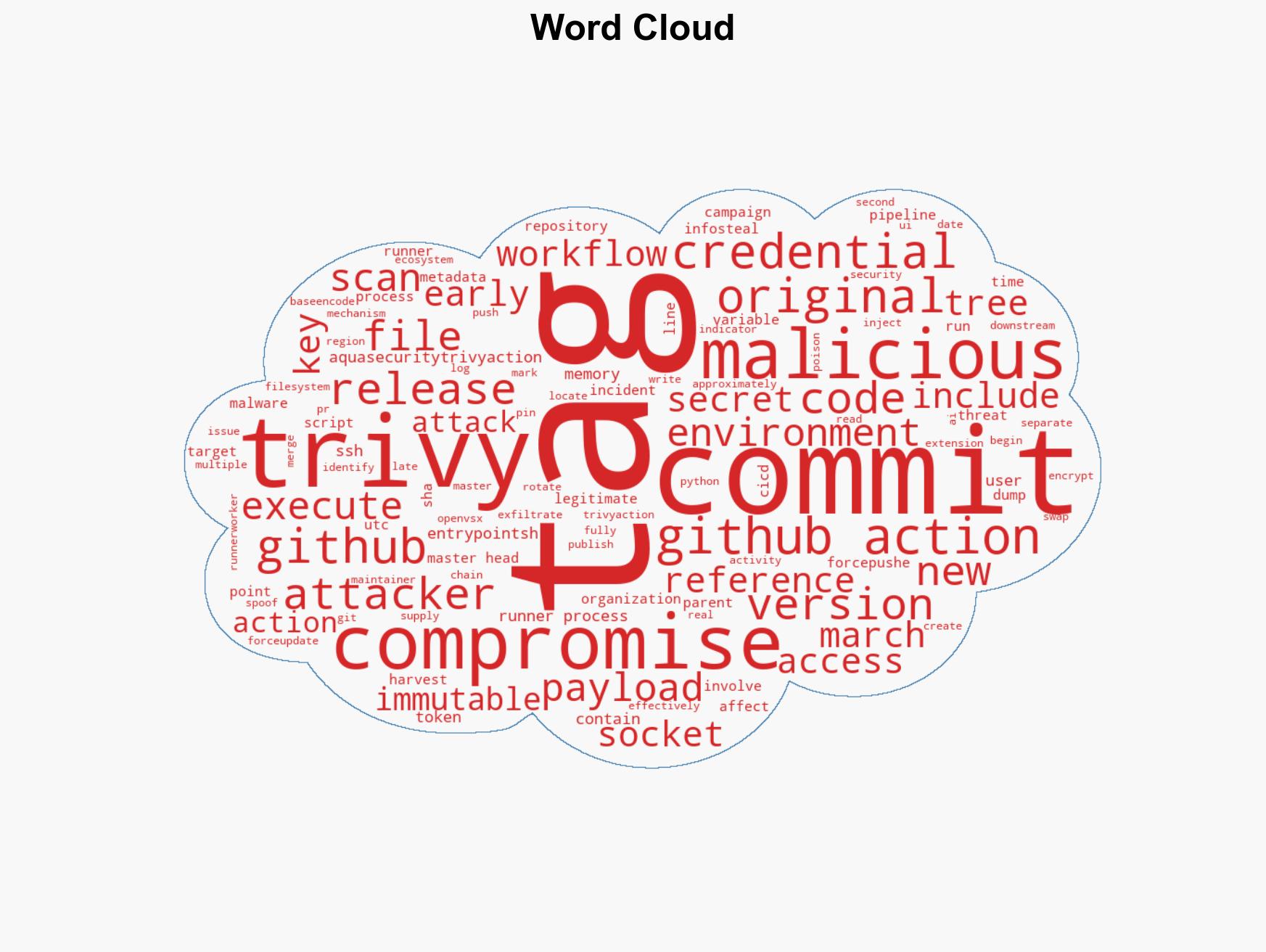
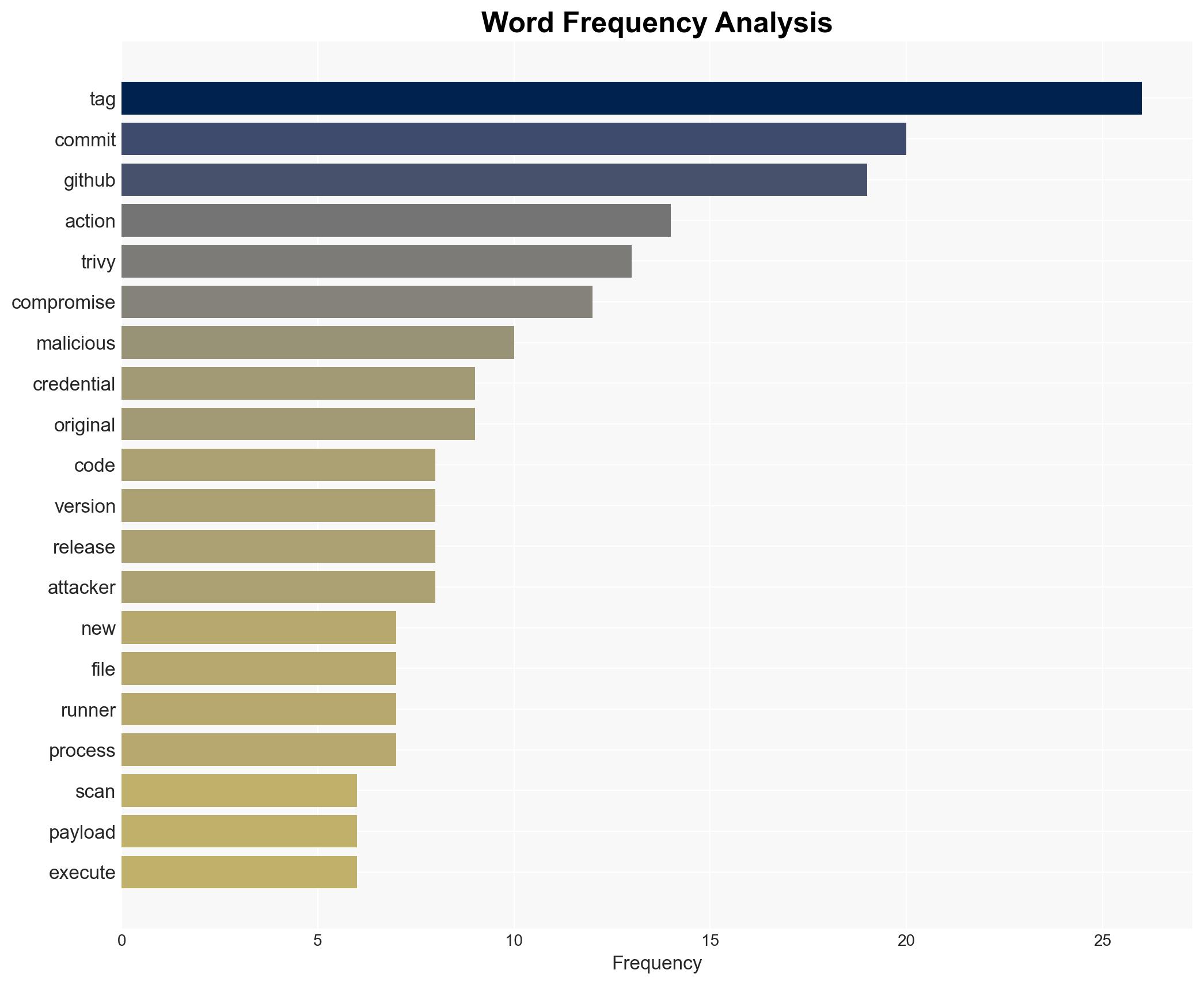
New Supply Chain Attack Targets Trivy, Compromising GitHub Actions Tags and Affecting CI/CD Workflows
Published on: 2026-03-22
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Trivy under attack again Widespread GitHub Actions tag compromise secrets
1. BLUF (Bottom Line Up Front)
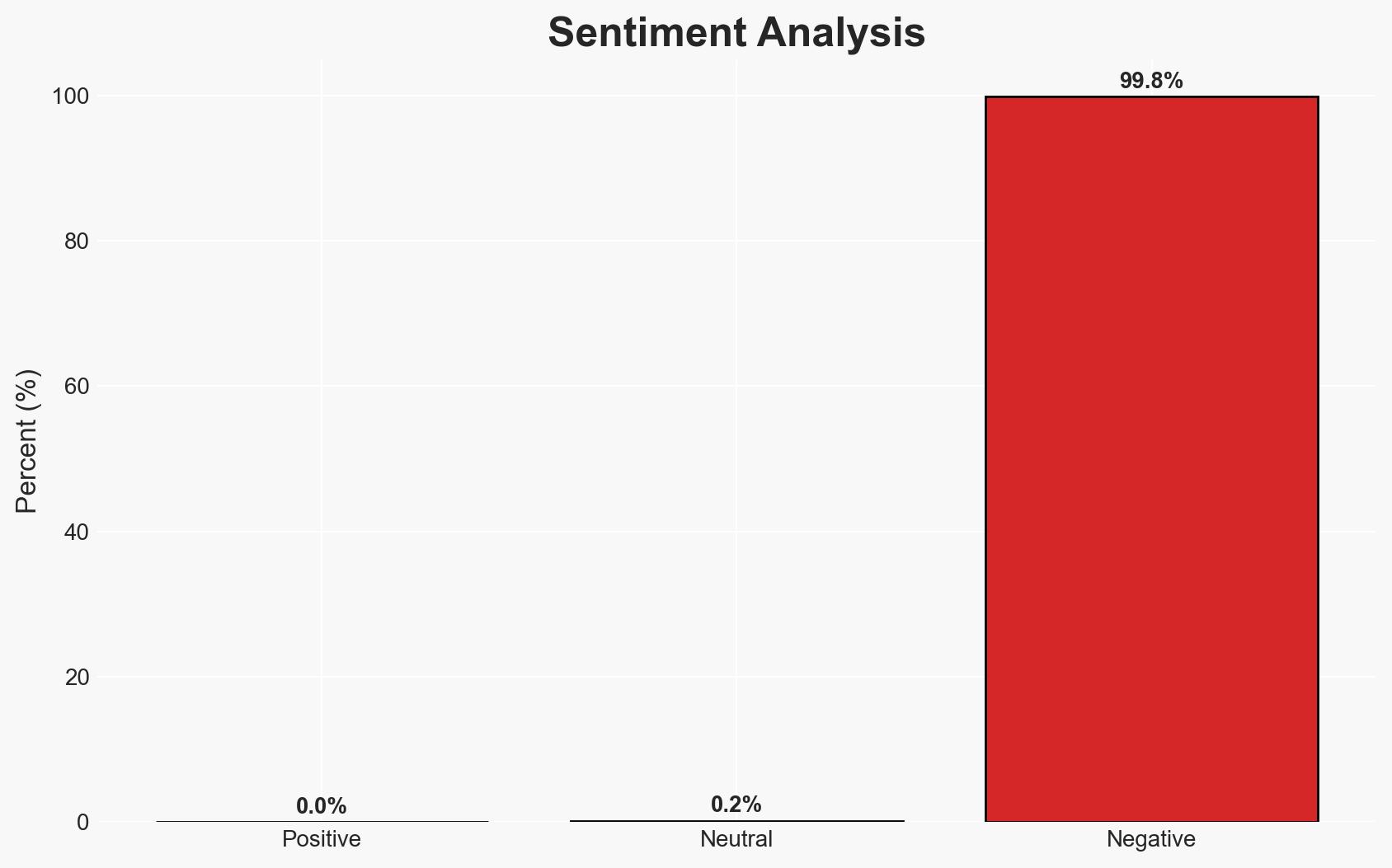
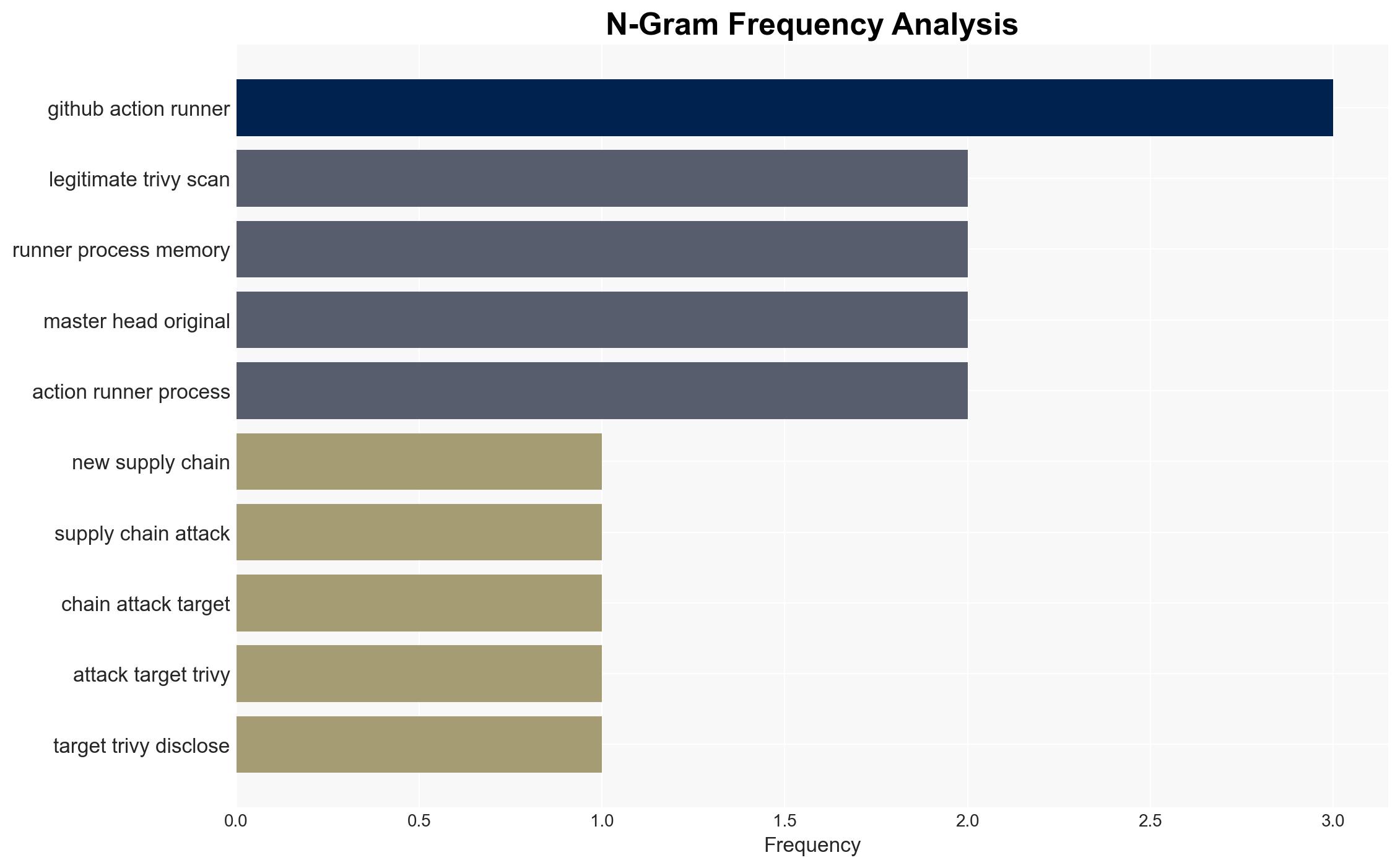
The Trivy ecosystem has experienced a second supply chain attack in March, compromising GitHub Actions tags and potentially affecting over 10,000 CI/CD workflows. The attack exploits compromised credentials, turning trusted version tags into vectors for malware distribution. The overall confidence in this assessment is moderate, given the ongoing investigation and incomplete data.
2. Competing Hypotheses
- Hypothesis A: The attack is a continuation of the earlier March breach, exploiting previously exfiltrated credentials. Supporting evidence includes the timing and method of compromise, but uncertainty remains regarding the attacker’s identity and broader objectives.
- Hypothesis B: The attack is an independent incident, possibly by a different actor exploiting newly discovered vulnerabilities. This is less supported due to the lack of evidence for new vulnerabilities and the reuse of compromised credentials.
- Assessment: Hypothesis A is currently better supported due to the continuity in attack methods and the use of previously compromised credentials. Indicators that could shift this judgment include discovery of new vulnerabilities or different attack signatures.
3. Key Assumptions and Red Flags
- Assumptions: The attack leverages previously compromised credentials; the malicious payload targets sensitive CI/CD environment data; the attack is financially or strategically motivated.
- Information Gaps: Details on the attacker’s identity and objectives; full scope of affected systems; effectiveness of credential rotation post-breach.
- Bias & Deception Risks: Potential bias in attributing the attack to the same actor without conclusive evidence; deception risk from attacker misinformation or false flags.
4. Implications and Strategic Risks
This development could lead to increased scrutiny on supply chain security and prompt broader security reforms in CI/CD practices. The attack may also influence geopolitical tensions if state actors are implicated.
- Political / Geopolitical: Potential for increased tensions if linked to state-sponsored actors.
- Security / Counter-Terrorism: Heightened alert for similar supply chain attacks across other platforms.
- Cyber / Information Space: Increased focus on securing CI/CD pipelines and dependency management.
- Economic / Social: Potential financial impact on affected organizations and erosion of trust in open-source ecosystems.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct thorough audits of CI/CD pipelines; rotate credentials and implement stricter access controls; monitor for further malicious activity.
- Medium-Term Posture (1–12 months): Develop partnerships for threat intelligence sharing; enhance supply chain security measures; invest in advanced detection capabilities.
- Scenario Outlook: Best: Rapid containment and patching with minimal impact. Worst: Widespread exploitation leading to significant data breaches. Most-Likely: Gradual mitigation with increased security awareness and policy changes.
6. Key Individuals and Entities
- Paul McCarty (disclosed the attack)
- Aqua Security (maintains Trivy)
- Socket (detected the attack)
- Not clearly identifiable from open sources in this snippet (attacker identity)
7. Thematic Tags
cybersecurity, supply chain attack, cyber security, GitHub Actions, CI/CD pipelines, malware distribution, credential compromise, open-source security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us