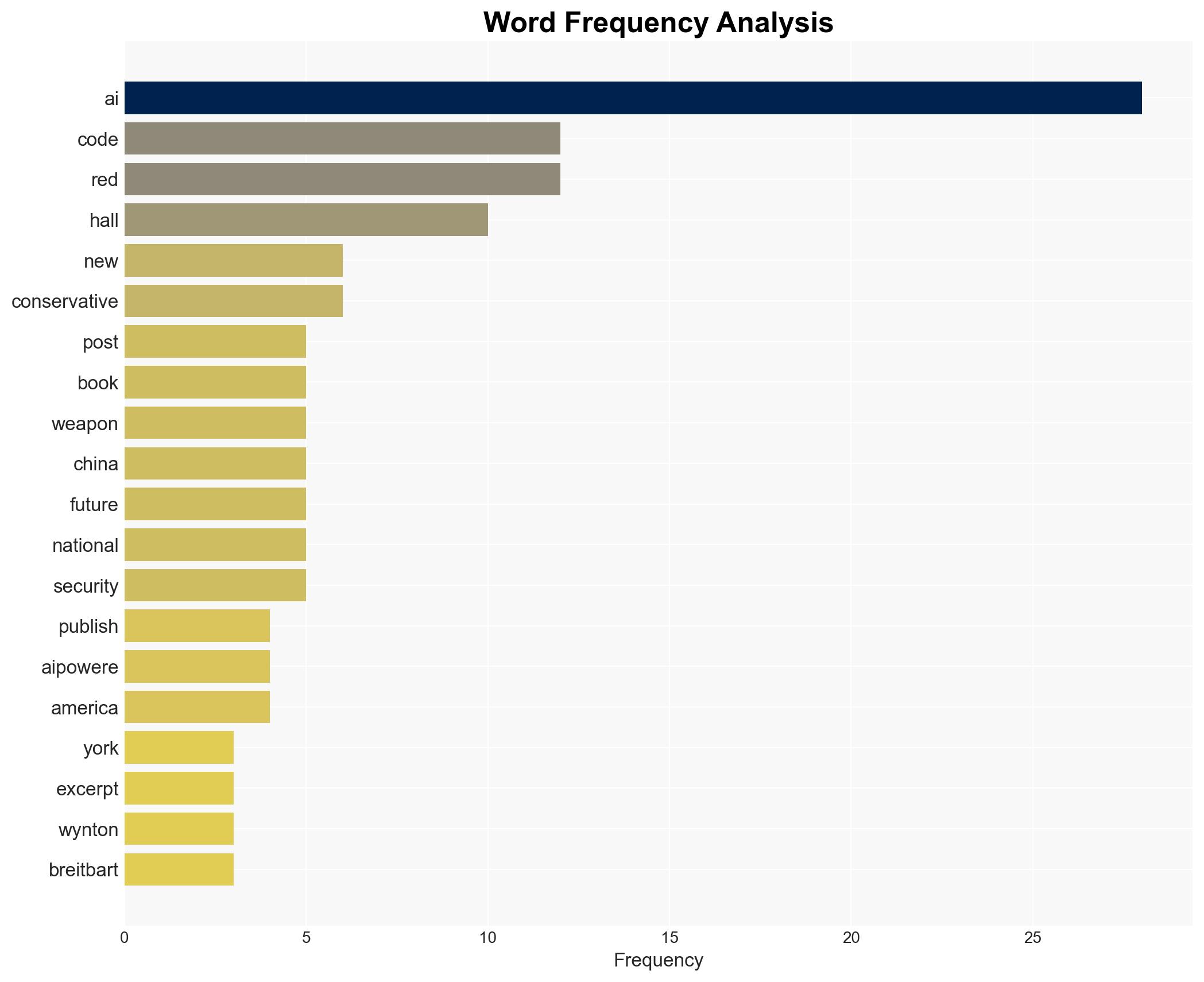
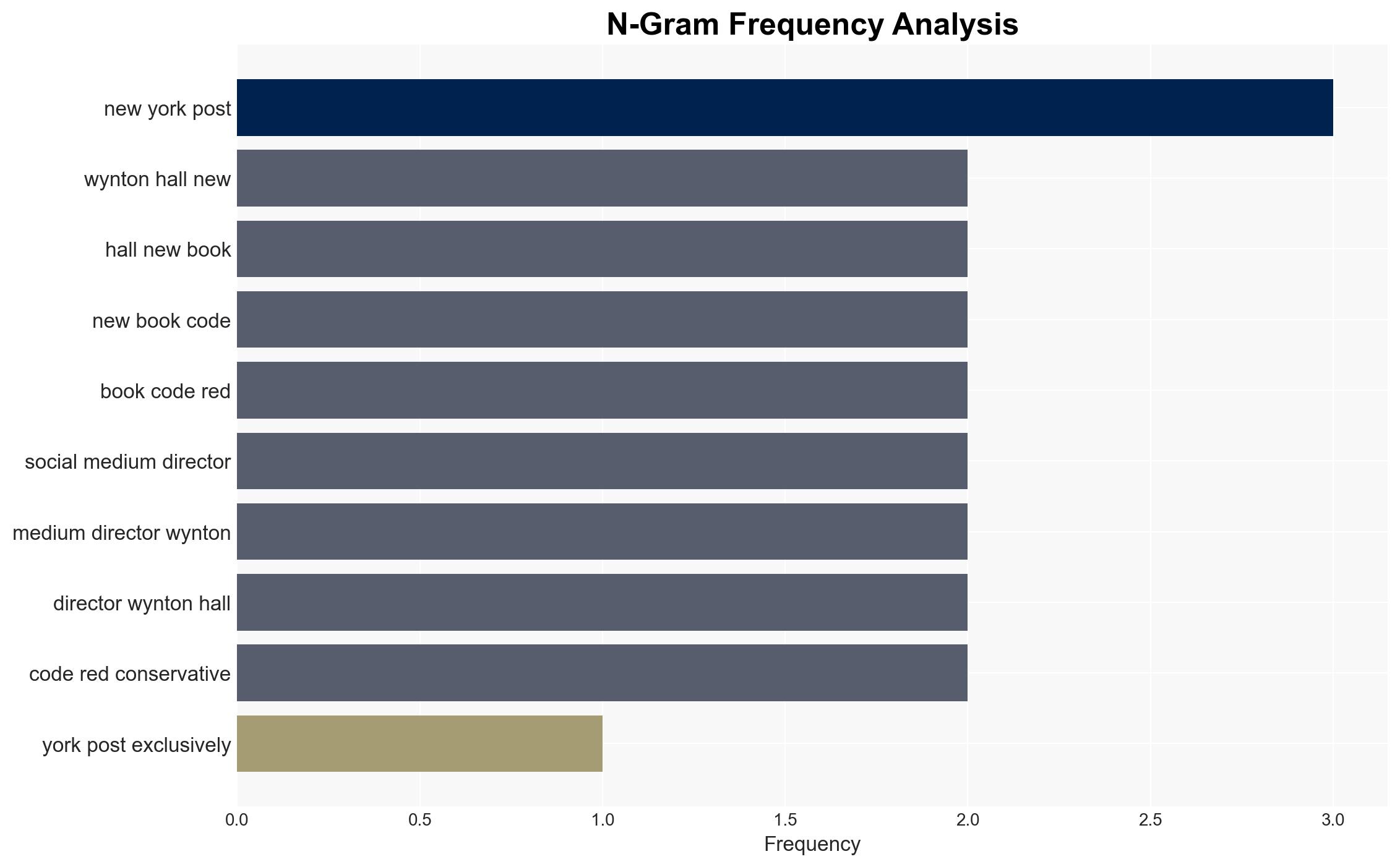
New York Post Reveals Excerpt from ‘Code Red’ Addressing the Threat of AI-Driven Autonomous Weapons
Published on: 2026-03-15
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: New York Post Publishes Stunning Excerpt of ‘CODE RED’ Exposing Truth of AI-Powered Autonomous Weapons
1. BLUF (Bottom Line Up Front)
The publication of an excerpt from Wynton Hall’s book “Code Red” highlights the growing accessibility of AI-powered autonomous weapons to both state and non-state actors, posing significant national security challenges. The book emphasizes the need for the U.S. to maintain its leadership in AI to counter these threats. This assessment is made with moderate confidence, given the potential biases in the source material and the lack of detailed technical data.
2. Competing Hypotheses
- Hypothesis A: The proliferation of AI-powered autonomous weapons will lead to a destabilized global security environment, with increased risks of conflict involving both state and non-state actors. This hypothesis is supported by the assertion that such technologies are becoming more accessible and cheaper.
- Hypothesis B: The U.S. and its allies will successfully manage the risks associated with AI-powered weapons through strategic policy and technological leadership, preventing significant destabilization. This is supported by the emphasis on U.S. leadership and policy development in the book.
- Assessment: Hypothesis A is currently better supported due to the rapid technological advancements and the potential for non-state actors to acquire these capabilities. However, effective U.S. policy and international cooperation could shift this judgment towards Hypothesis B.
3. Key Assumptions and Red Flags
- Assumptions: AI technology will continue to advance rapidly; non-state actors will seek to acquire AI weaponry; U.S. policy will significantly influence global AI dynamics.
- Information Gaps: Specific details on the current capabilities of AI-powered weapons and the extent of their proliferation among non-state actors.
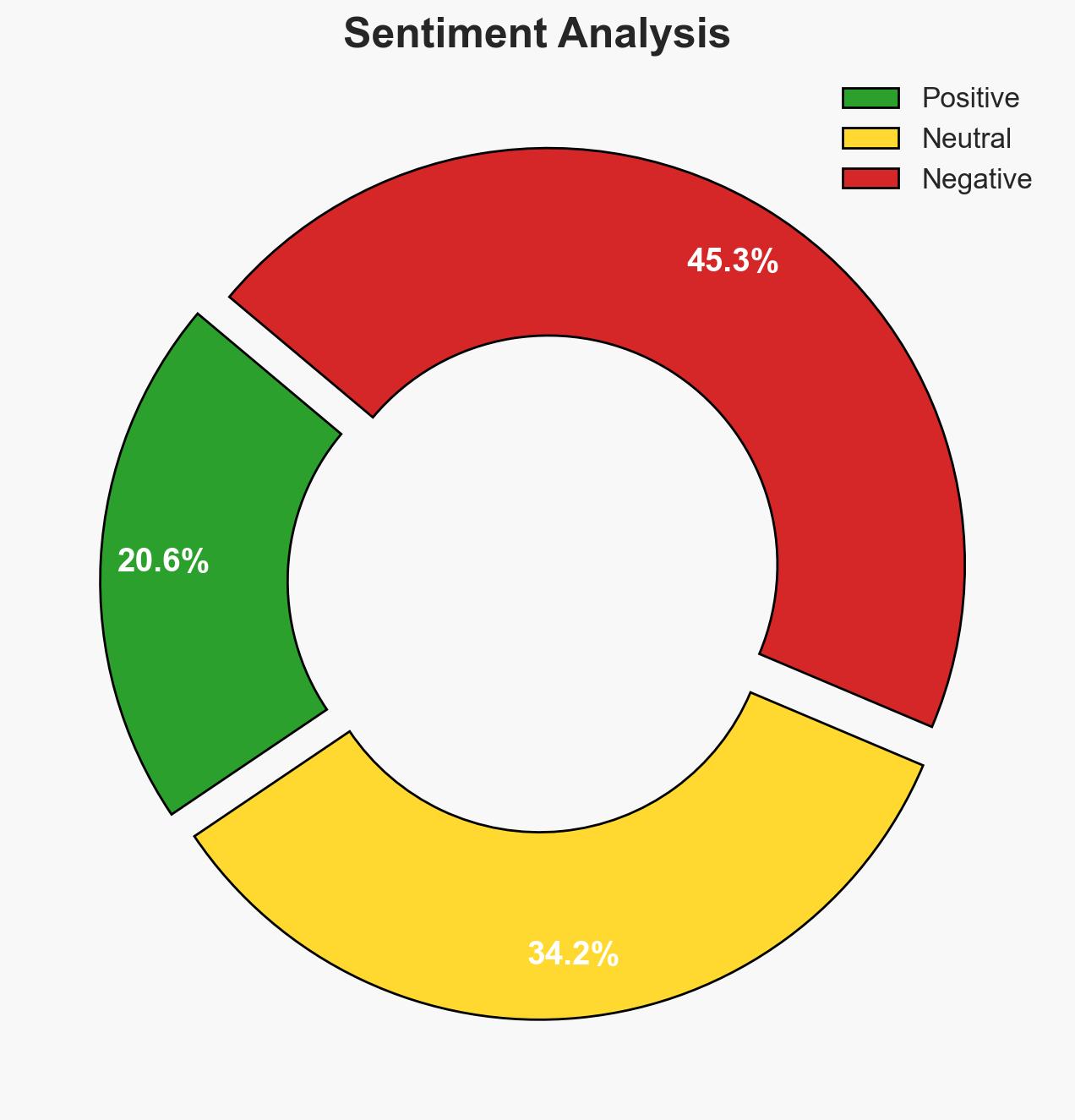
- Bias & Deception Risks: The source material may exhibit bias due to its political orientation and potential agenda-setting by the author and publishers.
4. Implications and Strategic Risks
The development and dissemination of AI-powered autonomous weapons could significantly alter global security dynamics, with potential impacts across multiple domains.
- Political / Geopolitical: Increased tensions between major powers, particularly the U.S. and China, and potential arms races involving AI technologies.
- Security / Counter-Terrorism: Enhanced capabilities for non-state actors, increasing the complexity of counter-terrorism operations.
- Cyber / Information Space: Potential for AI-driven cyber-attacks and misinformation campaigns, complicating information security efforts.
- Economic / Social: Disruption in labor markets due to AI advancements, with potential social unrest stemming from economic displacement.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase monitoring of AI technology proliferation, enhance intelligence sharing with allies, and initiate public-private dialogues on AI ethics and security.
- Medium-Term Posture (1–12 months): Develop comprehensive AI governance frameworks, invest in AI research and development, and strengthen international partnerships to manage AI risks.
- Scenario Outlook:
- Best: Effective global cooperation leads to robust AI governance, mitigating security risks.
- Worst: Unchecked proliferation of AI weapons results in widespread conflict and instability.
- Most-Likely: Gradual increase in AI weapon capabilities among various actors, with intermittent conflicts and ongoing policy adjustments.
6. Key Individuals and Entities
- Wynton Hall (Author of “Code Red”)
- New York Post (Publisher of the excerpt)
- Breitbart News (Affiliated media outlet)
- Not clearly identifiable from open sources in this snippet for other key entities.
7. Thematic Tags
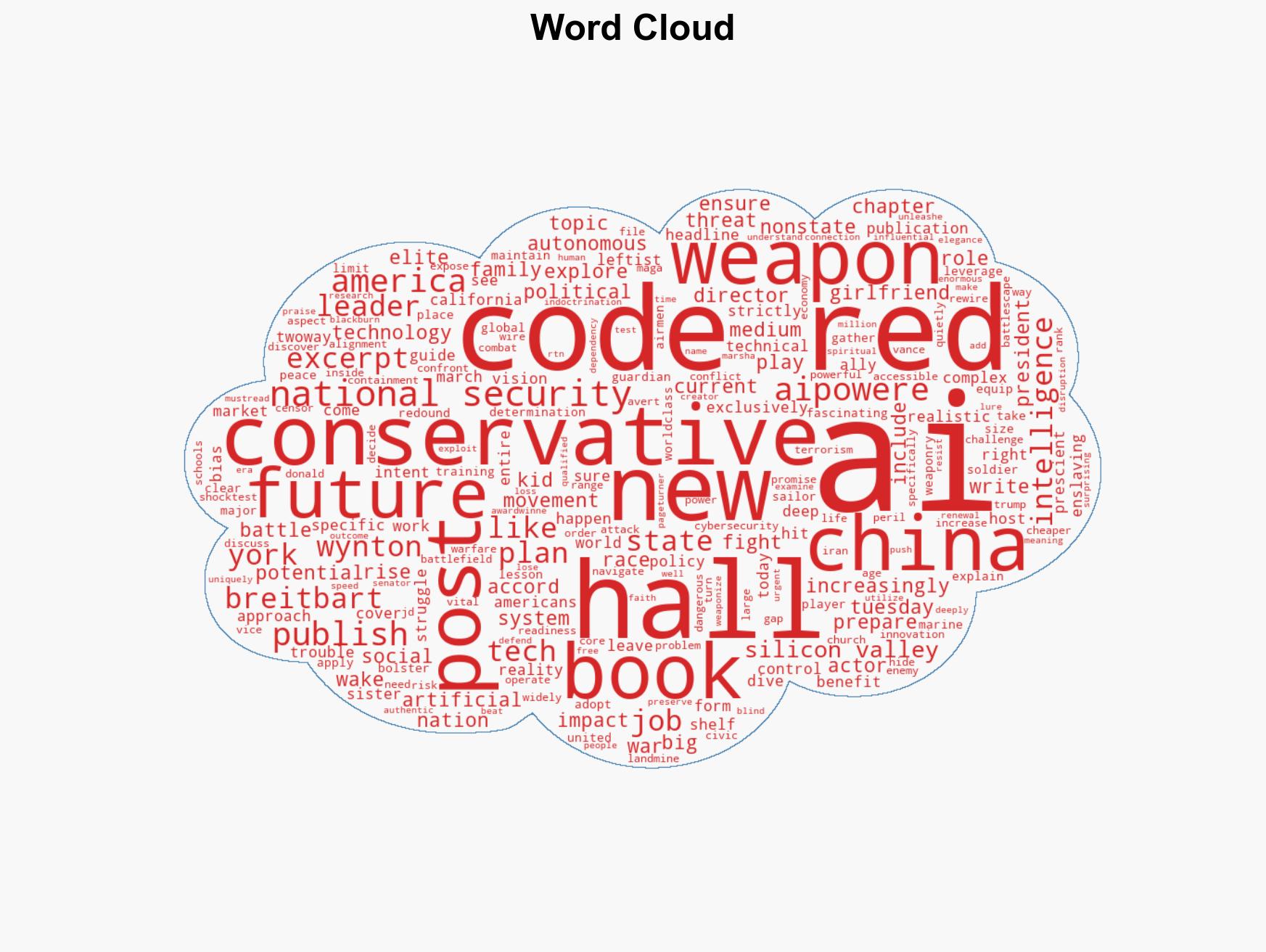
national security threats, AI weapons, national security, U.S.-China relations, non-state actors, technological proliferation, geopolitical tensions, cyber threats
Structured Analytic Techniques Applied
- Cognitive Bias Stress Test: Structured challenge to expose and correct biases.
- Bayesian Scenario Modeling: Use probabilistic forecasting for conflict trajectories or escalation likelihood.
- Network Influence Mapping: Map relationships between state and non-state actors for impact estimation.
Explore more:
National Security Threats Briefs ·
Daily Summary ·
Support us