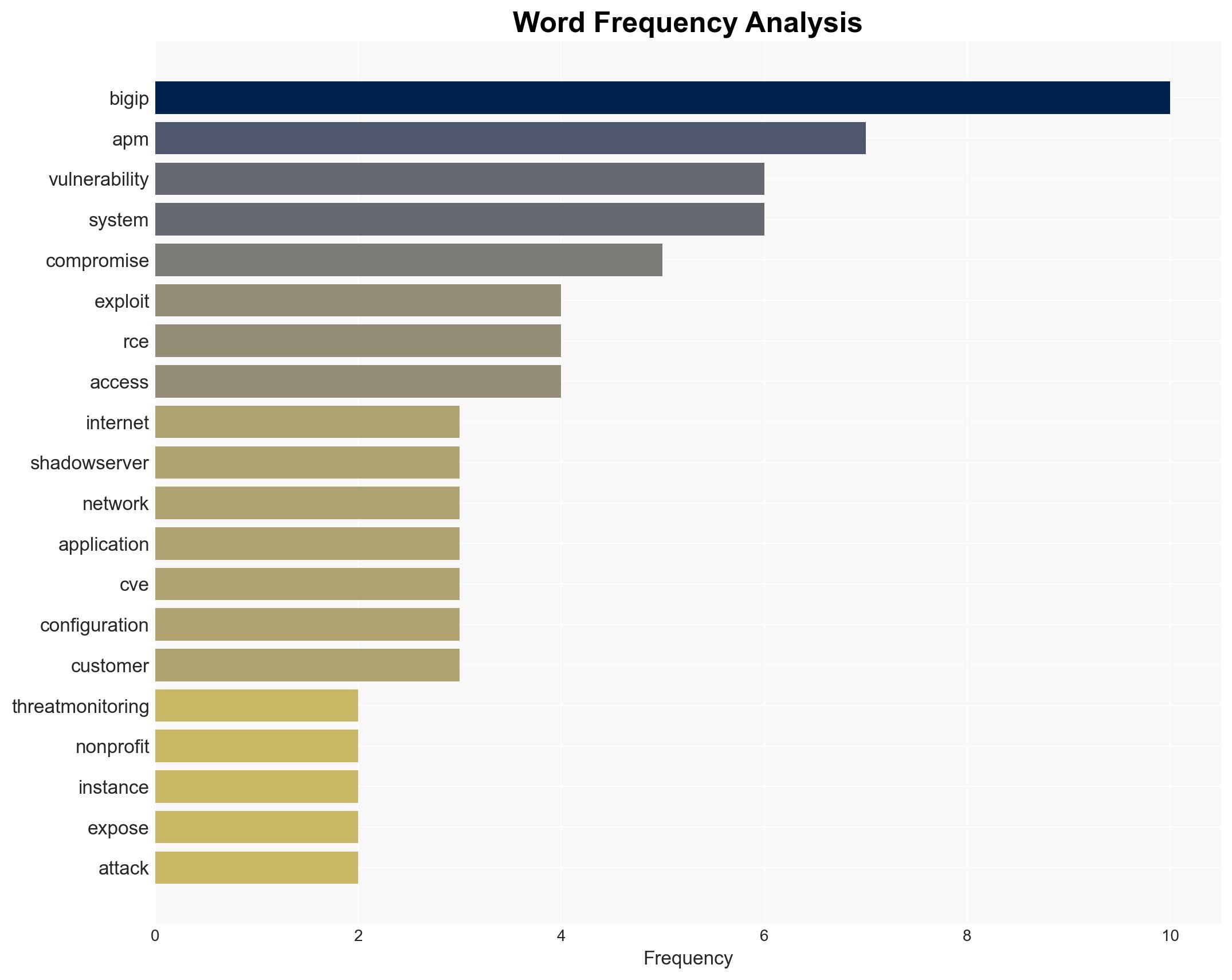
Over 14,000 F5 BIG-IP APM Instances Vulnerable to Remote Code Execution Exploits
Published on: 2026-04-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Over 14000 F5 BIG-IP APM instances still exposed to RCE attacks
1. BLUF (Bottom Line Up Front)
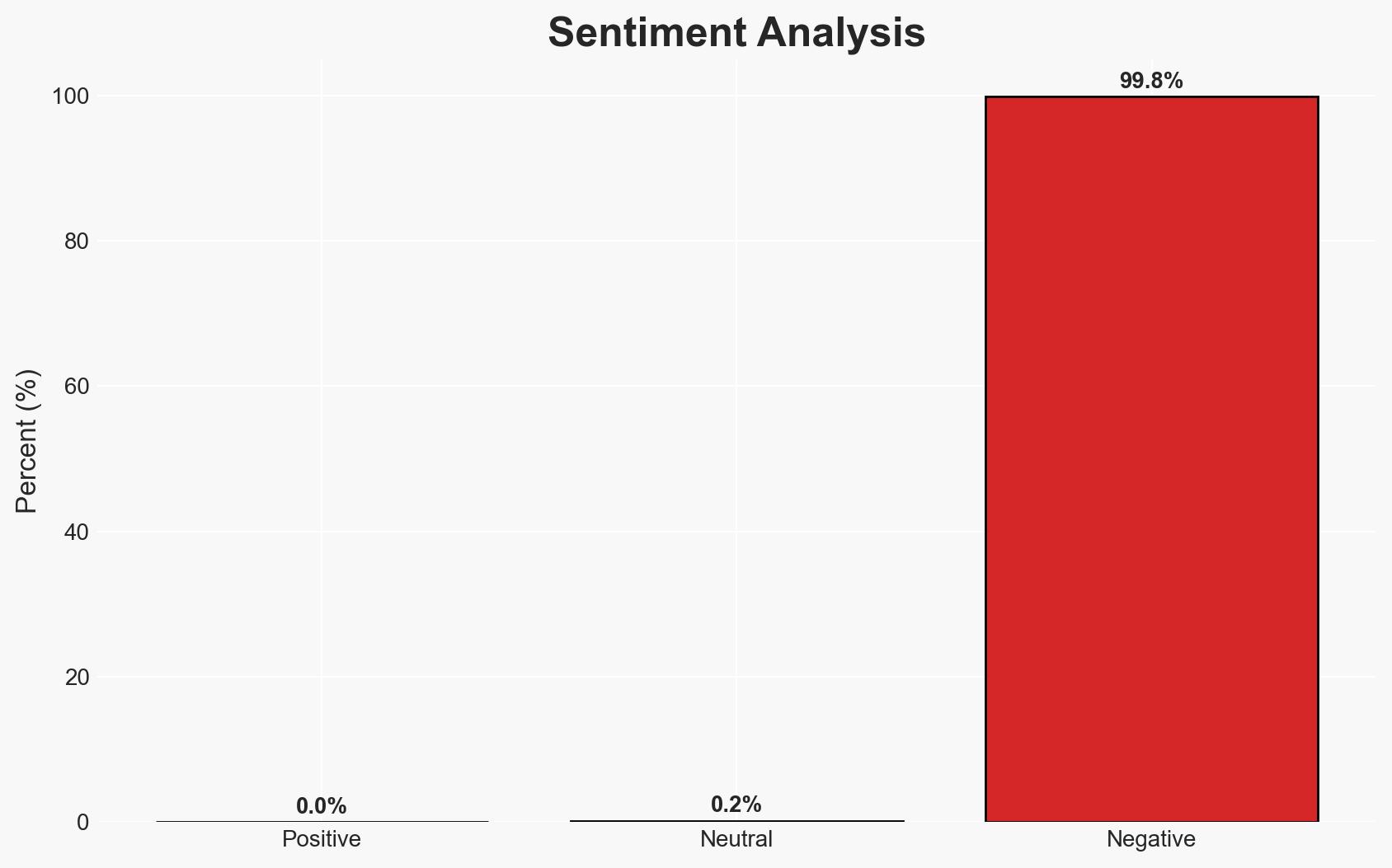
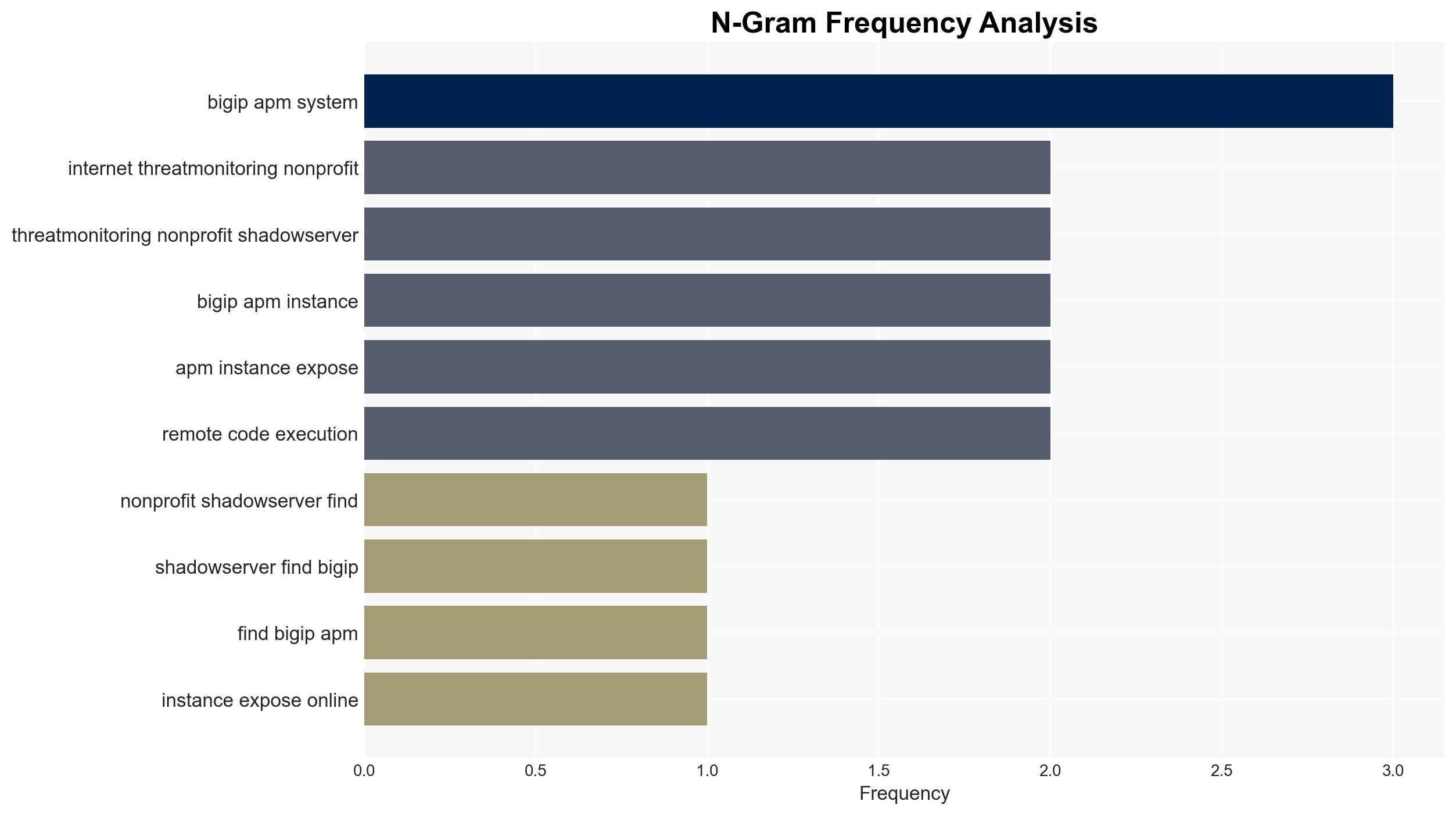
Over 14,000 F5 BIG-IP APM instances remain vulnerable to a critical remote code execution (RCE) attack, posing significant risks to organizations using these systems. This vulnerability, initially classified as a denial-of-service issue, has been actively exploited, potentially compromising sensitive data and network integrity. The situation requires urgent remediation efforts, particularly for organizations within critical infrastructure sectors. Overall confidence in this assessment is moderate due to the lack of detailed exposure data.
2. Competing Hypotheses
- Hypothesis A: The majority of exposed BIG-IP APM instances are actively being targeted by nation-state actors seeking to exploit vulnerabilities for espionage or disruptive purposes. This is supported by historical targeting of BIG-IP vulnerabilities by such groups. However, the lack of specific attribution data limits certainty.
- Hypothesis B: Cybercriminal groups are primarily exploiting the RCE vulnerability for financial gain, such as deploying ransomware or stealing data for resale. This is plausible given the high number of exposed instances and the financial incentives involved. Contradictory evidence includes the absence of reported financial demands or data leaks linked to these attacks thus far.
- Assessment: Hypothesis A is currently better supported due to the strategic interest nation-states have in exploiting vulnerabilities in widely used infrastructure components. Key indicators that could shift this judgment include evidence of financial transactions or ransomware demands linked to the exploitation of these vulnerabilities.
3. Key Assumptions and Red Flags
- Assumptions: Organizations have not uniformly applied patches; attackers have the capability to exploit the RCE vulnerability; the vulnerability is of high interest to both nation-state and cybercriminal actors.
- Information Gaps: Precise data on which organizations are affected; detailed attribution of the threat actors involved; specific methods of exploitation being used.
- Bias & Deception Risks: Potential bias in reporting from cybersecurity firms with vested interests; possible underreporting of incidents due to reputational concerns by affected entities.
4. Implications and Strategic Risks
The continued exposure of BIG-IP APM instances could lead to significant disruptions in both private and public sectors, particularly if critical infrastructure is affected. The evolving cyber threat landscape necessitates proactive defense measures to mitigate potential impacts.
- Political / Geopolitical: Increased tensions between nation-states if attribution to state-sponsored actors is confirmed, potentially leading to diplomatic disputes or sanctions.
- Security / Counter-Terrorism: Heightened risk of cyber-attacks on critical infrastructure, potentially impacting national security and emergency response capabilities.
- Cyber / Information Space: Potential for increased cyber espionage activities and data breaches, undermining trust in digital systems and services.
- Economic / Social: Economic impacts from data breaches or service disruptions, including potential loss of consumer trust and financial penalties for non-compliance with cybersecurity regulations.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urgently apply patches to all vulnerable BIG-IP APM instances; conduct thorough network audits to identify signs of compromise; enhance monitoring for indicators of exploitation.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for threat intelligence sharing; invest in training for IT staff on vulnerability management and incident response.
- Scenario Outlook:
- Best: Rapid patching and defensive measures prevent widespread exploitation, maintaining network integrity.
- Worst: Failure to patch leads to significant breaches, resulting in data loss and operational disruptions.
- Most-Likely: Mixed response with some organizations securing systems while others remain vulnerable, leading to sporadic incidents.
6. Key Individuals and Entities
- F5 Networks (technology provider)
- Shadowserver (threat-monitoring non-profit)
- U.S. Cybersecurity and Infrastructure Security Agency (CISA)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
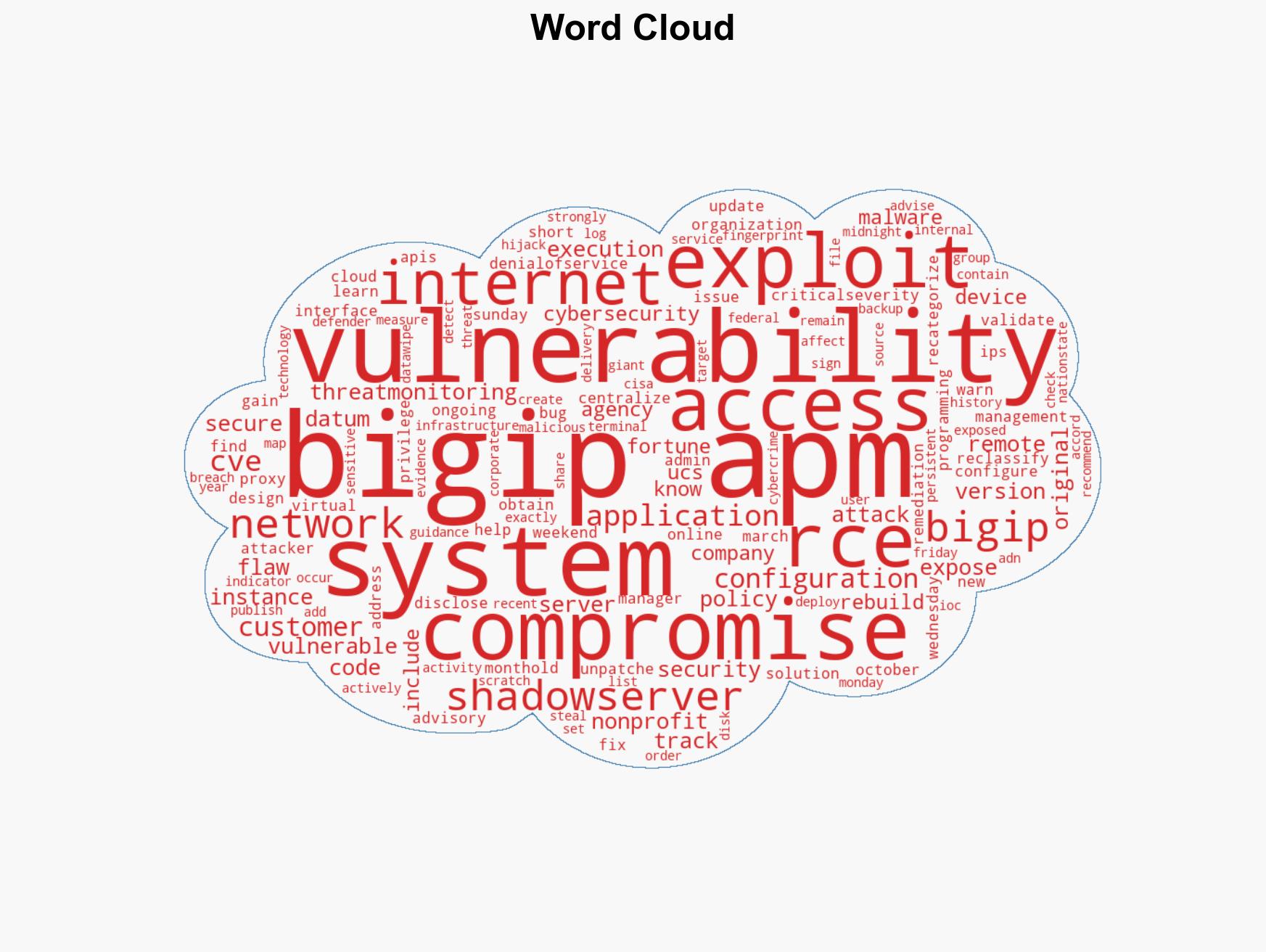
cybersecurity, remote code execution, vulnerability management, nation-state actors, cybercrime, critical infrastructure, threat intelligence
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us