NYC Health + Hospitals Investigates Data Breach Linked to Third-Party Vendor Security Compromise
Published on: 2026-03-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
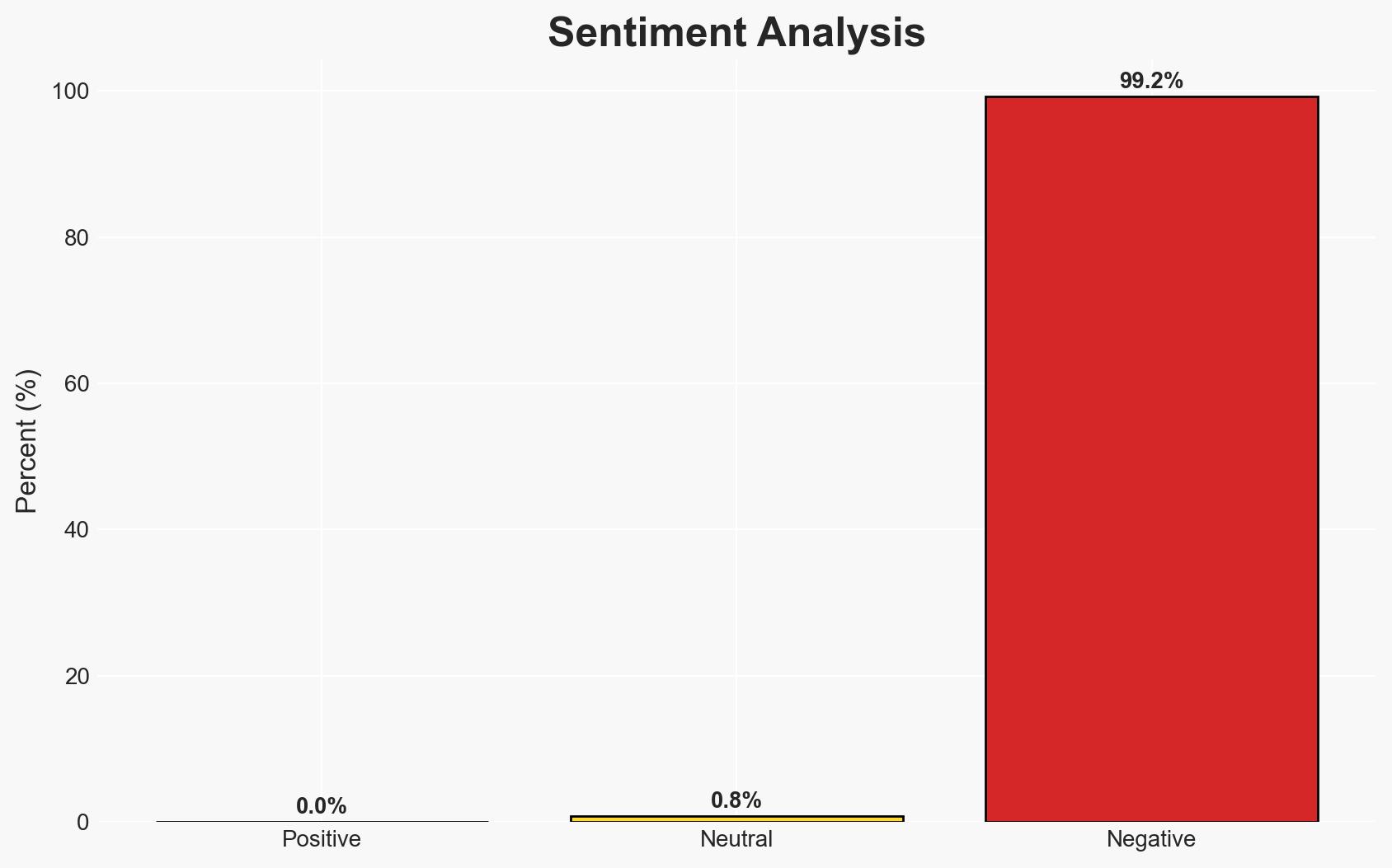
Intelligence Report: NYC Health Hospitals Reports Data Breach – Information Technology
1. BLUF (Bottom Line Up Front)
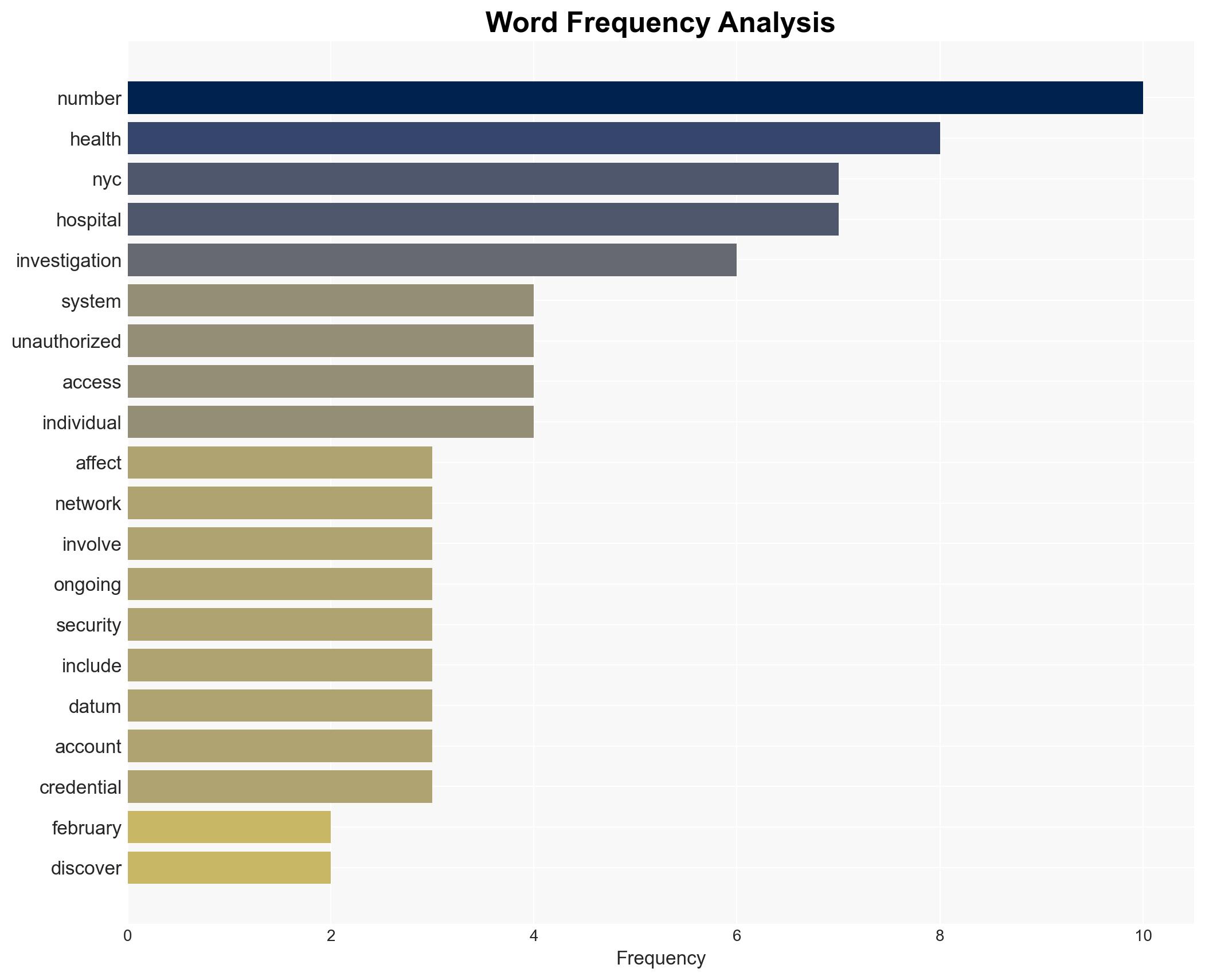
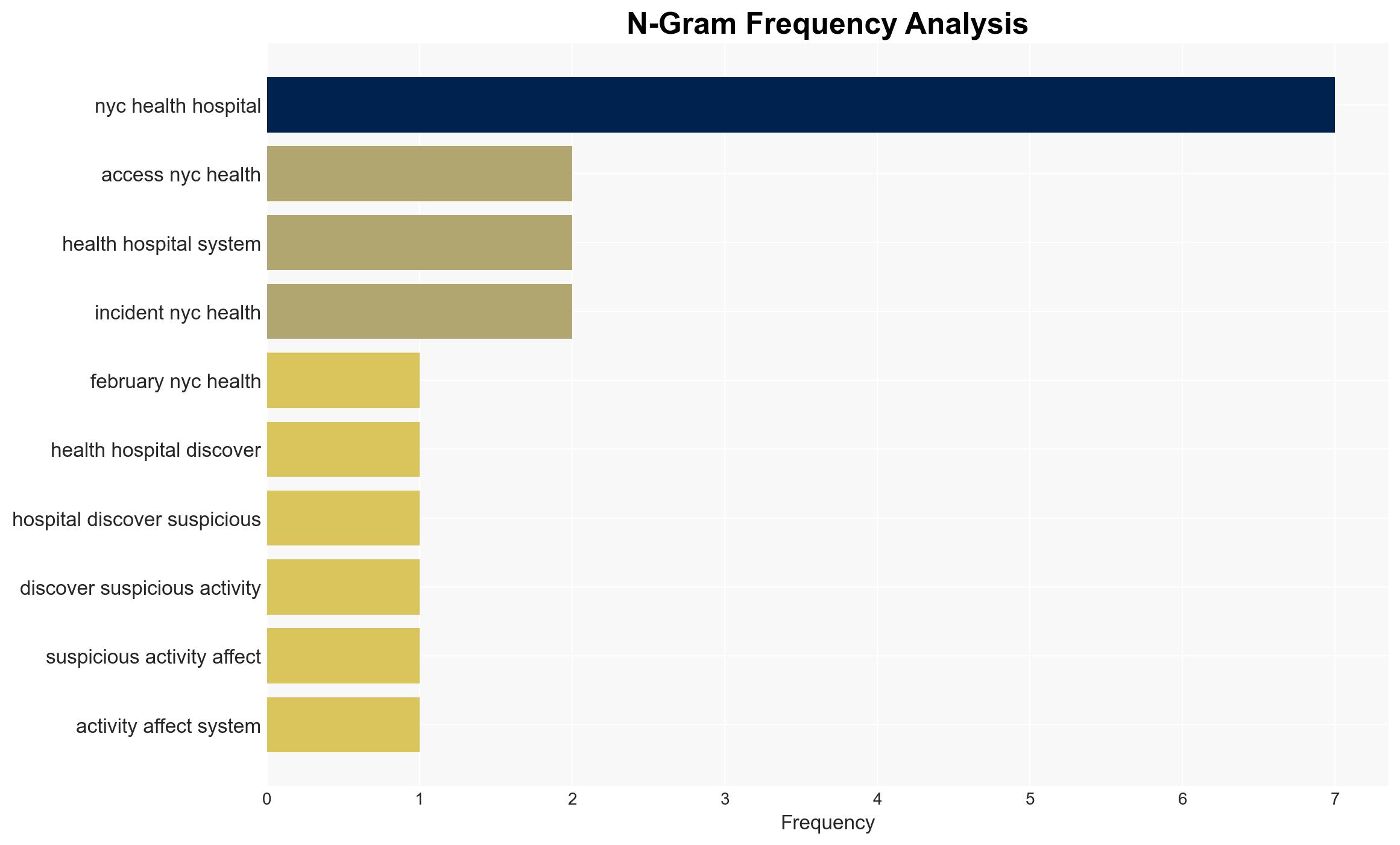
The NYC Health + Hospitals data breach, attributed to unauthorized access via a third-party vendor, potentially exposed sensitive personal and medical information of numerous individuals. The breach underscores vulnerabilities in third-party vendor management and highlights the need for enhanced cybersecurity measures. There is moderate confidence in the assessment that the breach was facilitated through a vendor-related security lapse.
2. Competing Hypotheses
- Hypothesis A: The breach was primarily due to a security lapse at a third-party vendor, allowing unauthorized access to NYC Health + Hospitals’ systems. Supporting evidence includes the ongoing investigation pointing to a vendor breach. Key uncertainties involve the specific nature of the vendor’s security failure and whether it was exploited by a known threat actor.
- Hypothesis B: The breach resulted from an internal security oversight within NYC Health + Hospitals, independent of third-party involvement. This hypothesis is less supported due to the current investigation’s focus on third-party vendor involvement. However, it cannot be entirely ruled out without further evidence.
- Assessment: Hypothesis A is currently better supported due to the investigation’s preliminary findings indicating third-party vendor involvement. Key indicators that could shift this judgment include new evidence of internal security lapses or identification of a specific threat actor exploiting internal vulnerabilities.
3. Key Assumptions and Red Flags
- Assumptions: The breach was not part of a larger coordinated attack; the third-party vendor was the primary entry point; NYC Health + Hospitals’ internal systems were otherwise secure.
- Information Gaps: Specific details on the third-party vendor’s security protocols and the identity of the unauthorized actor remain unknown.
- Bias & Deception Risks: Potential bias in attributing the breach solely to third-party vendors without fully exploring internal vulnerabilities; risk of deception by the unauthorized actor to mislead investigators.
4. Implications and Strategic Risks
The breach could have significant long-term impacts on trust in public health institutions and highlight systemic vulnerabilities in vendor management.
- Political / Geopolitical: Potential for increased regulatory scrutiny and policy changes regarding data protection and vendor management in public institutions.
- Security / Counter-Terrorism: Heightened risk of similar breaches targeting other public health entities, potentially exploiting vendor relationships.
- Cyber / Information Space: Increased focus on cybersecurity measures and vendor risk assessments across the healthcare sector.
- Economic / Social: Possible financial liabilities and reputational damage for NYC Health + Hospitals, affecting public confidence and operational stability.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive security audit of all third-party vendors, enhance monitoring of network activities, and communicate transparently with affected individuals.
- Medium-Term Posture (1–12 months): Develop robust vendor management policies, invest in advanced cybersecurity technologies, and establish partnerships for threat intelligence sharing.
- Scenario Outlook:
- Best: Rapid containment and remediation lead to minimal impact, with strengthened cybersecurity posture.
- Worst: Further breaches occur due to unresolved vulnerabilities, leading to significant data loss and regulatory penalties.
- Most-Likely: Gradual improvement in security measures, with ongoing challenges in vendor management and data protection.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
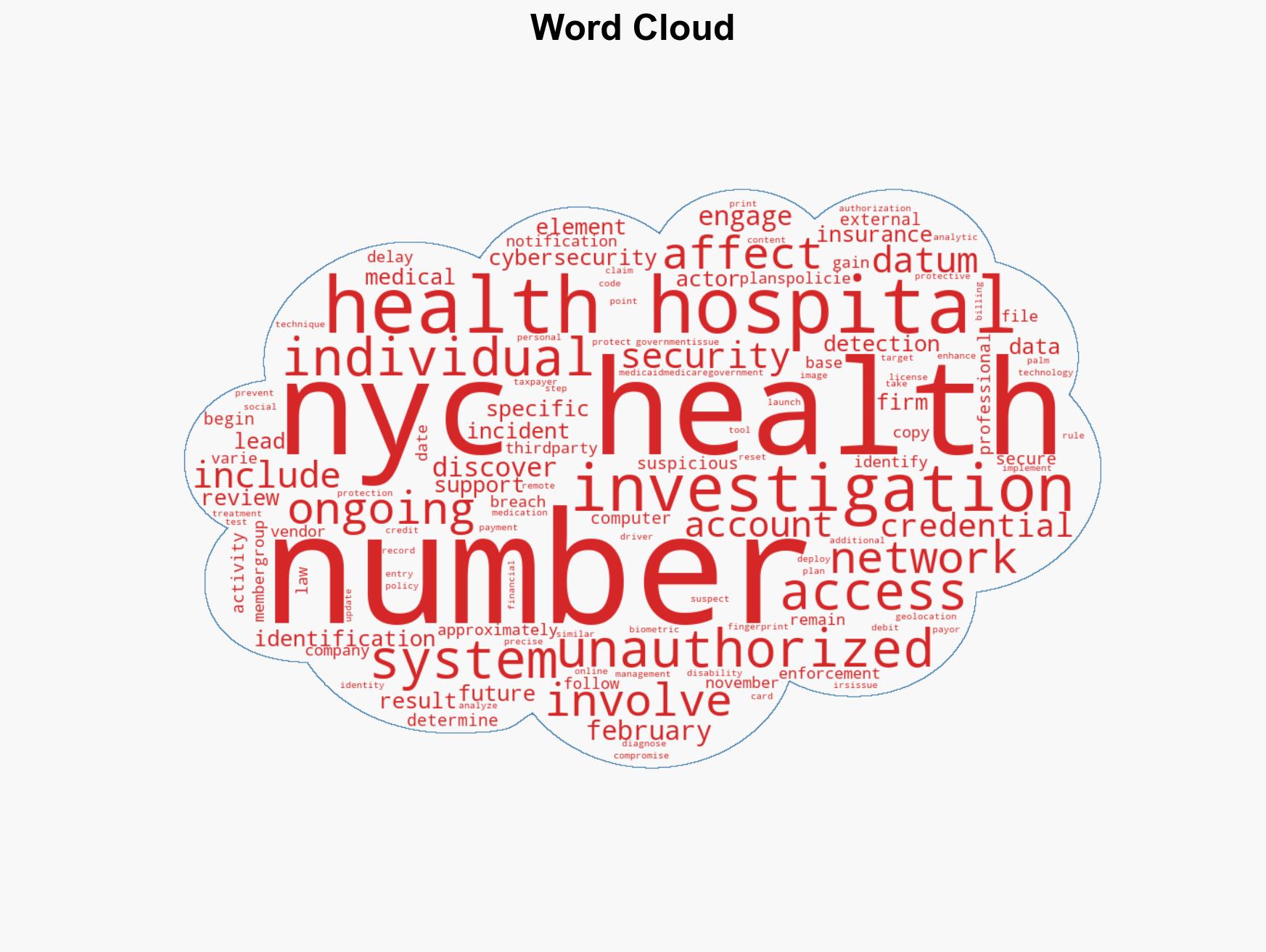
cybersecurity, data breach, third-party risk, healthcare security, vendor management, information security, public health
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us