Newly Identified DarkSword Exploit Chain Targets iOS 18, Affecting Millions of Devices Worldwide
Published on: 2026-03-18
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Researchers discover zero-day DarkSword exploit chain in iOS 18
1. BLUF (Bottom Line Up Front)
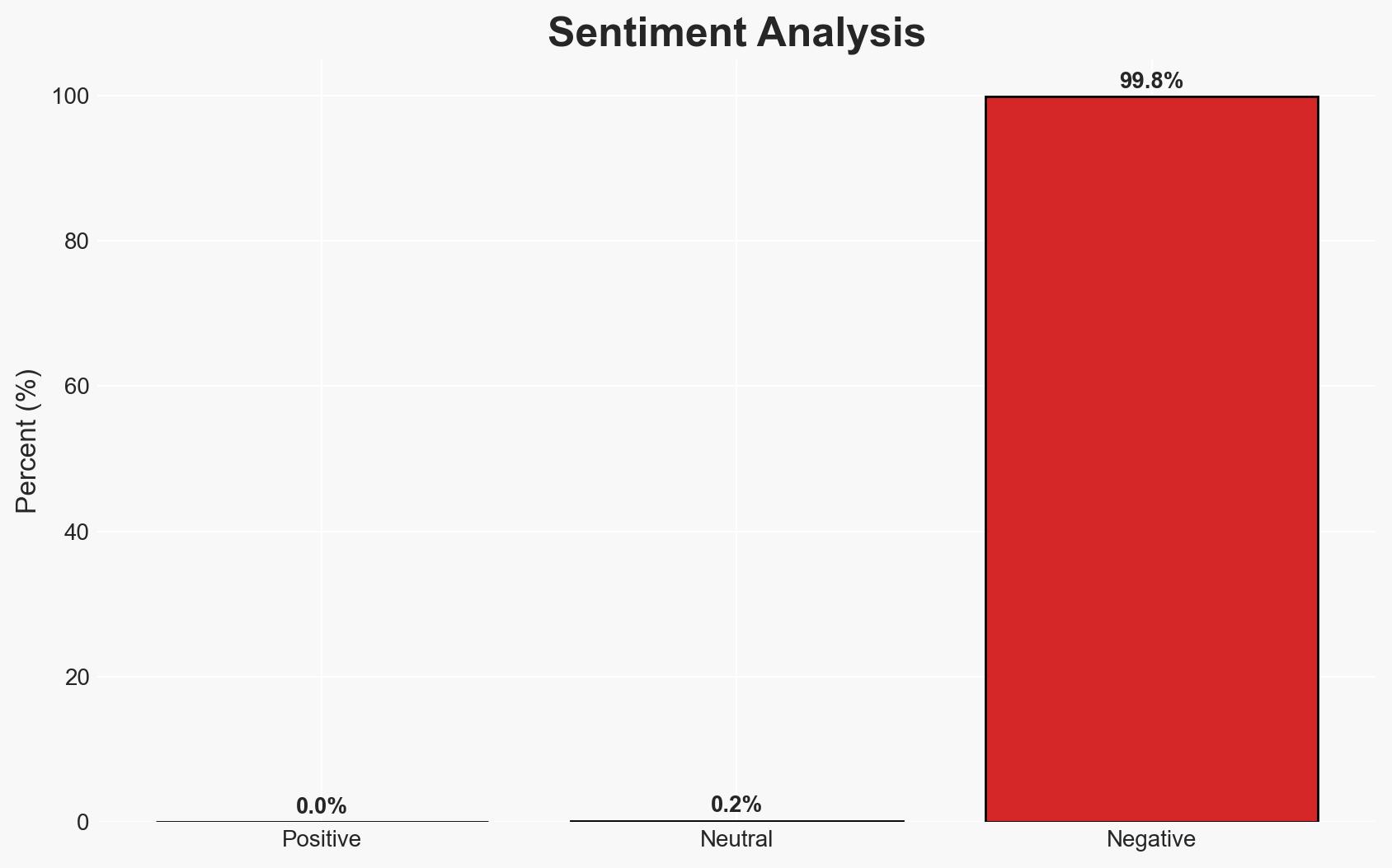
The discovery of the DarkSword exploit chain in iOS 18 represents a significant cybersecurity threat, potentially impacting hundreds of millions of iPhone users globally. The exploit has been linked to Russian state-sponsored actors and other threat groups, targeting users in multiple countries. The most likely hypothesis is that DarkSword is being used for state-sponsored espionage and commercial surveillance. Overall confidence in this assessment is moderate due to existing information gaps and potential biases in open-source reporting.
2. Competing Hypotheses
- Hypothesis A: DarkSword is primarily used by state-sponsored actors, such as the Russian group, for espionage purposes. This is supported by the targeting of Ukrainian websites and the involvement of a known Russian hacking group. However, the use by other threat actors suggests broader utilization.
- Hypothesis B: DarkSword is being widely used by various commercial surveillance vendors and independent threat actors for financial gain and data theft. This hypothesis is supported by the diversity of targets and the nature of the data exfiltrated, but lacks direct evidence of commercial actor involvement.
- Assessment: Hypothesis A is currently better supported due to the specific targeting patterns and the involvement of a Russian state-sponsored group. Indicators that could shift this judgment include evidence of financial transactions linked to commercial actors or broader targeting patterns.
3. Key Assumptions and Red Flags
- Assumptions: The exploit chain is primarily used for espionage; Russian state-sponsored actors are the main users; iOS 18 vulnerabilities are not yet patched.
- Information Gaps: The full extent of DarkSword’s deployment, the identities of all involved threat actors, and the specific data exfiltrated remain unclear.
- Bias & Deception Risks: Potential bias in attributing the exploit to Russian actors based on historical patterns; open-source reporting may be incomplete or influenced by geopolitical narratives.
4. Implications and Strategic Risks
The DarkSword exploit chain could lead to increased geopolitical tensions, particularly between Russia and affected countries. The ongoing vulnerability in iOS 18 poses a persistent security risk, potentially leading to widespread data breaches and loss of sensitive information.
- Political / Geopolitical: Escalation of cyber tensions between Russia and Ukraine, and potential diplomatic strains with other affected nations.
- Security / Counter-Terrorism: Increased vulnerability of critical infrastructure and personal data, complicating counter-terrorism efforts due to potential data leaks.
- Cyber / Information Space: Heightened focus on mobile device security; potential for increased cyber espionage activities.
- Economic / Social: Potential economic impacts from data breaches; erosion of public trust in digital security measures.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of iOS 18 vulnerabilities; collaborate with Apple for patch development; increase awareness among users in targeted regions.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for threat intelligence sharing; invest in advanced detection and response capabilities for mobile threats.
- Scenario Outlook:
- Best: Rapid patching of vulnerabilities and neutralization of threat actors.
- Worst: Expansion of DarkSword usage to additional state and non-state actors, leading to widespread data breaches.
- Most-Likely: Continued exploitation by state-sponsored actors with gradual mitigation efforts by affected entities.
6. Key Individuals and Entities
- Google LLC (GTIG threat intelligence team)
- Lookout Inc.
- iVerify Inc.
- Russian state-sponsored hacking group
- Apple Inc.
7. Thematic Tags
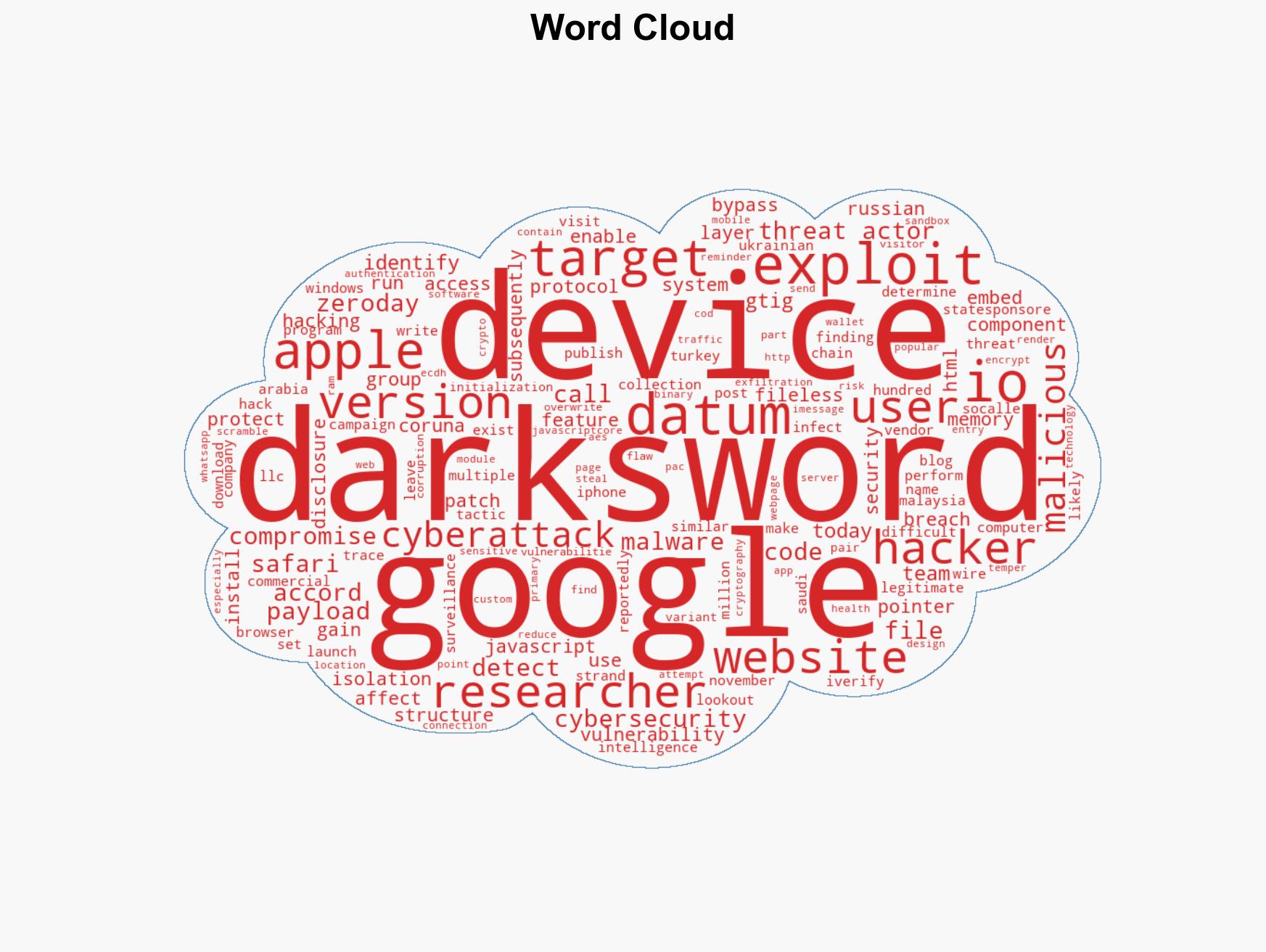
cybersecurity, state-sponsored espionage, mobile security, zero-day exploits, data exfiltration, geopolitical tensions, cyber-espionage
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us