OpenClaw vulnerability enables data theft via local AI agent exploitation, patch released in version 2026.2.26
Published on: 2026-03-02
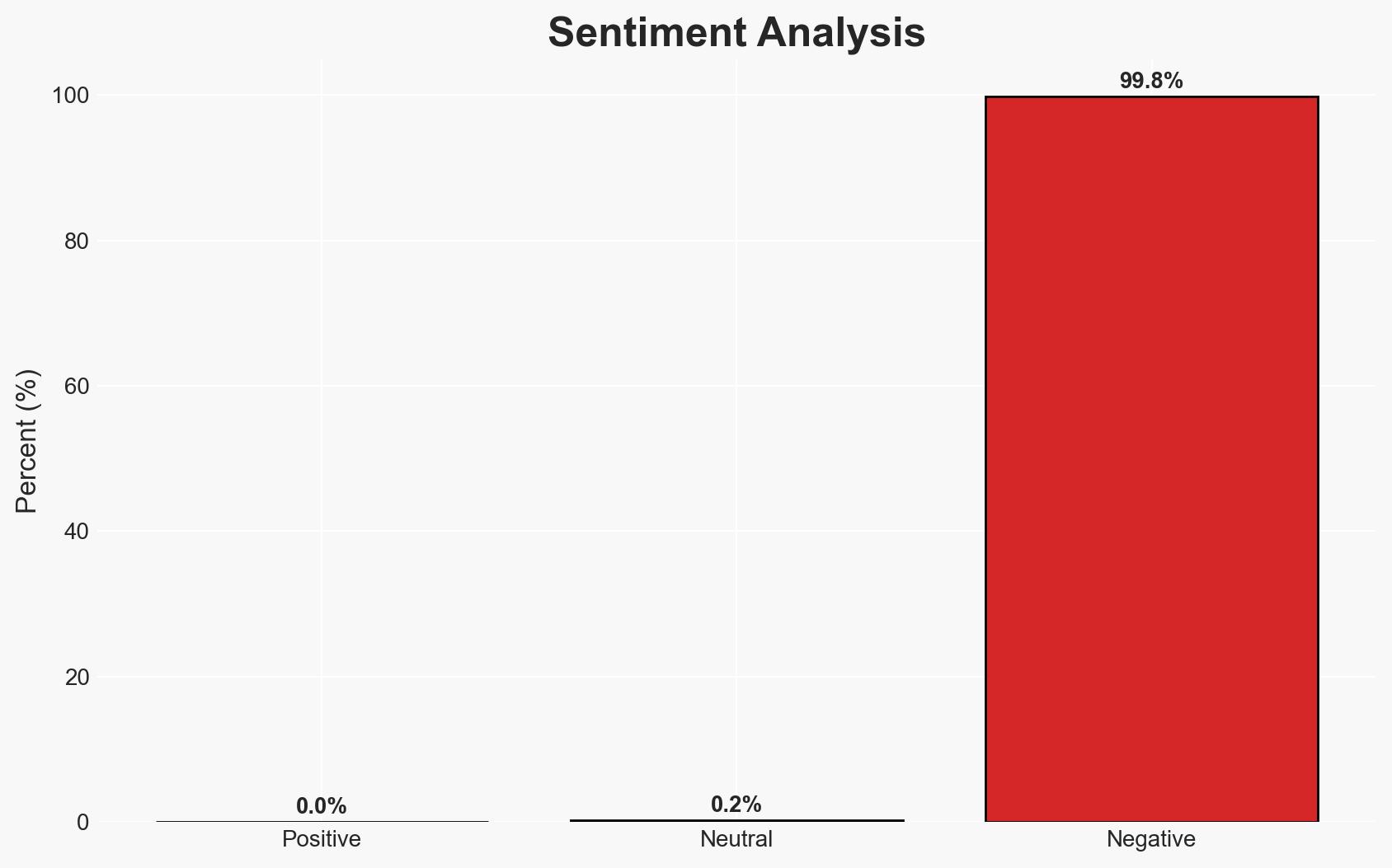
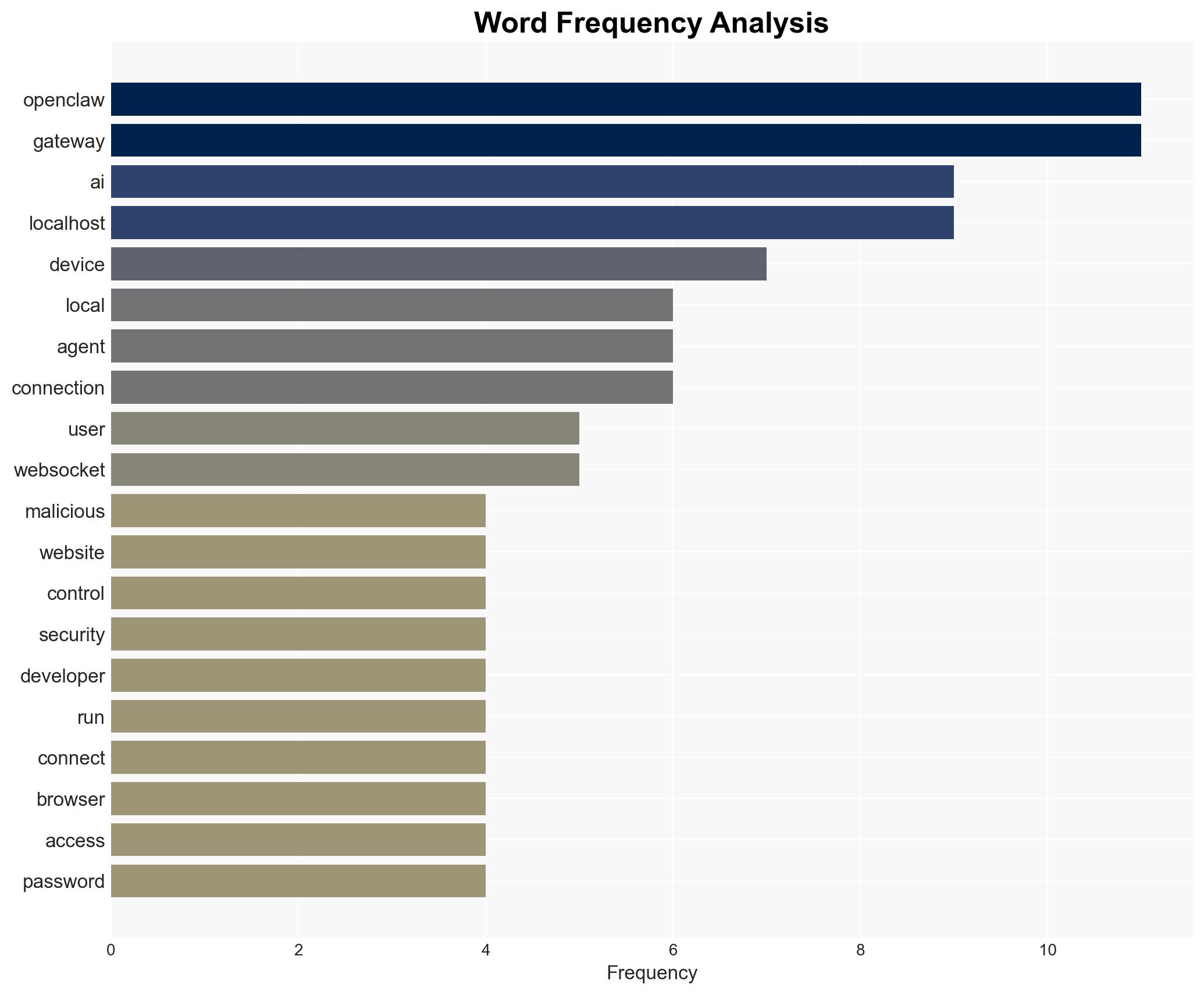
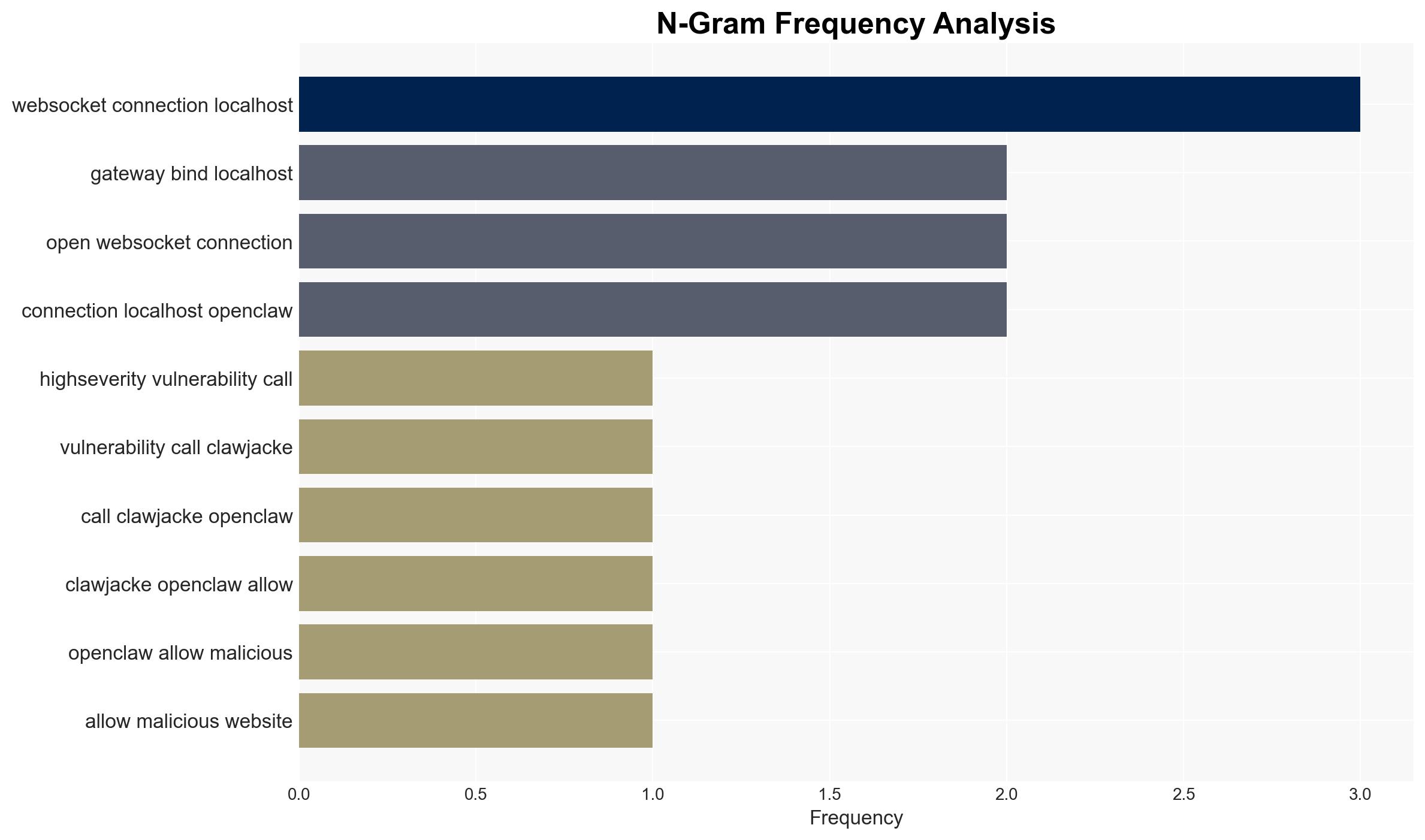
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: ClawJacked flaw exposed OpenClaw users to data theft
1. BLUF (Bottom Line Up Front)
The ClawJacked vulnerability in OpenClaw presents a significant security risk, allowing malicious websites to hijack local AI agent instances and access sensitive data. This affects users who run OpenClaw with the gateway bound to localhost. The most supported hypothesis is that the vulnerability stems from inherent design flaws in the OpenClaw architecture. Overall confidence in this assessment is moderate, pending further data on exploitation instances.
2. Competing Hypotheses
- Hypothesis A: The vulnerability is primarily due to architectural flaws in OpenClaw’s design, specifically its trust of localhost traffic and lack of rate limiting. This is supported by the design details and the attack chain described. Key uncertainties include the prevalence of exploitation and whether similar vulnerabilities exist in comparable systems.
- Hypothesis B: The vulnerability was introduced through a recent update or misconfiguration, rather than inherent design flaws. This is less supported given the consistent design issues highlighted by Oasis Security. However, without detailed version history analysis, this cannot be entirely ruled out.
- Assessment: Hypothesis A is currently better supported due to the detailed architectural weaknesses identified. Indicators that could shift this judgment include evidence of similar vulnerabilities in other systems or confirmation of recent code changes introducing the flaw.
3. Key Assumptions and Red Flags
- Assumptions: OpenClaw’s design inherently trusts localhost traffic; the vulnerability affects all versions prior to the patch; exploitation requires user interaction with a malicious site.
- Information Gaps: Data on the number of affected users and instances of active exploitation; details on potential mitigations prior to the patch.
- Bias & Deception Risks: Potential bias from Oasis Security’s report focusing on architectural flaws; risk of underestimating the vulnerability’s exploitation scope due to lack of widespread reporting.
4. Implications and Strategic Risks
This vulnerability could have significant implications for users of OpenClaw, particularly developers and organizations relying on AI automation. The flaw may also prompt scrutiny of similar open-source frameworks.
- Political / Geopolitical: Limited direct implications, but potential for increased regulatory scrutiny on open-source security practices.
- Security / Counter-Terrorism: Increased risk of cyber espionage or data theft targeting organizations using OpenClaw.
- Cyber / Information Space: Potential for exploitation in broader cyber operations, highlighting vulnerabilities in AI frameworks.
- Economic / Social: Potential economic impact on organizations relying on OpenClaw for automation, leading to operational disruptions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urgently apply the patch (version 2026.2.26) to all OpenClaw instances; conduct security audits to identify similar vulnerabilities.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms to enhance open-source security; invest in user education on safe browsing practices.
- Scenario Outlook:
- Best: Vulnerability is fully mitigated with no further exploitation, leading to improved security practices.
- Worst: Widespread exploitation leads to significant data breaches and loss of trust in open-source AI frameworks.
- Most-Likely: Patch adoption mitigates immediate risks, but similar vulnerabilities emerge in other systems, prompting ongoing security challenges.
6. Key Individuals and Entities
- Oasis Security (discoverer of the vulnerability)
- OpenClaw (developer of the affected software)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
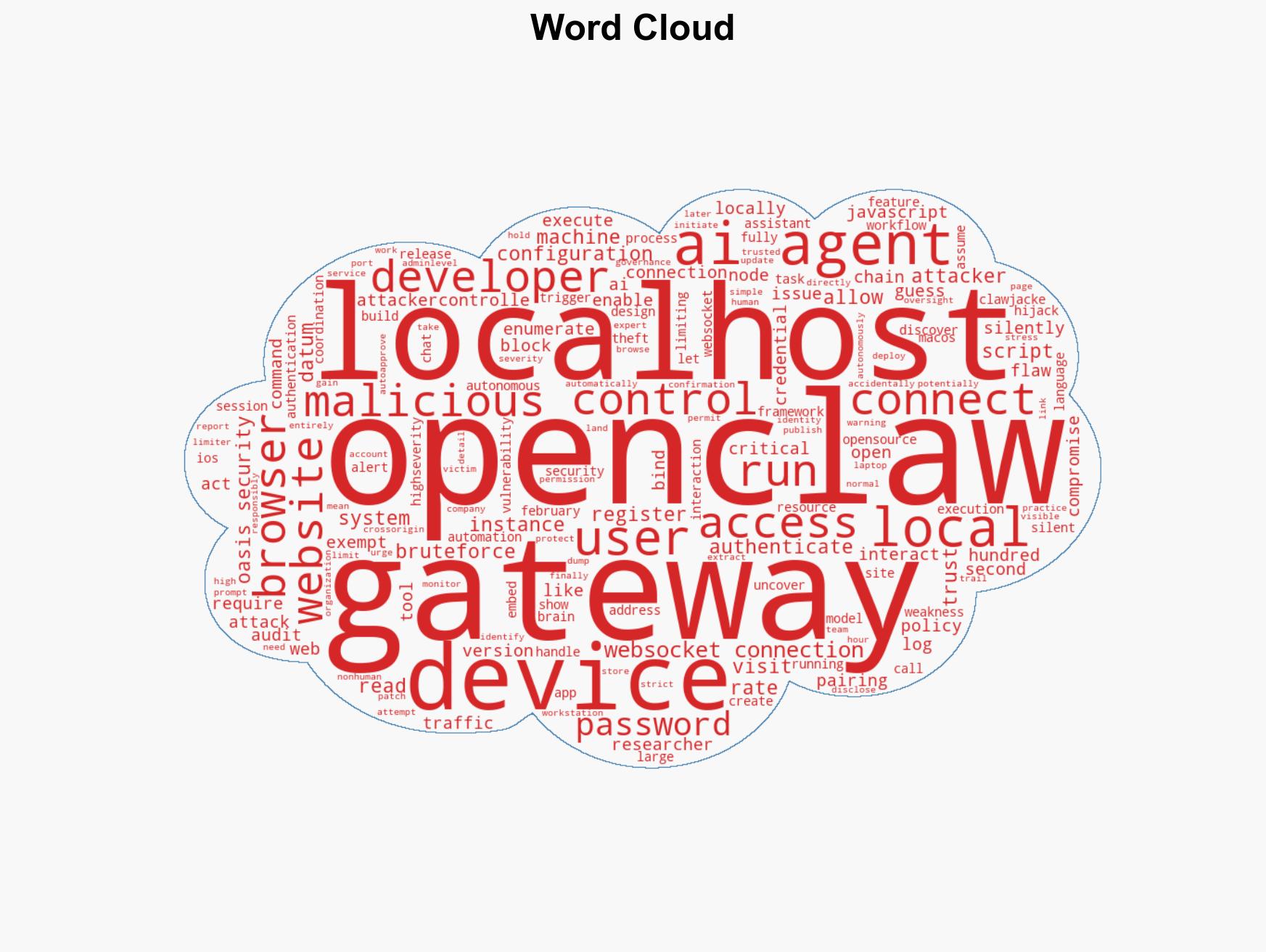
cybersecurity, open-source software, AI vulnerabilities, data theft, cyber-espionage, software patching
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us