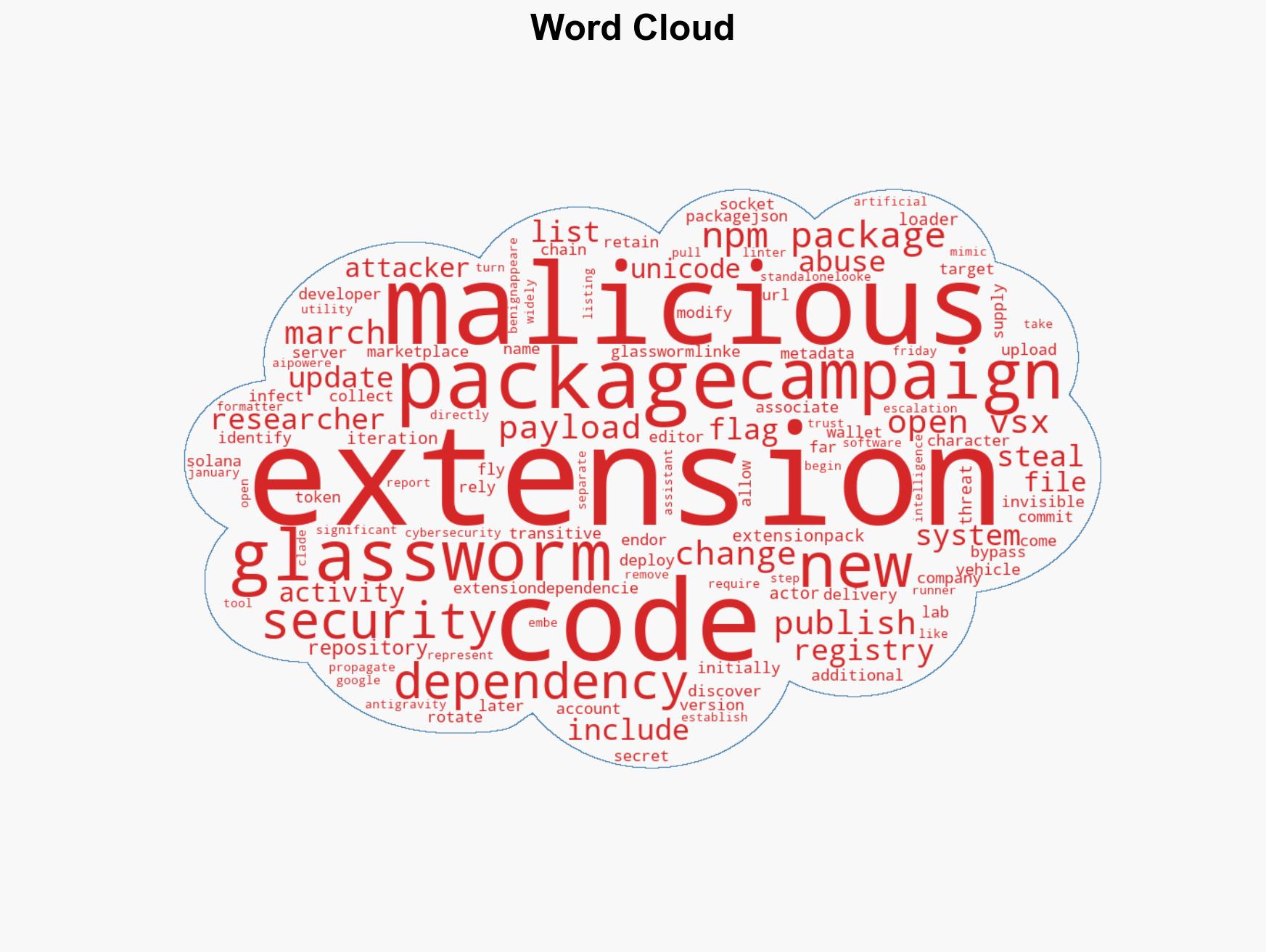
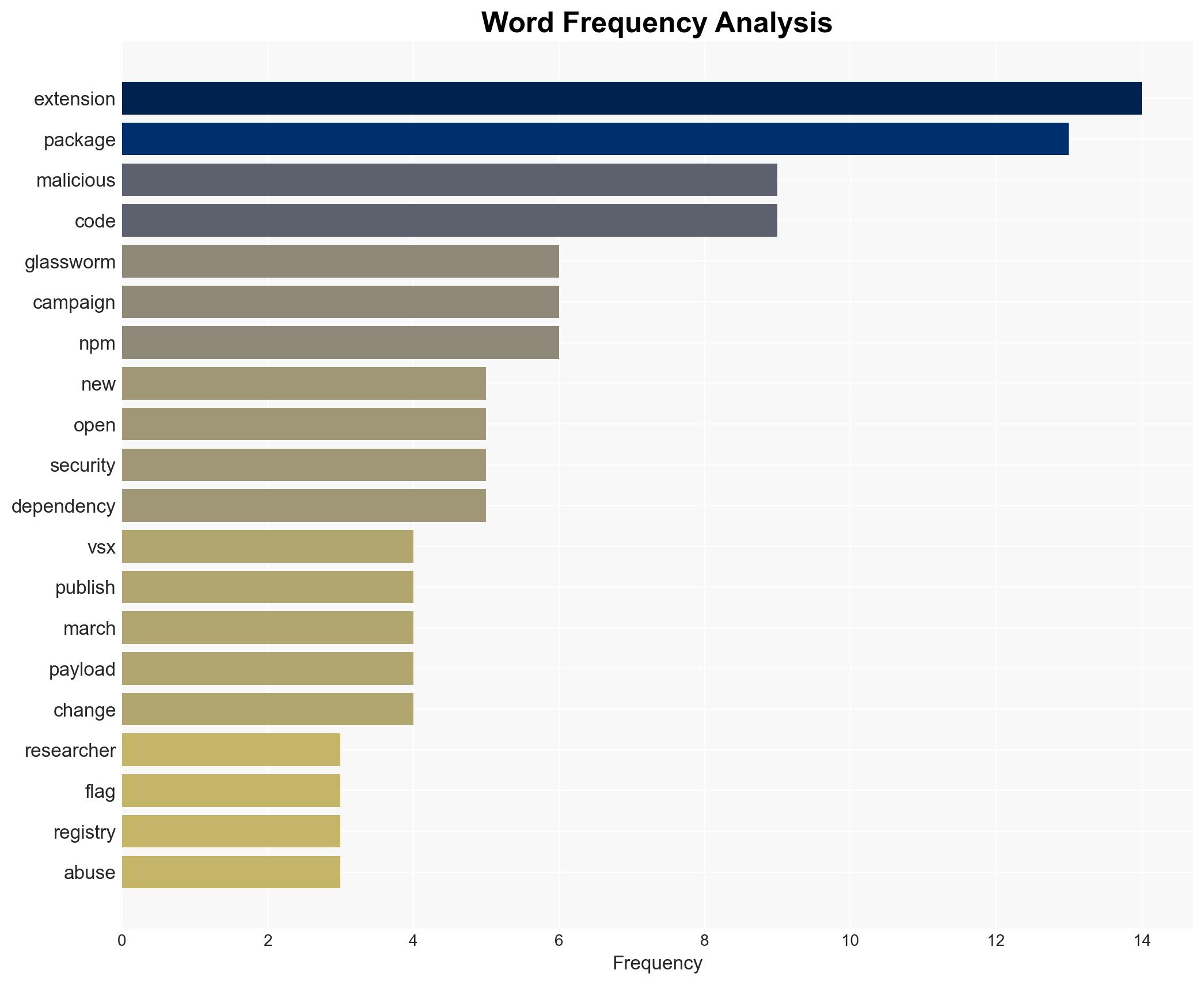
New GlassWorm Campaign Exploits 72 Open VSX Extensions to Compromise Developer Environments
Published on: 2026-03-14
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: GlassWorm Supply-Chain Attack Abuses 72 Open VSX Extensions to Target Developers
1. BLUF (Bottom Line Up Front)
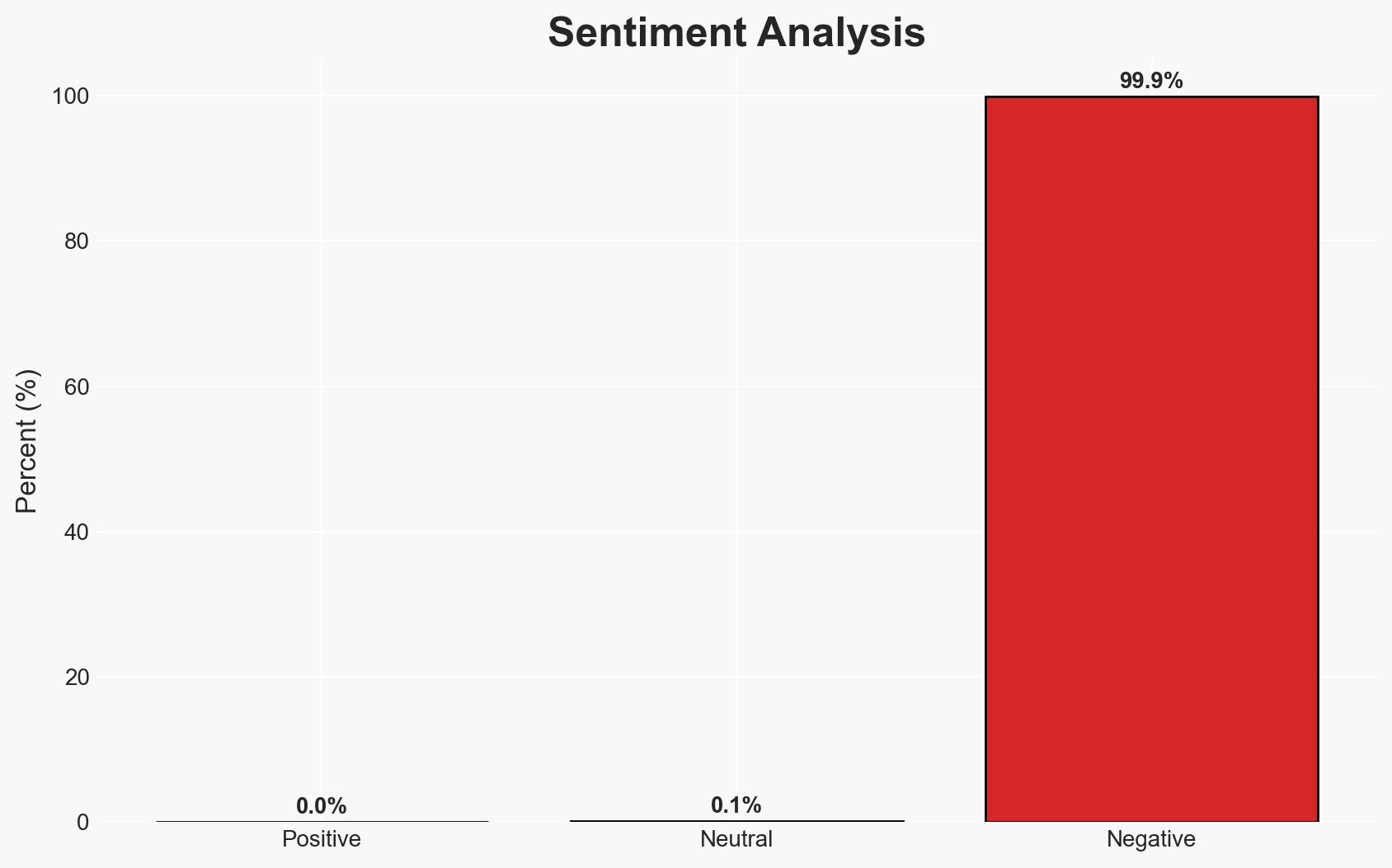
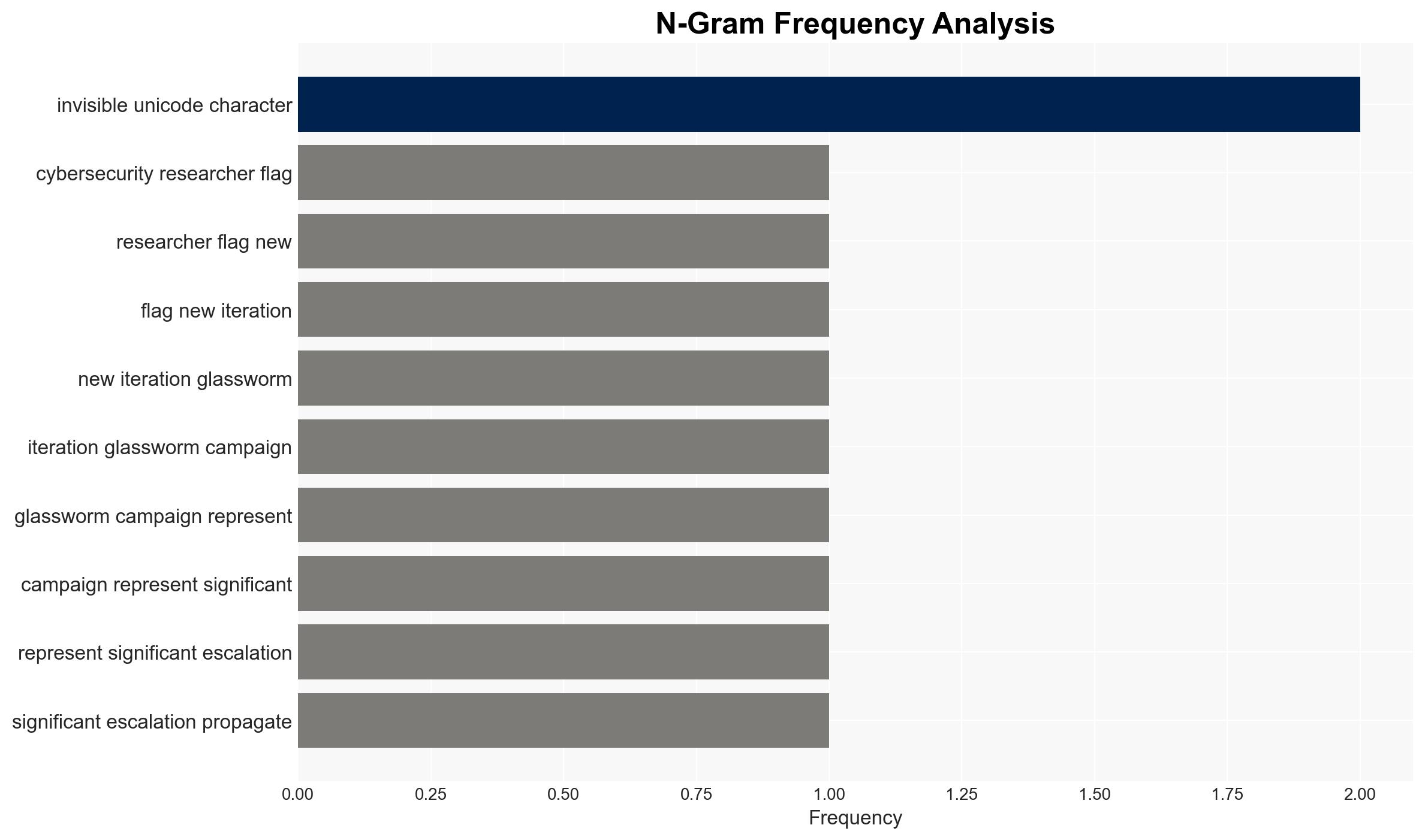
The GlassWorm campaign represents a significant escalation in supply-chain attacks targeting developers through the Open VSX registry. By exploiting extension dependencies, the campaign can covertly deliver malicious payloads, posing a substantial threat to software development environments. This attack primarily affects developers using widely adopted tools and extensions. Overall, there is moderate confidence in the assessment due to the evolving nature of the threat and limited visibility into the full scope of the campaign.
2. Competing Hypotheses
- Hypothesis A: The GlassWorm campaign is primarily motivated by financial gain through cryptocurrency theft and proxy abuse. Supporting evidence includes the use of Solana transactions and cryptocurrency wallet draining tactics. Contradicting evidence is the lack of explicit financial demands or ransom notes.
- Hypothesis B: The campaign aims to establish a broad network of compromised systems for future cyber operations, possibly state-sponsored. Supporting evidence includes sophisticated obfuscation techniques and the strategic targeting of developer tools. Contradicting evidence is the absence of direct links to state actors or geopolitical motives.
- Assessment: Hypothesis A is currently better supported due to the direct financial implications observed. However, indicators such as increased sophistication or geopolitical targeting could shift this judgment towards Hypothesis B.
3. Key Assumptions and Red Flags
- Assumptions: The campaign’s primary goal is financial gain; developers are the main target; Open VSX’s removal of extensions mitigates immediate risk; GlassWorm’s tactics will continue to evolve.
- Information Gaps: Full list of affected extensions; identity of the threat actor; extent of compromised systems; long-term objectives of the campaign.
- Bias & Deception Risks: Potential bias in attributing financial motives without considering broader strategic objectives; risk of deception through false-flag operations or misattribution.
4. Implications and Strategic Risks
The GlassWorm campaign could lead to increased scrutiny of software supply chains and heightened security measures in developer environments. Over time, this may drive changes in how software dependencies are managed and reviewed.
- Political / Geopolitical: Potential for increased tensions if state-sponsored involvement is suspected or confirmed.
- Security / Counter-Terrorism: Heightened risk of similar tactics being adopted by other threat actors, increasing the overall threat landscape.
- Cyber / Information Space: Potential for widespread disruption in software development processes and trust in open-source platforms.
- Economic / Social: Possible economic impacts on companies reliant on compromised tools, leading to broader industry instability.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of Open VSX and similar platforms; conduct security audits of developer environments; increase awareness among developers.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for threat intelligence sharing; invest in supply chain security technologies; establish incident response protocols.
- Scenario Outlook: Best: Rapid containment and mitigation of the campaign; Worst: Expansion of the campaign with significant economic and security impacts; Most-Likely: Continued evolution of tactics with moderate disruption.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, supply-chain attack, malware campaign, software development, Open VSX, financial cybercrime, developer tools
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us