Potential Global Surge in Shiite Extremism Following Iran’s Regime Collapse Amid U.S.-Israeli Conflict
Published on: 2026-03-13
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: How the Iran War Could Usher in a New Era of Global Shiite Extremism
1. BLUF (Bottom Line Up Front)
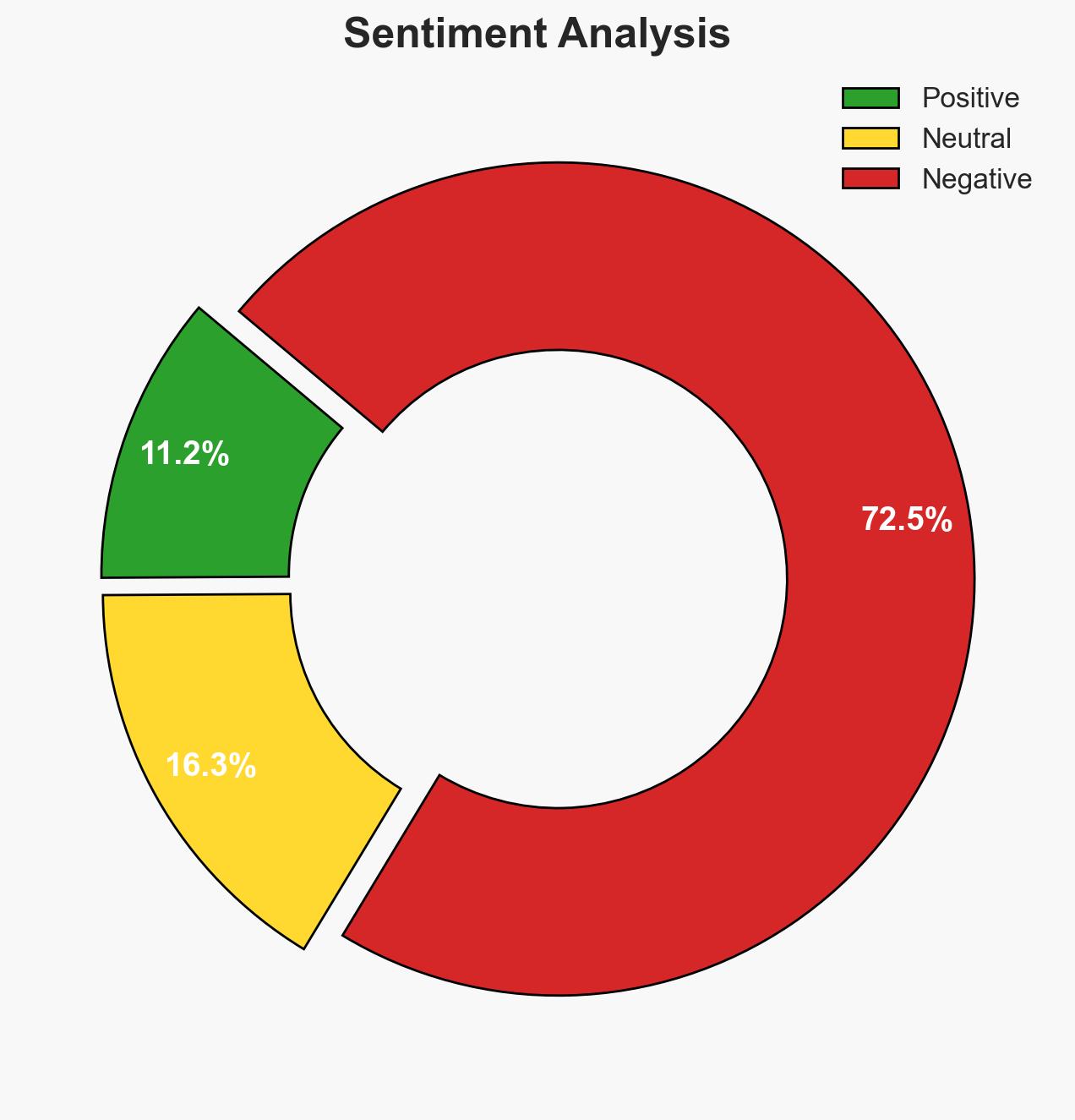
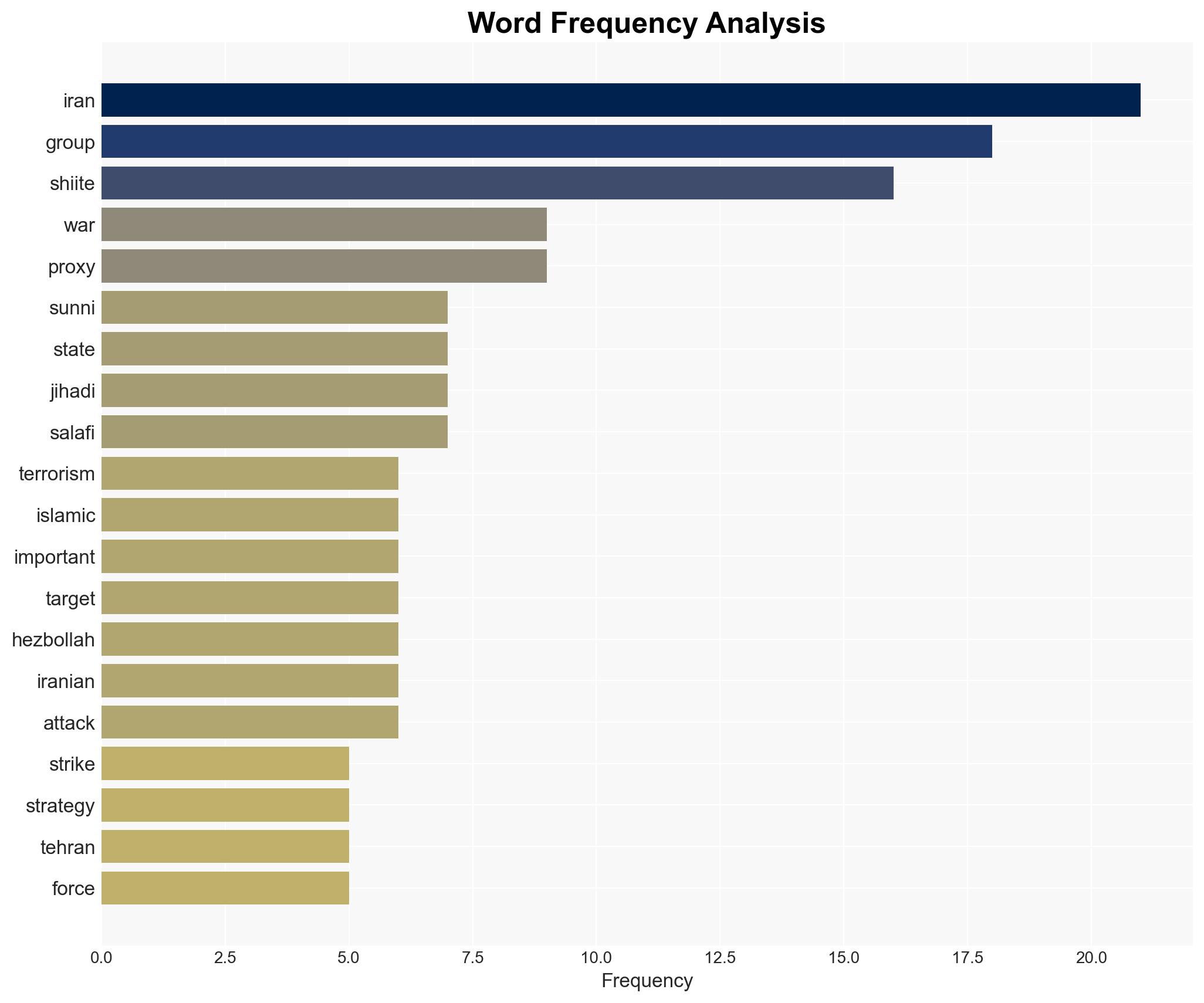
The targeted assassination of Iran’s supreme leader has the potential to catalyze global Shiite extremism, with Iranian proxies becoming more decentralized and unpredictable. This development could lead to increased terrorist activities against U.S. and Jewish targets worldwide. Overall, there is moderate confidence in this assessment due to existing uncertainties about the cohesion and future actions of Iranian proxies.
2. Competing Hypotheses
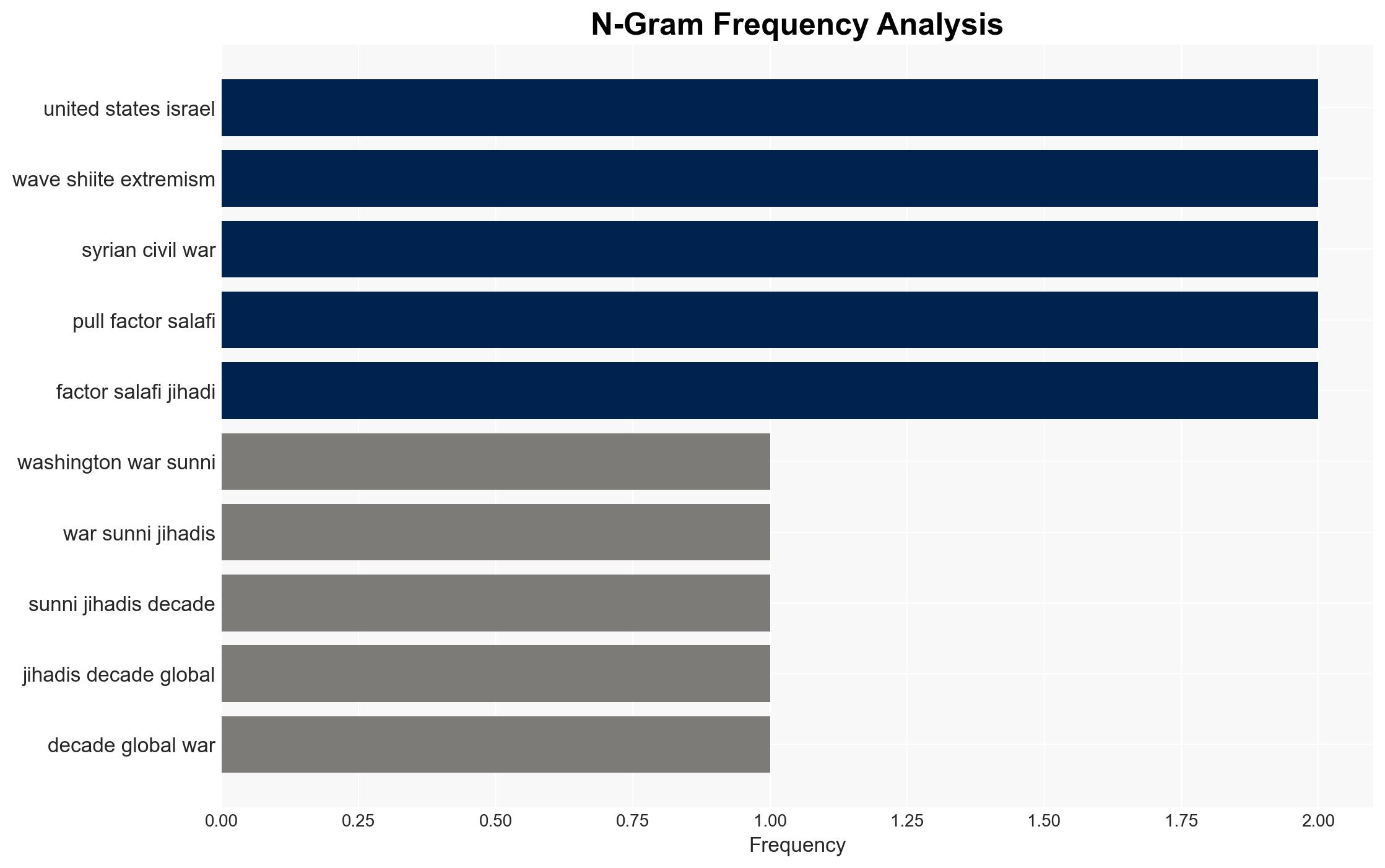
- Hypothesis A: The collapse of Iran’s central command will lead to a surge in Shiite extremism globally, as decentralized proxies act independently and aggressively. Supporting evidence includes the historical precedent of proxy groups acting autonomously when central control is weakened. Contradicting evidence includes the possibility that some proxies may prioritize local agendas over global jihad.
- Hypothesis B: Despite the loss of central leadership, Iranian proxies will remain largely contained and focused on regional conflicts, minimizing global extremist threats. This is supported by the current focus of groups like Hezbollah on regional power dynamics. However, the risk of global attacks remains if proxies seek to retaliate against perceived aggressors.
- Assessment: Hypothesis A is currently better supported due to the historical tendency of decentralized groups to engage in terrorism and the symbolic motivation provided by the assassination. Key indicators that could shift this judgment include changes in proxy group leadership dynamics and external diplomatic interventions.
3. Key Assumptions and Red Flags
- Assumptions: The IRGC’s command structure is significantly weakened; Iranian proxies will act independently; Shiite extremism will prioritize global over local targets.
- Information Gaps: The current state of communication and coordination among Iranian proxies; the specific intentions and capabilities of these groups post-assassination.
- Bias & Deception Risks: Potential overestimation of the proxies’ global reach; reliance on sources with inherent biases against Iran or Shiite groups.
4. Implications and Strategic Risks
This development could lead to a fragmented yet aggressive Shiite extremist landscape, challenging global security frameworks and potentially altering geopolitical alliances.
- Political / Geopolitical: Escalation of tensions in the Middle East, potential realignment of regional alliances, increased diplomatic strains.
- Security / Counter-Terrorism: Heightened threat levels for U.S. and allied interests, necessitating increased vigilance and counter-terrorism measures.
- Cyber / Information Space: Potential for increased cyber operations targeting critical infrastructure and information warfare campaigns.
- Economic / Social: Possible disruptions in global oil markets, increased refugee flows, and social unrest in affected regions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance intelligence sharing among allies; increase security measures at potential target sites; monitor proxy communications for shifts in strategy.
- Medium-Term Posture (1–12 months): Strengthen regional partnerships; develop resilience against asymmetric threats; invest in counter-radicalization programs.
- Scenario Outlook:
- Best: Diplomatic resolution reduces tensions, proxies remain regionally focused.
- Worst: Global surge in Shiite extremist attacks, destabilizing multiple regions.
- Most-Likely: Increased regional violence with sporadic global attacks, driven by decentralized proxy actions.
6. Key Individuals and Entities
- Ayatollah Ali Khamenei (deceased), Hezbollah, IRGC, Iraqi Shiite militias, Houthis
7. Thematic Tags
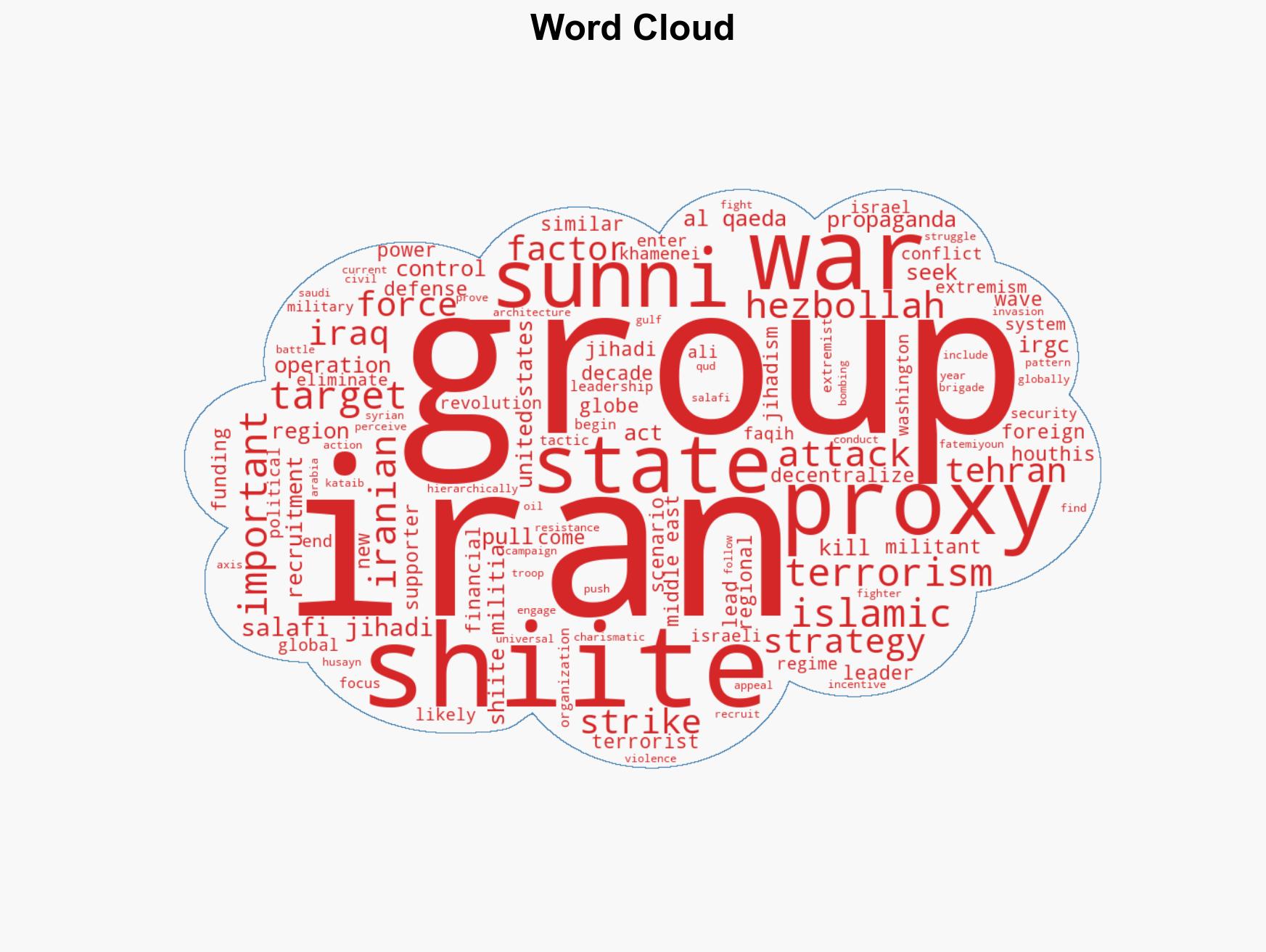
Counter-Terrorism, Shiite extremism, Middle East conflict, proxy warfare, geopolitical instability, intelligence sharing, regional security
Structured Analytic Techniques Applied
- ACH 2.0: Reconstruct likely threat actor intentions via hypothesis testing and structured refutation.
- Indicators Development: Track radicalization signals and propaganda patterns to anticipate operational planning.
- Narrative Pattern Analysis: Analyze spread/adaptation of ideological narratives for recruitment/incitement signals.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
Explore more:
Counter-Terrorism Briefs ·
Daily Summary ·
Support us