New Malware Variant RESURGE Exploits Ivanti Vulnerability – Infosecurity Magazine
Published on: 2025-03-31
Intelligence Report: New Malware Variant RESURGE Exploits Ivanti Vulnerability – Infosecurity Magazine
1. BLUF (Bottom Line Up Front)
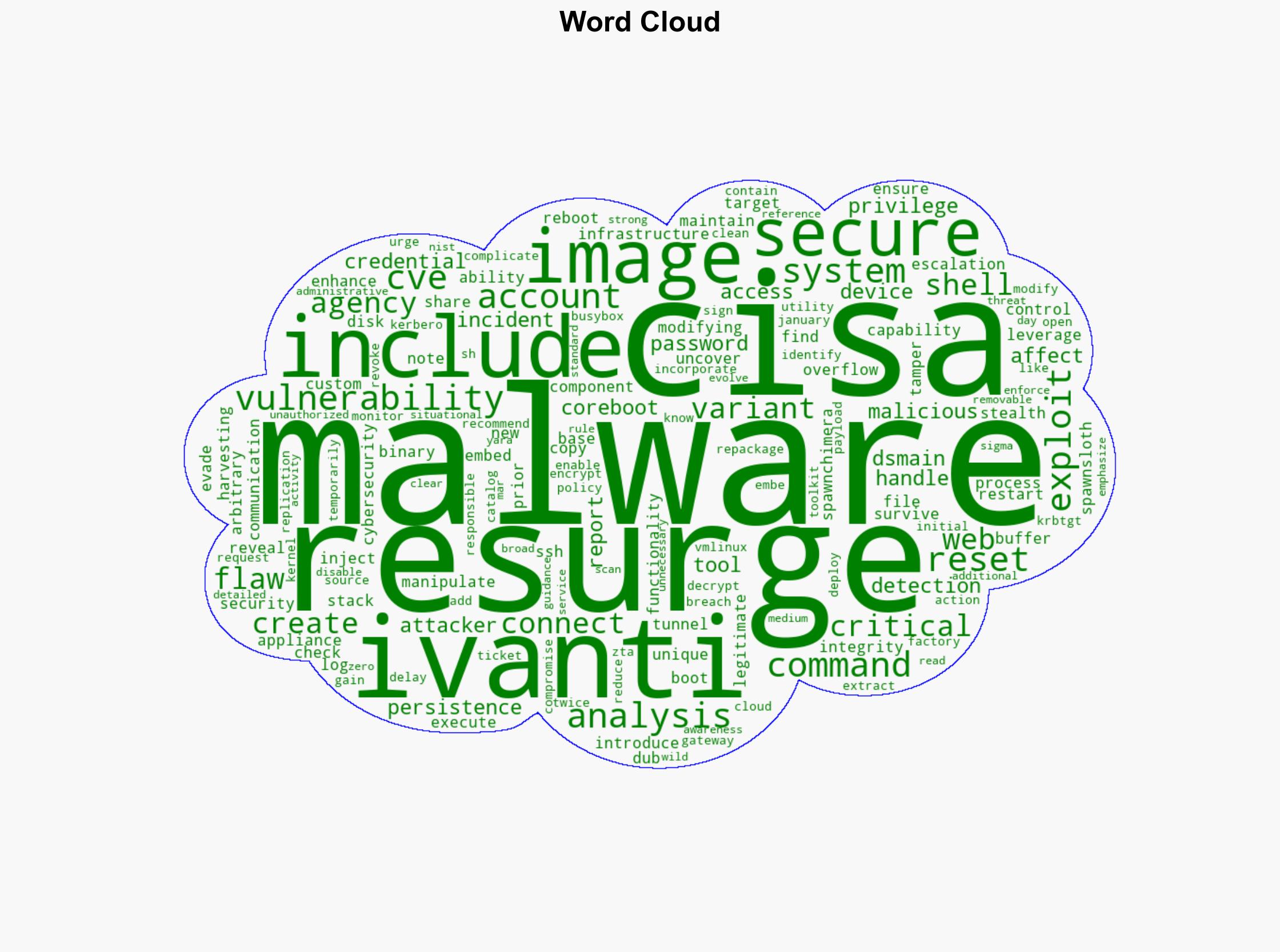
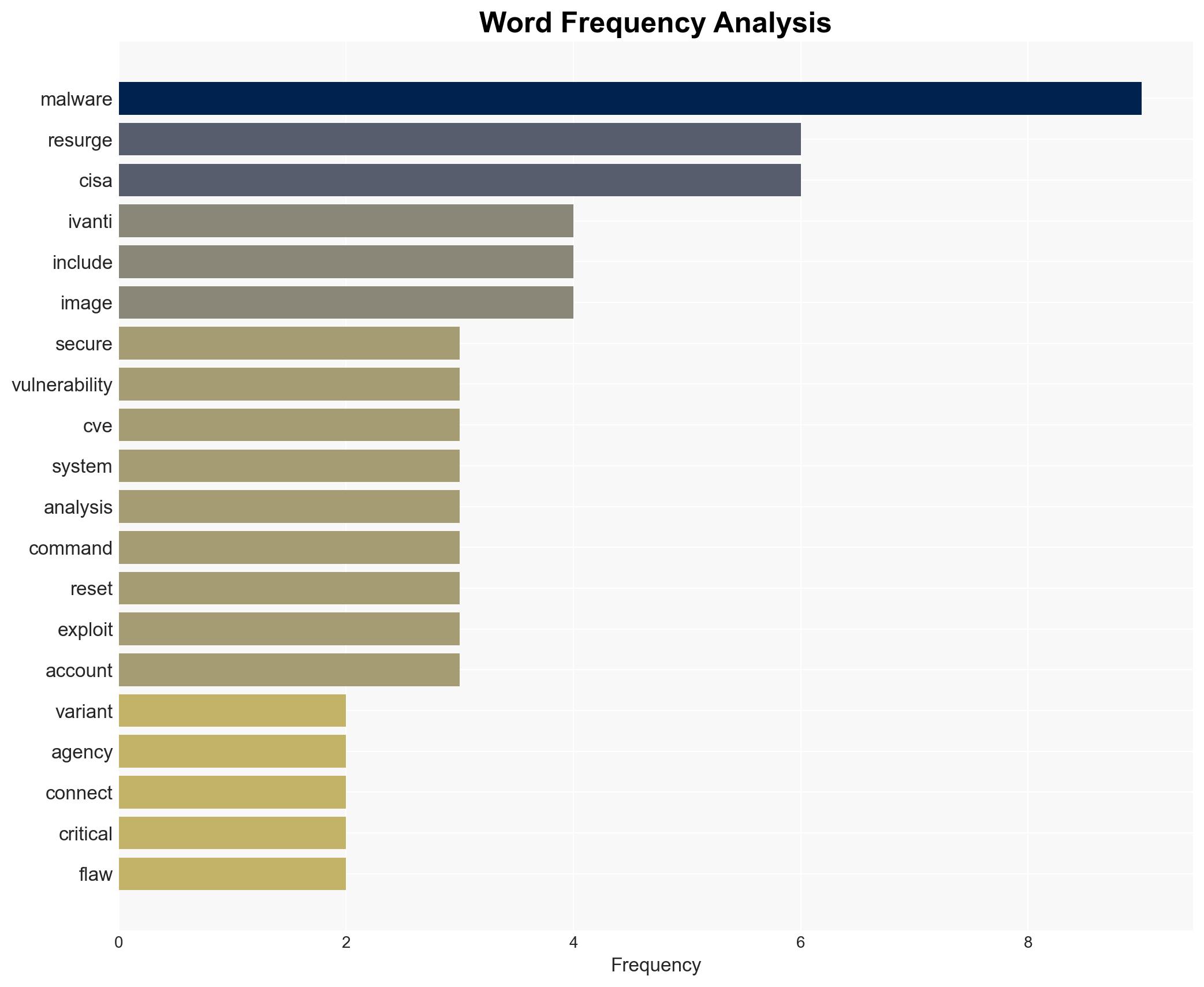
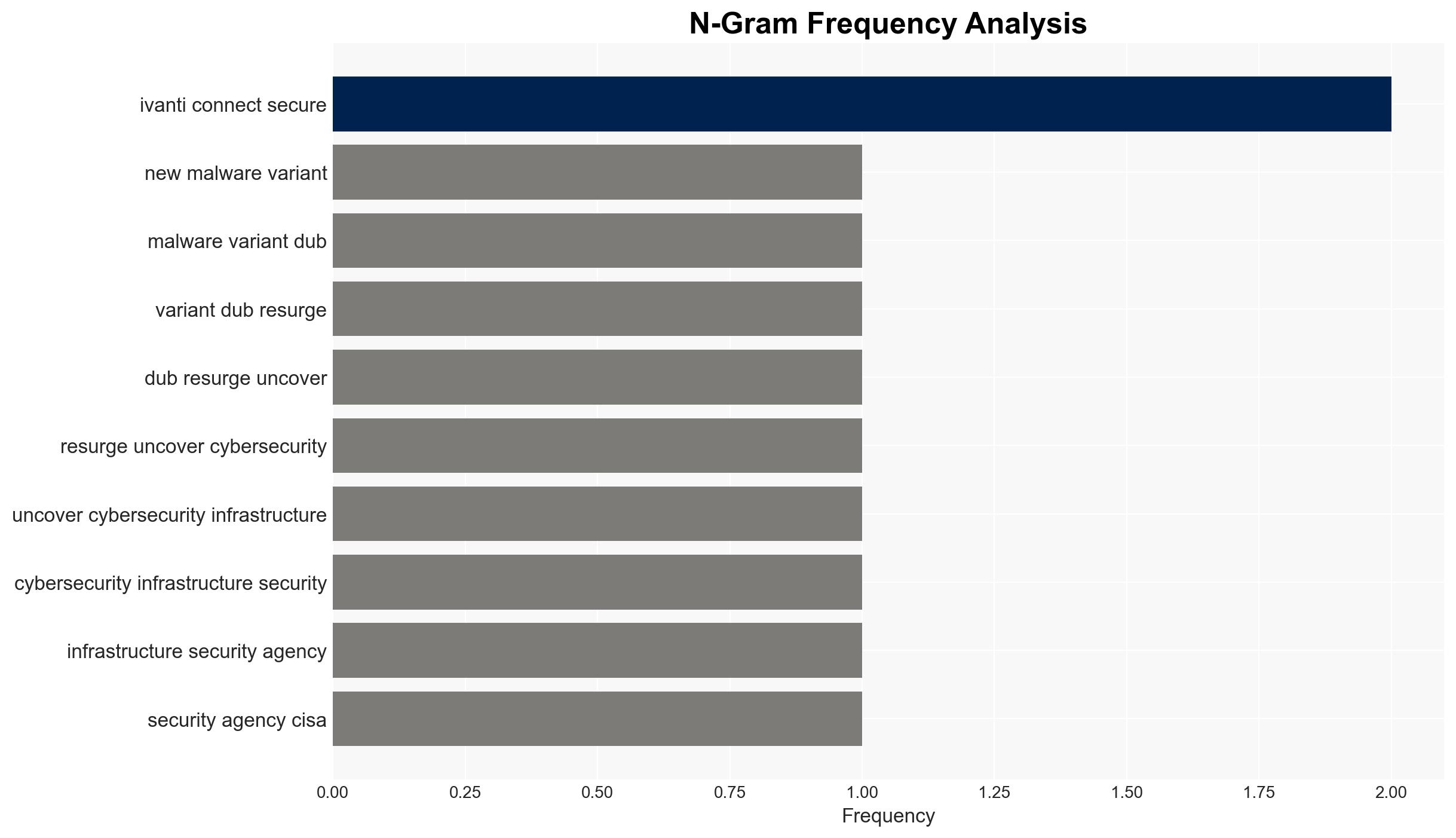
The newly identified malware variant, RESURGE, exploits a critical vulnerability in Ivanti’s Connect Secure appliance. This vulnerability, identified as CVE, allows attackers to manipulate system files and maintain persistence through system reboots. The malware’s capabilities include credential harvesting, privilege escalation, and the creation of a command and control communication channel. Immediate action is recommended to mitigate the threat, including system resets and enhanced monitoring.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
RESURGE represents an evolution in malware sophistication, sharing functionalities with previous threats such as SpawnChimera, but introducing enhanced stealth and persistence capabilities. The malware utilizes a stack-based buffer overflow flaw to deploy a web shell, enabling remote command execution. It also incorporates open-source tools to modify kernel images, complicating detection efforts. The inclusion of a custom binary, DSMaintain, further facilitates unauthorized access and persistence.
3. Implications and Strategic Risks
The exploitation of Ivanti’s vulnerability by RESURGE poses significant risks to national security and economic stability. The malware’s ability to execute arbitrary commands and reset passwords could lead to unauthorized access to sensitive information. The potential for widespread disruption in sectors reliant on Ivanti’s technology is substantial, necessitating immediate attention from cybersecurity agencies and affected organizations.
4. Recommendations and Outlook
Recommendations:
- Conduct a factory reset of compromised devices and deploy clean images from cloud systems.
- Reset credentials for all accounts, including the KRBTGT account, to prevent unauthorized access.
- Implement strong password policies and disable unnecessary services to reduce attack surfaces.
- Enhance monitoring of administrative accounts for signs of unauthorized activity.
- Submit malware samples to relevant agencies for further analysis and development of detection rules.
Outlook:
In the best-case scenario, swift implementation of recommended actions will mitigate the threat of RESURGE, preventing further exploitation. The worst-case scenario involves widespread compromise of systems, leading to significant data breaches and operational disruptions. The most likely outcome is a moderate level of impact, with affected entities taking steps to contain and remediate the threat.
5. Key Individuals and Entities
The report mentions significant individuals and organizations involved in the analysis and response to the RESURGE threat. These include Ivanti, CISA, and other cybersecurity entities. Their roles and affiliations are not specified in this report.