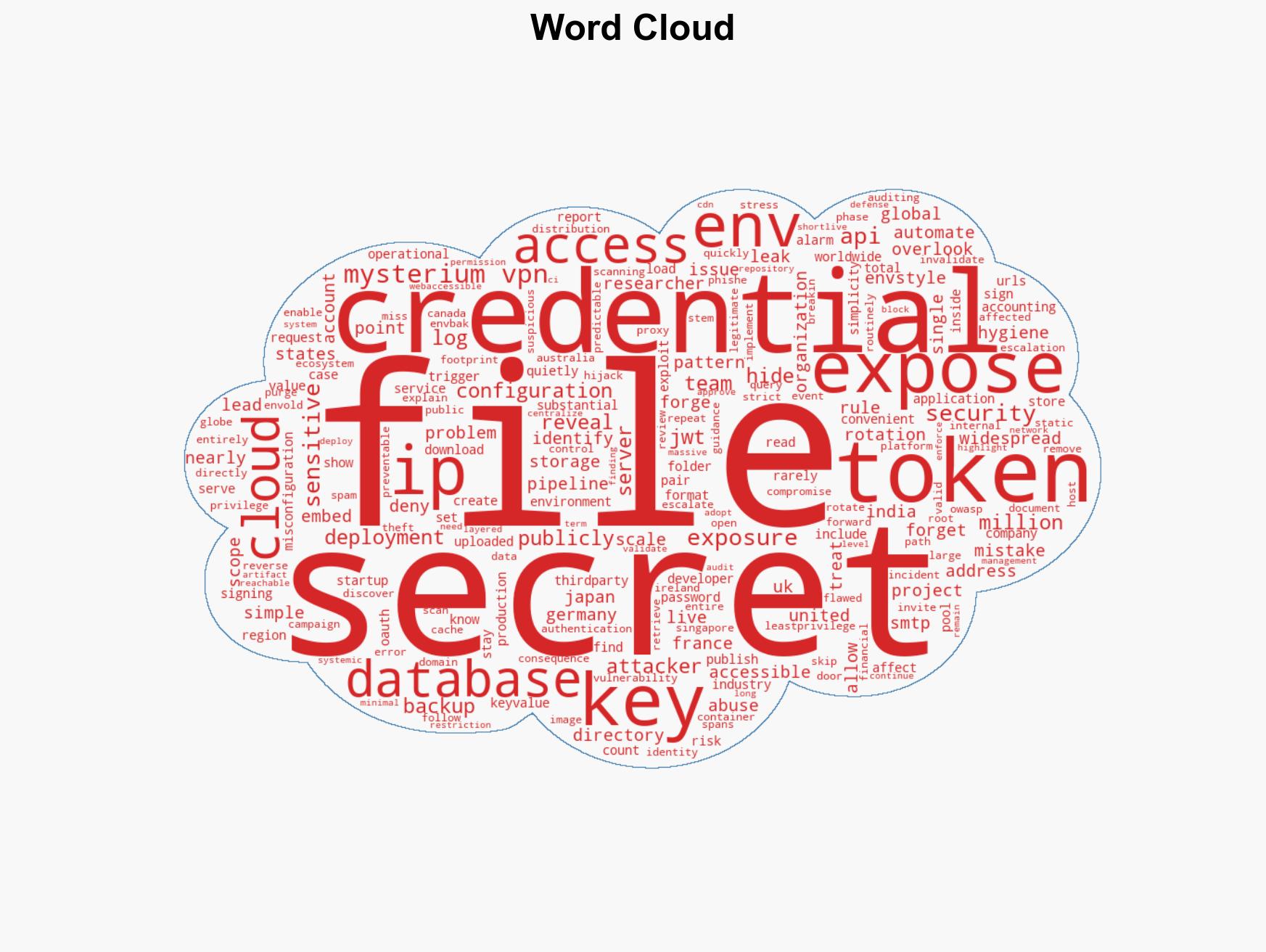
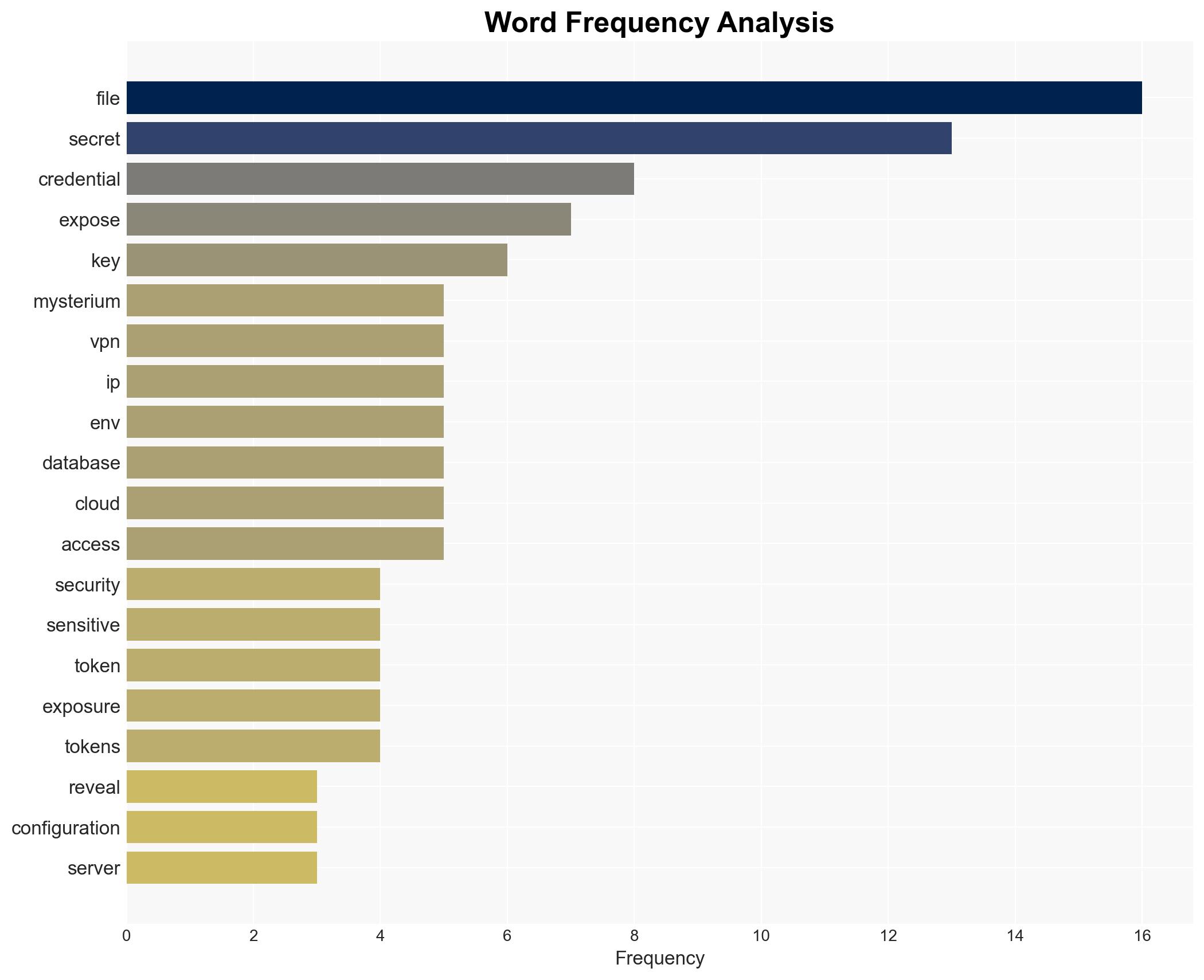
Over 12 Million IP Addresses Expose .env Files, Highlighting Global Security Vulnerabilities
Published on: 2026-02-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: 12 Million exposed env files reveal widespread security failures
1. BLUF (Bottom Line Up Front)
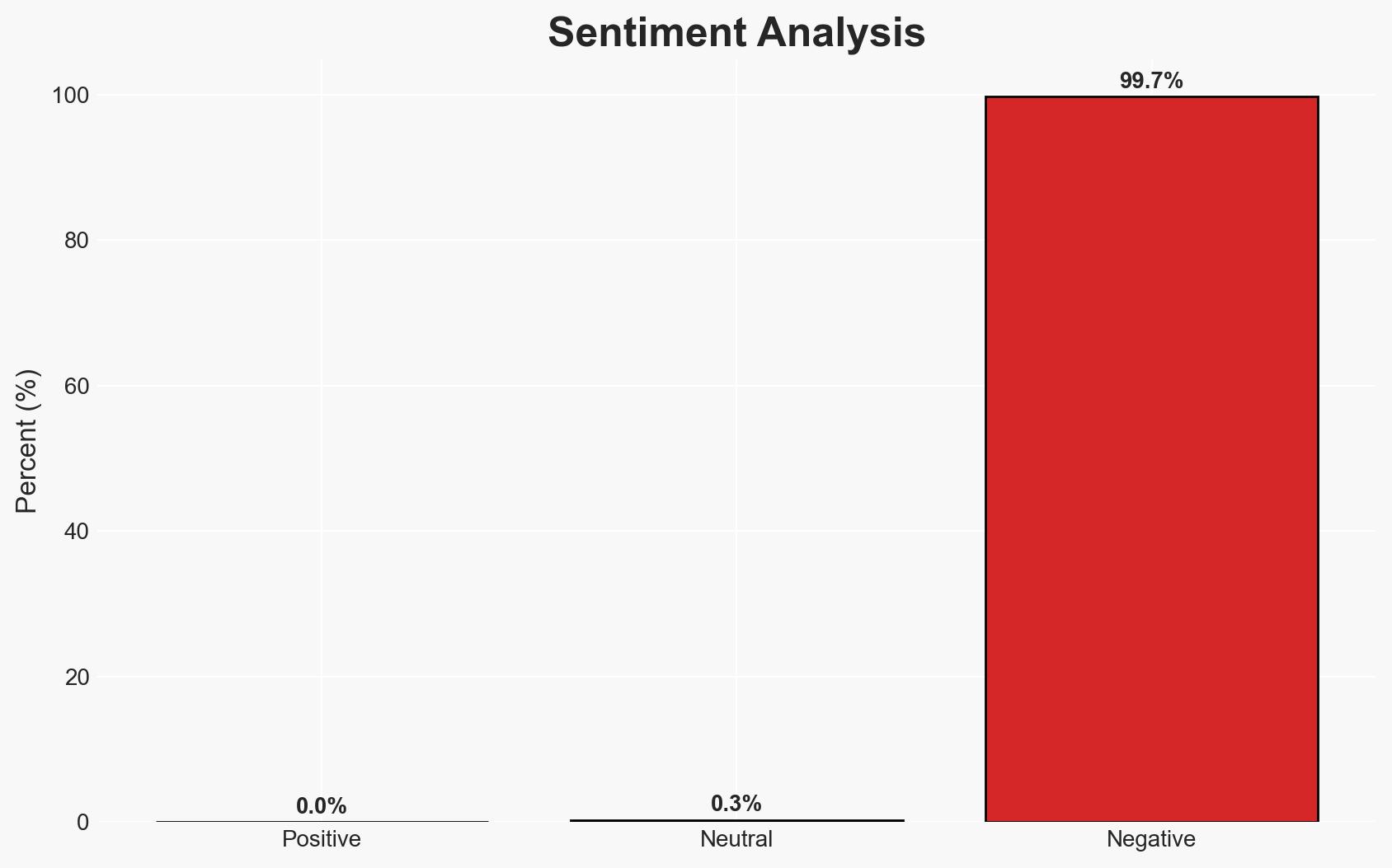
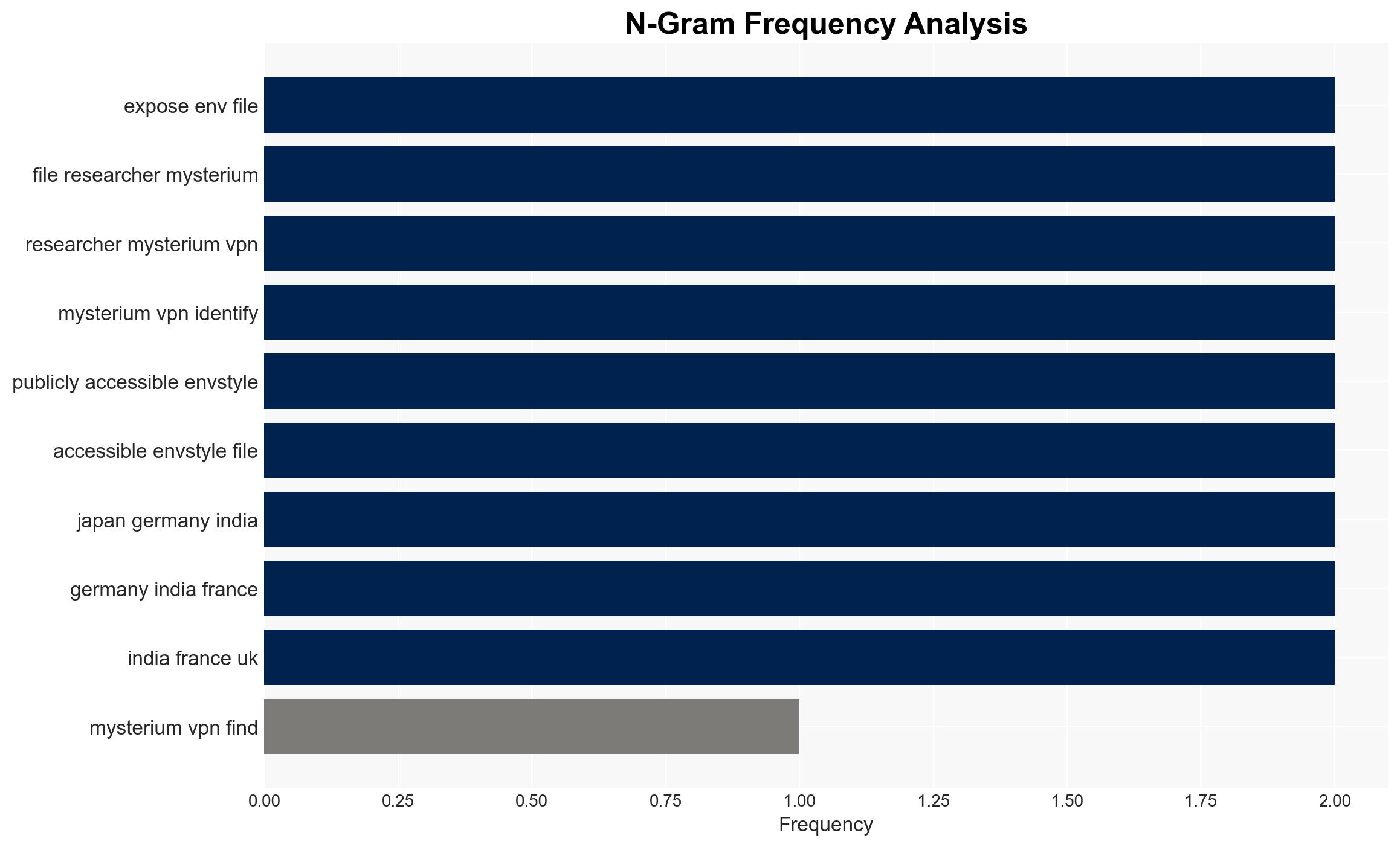
The exposure of over 12 million IP addresses with publicly accessible .env files represents a significant global security vulnerability, primarily due to poor operational security practices. The United States is the most affected, but the issue spans multiple countries, indicating a systemic problem. This vulnerability could lead to severe data breaches and exploitation by threat actors. Overall confidence in this assessment is moderate, given the scale and distribution of the exposure.
2. Competing Hypotheses
- Hypothesis A: The widespread exposure of .env files is primarily due to systemic operational security failures across multiple organizations and industries. Evidence supporting this includes the global distribution of affected IPs and the nature of the exposed data. However, the lack of specific organizational data limits the ability to pinpoint precise causes.
- Hypothesis B: The exposure is the result of a coordinated cyber campaign exploiting known vulnerabilities in server configurations. While the scale and uniformity of the issue might suggest coordinated action, there is currently no direct evidence supporting this hypothesis.
- Assessment: Hypothesis A is currently better supported due to the widespread nature and distribution of the exposures, which align more closely with common operational security lapses rather than a targeted campaign. Indicators such as the discovery of specific exploit tools or patterns could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Organizations have not implemented adequate security controls; the exposure is not the result of a single platform flaw; threat actors are likely to exploit these vulnerabilities.
- Information Gaps: Specific organizational data and incident reports; detailed analysis of potential exploitation by threat actors.
- Bias & Deception Risks: Potential bias in reporting from Mysterium VPN; lack of corroborative data from other cybersecurity entities; possibility of deliberate misinformation by affected organizations to downplay the issue.
4. Implications and Strategic Risks
The exposure of sensitive credentials could lead to significant data breaches and exploitation by cybercriminals, impacting organizational integrity and national security. Over time, this could erode trust in digital infrastructures and increase regulatory scrutiny.
- Political / Geopolitical: Potential for increased international tensions if state actors are implicated in exploiting these vulnerabilities.
- Security / Counter-Terrorism: Increased risk of cyber-attacks and data breaches, potentially facilitating terrorism financing or operations.
- Cyber / Information Space: Heightened vulnerability to cyber espionage and information warfare, with potential impacts on critical infrastructure.
- Economic / Social: Potential economic losses from data breaches and increased costs for cybersecurity measures; erosion of public trust in digital services.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a rapid assessment of exposed IPs; implement immediate security patches and configuration reviews; increase monitoring for exploitation attempts.
- Medium-Term Posture (1–12 months): Develop and enforce stricter operational security protocols; enhance cross-industry collaboration on security best practices; invest in cybersecurity training and awareness.
- Scenario Outlook:
- Best: Rapid mitigation reduces exposure, leading to minimal exploitation.
- Worst: Widespread exploitation results in significant data breaches and economic damage.
- Most-Likely: Gradual improvement in security practices with sporadic exploitation incidents.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, data breach, operational security, global security, cyber hygiene, information security, vulnerability management
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us