New Tool Developed to Identify Covert BPFDoor Backdoors in Critical Telecom Networks
Published on: 2026-03-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Researchers release tool to detect stealthy BPFDoor implants in critical infrastructure networks
1. BLUF (Bottom Line Up Front)
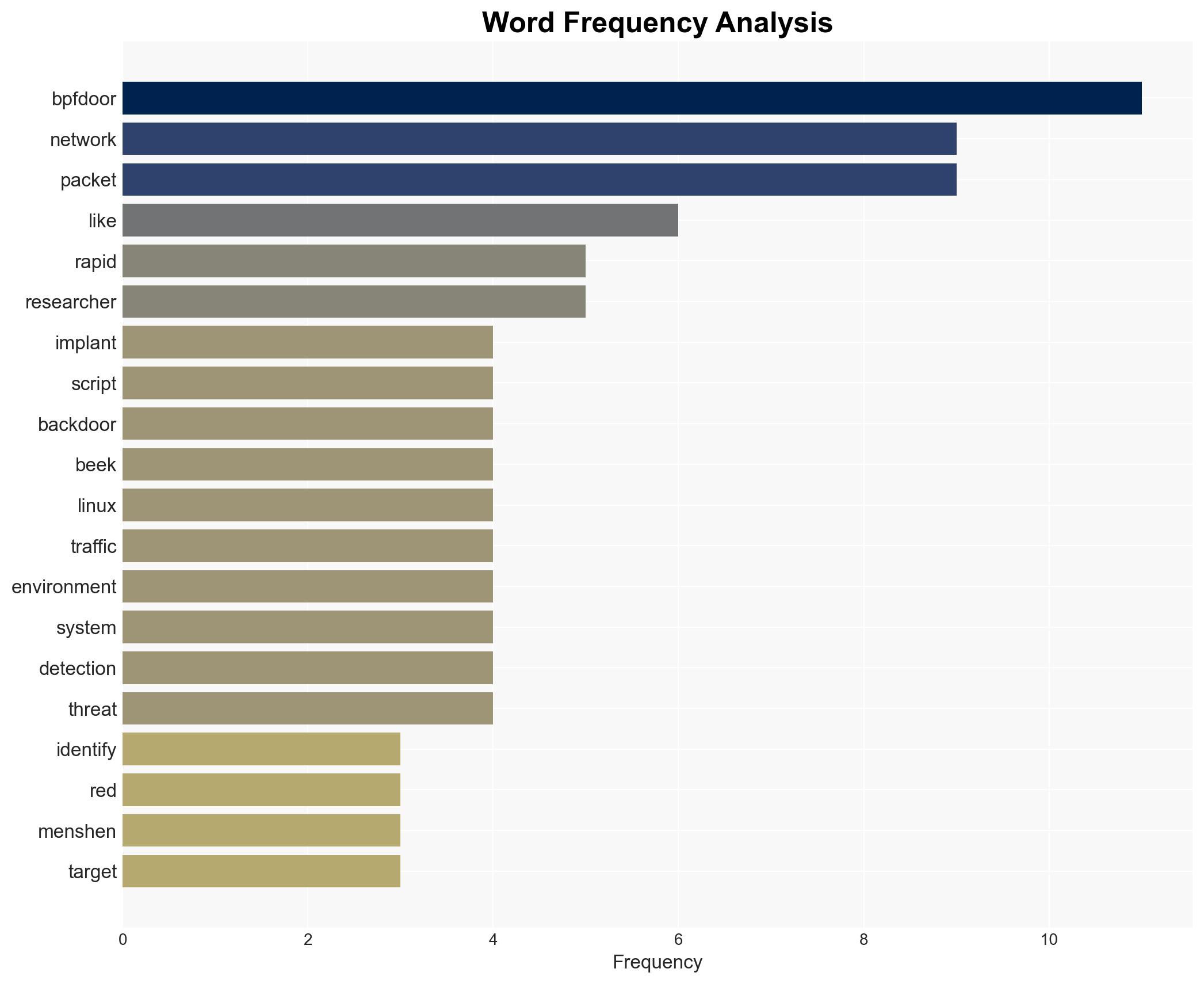
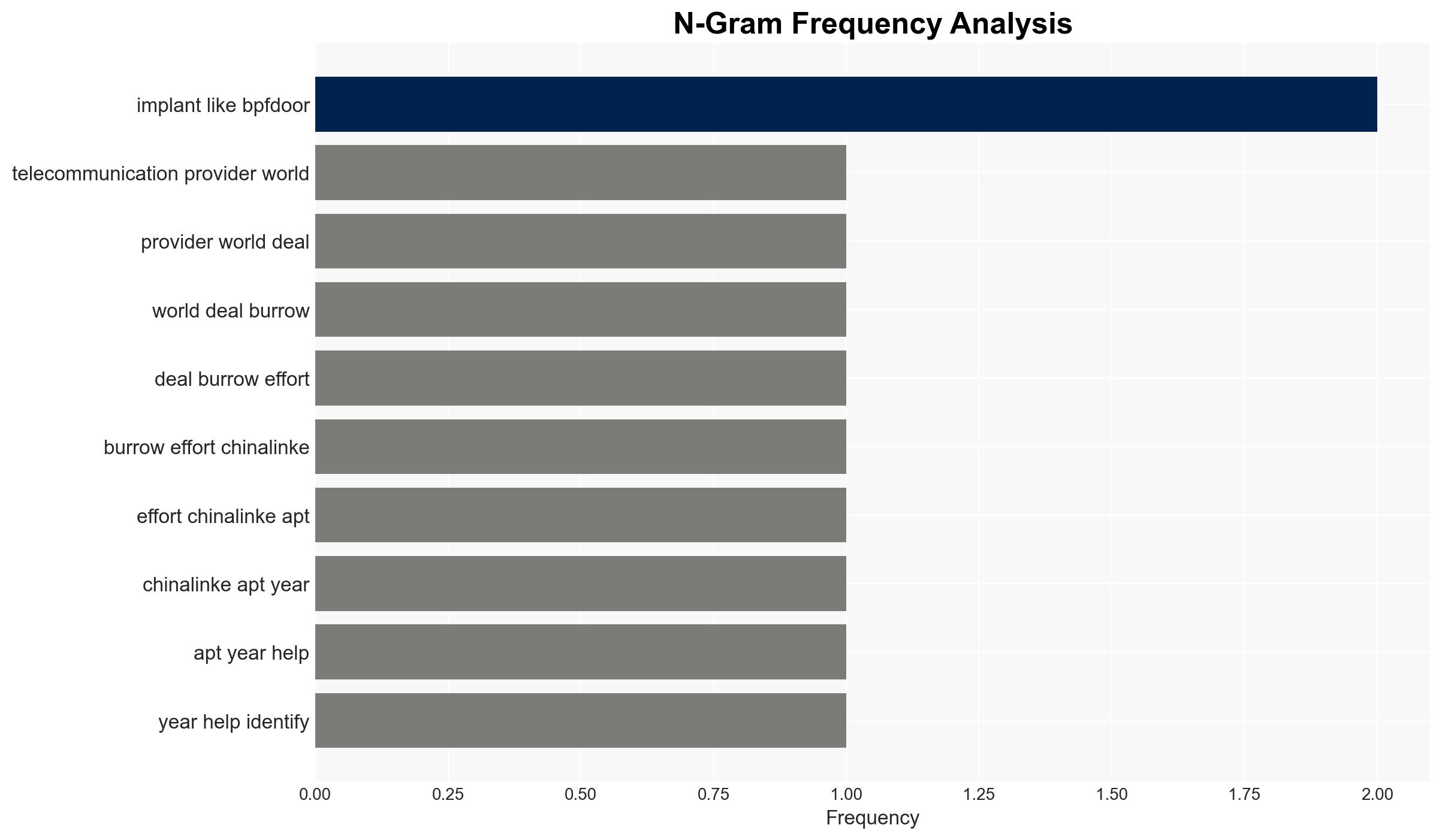
The release of a detection tool by Rapid7 to identify BPFDoor implants represents a significant step in countering the cyber threat posed by China-linked APT groups, particularly Red Menshen. This development primarily affects telecommunications and critical infrastructure sectors globally. The most likely hypothesis is that the tool will enhance detection capabilities, but the threat actors may adapt their tactics. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The detection tool will significantly disrupt Red Menshen’s operations by enabling telecommunications providers to identify and remove BPFDoor implants. Supporting evidence includes the tool’s ability to detect hard-to-spot kernel-level implants. However, uncertainty remains regarding the adaptability of Red Menshen to this new defensive measure.
- Hypothesis B: Red Menshen will adapt to the new detection capabilities, potentially developing more sophisticated implants or altering their tactics to evade detection. This is supported by the group’s history of evolving techniques and the inherent adaptability of APT groups. Contradicting evidence includes the immediate impact of the detection tool on current BPFDoor deployments.
- Assessment: Hypothesis B is currently better supported due to the historical adaptability of APT groups like Red Menshen. Indicators that could shift this judgment include evidence of widespread removal of BPFDoor implants without corresponding adaptation by the threat actors.
3. Key Assumptions and Red Flags
- Assumptions: The detection tool is effective across different BPFDoor variants; Red Menshen is primarily targeting telecommunications sectors; APT groups will continue to prioritize stealth and persistence.
- Information Gaps: Detailed effectiveness metrics of the detection tool; Red Menshen’s current operational adjustments; full scope of BPFDoor’s deployment across sectors.
- Bias & Deception Risks: Potential over-reliance on Rapid7’s analysis; possible underestimation of Red Menshen’s adaptability; deception by threat actors to mislead detection efforts.
4. Implications and Strategic Risks
This development could lead to a temporary reduction in Red Menshen’s operational effectiveness, but may also drive the group to innovate further. The broader dynamics of cyber defense and offense will continue to evolve as both sides adapt.
- Political / Geopolitical: Increased tensions between affected nations and China, potential for diplomatic confrontations.
- Security / Counter-Terrorism: Enhanced detection capabilities may reduce immediate threats but could lead to more sophisticated future attacks.
- Cyber / Information Space: Potential shift in cyber defense strategies, increased focus on kernel-level threats.
- Economic / Social: Potential disruptions to telecommunications services, increased costs for enhanced cybersecurity measures.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Deploy the detection tool across vulnerable networks, conduct comprehensive threat assessments, and increase monitoring for Red Menshen activity.
- Medium-Term Posture (1–12 months): Develop partnerships for intelligence sharing, invest in advanced threat detection capabilities, and enhance incident response protocols.
- Scenario Outlook:
- Best: Significant reduction in BPFDoor incidents, leading to improved cybersecurity posture.
- Worst: Red Menshen adapts quickly, deploying more sophisticated implants undetected by current tools.
- Most-Likely: Temporary disruption of Red Menshen activities, followed by gradual adaptation and resumption of operations.
6. Key Individuals and Entities
- Red Menshen (China-linked APT group)
- Rapid7 (Cybersecurity firm)
- Christiaan Beek (VP of Cyber Intelligence at Rapid7)
- Salt Typhoon (China-linked APT group)
7. Thematic Tags
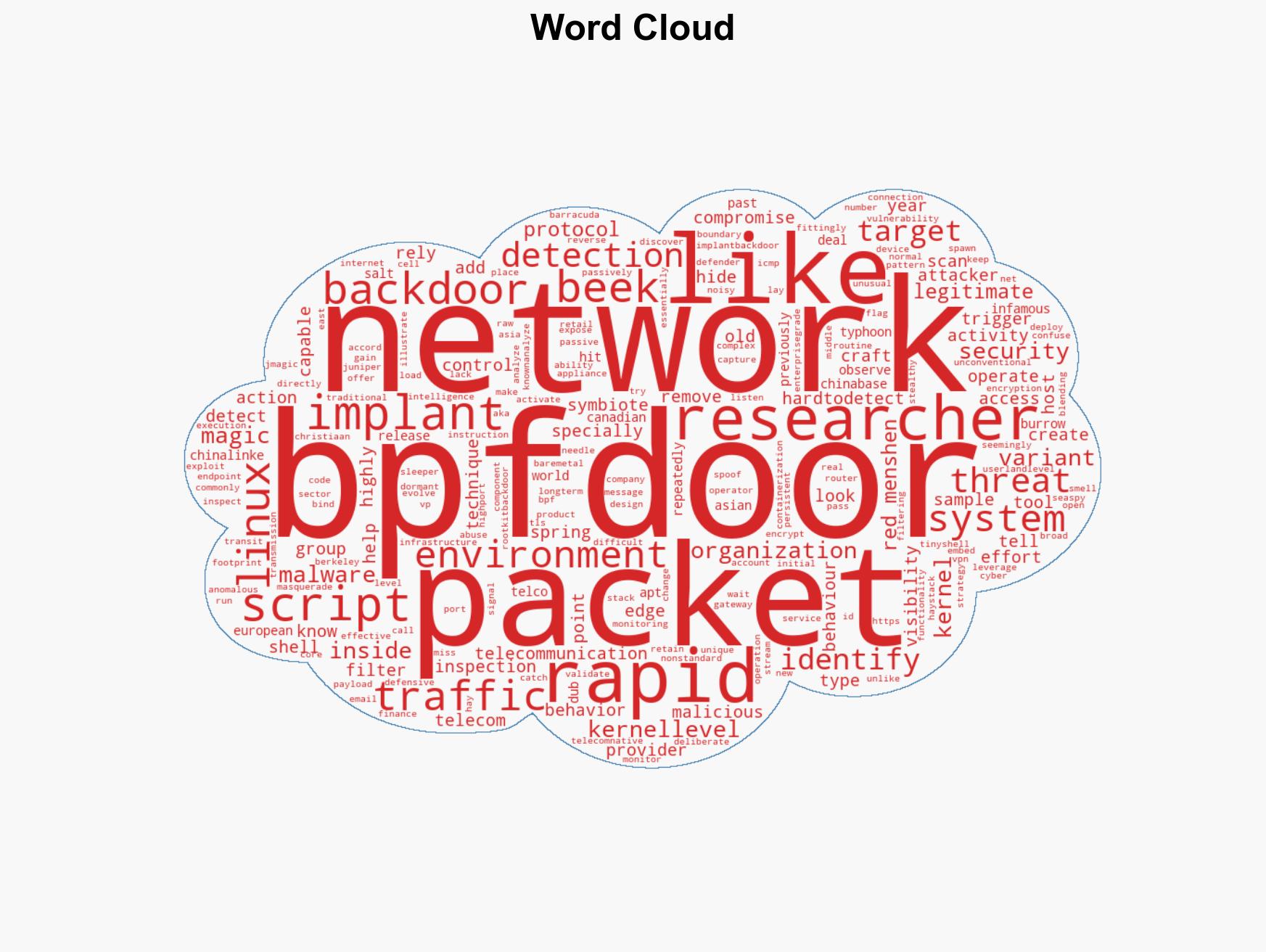
cybersecurity, cyber-espionage, telecommunications security, APT groups, cyber defense, critical infrastructure, malware detection, cybersecurity strategy
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us