Phishing Scheme Exploits Fake Google Security Page to Distribute Malicious PWA for Credential Theft
Published on: 2026-03-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Fake Google Security site uses PWA app to steal credentials MFA codes
1. BLUF (Bottom Line Up Front)
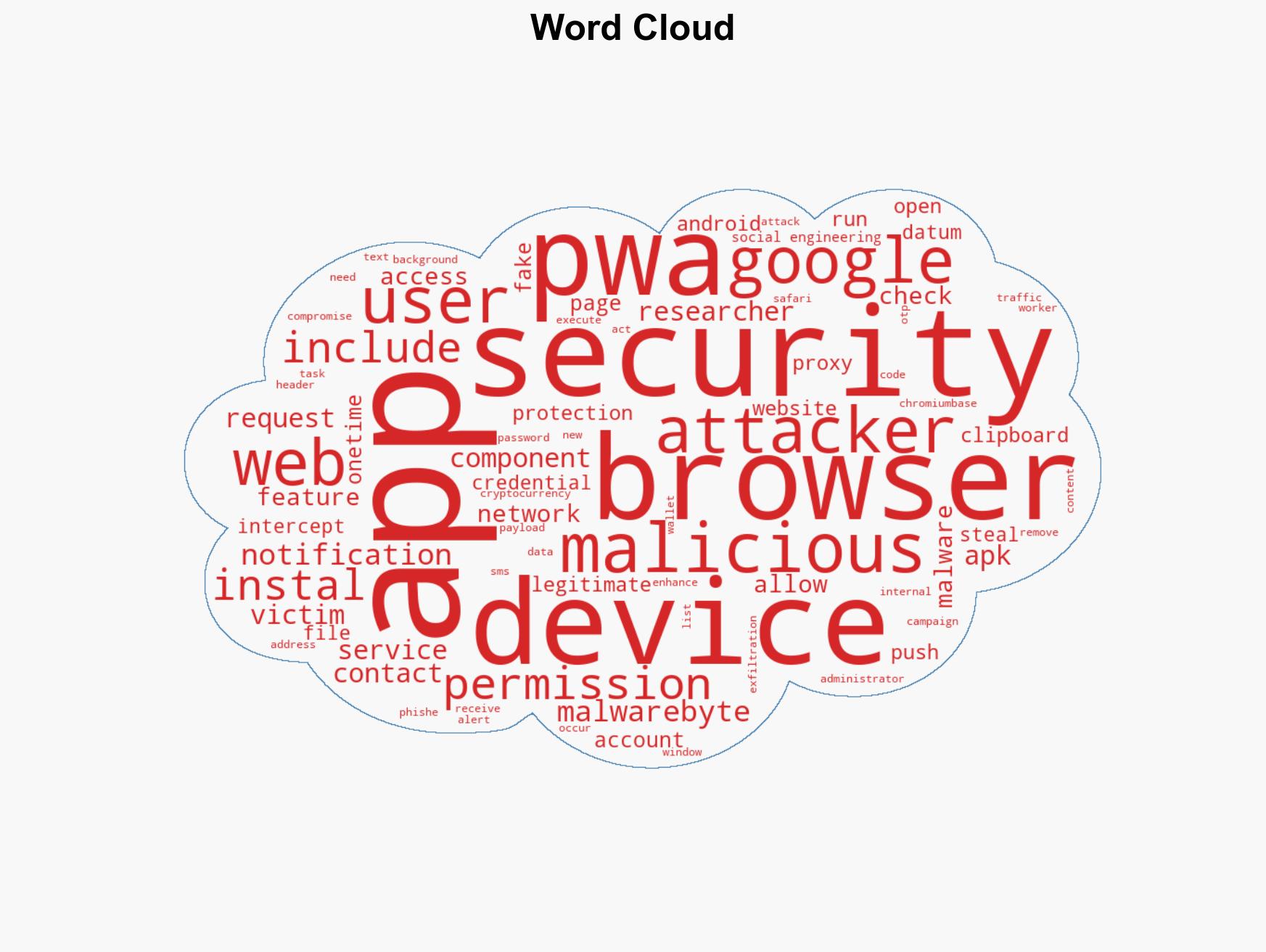
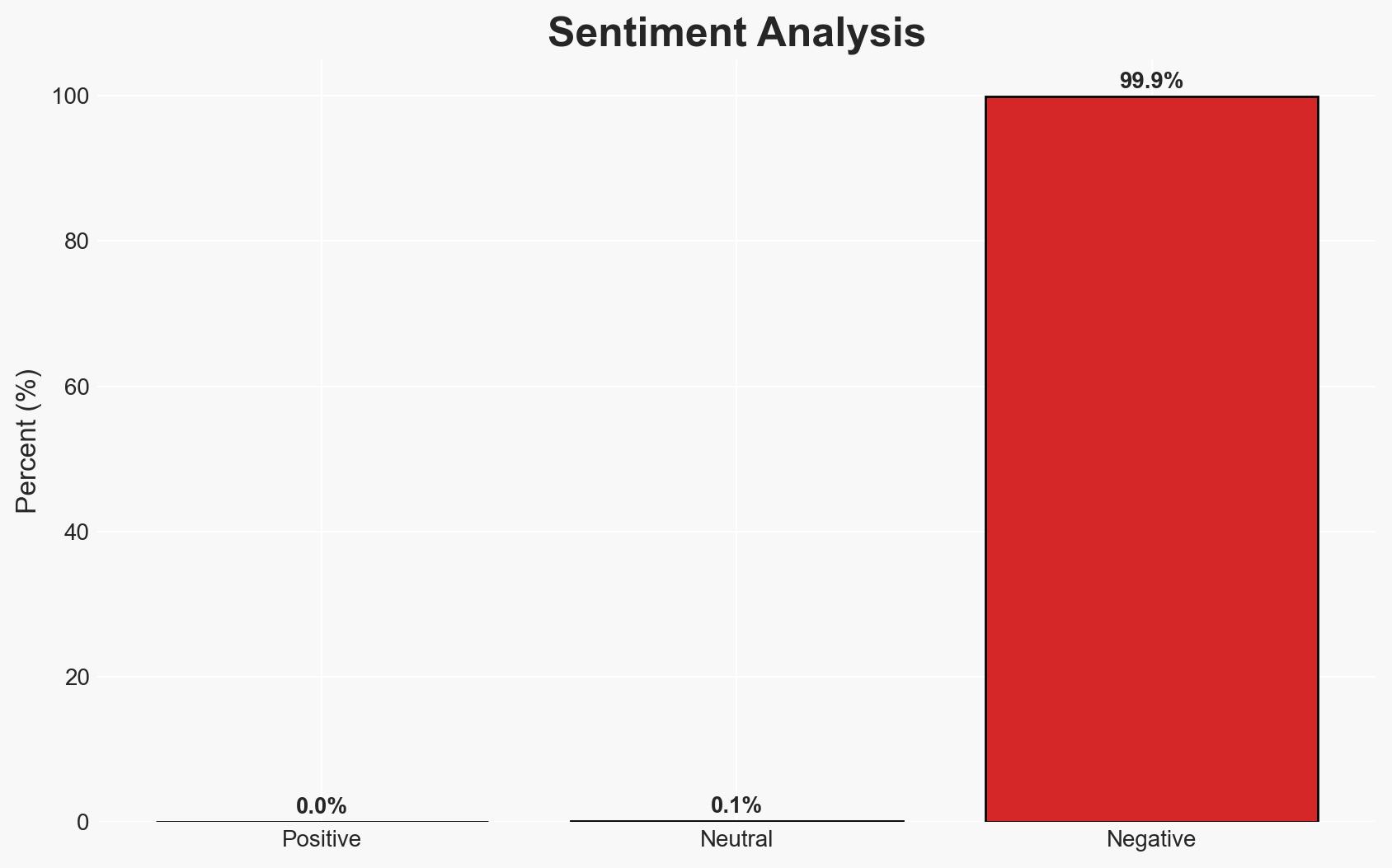
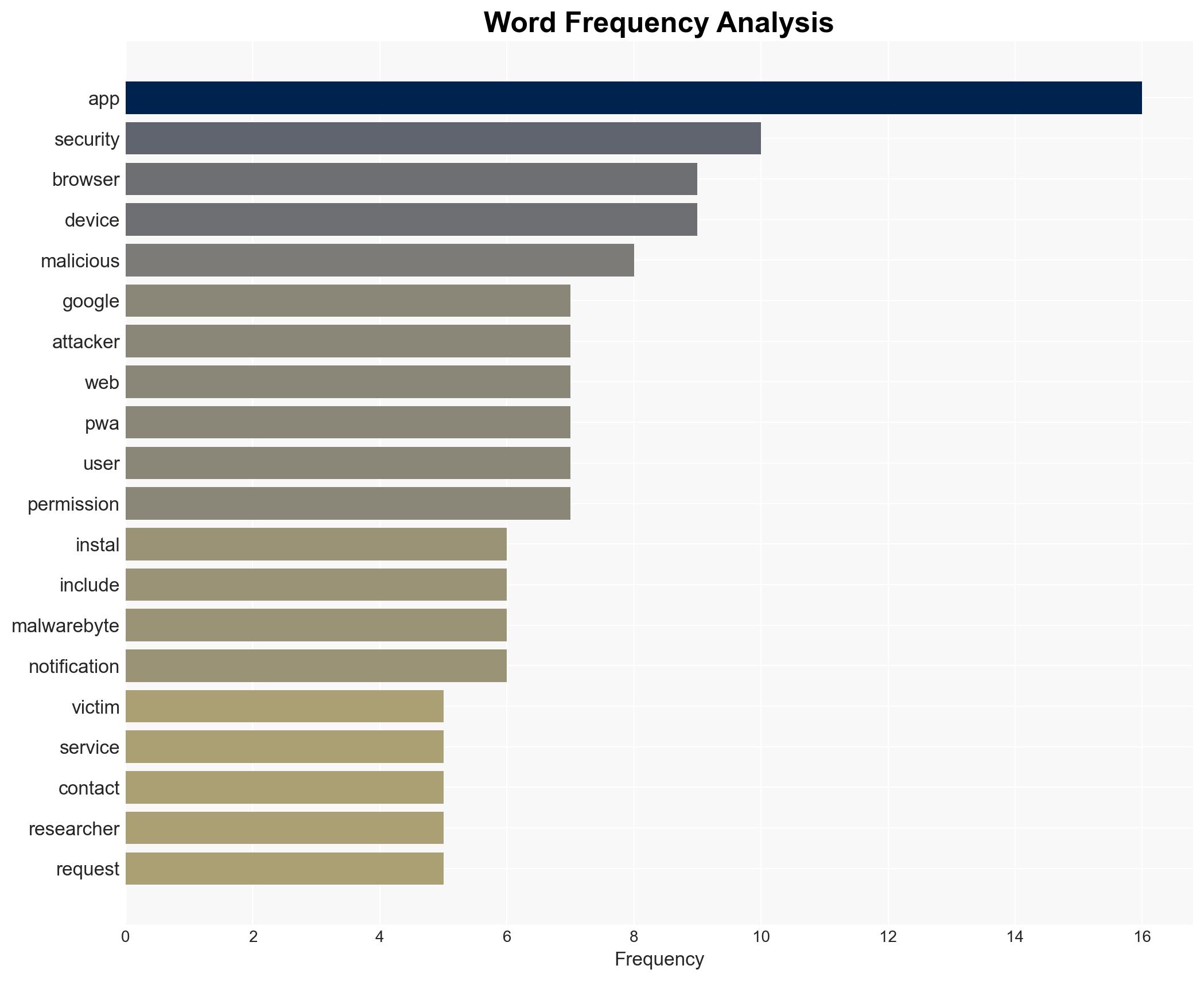
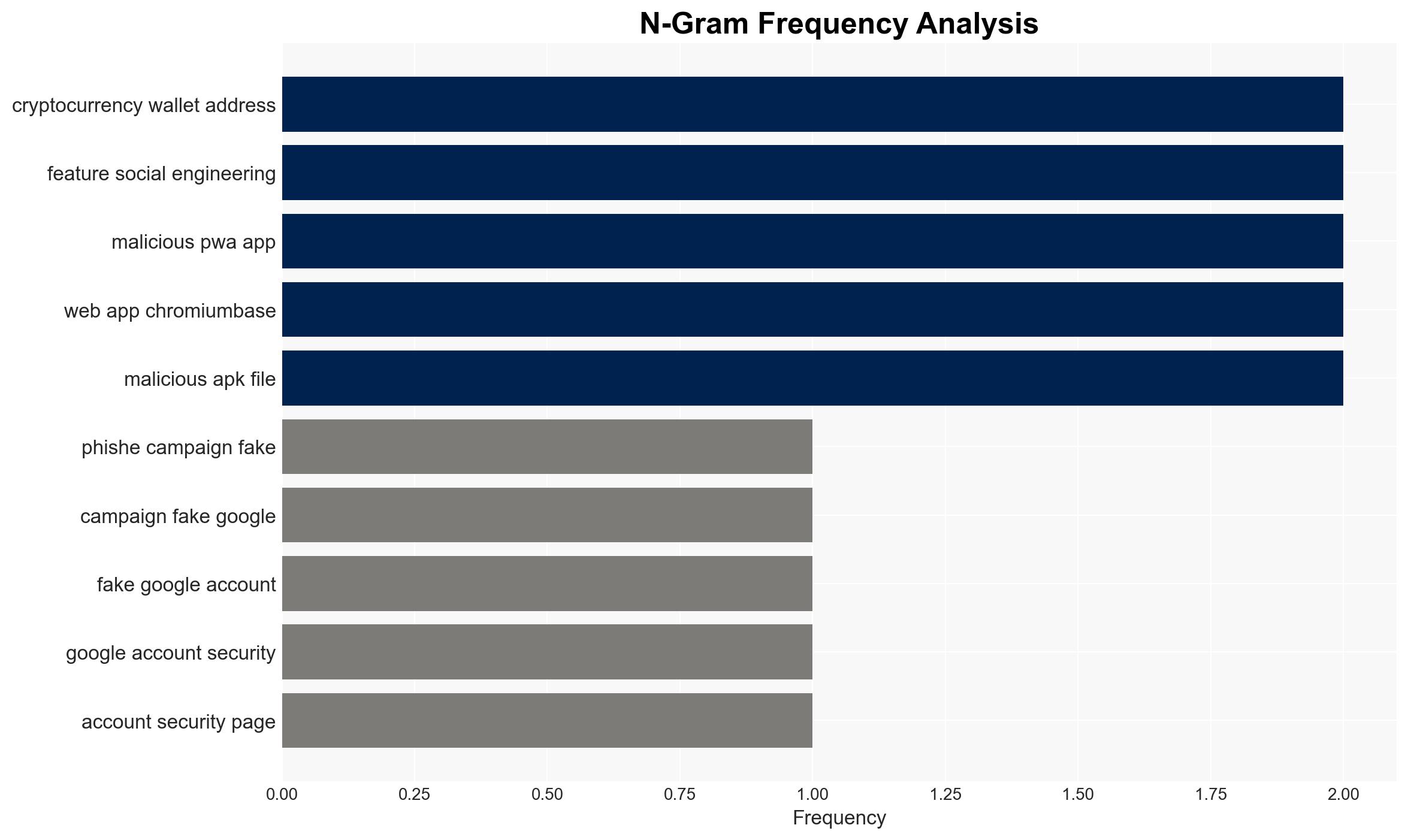
A phishing campaign is exploiting a fake Google security site to deploy a Progressive Web App (PWA) that steals credentials and one-time passcodes. The campaign targets users by masquerading as a legitimate Google service, affecting individuals and potentially organizations with moderate confidence. The most likely hypothesis is that this is a financially motivated cybercrime operation.
2. Competing Hypotheses
- Hypothesis A: The campaign is a financially motivated cybercrime operation aimed at stealing cryptocurrency and personal data. This is supported by the focus on harvesting cryptocurrency wallet addresses and one-time passwords. However, the lack of direct attribution to a known group introduces uncertainty.
- Hypothesis B: The campaign could be a state-sponsored operation aimed at broader espionage activities. This is contradicted by the primary focus on financial data rather than strategic information, and there is no evidence of state actor involvement.
- Assessment: Hypothesis A is currently better supported due to the specific targeting of financial assets and personal data. Indicators such as a shift in target demographics or the discovery of state actor involvement could alter this assessment.
3. Key Assumptions and Red Flags
- Assumptions: The attackers are primarily financially motivated; the PWA’s functionality is accurately described; the campaign is not currently linked to a state actor.
- Information Gaps: Attribution to specific individuals or groups; the full scope of the campaign’s reach and impact; potential state actor involvement.
- Bias & Deception Risks: Confirmation bias towards financial motives; potential manipulation of data by the attackers to mislead investigators.
4. Implications and Strategic Risks
This development could lead to increased sophistication in phishing campaigns and the adoption of PWA techniques by other cybercriminals.
- Political / Geopolitical: Minimal direct impact unless linked to state actors or geopolitical tensions.
- Security / Counter-Terrorism: Increased threat to personal and organizational data security; potential for similar tactics in other malicious campaigns.
- Cyber / Information Space: Highlights vulnerabilities in PWA technology and the need for enhanced user awareness and security measures.
- Economic / Social: Potential financial losses for individuals and organizations; erosion of trust in digital security services.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase monitoring of phishing campaigns using PWA technology; enhance public awareness campaigns on phishing risks.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies to improve PWA security; invest in cybersecurity training and resilience measures.
- Scenario Outlook: Best: Campaign is quickly mitigated with minimal impact. Worst: Broader adoption of PWA-based attacks leads to significant financial and data losses. Most-Likely: Continued use of PWA techniques in phishing with moderate impact.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, phishing, financial crime, PWA, digital security, cybercrime, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us