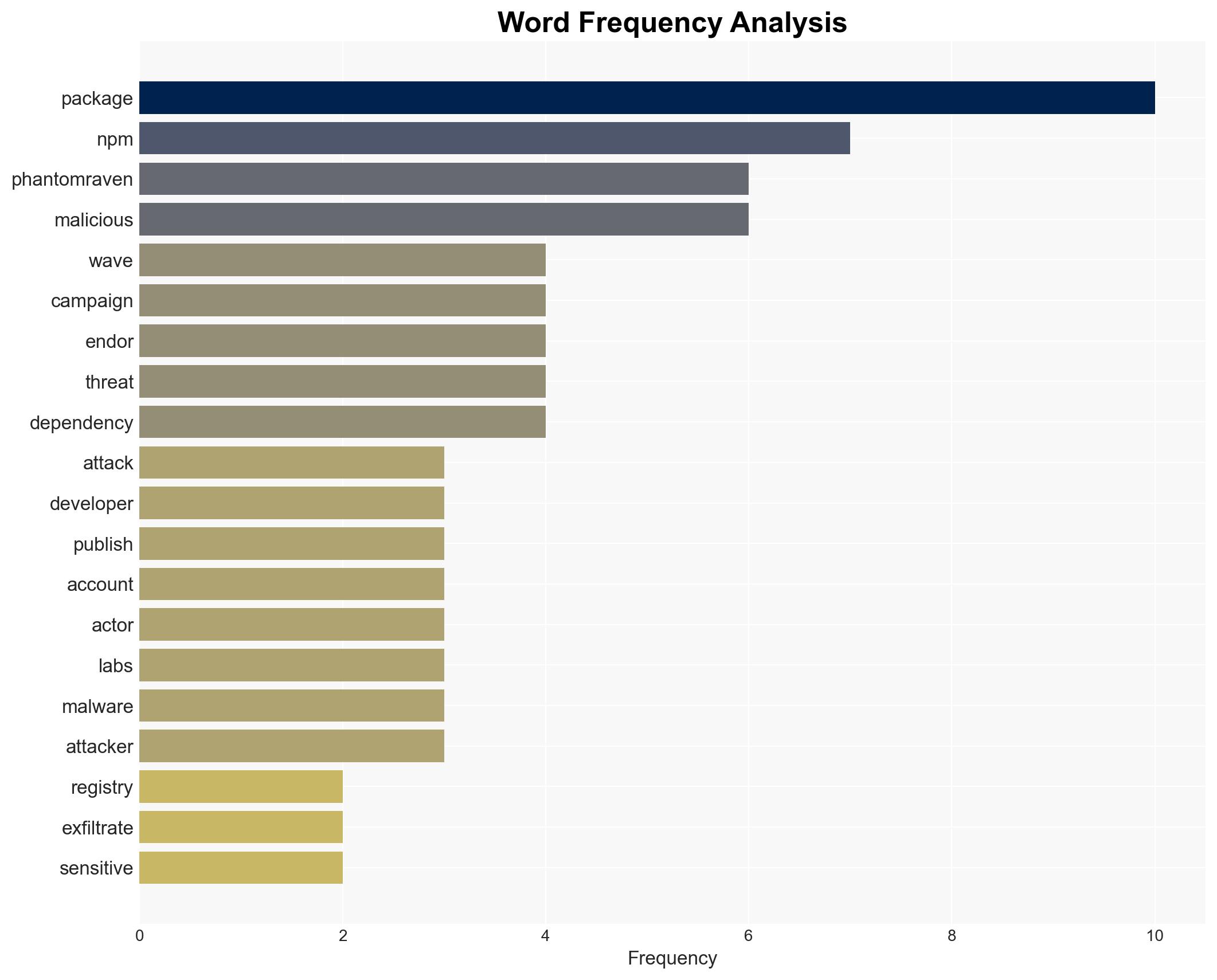
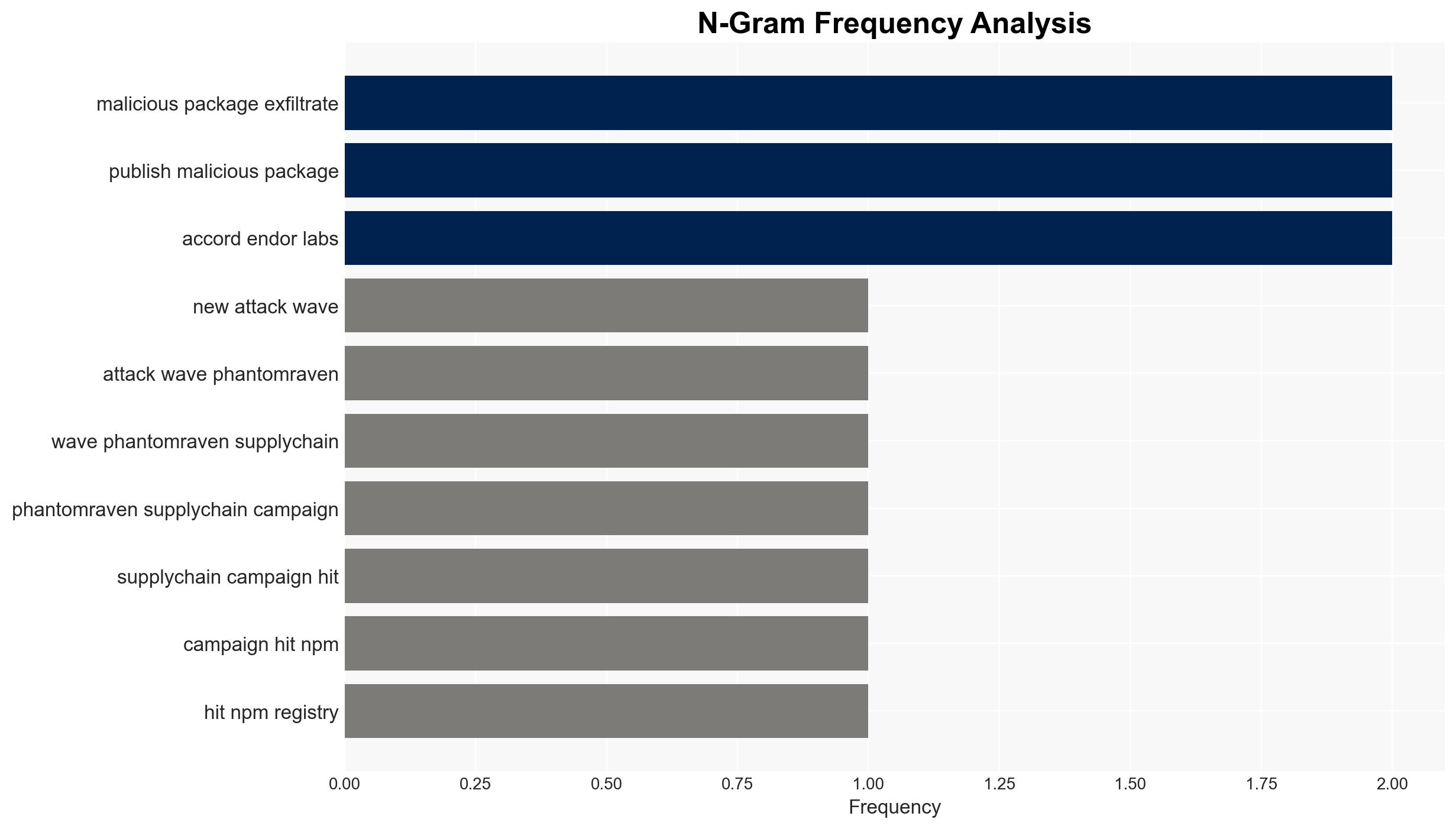
PhantomRaven campaign targets npm with 88 malicious packages to exfiltrate developer data
Published on: 2026-03-11
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: New PhantomRaven NPM attack wave steals dev data via 88 packages
1. BLUF (Bottom Line Up Front)
The PhantomRaven campaign represents a persistent supply-chain threat targeting JavaScript developers via the npm registry, using sophisticated evasion techniques like Remote Dynamic Dependencies. The campaign has successfully exfiltrated sensitive data from compromised systems. The most likely hypothesis is that the campaign is driven by a financially motivated group exploiting the npm ecosystem’s vulnerabilities. Overall confidence in this assessment is moderate due to information gaps regarding the threat actor’s identity and ultimate objectives.
2. Competing Hypotheses
- Hypothesis A: The PhantomRaven campaign is operated by a financially motivated cybercriminal group exploiting npm’s vulnerabilities to steal sensitive data for resale or ransom. This is supported by the campaign’s focus on exfiltrating credentials and tokens, which are valuable on black markets. However, the lack of direct financial demands or evidence of resale limits this hypothesis.
- Hypothesis B: The campaign is state-sponsored, aiming to gather intelligence on software development practices and infrastructure. The consistent infrastructure and sophisticated evasion techniques suggest a well-resourced operation. Contradicting this is the lack of geopolitical indicators or targeting patterns typical of state-sponsored activities.
- Assessment: Hypothesis A is currently better supported due to the campaign’s focus on credential theft and the use of disposable accounts, which are common in financially motivated cybercrime. Indicators that could shift this judgment include evidence of geopolitical targeting or state-level operational patterns.
3. Key Assumptions and Red Flags
- Assumptions: The npm ecosystem remains vulnerable to similar attacks; the threat actor is primarily motivated by financial gain; the use of Remote Dynamic Dependencies is a deliberate evasion tactic.
- Information Gaps: The identity and ultimate objectives of the threat actor; the full extent of the data exfiltrated; potential connections to other known cybercriminal groups or state actors.
- Bias & Deception Risks: Potential cognitive bias towards attributing the attack to cybercriminals due to the focus on credential theft; source bias from cybersecurity firms with vested interests in highlighting threats.
4. Implications and Strategic Risks
The PhantomRaven campaign could lead to increased scrutiny and regulation of software supply chains, impacting developer practices and software distribution. If state-sponsored, it could escalate tensions in cyber diplomacy.
- Political / Geopolitical: Potential for increased international cooperation on cybersecurity standards and supply chain security.
- Security / Counter-Terrorism: Heightened awareness and defensive measures in software development environments; potential for copycat attacks.
- Cyber / Information Space: Increased focus on securing software repositories and enhancing detection capabilities for supply chain attacks.
- Economic / Social: Potential economic impact on companies reliant on npm packages; increased costs for implementing enhanced security measures.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of npm repositories for suspicious activity; conduct security audits of dependencies; inform developers of the threat and mitigation strategies.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for threat intelligence sharing; invest in research for automated detection of supply chain attacks.
- Scenario Outlook: Best: Rapid identification and neutralization of the threat actor. Worst: Proliferation of similar attacks leading to widespread data breaches. Most-Likely: Continued low-level attacks with gradual improvements in detection and mitigation.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, supply-chain attack, npm registry, cybercrime, data exfiltration, Remote Dynamic Dependencies, software security, threat intelligence
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us