Preparing for the Rise of AI-Driven Cyber Threats: Essential Strategies for Securing Infrastructure
Published on: 2026-02-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Securing AI infrastructure is critical here’s how to do it
1. BLUF (Bottom Line Up Front)
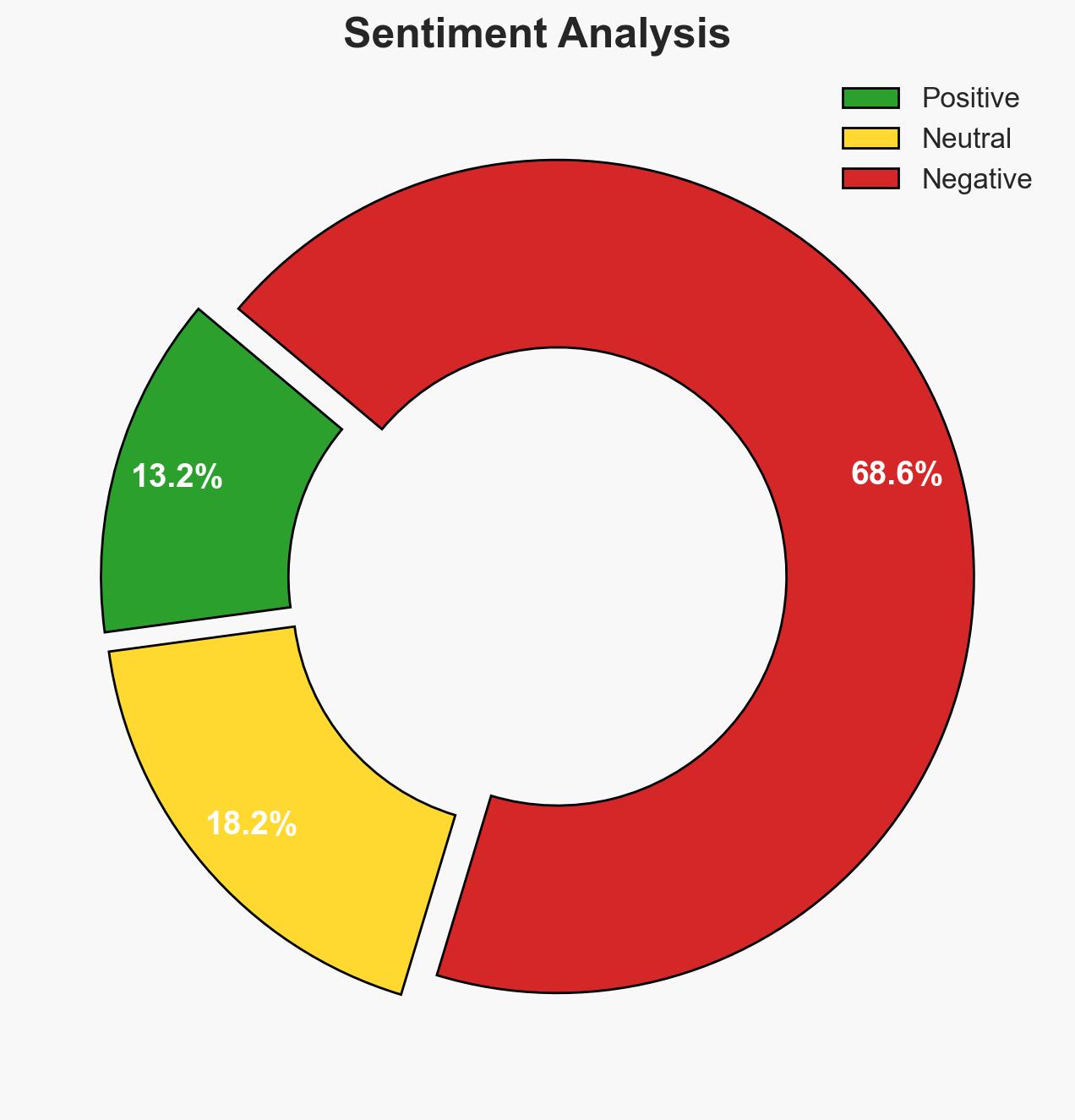
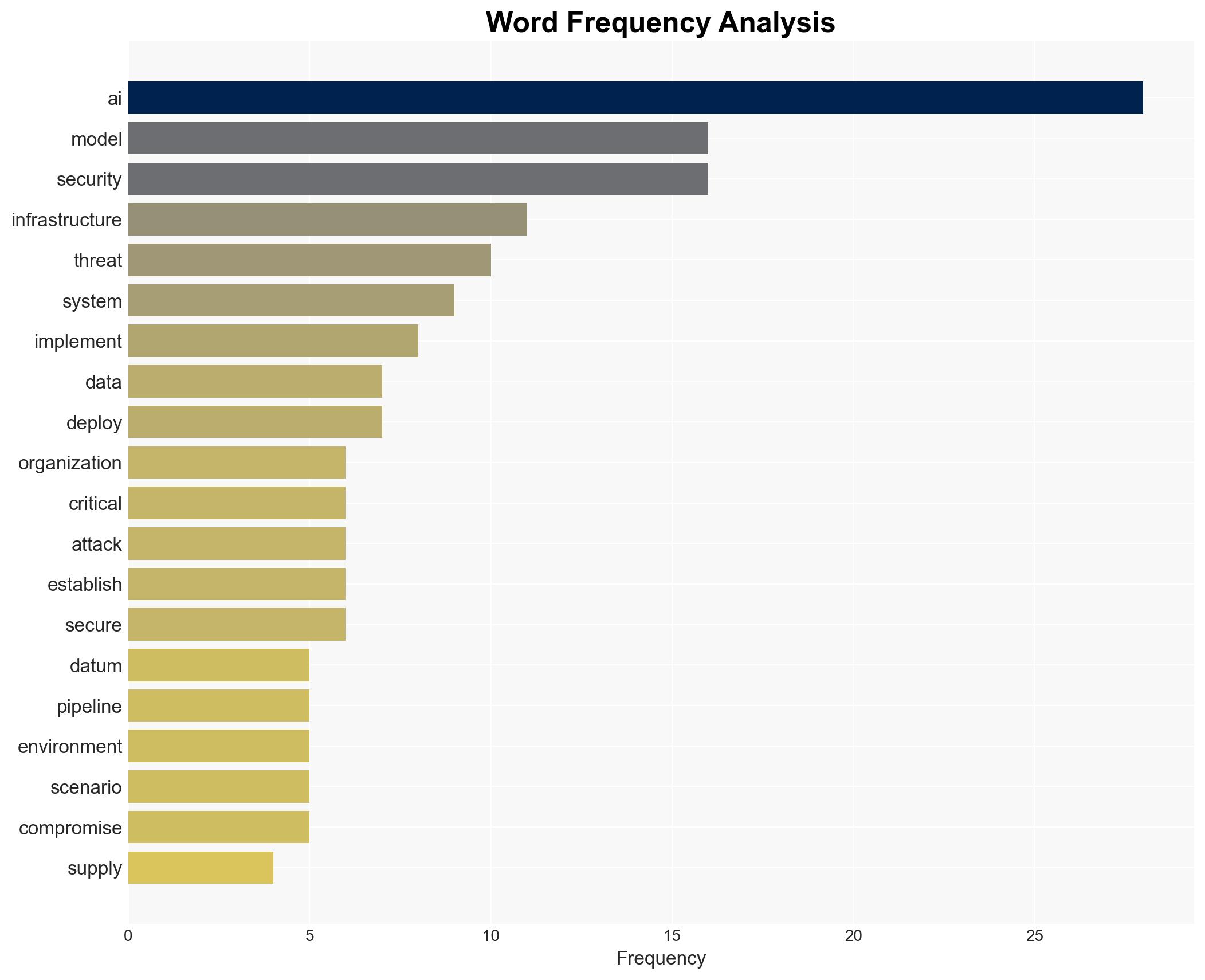
AI infrastructure is increasingly vulnerable to sophisticated cyber threats, with 2026 projected as a pivotal year for AI-powered cyberattacks. Organizations must rapidly enhance their defenses to protect against evolving threats that target AI systems. The most likely hypothesis is that AI infrastructure will be targeted through data poisoning and model supply chain compromises, posing significant risks to critical sectors. Overall confidence in this assessment is moderate, given the evolving nature of the threat landscape.
2. Competing Hypotheses
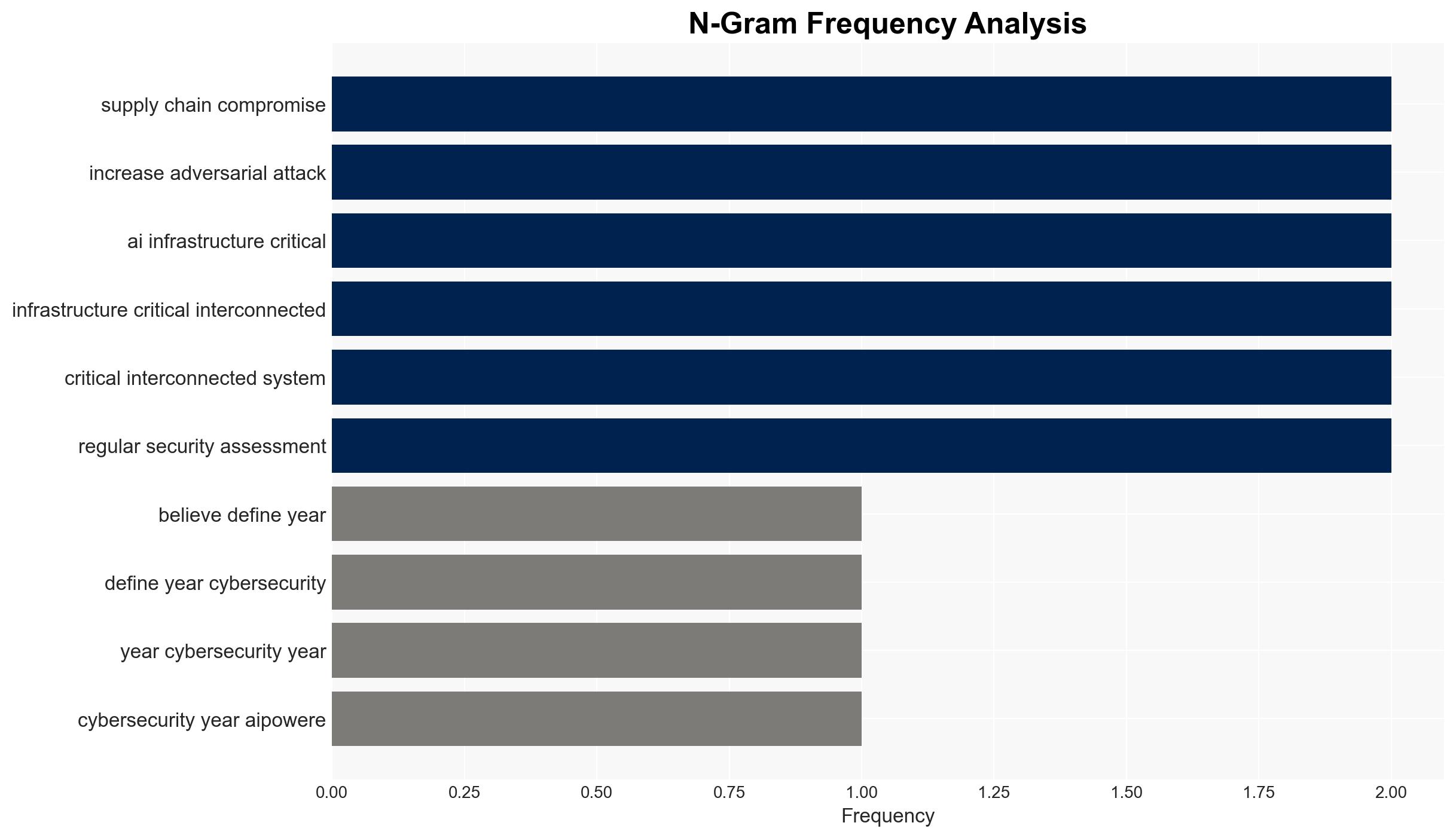
- Hypothesis A: AI infrastructure will face significant threats from data poisoning and supply chain compromises, leading to widespread vulnerabilities. This is supported by the increasing integration of AI systems in critical operations and the emerging threat scenarios outlined. However, the lack of large-scale breaches to date introduces uncertainty.
- Hypothesis B: AI infrastructure will remain relatively secure due to ongoing advancements in cybersecurity measures and organizational preparedness. While some evidence supports this, the rapid evolution of AI threats and the complexity of AI systems challenge this hypothesis.
- Assessment: Hypothesis A is currently better supported due to the documented threat scenarios and the increasing sophistication of AI-powered attacks. Indicators such as successful large-scale breaches or significant advancements in defensive measures could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: AI systems will continue to be integrated into critical infrastructure; threat actors will develop more sophisticated AI-powered attacks; organizations will not significantly enhance their cybersecurity posture in the short term.
- Information Gaps: Specific details on the current state of AI infrastructure security measures and the capabilities of threat actors targeting AI systems.
- Bias & Deception Risks: Potential bias in underestimating the capabilities of defensive measures; risk of deception from threat actors exaggerating their capabilities to induce fear or confusion.
4. Implications and Strategic Risks
The evolution of AI threats could lead to significant disruptions in critical sectors, impacting national security and economic stability. The interplay between AI advancements and cybersecurity measures will shape the future threat landscape.
- Political / Geopolitical: Increased tensions between nations over AI capabilities and cybersecurity breaches could escalate into broader geopolitical conflicts.
- Security / Counter-Terrorism: Enhanced AI threats could be exploited by terrorist groups to target critical infrastructure, necessitating improved counter-terrorism strategies.
- Cyber / Information Space: The digital landscape may see increased misinformation campaigns and cyber espionage activities leveraging compromised AI systems.
- Economic / Social: Potential economic losses from intellectual property theft and disruptions in critical services could affect social cohesion and trust in technology.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct comprehensive audits of AI systems, enhance monitoring for data integrity, and establish rapid response protocols for AI-related incidents.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms, invest in AI-specific security training, and implement robust supply chain security measures.
- Scenario Outlook: Best: Enhanced defenses mitigate AI threats; Worst: Large-scale breaches disrupt critical infrastructure; Most-Likely: Incremental improvements in security with occasional breaches highlighting vulnerabilities.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
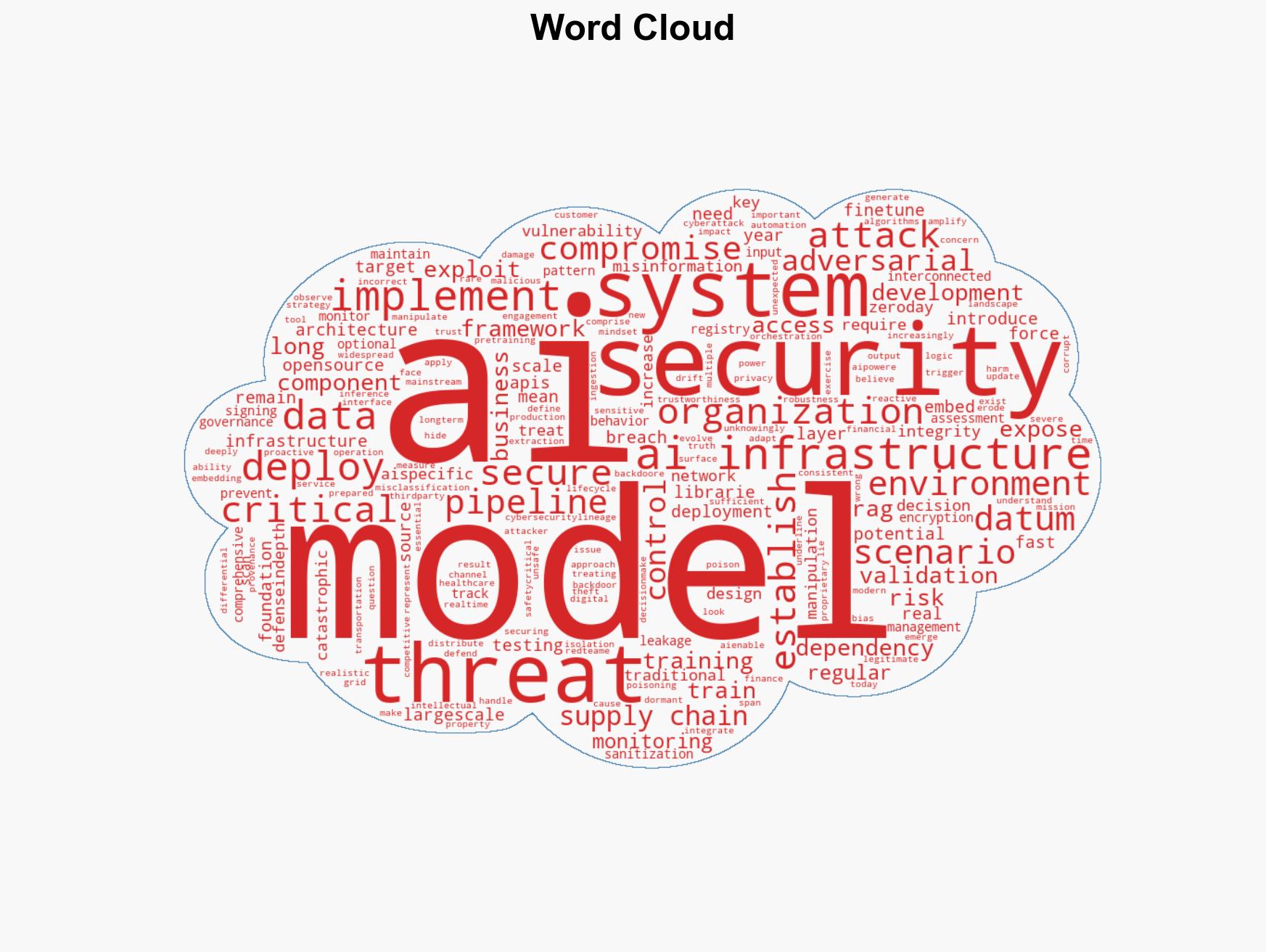
cybersecurity, AI security, cyber threats, data poisoning, critical infrastructure, misinformation, supply chain security, intellectual property theft
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model hostile behavior to identify vulnerabilities.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
- Cognitive Bias Stress Test: Structured challenge to expose and correct biases.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us