Organizations Must Act Now to Safeguard Data Against Future Quantum Decryption Threats
Published on: 2026-02-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Expert Recommends Prepare for PQC Right Now
1. BLUF (Bottom Line Up Front)
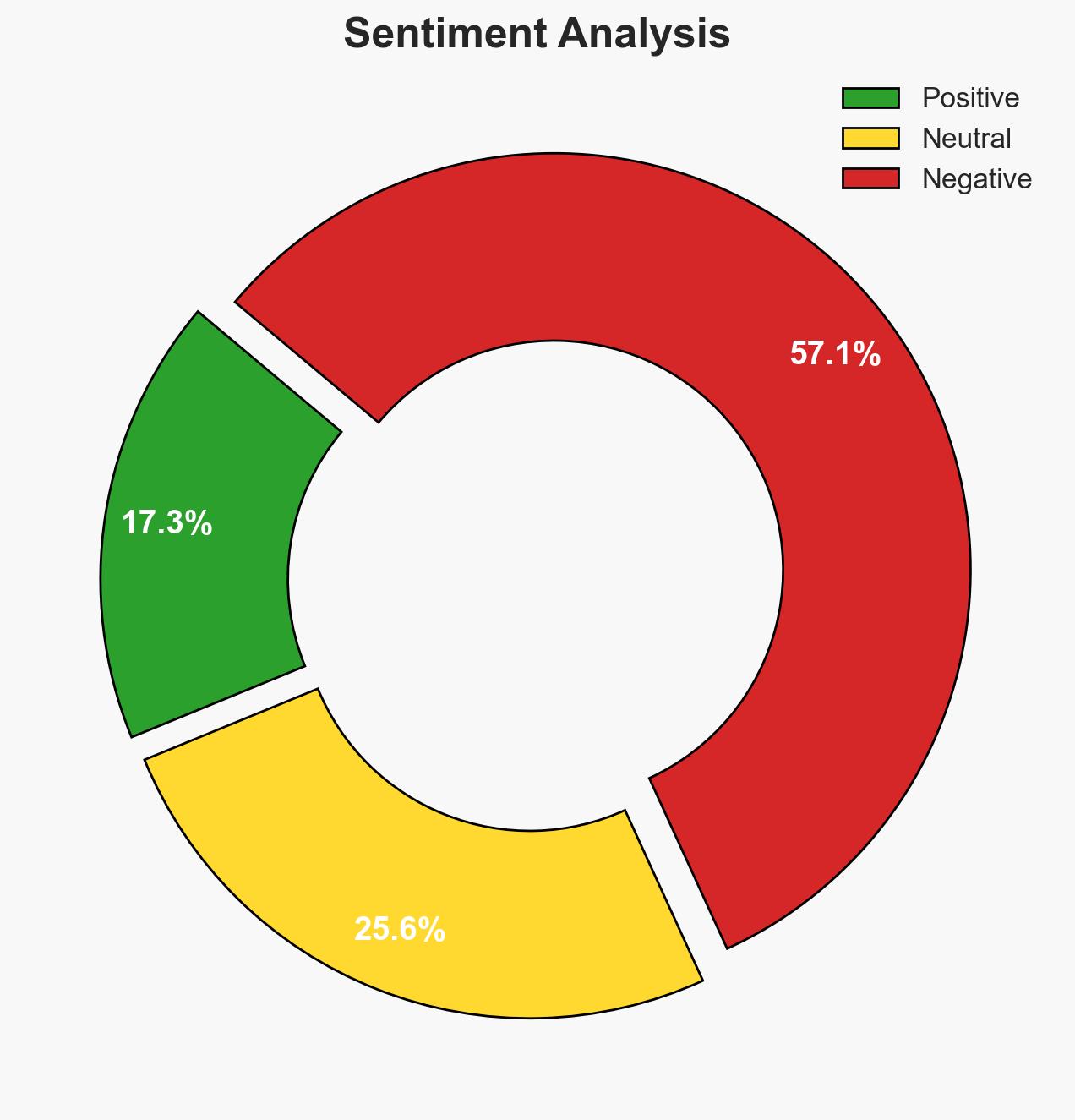
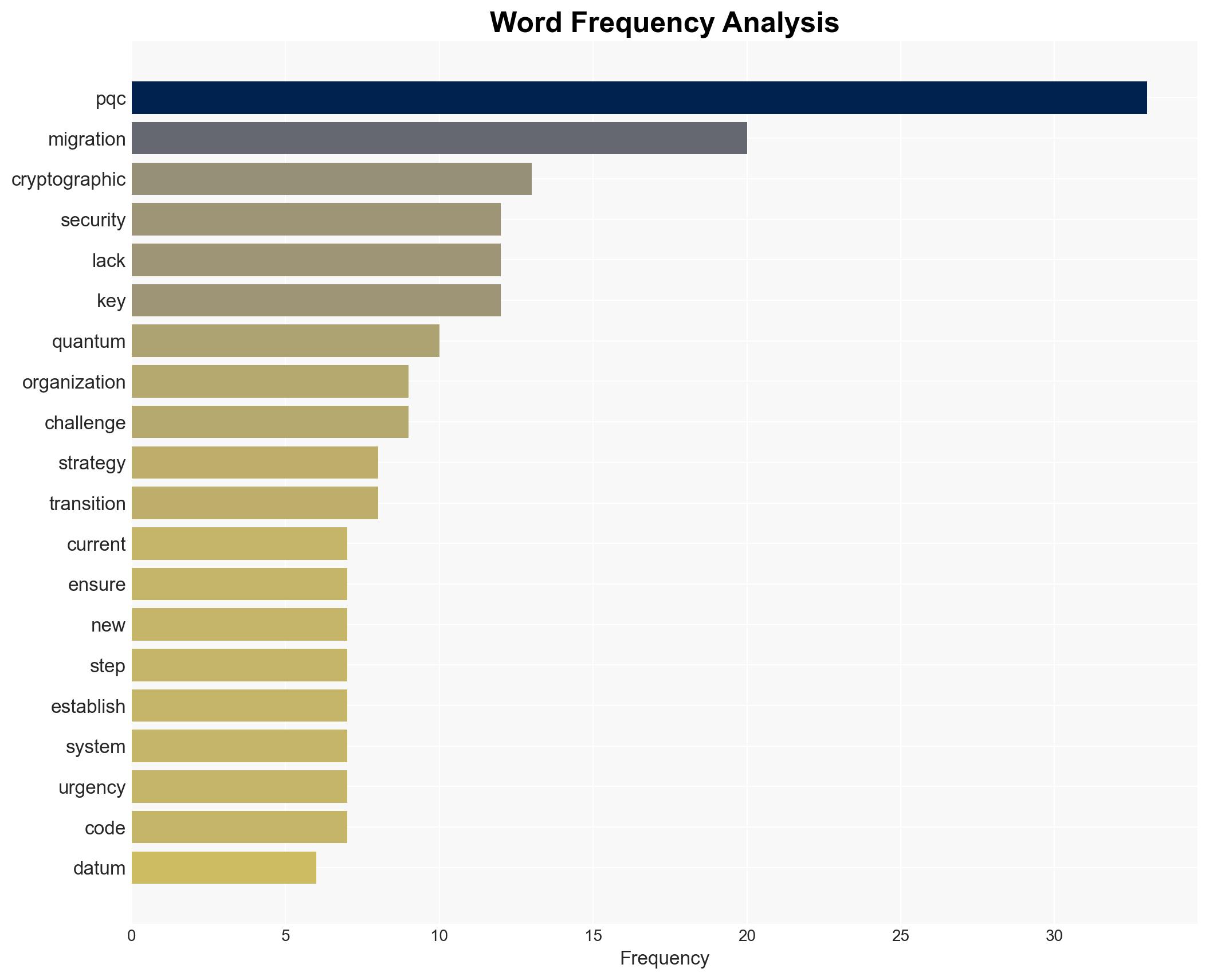
The imminent threat posed by quantum computing to current encryption standards necessitates immediate preparation for Post-Quantum Cryptography (PQC) migration. Organizations holding sensitive data must act to secure information against future quantum-enabled decryption. The most likely hypothesis is that adversaries will exploit the “Harvest Now, Decrypt Later” strategy, targeting data with long-term value. Confidence in this assessment is moderate, given the current state of quantum computing technology and industry readiness.
2. Competing Hypotheses
- Hypothesis A: Quantum computing will mature by 2030-2035, enabling adversaries to decrypt currently secure data, necessitating immediate PQC migration. This is supported by the ongoing development of quantum technologies and the “Harvest Now, Decrypt Later” strategy. However, uncertainties remain regarding the exact timeline for achieving cryptographically relevant quantum computers (CRQC).
- Hypothesis B: Quantum computing will not achieve the necessary capabilities to threaten current encryption within the next two decades, allowing more time for PQC migration. This is contradicted by the rapid advancements in quantum research and the strategic interest in quantum capabilities by state and non-state actors.
- Assessment: Hypothesis A is currently better supported due to the strategic interest in quantum computing and the potential for rapid technological breakthroughs. Indicators such as advancements in error correction and scaling of quantum computers could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Quantum computing will advance to a cryptographically relevant stage by 2030-2035; adversaries will continue to prioritize data with long-term value; current encryption standards will be vulnerable to future quantum attacks.
- Information Gaps: Precise timeline for quantum computing advancements; specific adversary capabilities and intentions regarding quantum decryption.
- Bias & Deception Risks: Potential overestimation of quantum computing capabilities; reliance on industry projections that may be optimistic or influenced by vested interests.
4. Implications and Strategic Risks
The development of quantum computing could significantly alter the security landscape, necessitating a reevaluation of cryptographic standards and data protection strategies.
- Political / Geopolitical: Nations may accelerate quantum research, leading to a technological arms race and potential geopolitical tensions.
- Security / Counter-Terrorism: Enhanced capabilities for data decryption could increase the effectiveness of cyber espionage and disrupt counter-terrorism operations.
- Cyber / Information Space: The threat of quantum decryption could lead to increased cyber extortion and data breaches, undermining trust in digital communications.
- Economic / Social: Economic sectors reliant on secure data transmission may face increased risks, affecting financial stability and consumer trust.
5. Recommendations and Outlook
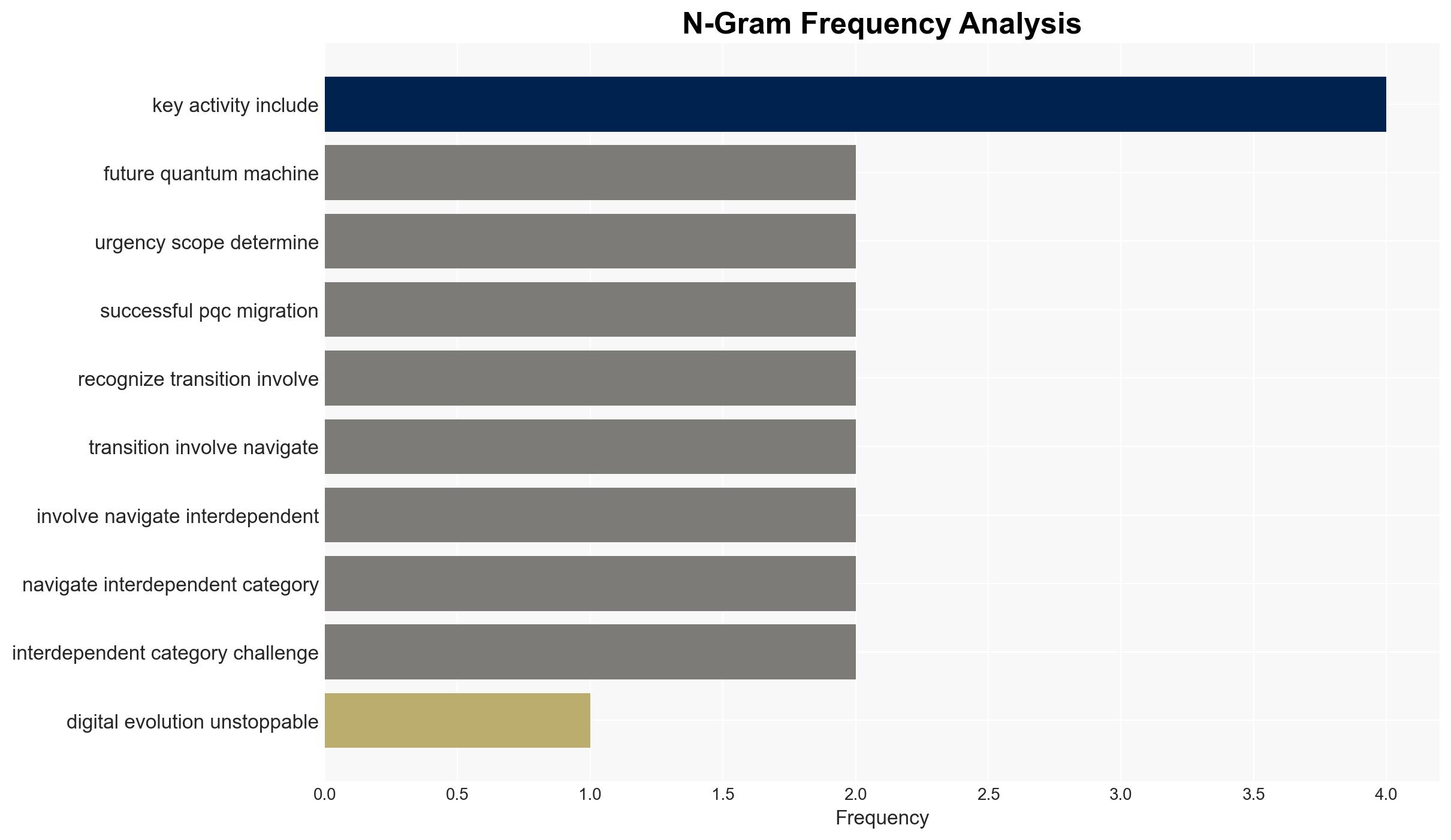
- Immediate Actions (0–30 days): Initiate PQC readiness assessments; enhance monitoring of quantum computing advancements; engage with industry experts for guidance.
- Medium-Term Posture (1–12 months): Develop a comprehensive PQC migration strategy; establish partnerships with technology providers; invest in workforce training for new cryptographic standards.
- Scenario Outlook:
- Best: Quantum computing advances slowly, allowing ample time for PQC adoption.
- Worst: Rapid quantum breakthroughs lead to widespread data breaches before PQC migration is complete.
- Most-Likely: Gradual advancements in quantum technology necessitate phased PQC implementation.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
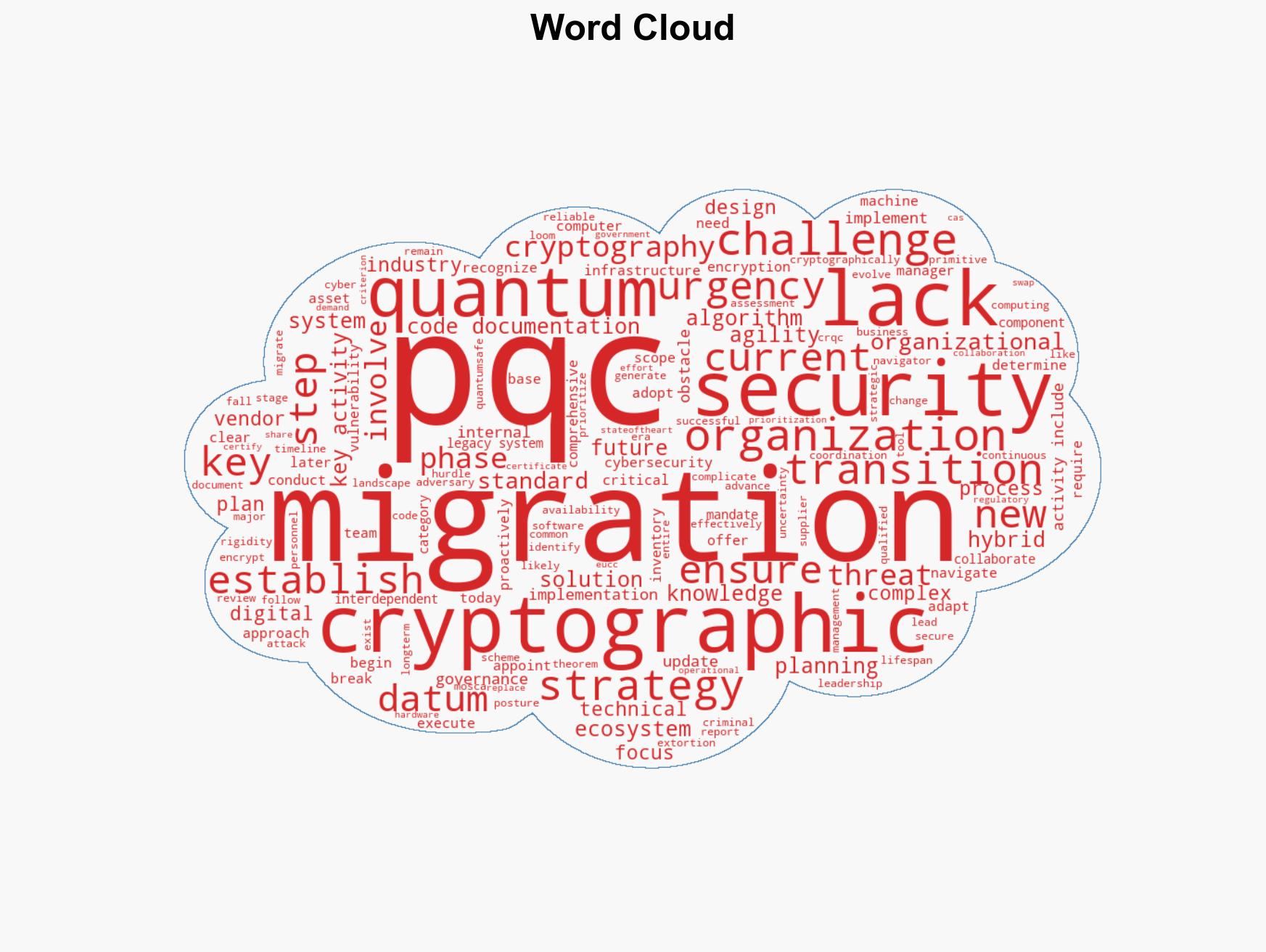
cybersecurity, quantum computing, cryptography, cyber security, data protection, cyber threats, digital trust, encryption
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us