Olympique Marseille reports attempted cyberattack amid claims of data breach by threat actor
Published on: 2026-02-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Olympique Marseille confirms ‘attempted’ cyberattack after data leak
1. BLUF (Bottom Line Up Front)
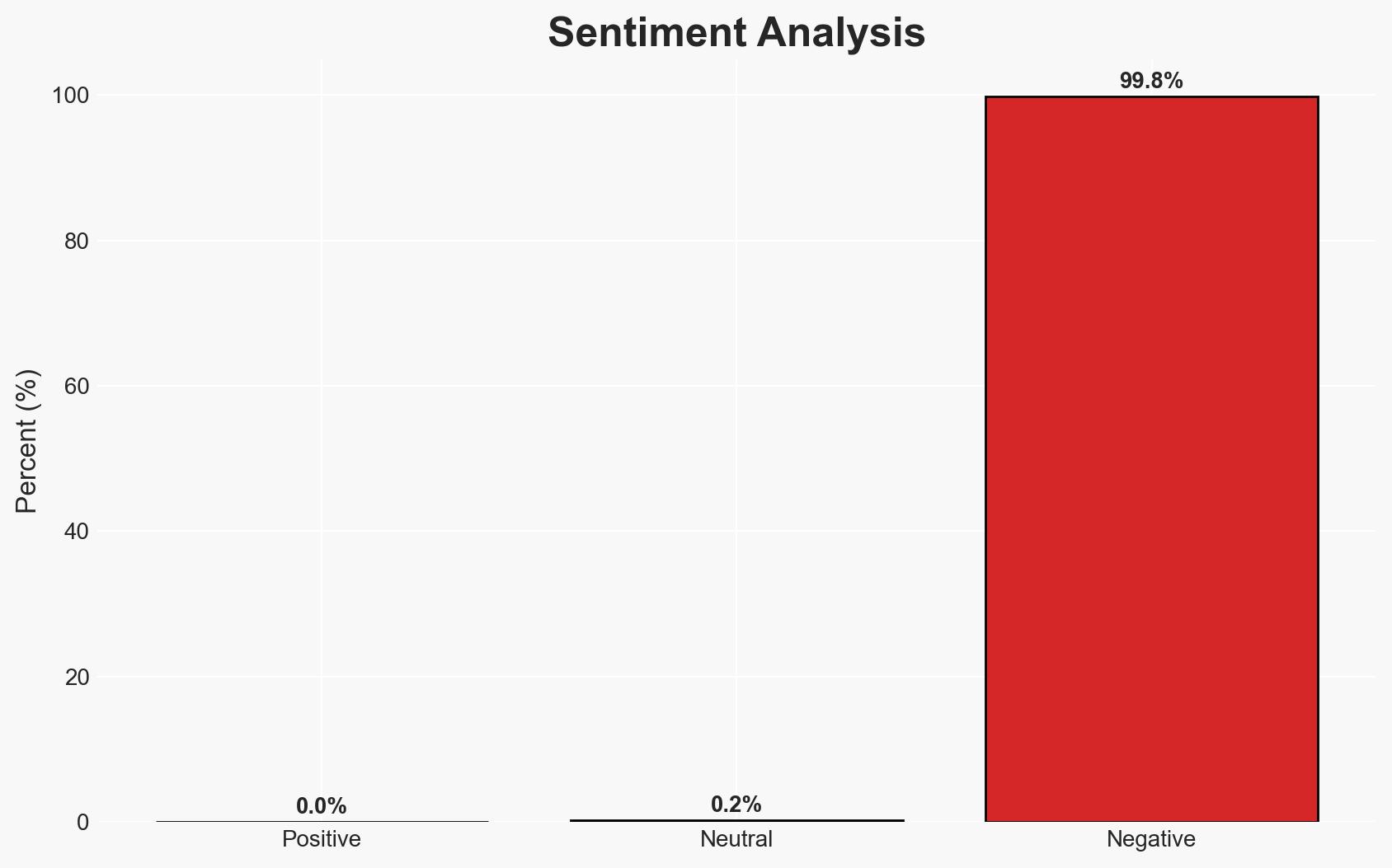
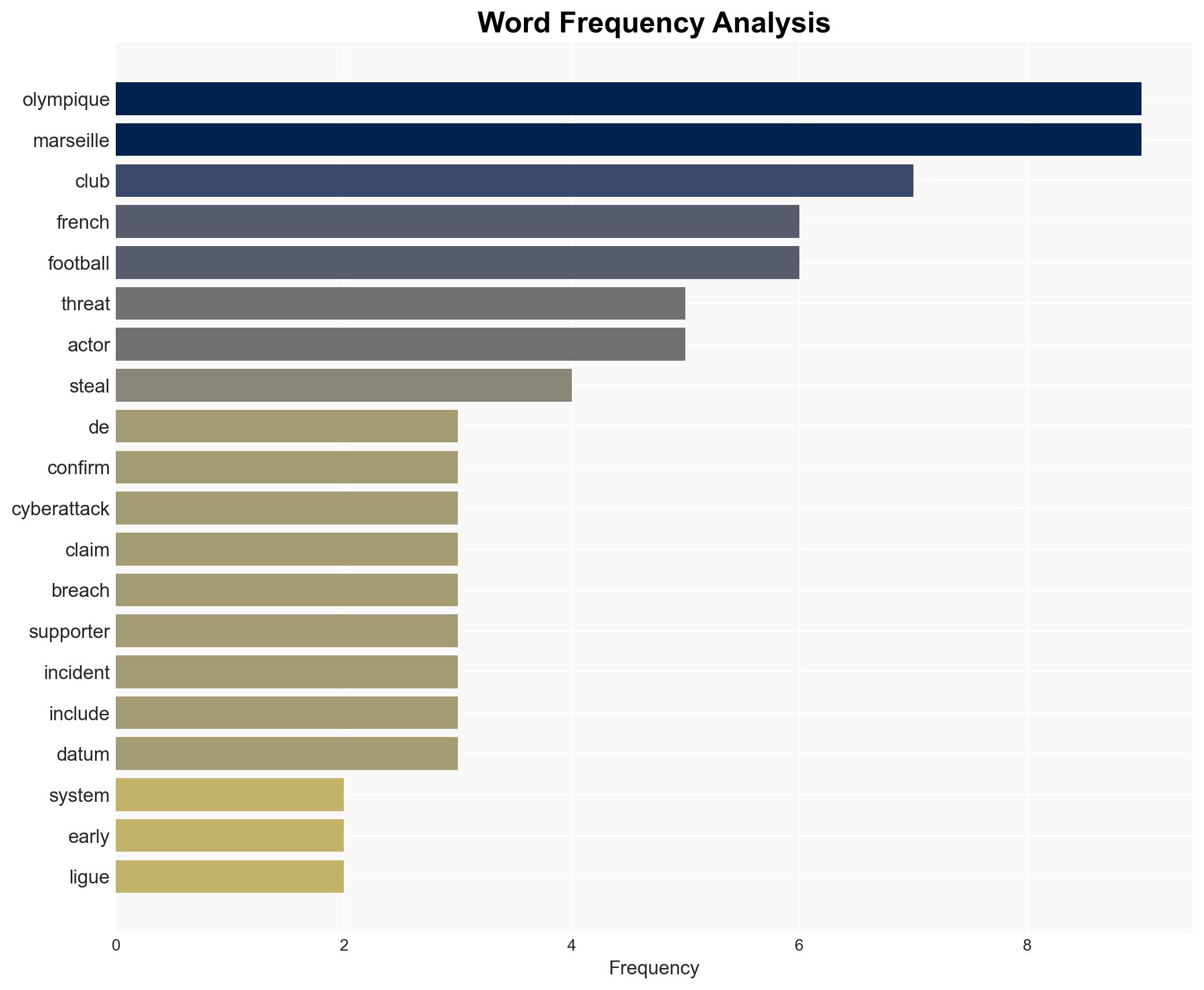
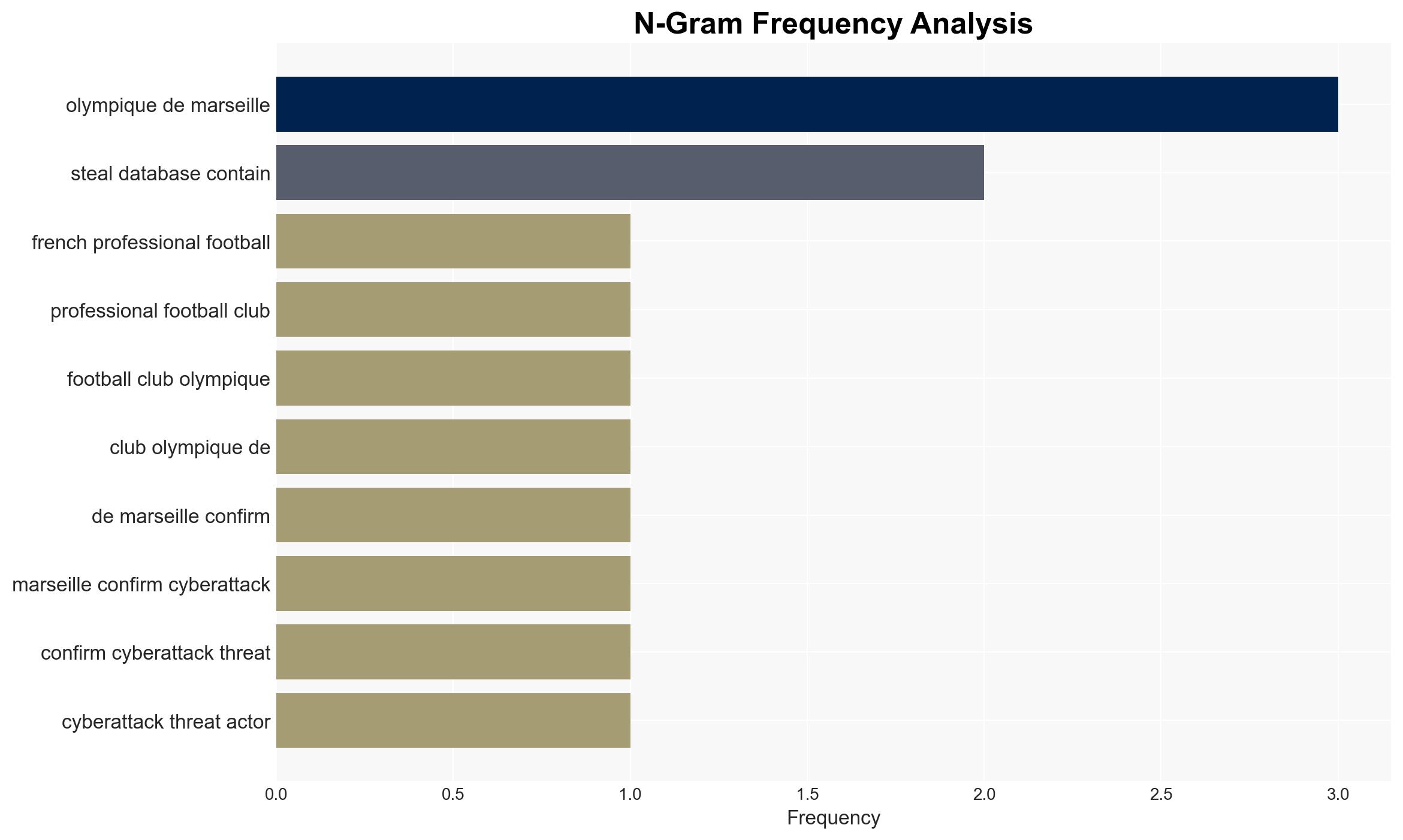
Olympique Marseille has confirmed an attempted cyberattack following claims of a data breach by a threat actor. The breach reportedly involves personal data of staff and supporters. The club has taken measures to control the situation, but further investigation is ongoing. This assessment is made with moderate confidence due to limited information on the breach’s full scope and impact.
2. Competing Hypotheses
- Hypothesis A: The cyberattack resulted in a significant data breach, compromising sensitive personal information of Olympique Marseille’s staff and supporters. Supporting evidence includes the threat actor’s claims and leaked data samples. However, the club’s statement suggests no sensitive financial data was compromised, creating uncertainty about the breach’s severity.
- Hypothesis B: The cyberattack was thwarted before any substantial data breach occurred. Olympique Marseille’s quick response and control over the situation support this hypothesis. Contradicting evidence includes the threat actor’s claims of having accessed and leaked data.
- Assessment: Hypothesis A is currently better supported due to the existence of leaked data samples and the threat actor’s detailed claims. Indicators such as further data leaks or confirmation from third-party investigations could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The threat actor’s claims are partially accurate; Olympique Marseille’s cybersecurity measures were effective in limiting the breach; the data leak does not include financial information.
- Information Gaps: The exact extent of the data breach, the identity and motivations of the threat actor, and the potential involvement of other entities remain unclear.
- Bias & Deception Risks: The threat actor may exaggerate claims to enhance credibility; Olympique Marseille may downplay the breach’s impact to protect reputation.
4. Implications and Strategic Risks
This cyberattack highlights vulnerabilities in sports organizations’ cybersecurity, potentially leading to increased targeting by cybercriminals. The incident could prompt regulatory scrutiny and affect stakeholder trust.
- Political / Geopolitical: Limited direct implications, but potential for increased regulatory focus on cybersecurity in sports.
- Security / Counter-Terrorism: No immediate counter-terrorism implications, but highlights the need for robust cybersecurity in high-profile organizations.
- Cyber / Information Space: This incident may encourage similar attacks on other sports entities, emphasizing the need for improved cybersecurity measures.
- Economic / Social: Potential reputational damage to Olympique Marseille and loss of supporter trust, impacting merchandise sales and fan engagement.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a thorough forensic investigation, enhance cybersecurity protocols, and communicate transparently with stakeholders.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms, implement regular security audits, and increase staff training on cyber threats.
- Scenario Outlook:
- Best: No further data leaks occur, and trust is restored through effective communication and enhanced security measures.
- Worst: Additional data leaks emerge, leading to regulatory penalties and significant reputational damage.
- Most-Likely: Limited additional data exposure, with gradual recovery of trust through proactive measures and transparency.
6. Key Individuals and Entities
- Olympique Marseille
- French Data Protection Authority (CNIL)
- Threat Actor (Unnamed)
- French Football Federation (FFF)
7. Thematic Tags
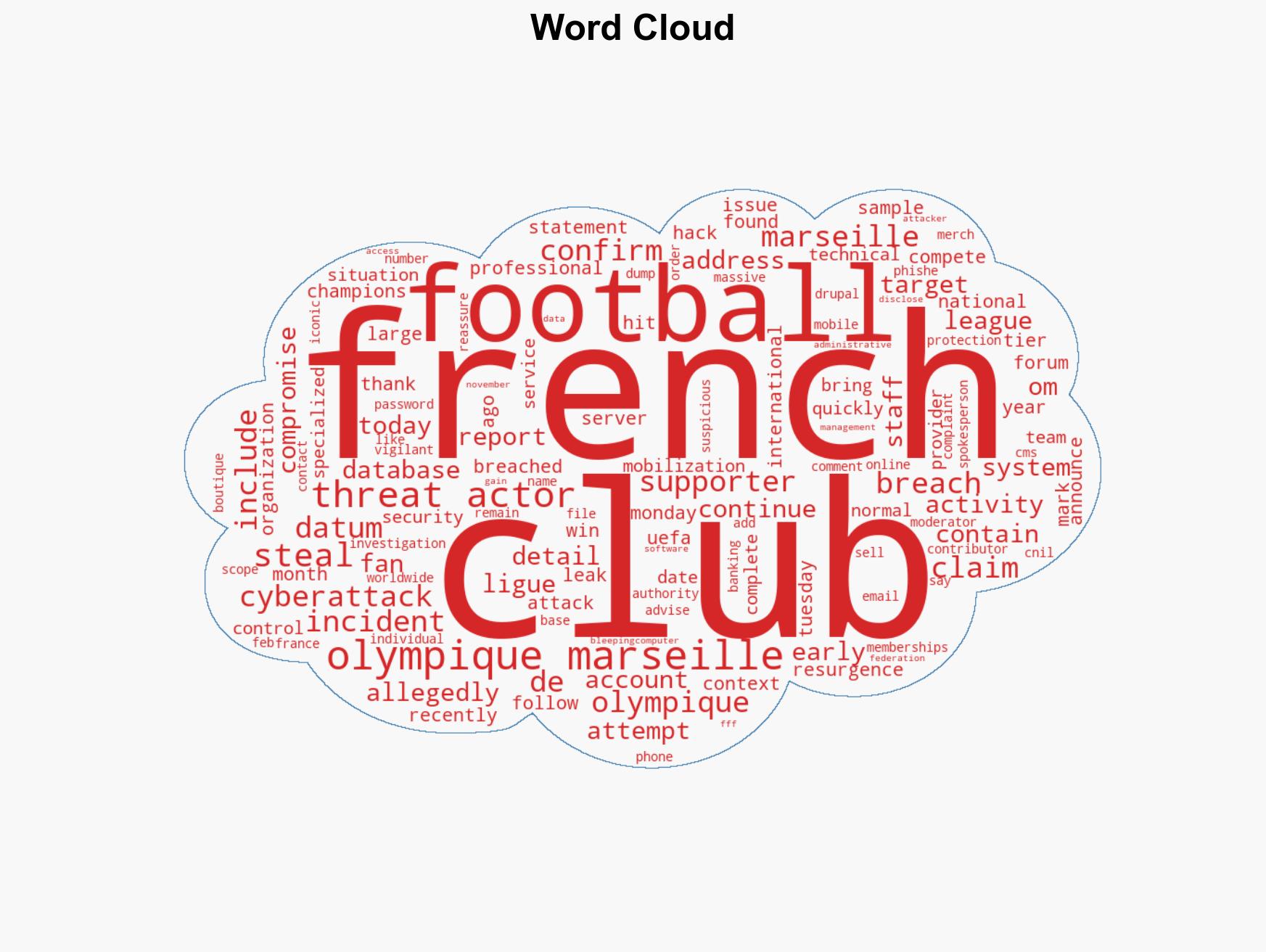
cybersecurity, data breach, sports organizations, information security, regulatory compliance, stakeholder trust
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us