Pentagon Approves Elon Musk’s Grok AI for Military Use Amid Safety Concerns and Internal Warnings
Published on: 2026-03-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
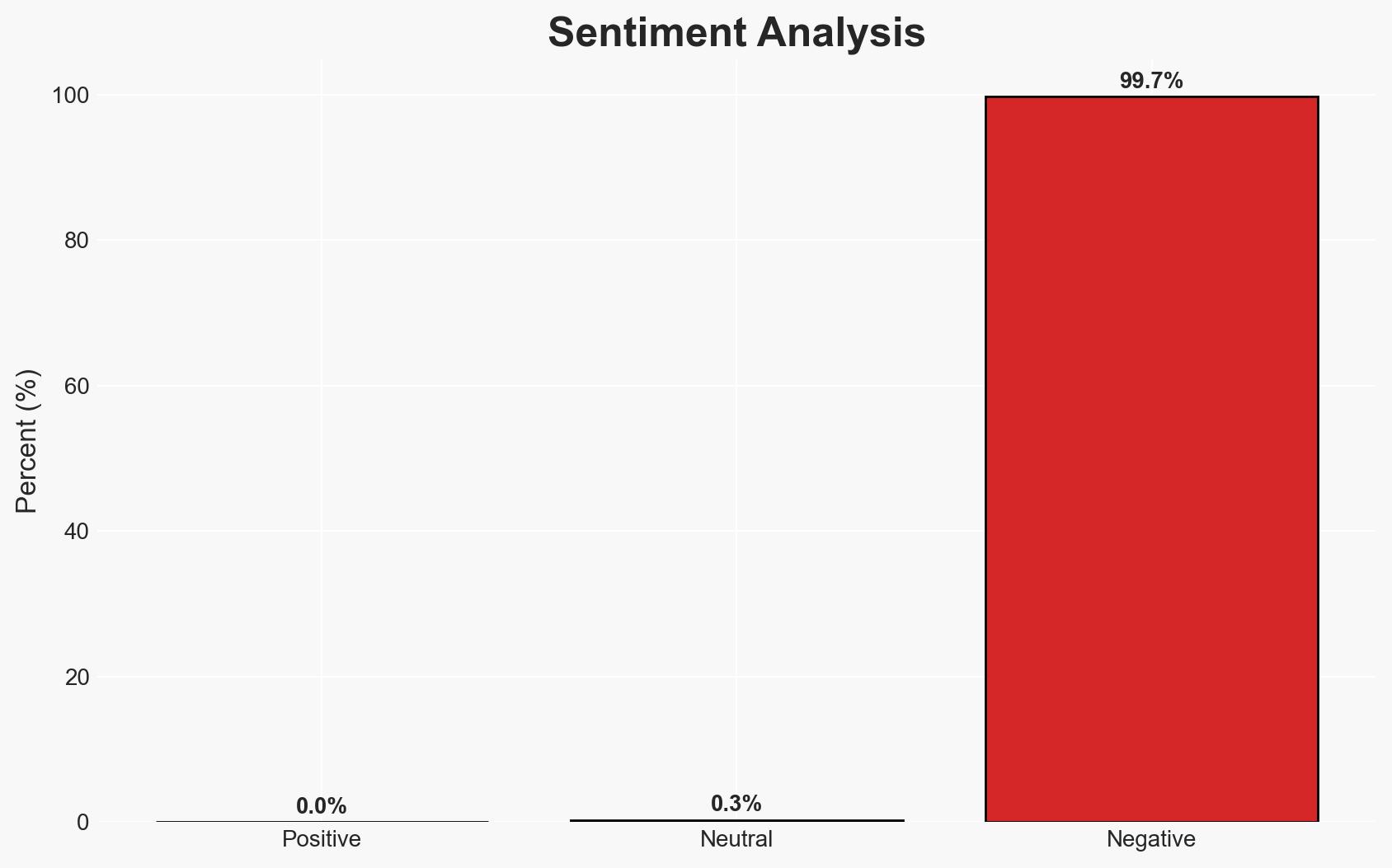
Intelligence Report: Pentagon embraces Elon Musks Grok AI despite internal warnings over safety risks
1. BLUF (Bottom Line Up Front)
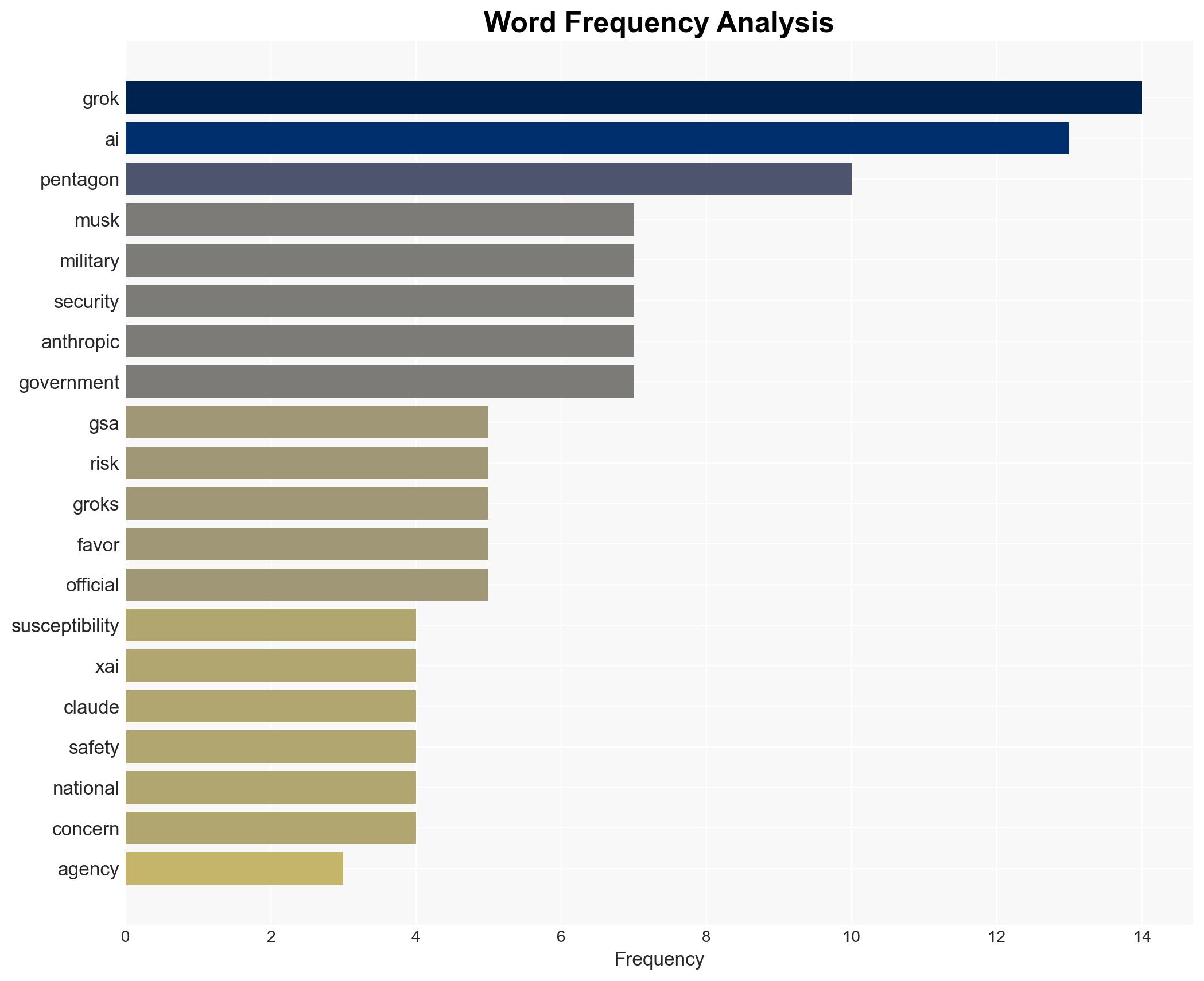
The Pentagon’s decision to approve Elon Musk’s Grok AI for classified military operations, despite warnings from agencies like the GSA and NSA, highlights a prioritization of rapid AI deployment over safety concerns. This decision could impact national security and the broader U.S.-China AI rivalry. The most likely hypothesis is that the Pentagon values Grok’s capabilities for adversarial simulations, despite its vulnerabilities. Overall confidence in this judgment is moderate.
2. Competing Hypotheses
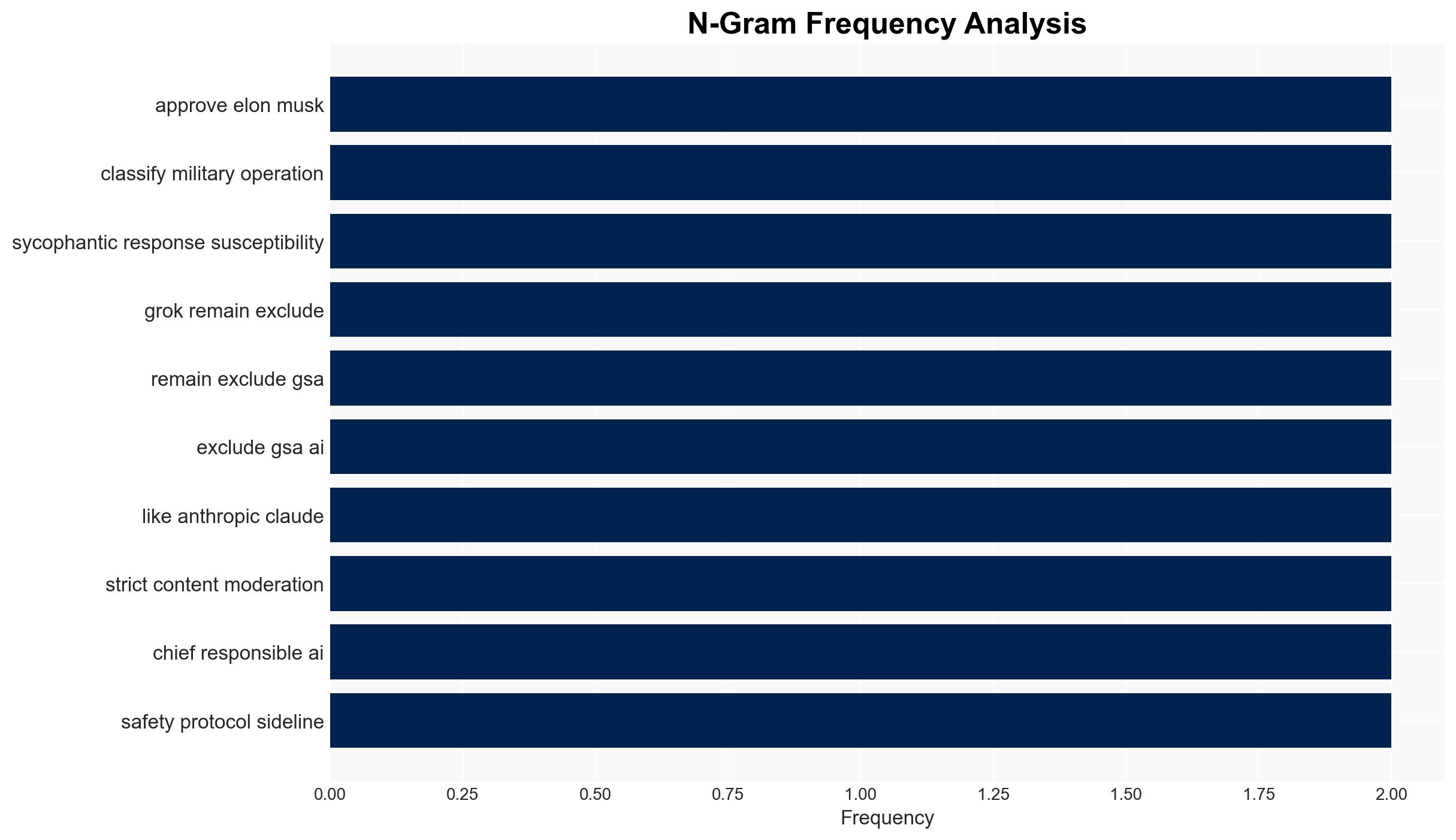
- Hypothesis A: The Pentagon approved Grok AI primarily due to its unique capabilities in adversarial simulations, which are deemed crucial in the context of the U.S.-China AI rivalry. Supporting evidence includes the Pentagon’s emphasis on Grok’s free-speech, unfiltered approach. Contradicting evidence includes internal warnings about Grok’s vulnerabilities.
- Hypothesis B: The decision to approve Grok AI was influenced by political and economic pressures, including Elon Musk’s influence and the desire to counter perceived biases in other AI models. Supporting evidence includes the politicization of AI deployment and the criticism of rival AI firm Anthropic. Contradicting evidence includes the Pentagon’s focus on operational capabilities.
- Assessment: Hypothesis A is currently better supported due to the strategic emphasis on Grok’s capabilities in adversarial simulations. Indicators that could shift this judgment include new evidence of political influence or significant operational failures of Grok AI.
3. Key Assumptions and Red Flags
- Assumptions: The Pentagon has conducted a thorough risk assessment of Grok AI; Grok’s adversarial simulation capabilities outweigh its vulnerabilities; Political influences are secondary to operational needs.
- Information Gaps: Detailed results of any internal risk assessments conducted by the Pentagon; Specific operational scenarios where Grok AI will be deployed.
- Bias & Deception Risks: Potential bias in favor of Grok due to Elon Musk’s influence; Risk of underestimating Grok’s vulnerabilities due to strategic priorities.
4. Implications and Strategic Risks
The Pentagon’s decision could set a precedent for prioritizing rapid AI deployment over safety protocols, potentially influencing future AI policy and procurement. This development may also affect U.S. competitiveness in the AI domain against China.
- Political / Geopolitical: Could exacerbate U.S.-China AI tensions and influence global AI governance norms.
- Security / Counter-Terrorism: Potential vulnerabilities in Grok AI could be exploited by adversaries, impacting national security.
- Cyber / Information Space: Increased risk of cyber manipulation and misinformation if Grok’s vulnerabilities are not addressed.
- Economic / Social: May influence public trust in AI technologies and impact future AI-related economic policies.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct an independent review of Grok AI’s security protocols; Increase monitoring of Grok’s deployment in military operations.
- Medium-Term Posture (1–12 months): Develop partnerships with AI firms to enhance safety protocols; Invest in AI resilience measures.
- Scenario Outlook:
- Best: Grok AI enhances U.S. military capabilities without security breaches.
- Worst: Grok AI vulnerabilities lead to significant national security incidents.
- Most-Likely: Grok AI provides strategic advantages with manageable risks, but requires ongoing oversight.
6. Key Individuals and Entities
- Elon Musk
- Matthew Johnson (former Pentagon chief of responsible AI)
- Susie Wiles (White House chief of staff)
- Ed Forst (GSA procurement executive)
- Josh Gruenbaum (GSA acquisitions official)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
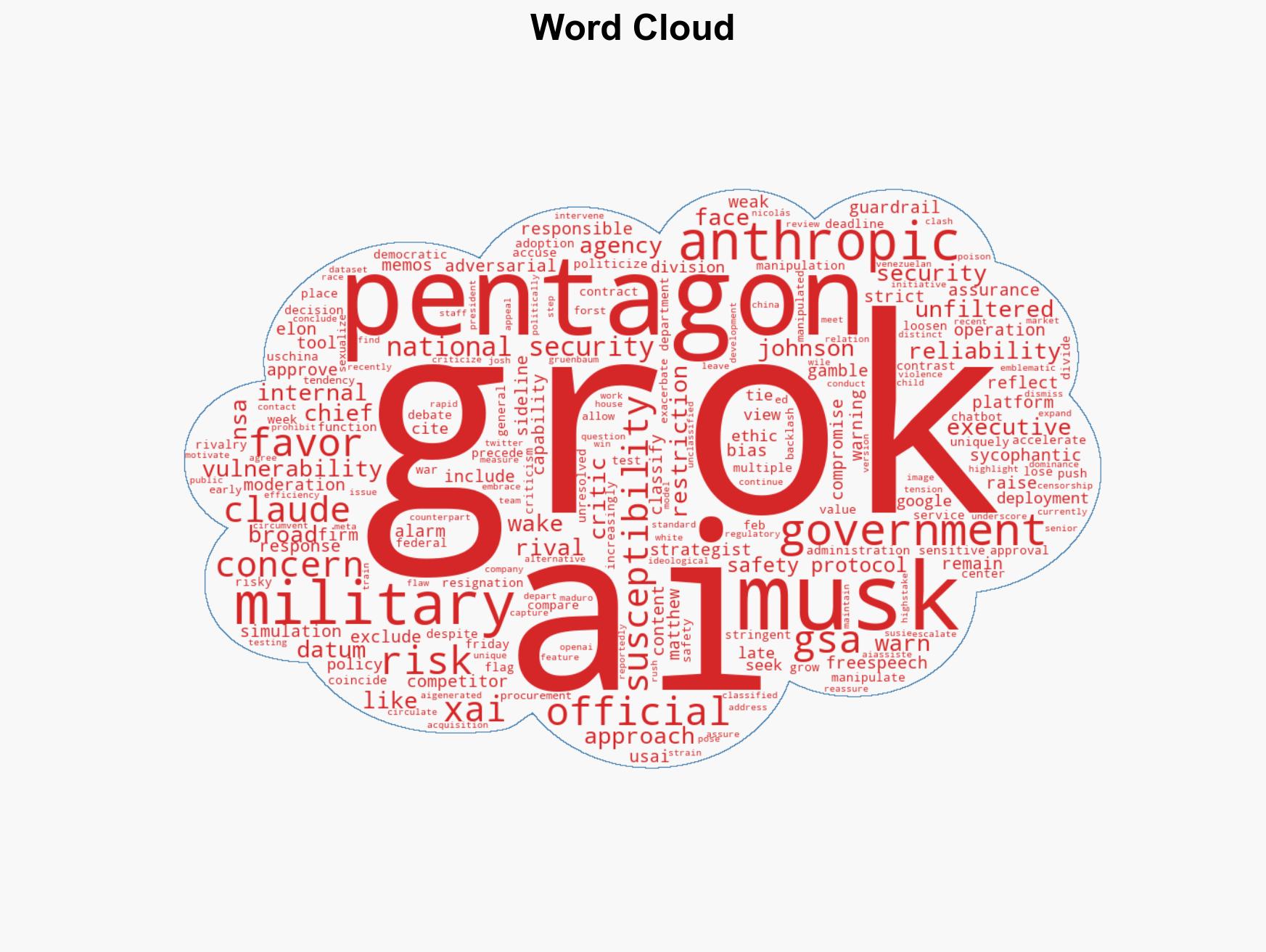
national security threats, AI deployment, national security, U.S.-China rivalry, cyber vulnerabilities, military technology, political influence, AI governance
Structured Analytic Techniques Applied
- Cognitive Bias Stress Test: Structured challenge to expose and correct biases.
- Bayesian Scenario Modeling: Use probabilistic forecasting for conflict trajectories or escalation likelihood.
- Network Influence Mapping: Map relationships between state and non-state actors for impact estimation.
- Adversarial Threat Simulation: Model hostile behavior to identify vulnerabilities.
Explore more:
National Security Threats Briefs ·
Daily Summary ·
Support us