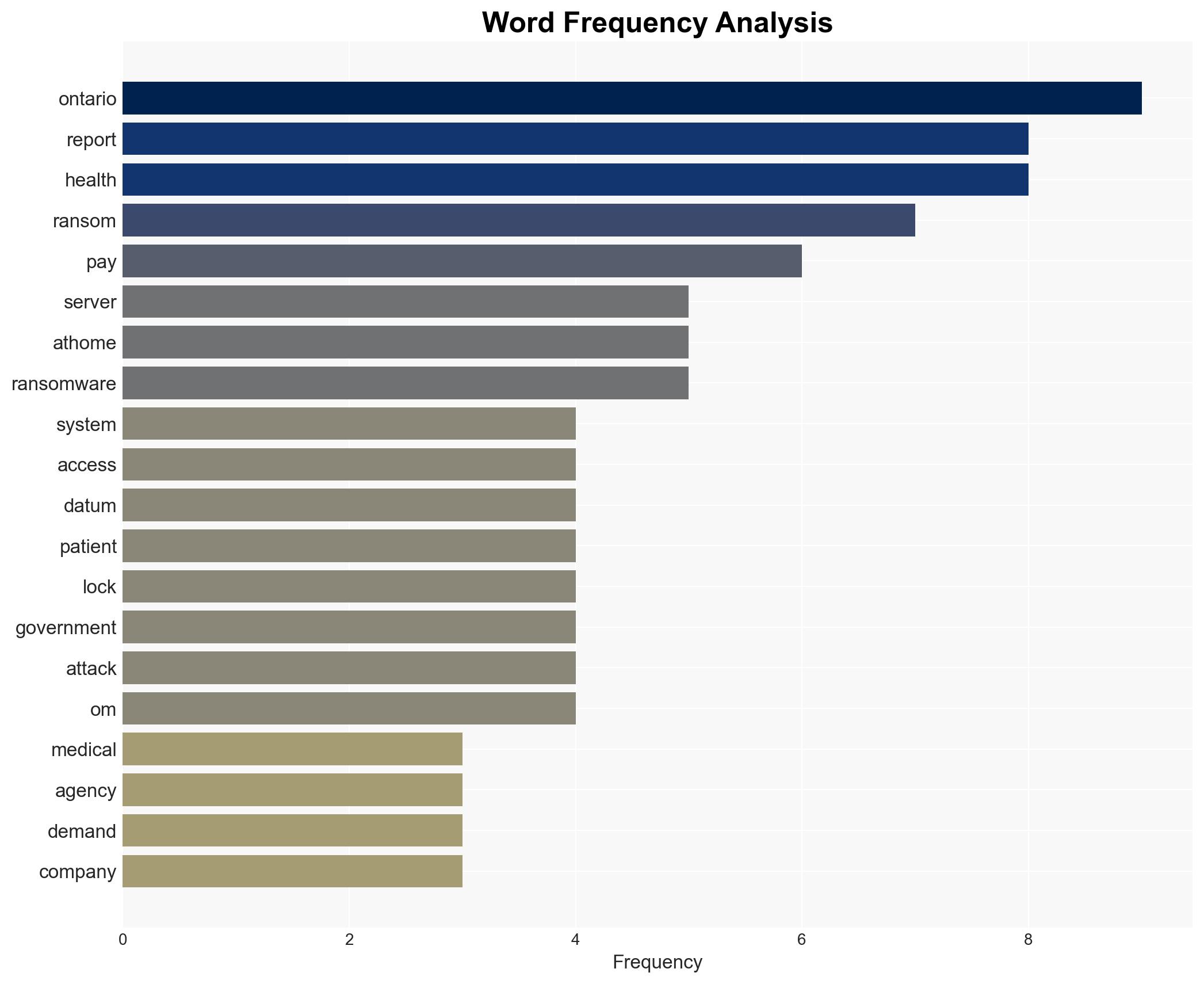
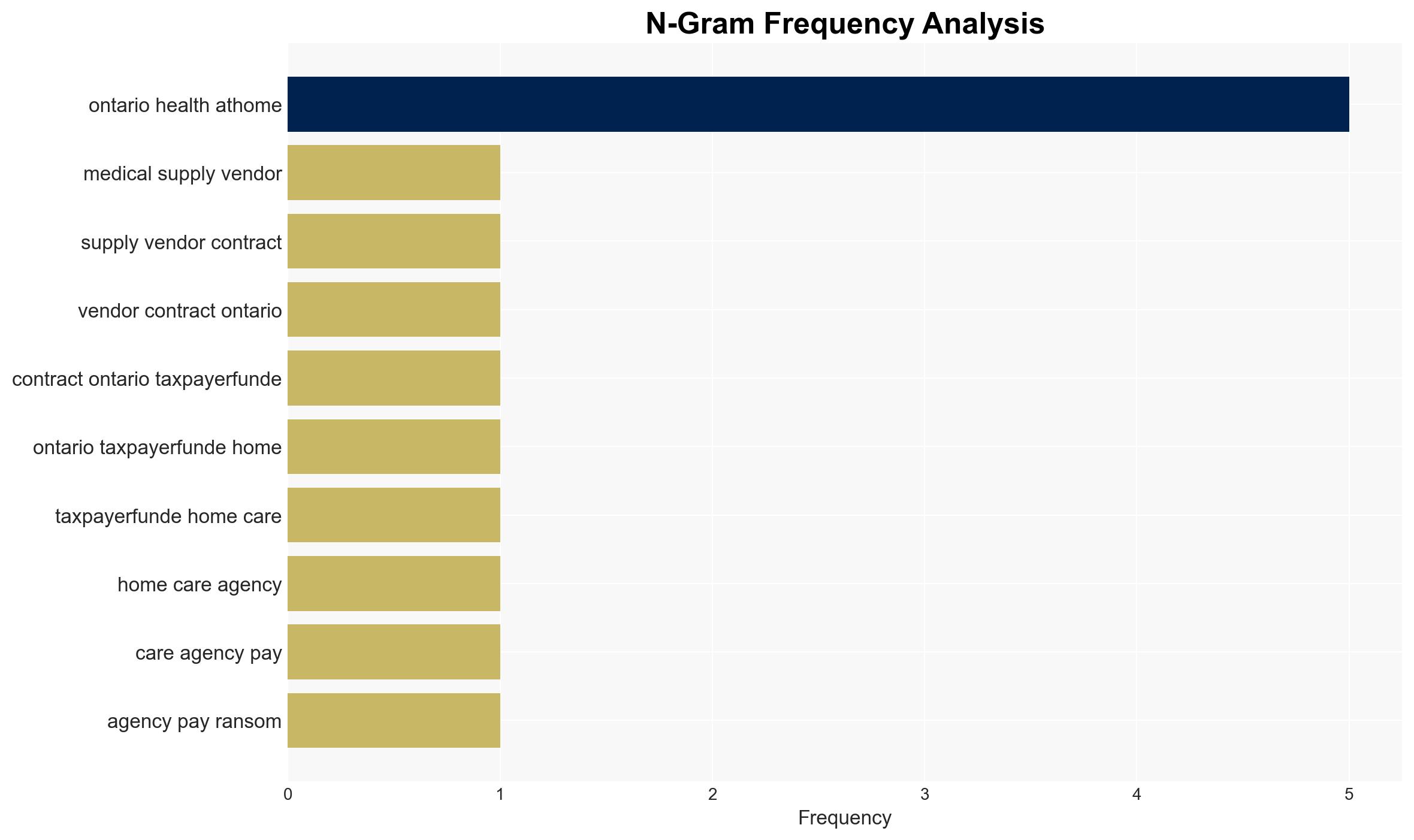
Ontario home care vendor reportedly paid ransom after ransomware attack compromised data of 200,000 patients
Published on: 2026-03-10
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
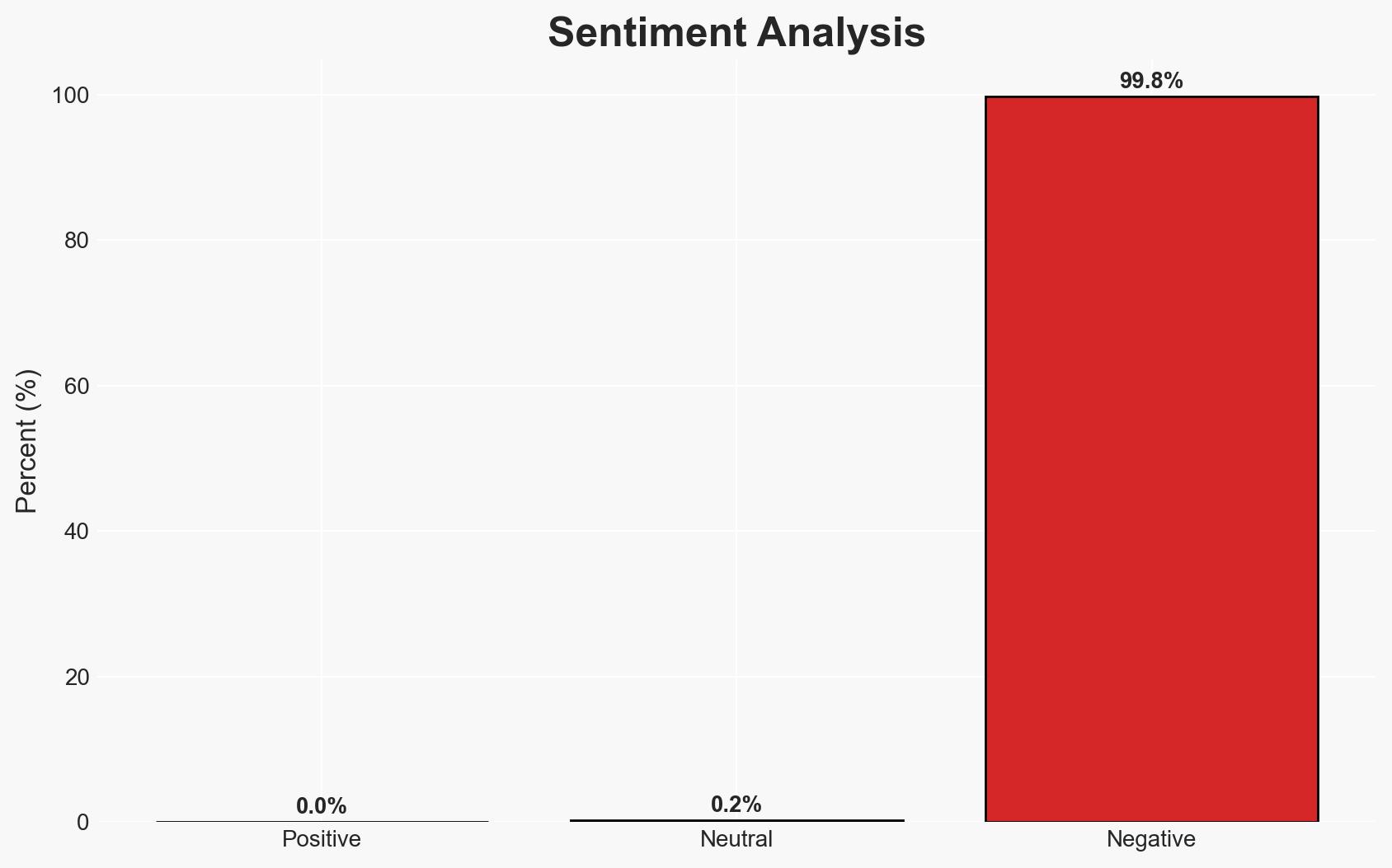
Intelligence Report: Ontario government home care vendor paid ransom to regain access to its servers report Globalnewsca
1. BLUF (Bottom Line Up Front)
A ransomware attack on Ontario Medical Supply (OMS) resulted in the payment of a ransom to regain access to locked servers, affecting up to 200,000 patients. The incident raises concerns about cybersecurity practices and potential taxpayer involvement. The most likely hypothesis is that OMS paid the ransom independently, with moderate confidence due to incomplete information on financial sources.
2. Competing Hypotheses
- Hypothesis A: OMS independently paid the ransom to regain access to its servers. This is supported by the report indicating a payment was made, but contradicted by the lack of clear evidence on the source of the funds. Key uncertainties include the exact financial arrangements and any indirect government involvement.
- Hypothesis B: The ransom payment involved taxpayer money, either directly or indirectly. This is suggested by political concerns raised about government involvement, but lacks direct evidence linking government funds to the payment.
- Assessment: Hypothesis A is currently better supported due to the explicit mention of OMS making the payment, although the source of funds remains unclear. Future disclosures or financial audits could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The ransomware attack was financially motivated; OMS had no alternative but to pay the ransom; no critical health data was exfiltrated; OMS acted independently in its decision to pay.
- Information Gaps: Specific details on the ransom payment source and amount; comprehensive audit of financial transactions related to the incident; full scope of data exfiltration.
- Bias & Deception Risks: Potential bias in OMS’s public statements minimizing data exfiltration; risk of deception in the attackers’ claims about data handling; political bias in interpreting government involvement.
4. Implications and Strategic Risks
This incident highlights vulnerabilities in healthcare cybersecurity and could lead to increased scrutiny and regulation. It may also encourage similar attacks if perceived as financially rewarding.
- Political / Geopolitical: Potential for political fallout if taxpayer funds were involved, leading to increased oversight and policy changes.
- Security / Counter-Terrorism: Increased risk of ransomware attacks targeting critical infrastructure, necessitating enhanced security measures.
- Cyber / Information Space: Potential for further cyber-attacks exploiting similar vulnerabilities; increased focus on cybersecurity resilience in healthcare.
- Economic / Social: Financial strain on OMS and potential loss of public trust; broader economic impact if healthcare systems are perceived as insecure.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a thorough audit of OMS’s financial transactions; enhance cybersecurity protocols; engage with cybersecurity experts to assess vulnerabilities.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms; implement comprehensive training for staff; establish a rapid response team for future incidents.
- Scenario Outlook:
- Best: Enhanced security measures prevent future attacks, restoring confidence.
- Worst: Continued cyber-attacks lead to significant data breaches and financial losses.
- Most-Likely: Incremental improvements in security with occasional incidents prompting further action.
6. Key Individuals and Entities
- Ontario Medical Supply (OMS)
- Ontario Health atHome
- Ministry of Health, Ontario
- Adil Shamji, Ontario Liberal MPP
- Information and Privacy Commissioner, Ontario
7. Thematic Tags
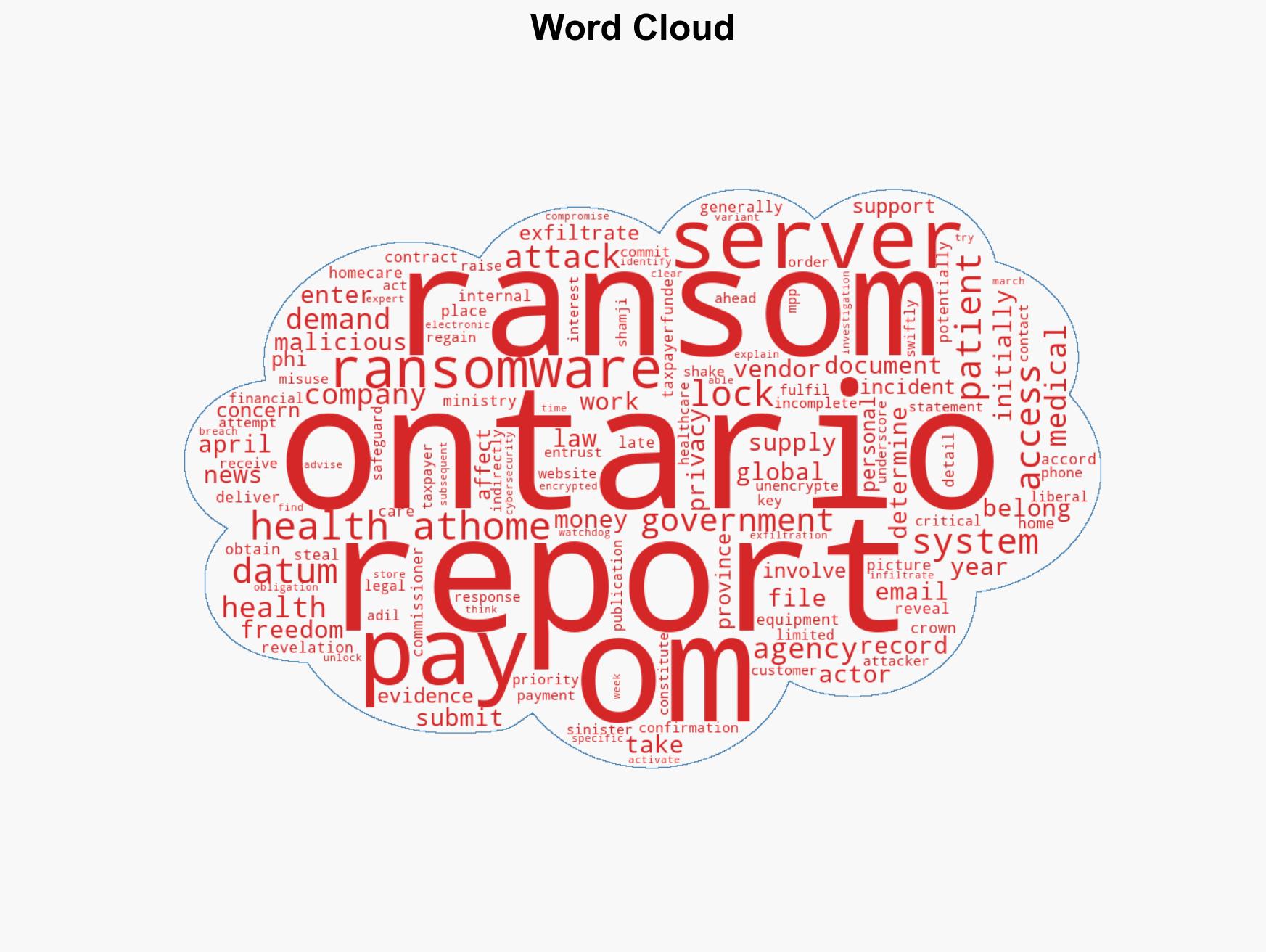
cybersecurity, ransomware, healthcare, data protection, government oversight, financial transparency, public trust
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us