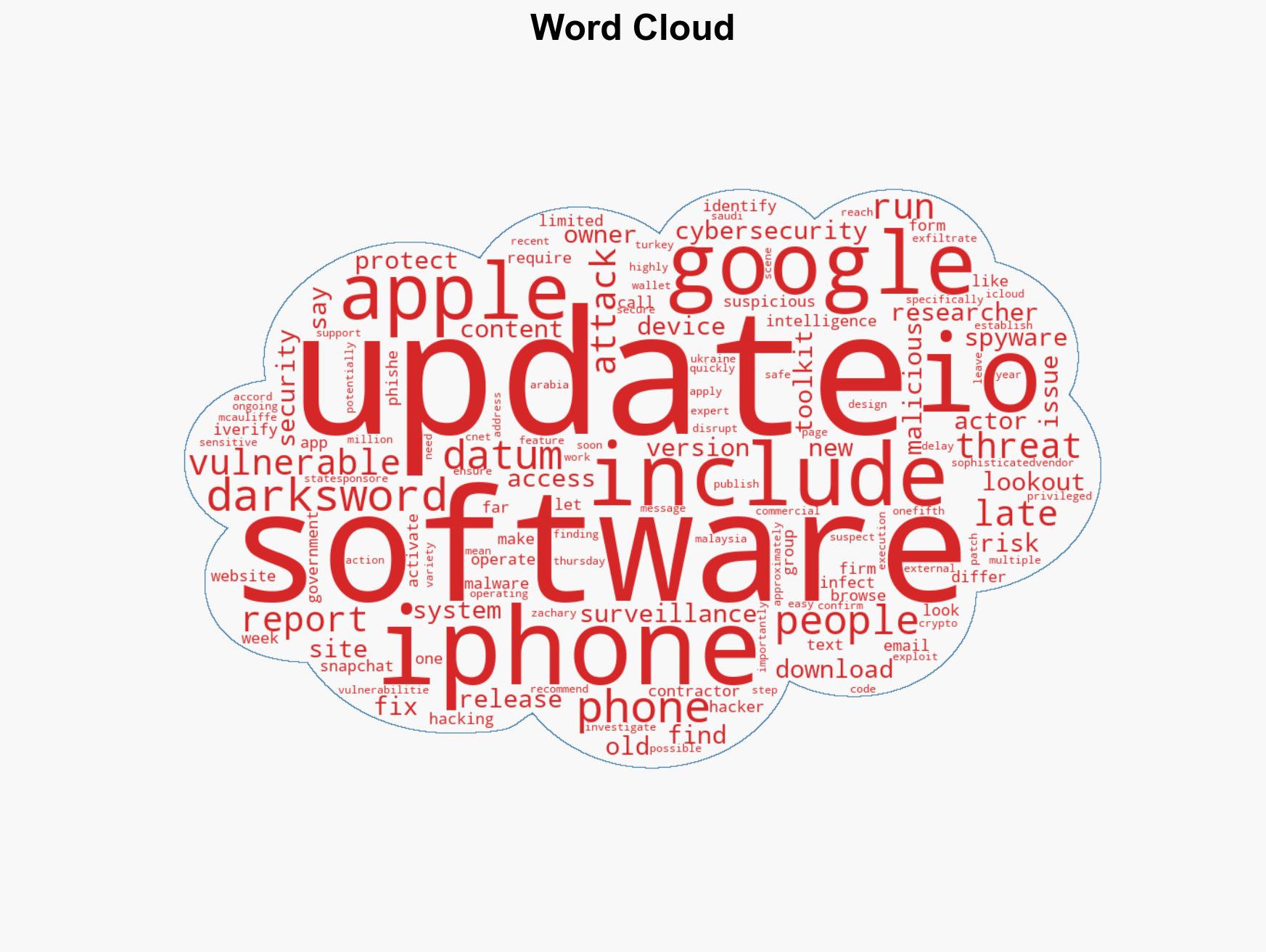
cybersecurity, state-sponsored actors, iOS vulnerabilities, cyber-espionage, digital privacy, geopolitical tensions
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us