North Korean APT37 utilizes cloud services and USB implants to target isolated networks in new cyber campaign
Published on: 2026-03-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: APT37 combines cloud storage and USB implants to infiltrate air-gapped systems
1. BLUF (Bottom Line Up Front)
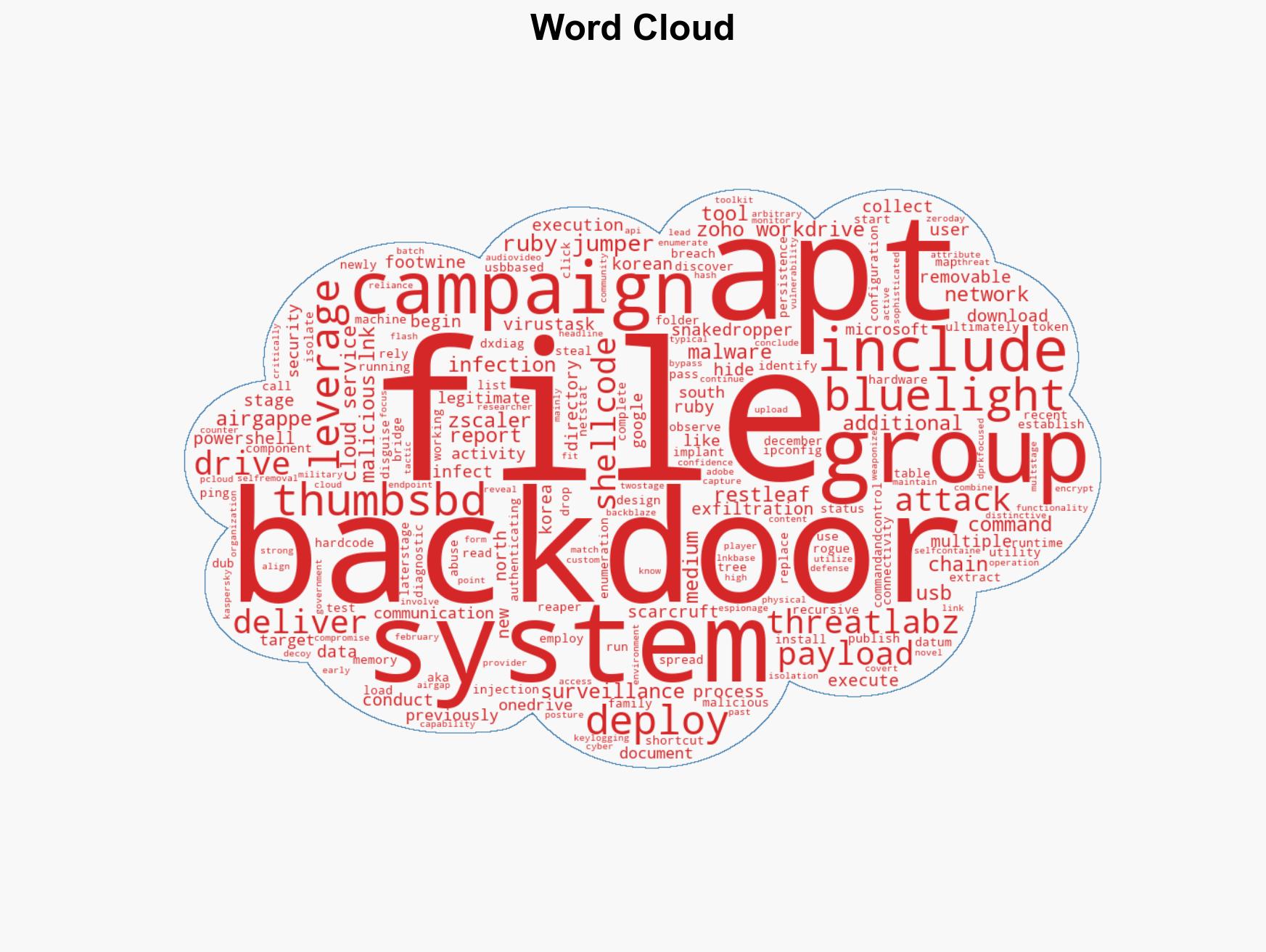
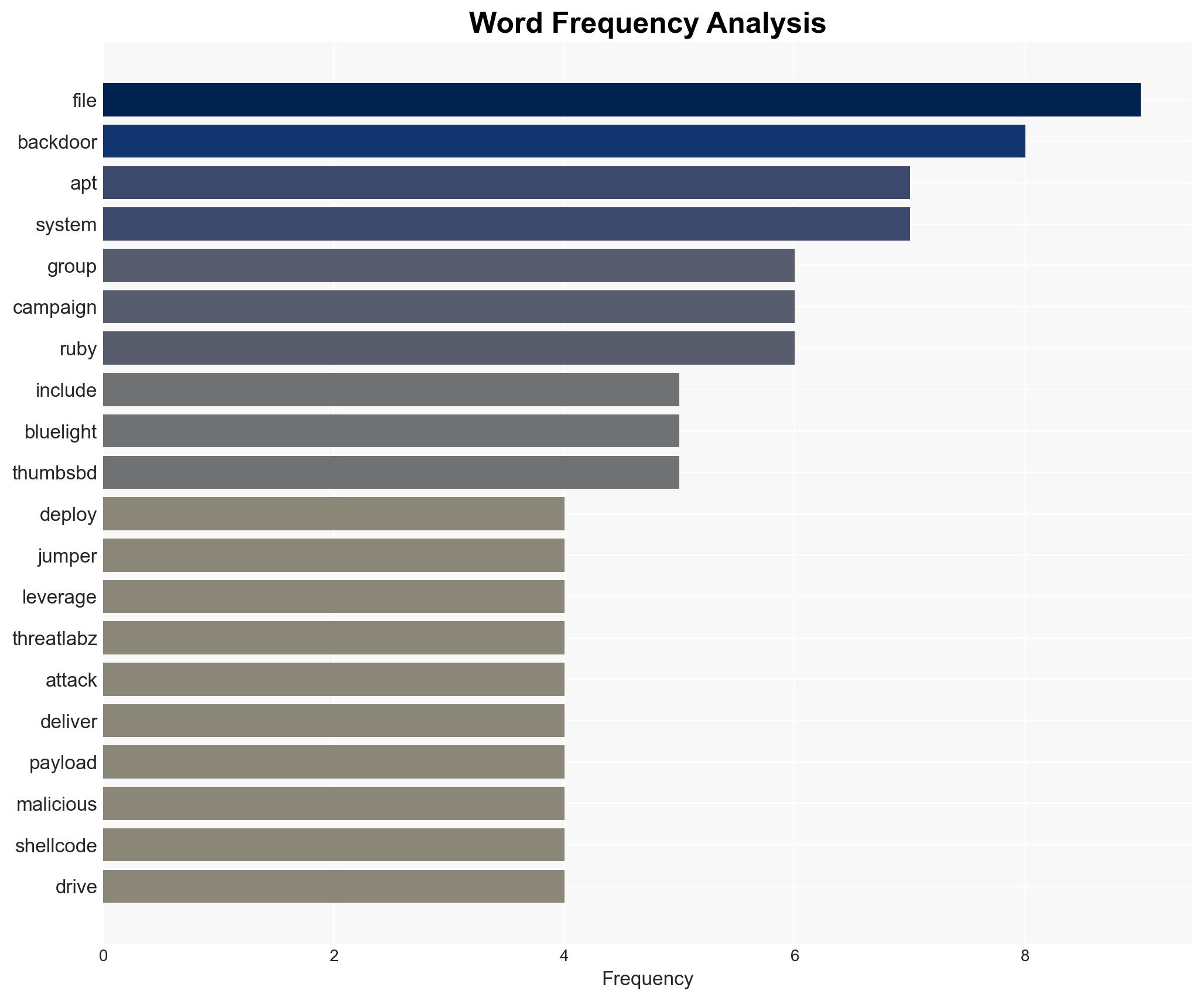
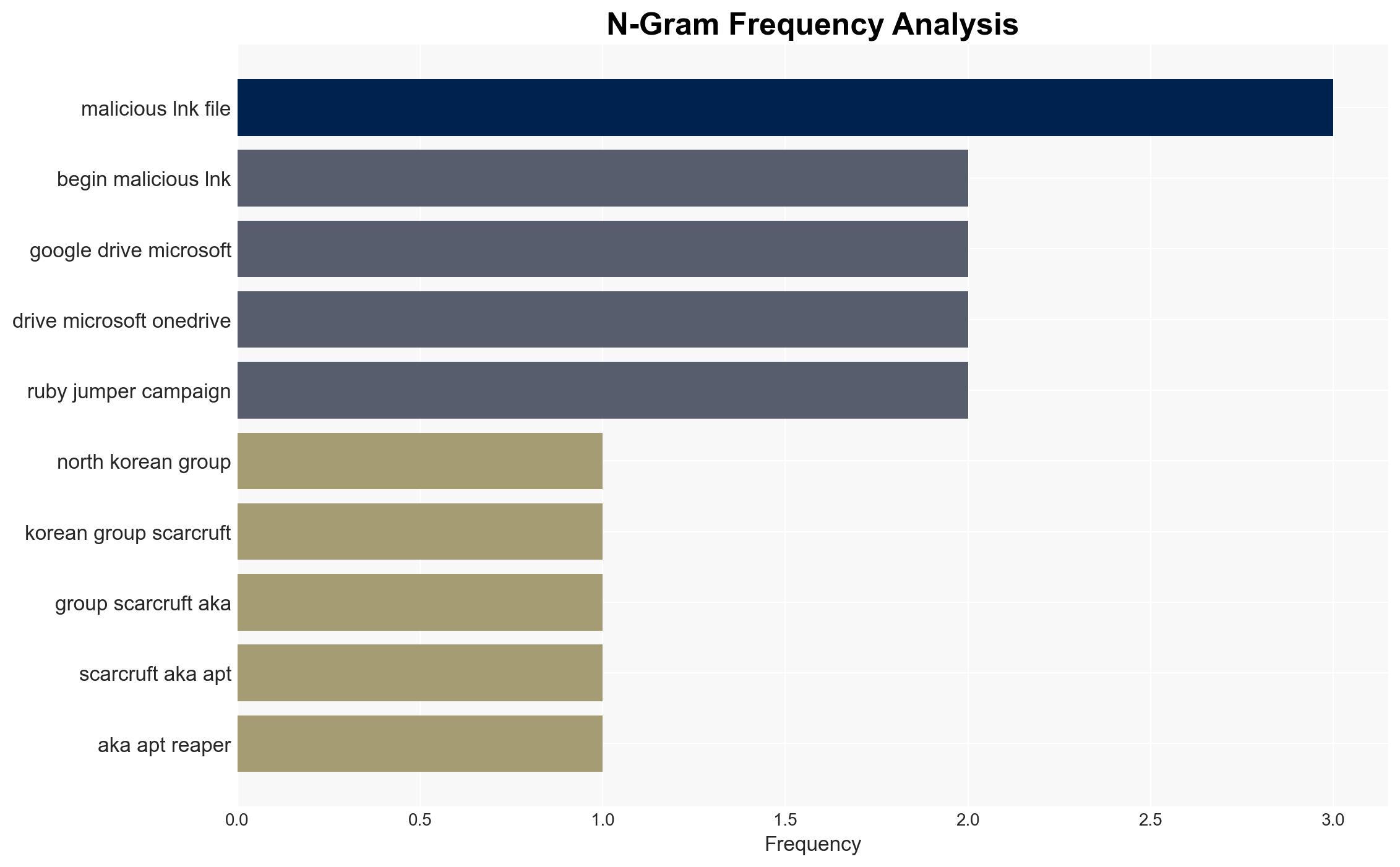
APT37, a North Korean cyber threat group, has developed a sophisticated attack campaign, “Ruby Jumper,” targeting air-gapped systems using cloud storage and USB implants. This campaign poses a significant espionage threat to isolated networks, with a high confidence level in attribution to APT37. The primary affected sectors include government and critical infrastructure entities.
2. Competing Hypotheses
- Hypothesis A: APT37 is primarily targeting air-gapped systems for espionage purposes, leveraging advanced techniques such as cloud-based C2 and USB implants. This is supported by the use of sophisticated tools like RESTLEAF and THUMBSBD, consistent with APT37’s historical tactics. However, the specific strategic objectives remain unclear.
- Hypothesis B: The campaign may serve as a broader testbed for developing and refining cyber capabilities against air-gapped systems, possibly for future disruptive operations. While the tools are sophisticated, evidence directly linking to disruptive intentions is limited.
- Assessment: Hypothesis A is currently better supported due to the alignment of tactics with known APT37 espionage activities and the high confidence attribution by Zscaler ThreatLabz. Indicators such as increased targeting of critical infrastructure could shift this judgment towards Hypothesis B.
3. Key Assumptions and Red Flags
- Assumptions: APT37 has the capability and intent to target air-gapped systems; the tools identified are primarily used for espionage; the campaign is state-sponsored.
- Information Gaps: Specific targets and objectives of the campaign; the full extent of the compromise; potential collaboration with other threat actors.
- Bias & Deception Risks: Attribution bias due to reliance on technical indicators; potential for false flag operations to mislead attribution; source bias from cybersecurity firms with vested interests.
4. Implications and Strategic Risks
This development indicates an escalation in APT37’s capabilities, potentially leading to increased targeting of sensitive and isolated networks. The use of cloud-based C2 and USB implants could inspire similar tactics among other threat actors.
- Political / Geopolitical: Potential diplomatic tensions due to North Korean cyber activities; increased scrutiny on North Korea’s cyber capabilities.
- Security / Counter-Terrorism: Heightened threat to national security infrastructure; need for enhanced security measures for air-gapped systems.
- Cyber / Information Space: Increased complexity in defending against multi-vector cyber threats; potential for information leaks and data breaches.
- Economic / Social: Potential economic impact from espionage activities; increased costs for cybersecurity defenses in targeted sectors.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cloud storage and removable media activities; conduct security audits on air-gapped systems; increase awareness and training for potential targets.
- Medium-Term Posture (1–12 months): Develop partnerships for intelligence sharing; invest in advanced detection and response capabilities; strengthen international collaboration on cyber defense.
- Scenario Outlook: Best: Increased defenses deter further attacks. Worst: Successful breaches lead to significant data exfiltration. Most-Likely: Continued attempts with varying degrees of success, prompting ongoing security enhancements.
6. Key Individuals and Entities
- APT37 (ScarCruft, Reaper, Group123)
- Zscaler ThreatLabz
- Zoho WorkDrive
7. Thematic Tags
cybersecurity, cyber-espionage, North Korea, air-gapped systems, cloud storage, USB implants, APT37
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us