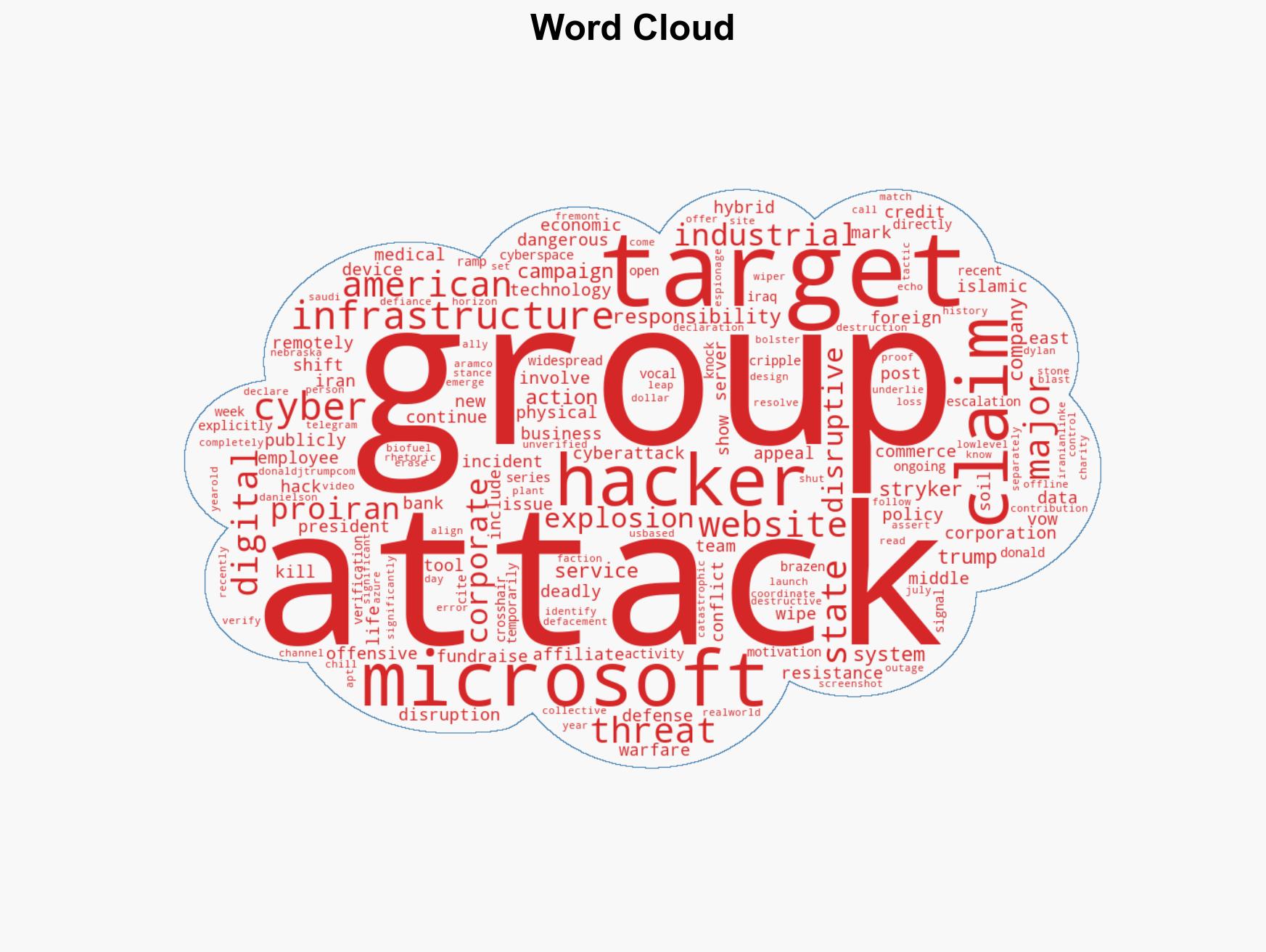
Pro-Iran Cyber Groups Intensify Attacks on U.S. Firms, Targeting Microsoft and Other Key Infrastructure
Published on: 2026-03-17
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Pro-Iran hackers claim Microsoft outage vow escalating attacks on US firms
1. BLUF (Bottom Line Up Front)
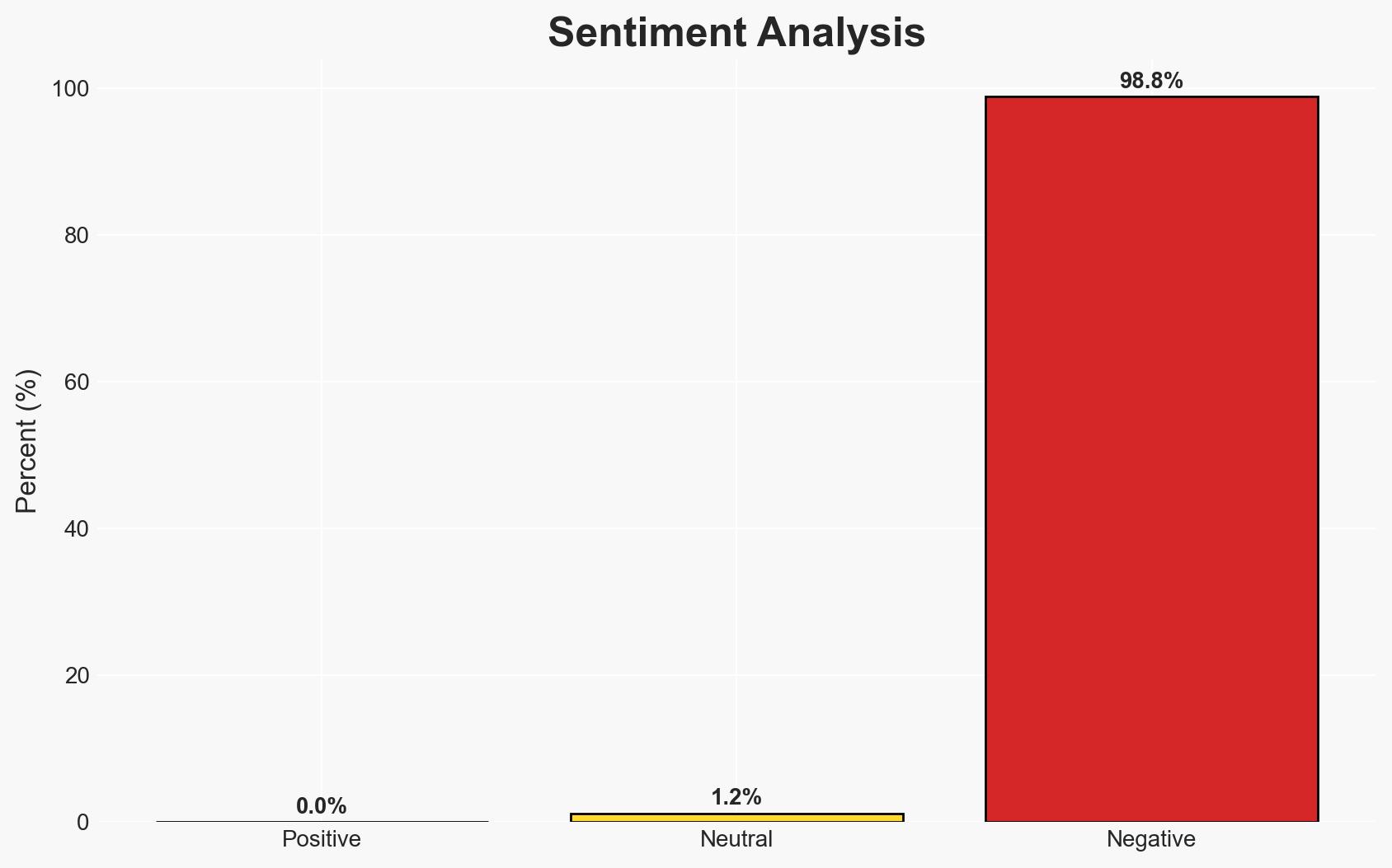
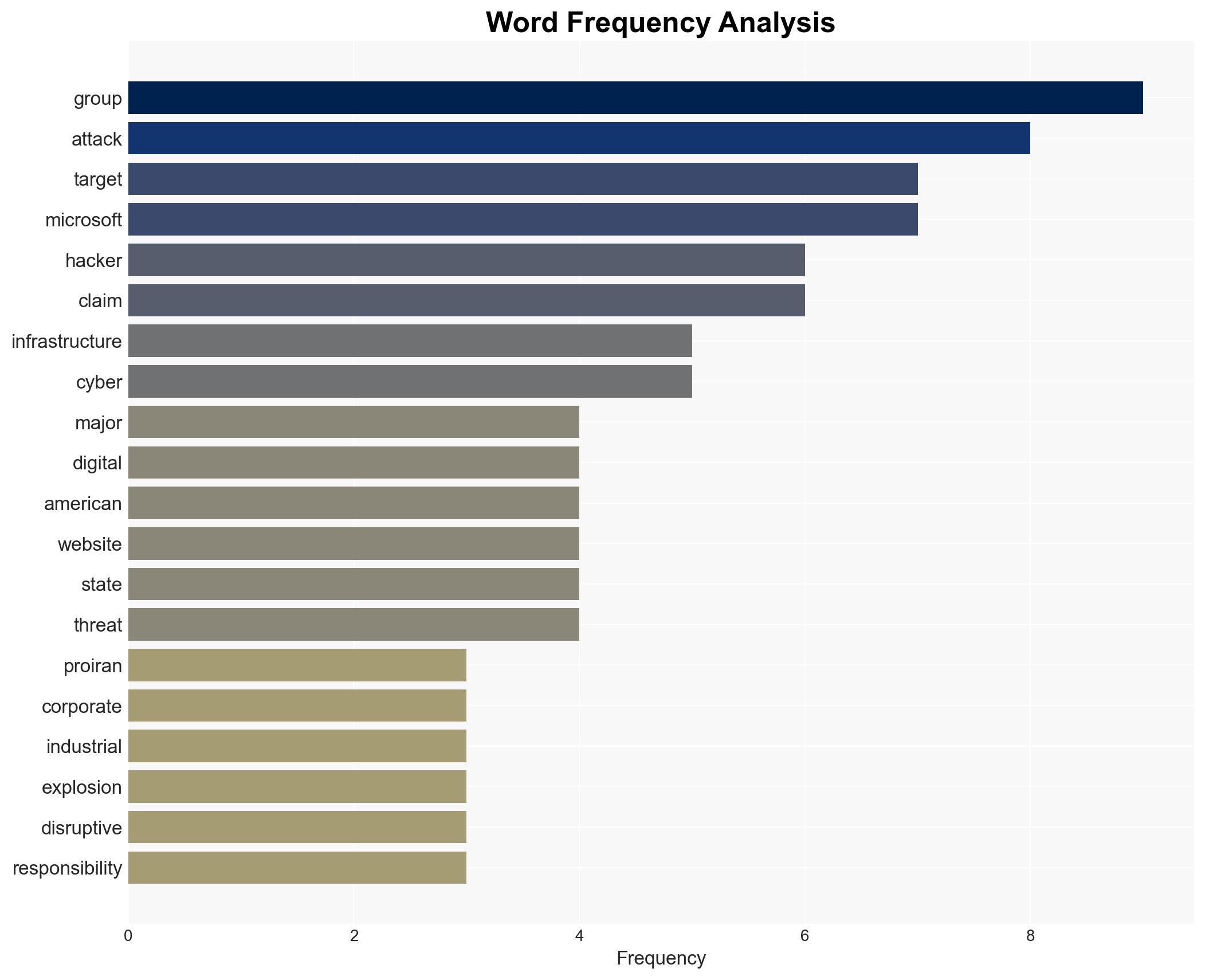
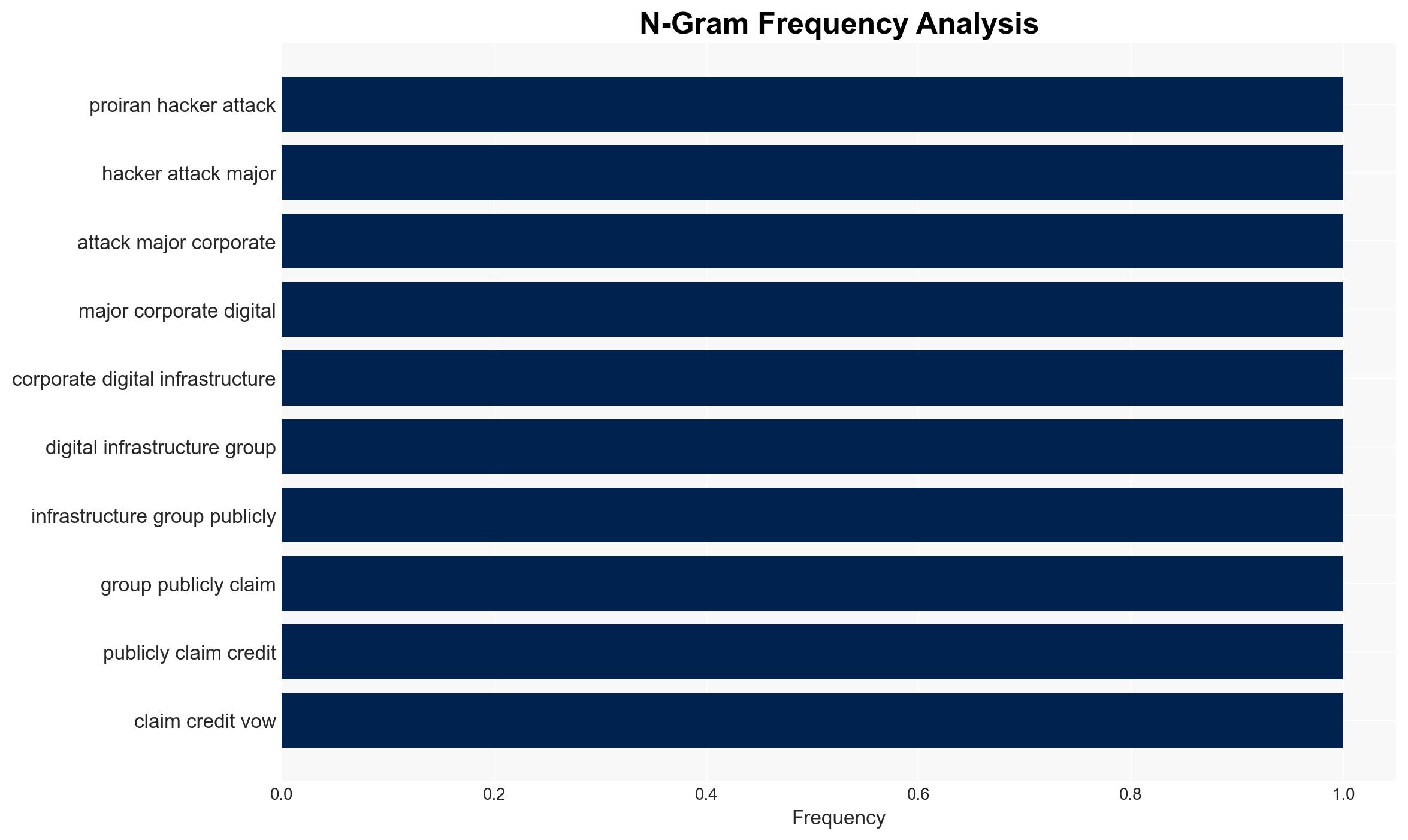
Pro-Iran hacking groups are intensifying cyberattacks on U.S. corporate and digital infrastructure, citing U.S. foreign policy as motivation. The attacks, including a claimed Microsoft 365 outage, represent a shift towards more disruptive and potentially destructive cyber operations. This escalation poses significant risks to U.S. economic and national security interests. Overall confidence in this assessment is moderate due to unverified claims and potential misinformation.
2. Competing Hypotheses
- Hypothesis A: Pro-Iran hackers are genuinely escalating cyberattacks on U.S. targets as a form of hybrid warfare, motivated by geopolitical tensions. Supporting evidence includes public claims of responsibility and alignment with known geopolitical grievances. Contradicting evidence includes the lack of independent verification of some claims, such as the industrial explosion.
- Hypothesis B: The cyberattacks are exaggerated or falsely attributed to pro-Iran groups to sow discord and fear, potentially by other actors with different agendas. Supporting evidence includes the possibility of misinformation campaigns and the lack of verification for some high-profile claims. Contradicting evidence includes the consistency of claims with past pro-Iran cyber activities.
- Assessment: Hypothesis A is currently better supported due to the alignment of the attacks with known geopolitical motivations and the groups’ historical patterns. Verification of claims, especially the industrial explosion, could shift this assessment.
3. Key Assumptions and Red Flags
- Assumptions: The groups claiming responsibility are genuinely aligned with Iranian interests; the attacks are technically feasible by these groups; U.S. foreign policy is a primary motivator for these actions.
- Information Gaps: Verification of the industrial explosion claim; technical attribution of the Microsoft 365 outage; details on the groups’ capabilities and infrastructure.
- Bias & Deception Risks: Potential bias in attributing attacks to pro-Iran groups without full technical evidence; risk of manipulation by actors seeking to exploit geopolitical tensions.
4. Implications and Strategic Risks
This development could lead to increased geopolitical tensions and retaliatory cyber operations. The risk of escalation into physical conflict remains if cyberattacks cause significant disruption or casualties.
- Political / Geopolitical: Potential for heightened U.S.-Iran tensions and impact on diplomatic relations.
- Security / Counter-Terrorism: Increased threat to U.S. critical infrastructure and potential for physical attacks linked to cyber operations.
- Cyber / Information Space: Escalation in cyber warfare tactics and potential for misinformation campaigns to amplify impact.
- Economic / Social: Disruption to major corporations could impact economic stability and public confidence in digital infrastructure.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of pro-Iran cyber activities; verify claims of attacks; strengthen defenses of critical infrastructure.
- Medium-Term Posture (1–12 months): Develop resilience measures and partnerships with private sector; enhance cyber capabilities and threat intelligence sharing.
- Scenario Outlook: Best: De-escalation through diplomatic engagement; Worst: Significant cyberattack causing physical damage; Most-Likely: Continued cyber skirmishes with periodic disruptions.
6. Key Individuals and Entities
- Islamic Cyber Resistance in Iraq – 313 Team
- Cyber Islamic Resistance
- APT IRAN
- Microsoft
- Commerce Bank
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, cyber warfare, Iran-U.S. relations, critical infrastructure, hybrid warfare, misinformation, geopolitical tensions, cyber resilience
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us