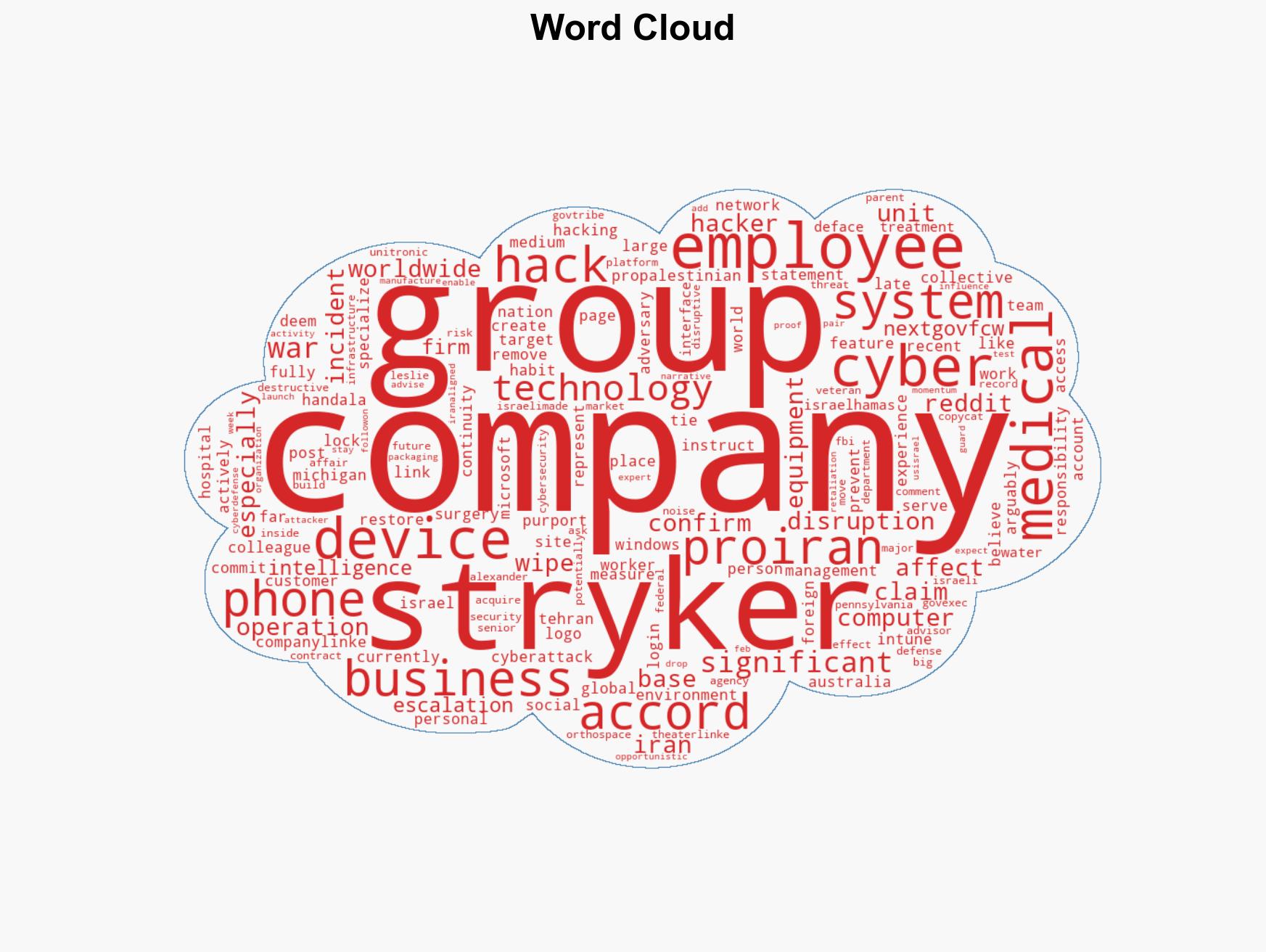
Pro-Iran Hacker Collective Allegedly Responsible for Stryker Cyberattack Disrupting Global Operations
Published on: 2026-03-11
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Suspected pro-Iran hacker group tied to Stryker cyberattack
1. BLUF (Bottom Line Up Front)
The cyberattack on Stryker, attributed to a pro-Iran hacker group, represents a significant escalation in cyber operations linked to geopolitical tensions involving Iran. The attack disrupted global operations of a major U.S. medical technology firm, with potential implications for U.S. national security and economic stability. This assessment is made with moderate confidence, given the attribution to the hacker group and the geopolitical context.
2. Competing Hypotheses
- Hypothesis A: The attack was orchestrated by a pro-Iran hacker group as a retaliatory measure against U.S. and Israeli interests. Supporting evidence includes the appearance of the Handala logo and claims of responsibility on social media. However, the lack of direct technical attribution and potential for false-flag operations are key uncertainties.
- Hypothesis B: The attack could be the work of an unrelated cybercriminal group exploiting geopolitical tensions for opportunistic gains. This is supported by the general increase in cybercriminal activity during geopolitical conflicts. Contradicting evidence includes the specific targeting of a company with ties to U.S. defense and Israeli technology.
- Assessment: Hypothesis A is currently better supported due to the specific geopolitical context and the hacker group’s known modus operandi. Indicators such as further claims of responsibility or technical forensics could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The hacker group has the capability to execute such an attack; the geopolitical context is a motivating factor; Stryker’s ties to U.S. defense and Israeli technology are relevant to the targeting decision.
- Information Gaps: Lack of detailed forensic evidence linking the attack to specific actors; limited insight into the hacker group’s strategic objectives.
- Bias & Deception Risks: Potential cognitive bias towards attributing attacks to known adversaries; risk of manipulation by the hacker group to exaggerate their capabilities or influence.
4. Implications and Strategic Risks
This development could lead to increased cyber operations against U.S. and allied interests, potentially escalating into broader geopolitical tensions. The attack underscores vulnerabilities in critical infrastructure and corporate networks.
- Political / Geopolitical: Potential for heightened tensions between the U.S., Israel, and Iran, with implications for diplomatic relations and regional stability.
- Security / Counter-Terrorism: Increased threat environment for U.S. and allied entities, necessitating enhanced cybersecurity measures.
- Cyber / Information Space: Potential for copycat attacks and influence operations leveraging the incident to sow discord or misinformation.
- Economic / Social: Disruption to Stryker’s operations could impact the healthcare sector and supply chains, with broader economic repercussions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cyber threats, particularly from Iran-aligned groups; implement incident response and recovery plans; engage with cybersecurity agencies for support.
- Medium-Term Posture (1–12 months): Strengthen cybersecurity infrastructure and resilience; foster international cooperation on cyber defense; conduct regular threat assessments.
- Scenario Outlook:
- Best: Effective mitigation and diplomacy reduce tensions, preventing further attacks.
- Worst: Escalation leads to widespread cyberattacks on critical infrastructure.
- Most-Likely: Continued sporadic cyber incidents with incremental improvements in defense capabilities.
6. Key Individuals and Entities
- Handala (pro-Iran and pro-Palestinian hacking group)
- Stryker (U.S.-based medical technology company)
- Alexander Leslie (Senior Advisor, Recorded Future)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, geopolitical tensions, Iran, U.S.-Israel relations, cyber retaliation, critical infrastructure, influence operations
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us