Programmer Gains Unintentional Access to 7,000 Robot Vacuums, Highlighting Smart Device Security Flaws
Published on: 2026-02-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Programmer accidentally hacked 7000 robot vacuums
1. BLUF (Bottom Line Up Front)
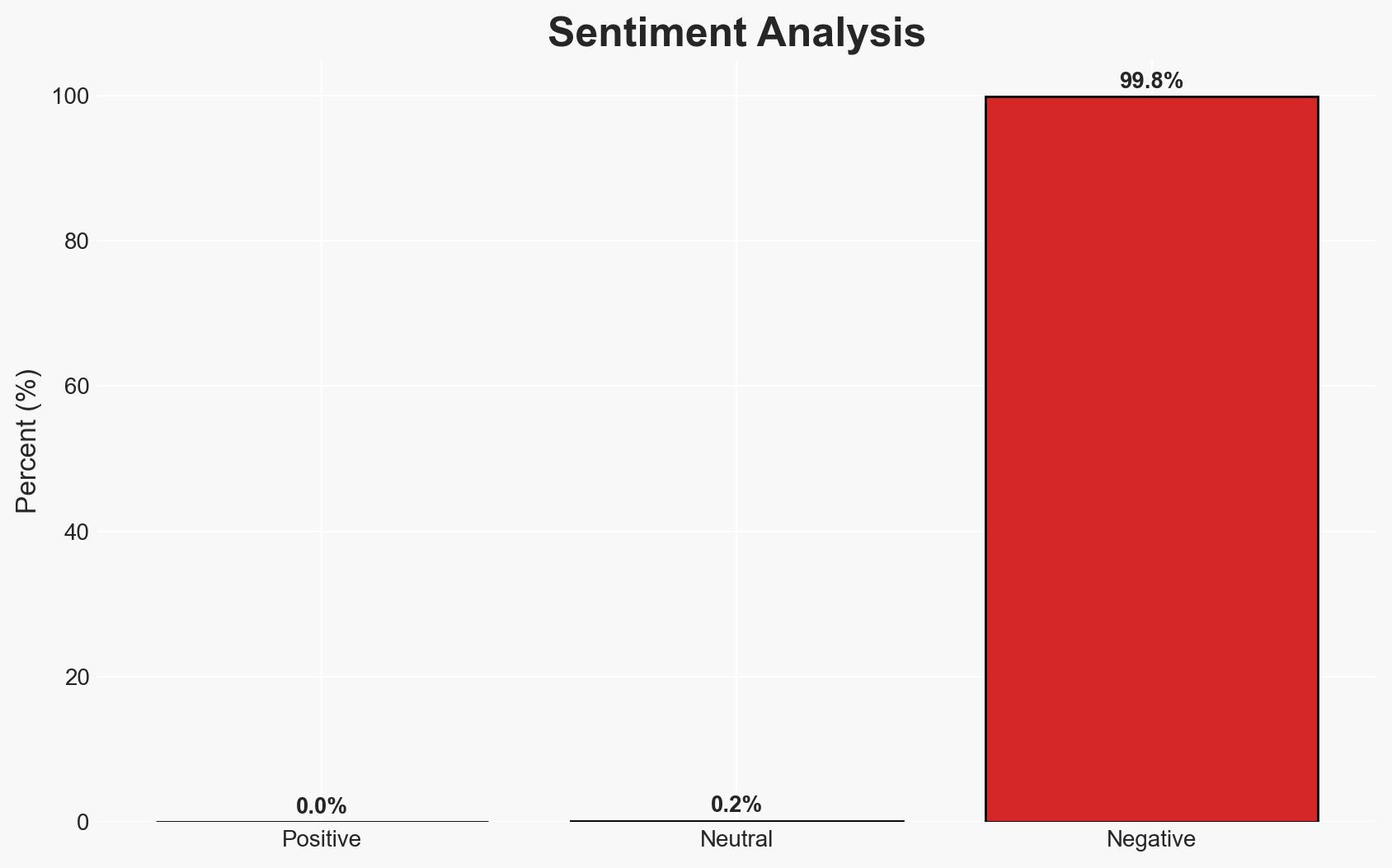
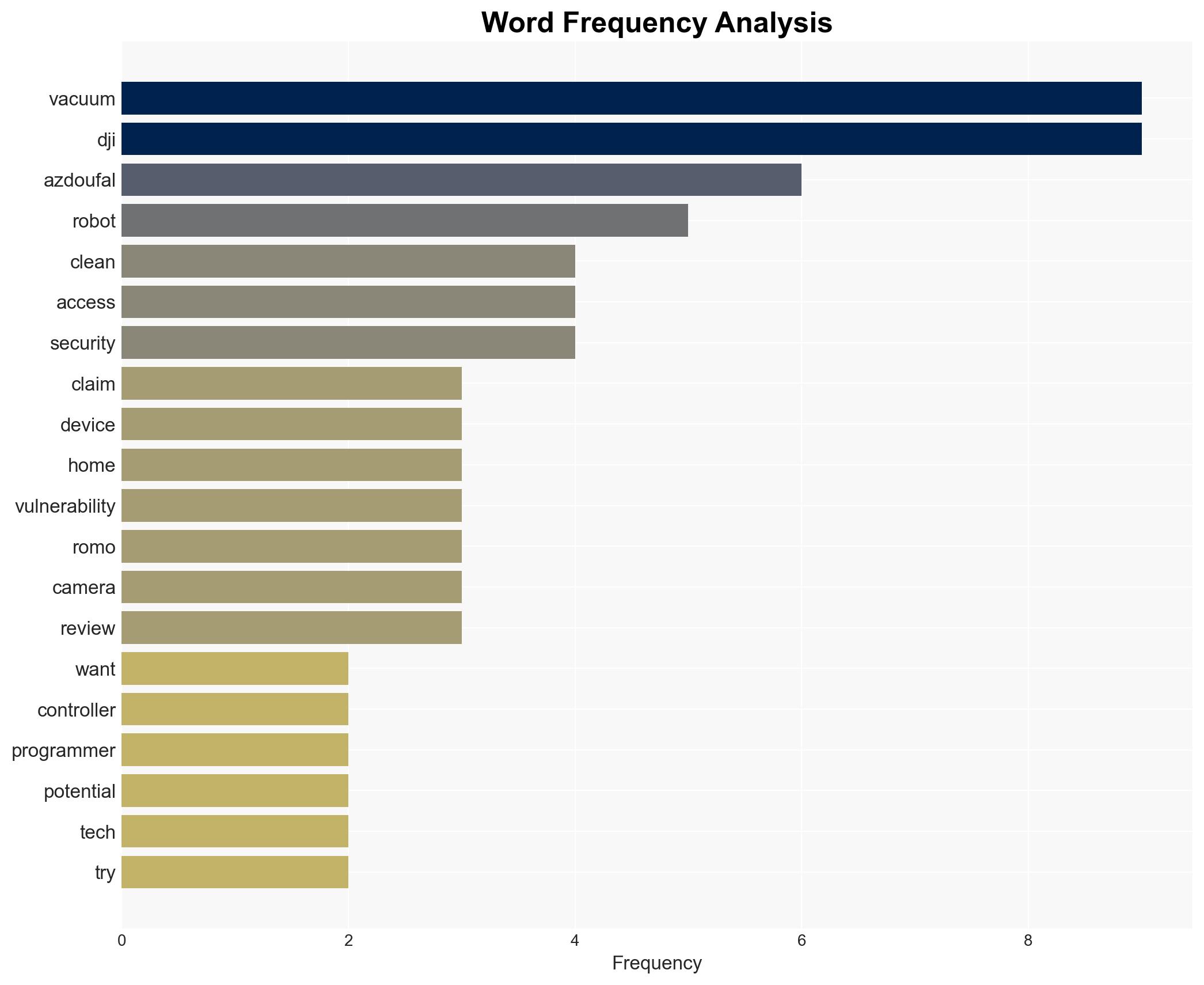
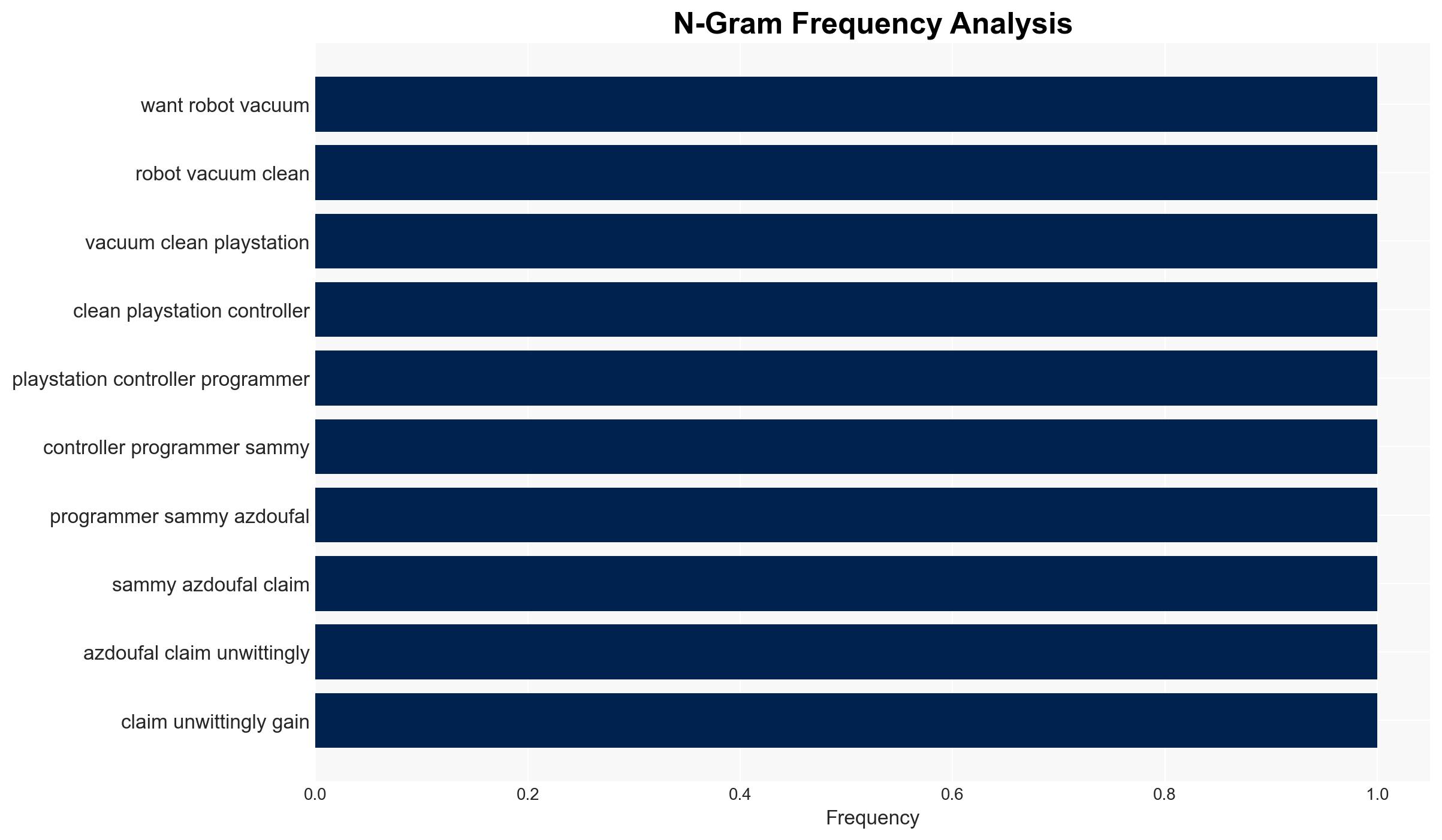
A programmer inadvertently accessed data from 7,000 robot vacuums, revealing significant vulnerabilities in smart home devices. This incident highlights potential security risks associated with IoT devices, affecting both manufacturers and consumers. The most likely hypothesis is that the breach was unintentional and due to a software vulnerability, with moderate confidence in this assessment.
2. Competing Hypotheses
- Hypothesis A: The breach was unintentional, resulting from a software vulnerability in DJI’s systems. This is supported by the programmer’s lack of intent and DJI’s acknowledgment of a vulnerability. However, the extent of the vulnerability and potential for exploitation by others remain uncertain.
- Hypothesis B: The breach was a deliberate act by the programmer to expose security flaws. This is less supported due to the programmer’s reported surprise and immediate notification to DJI and media outlets. The lack of control over the devices further contradicts this hypothesis.
- Assessment: Hypothesis A is currently better supported due to the programmer’s actions and DJI’s response. Indicators that could shift this judgment include evidence of prior knowledge or intent by the programmer or further breaches by other actors.
3. Key Assumptions and Red Flags
- Assumptions: The programmer’s actions were unintentional; DJI’s software had a genuine vulnerability; the breach was limited to data access without control capabilities.
- Information Gaps: Specific technical details of the vulnerability; extent of data accessed; DJI’s internal security measures and response timeline.
- Bias & Deception Risks: Potential bias in the programmer’s account; DJI’s public statements may downplay the severity of the vulnerability.
4. Implications and Strategic Risks
This incident could lead to increased scrutiny of IoT device security and regulatory actions. It may also impact consumer trust and market dynamics for smart home products.
- Political / Geopolitical: Potential regulatory actions or international scrutiny on Chinese tech manufacturers.
- Security / Counter-Terrorism: Increased risk of exploitation by malicious actors if similar vulnerabilities exist in other devices.
- Cyber / Information Space: Heightened awareness and potential for cyber operations targeting IoT vulnerabilities.
- Economic / Social: Possible decline in consumer confidence in smart home technologies, affecting sales and innovation.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a thorough vulnerability assessment of similar IoT devices; enhance monitoring for potential exploitation attempts.
- Medium-Term Posture (1–12 months): Develop partnerships with tech firms for improved security standards; invest in consumer awareness campaigns about IoT security.
- Scenario Outlook:
- Best: Rapid patching and improved security measures restore consumer confidence.
- Worst: Widespread exploitation of similar vulnerabilities leads to significant data breaches.
- Most-Likely: Incremental improvements in IoT security with ongoing regulatory discussions.
6. Key Individuals and Entities
- Sammy Azdoufal, Programmer
- DJI, Chinese technology manufacturer
- The Verge, Technology media outlet
7. Thematic Tags
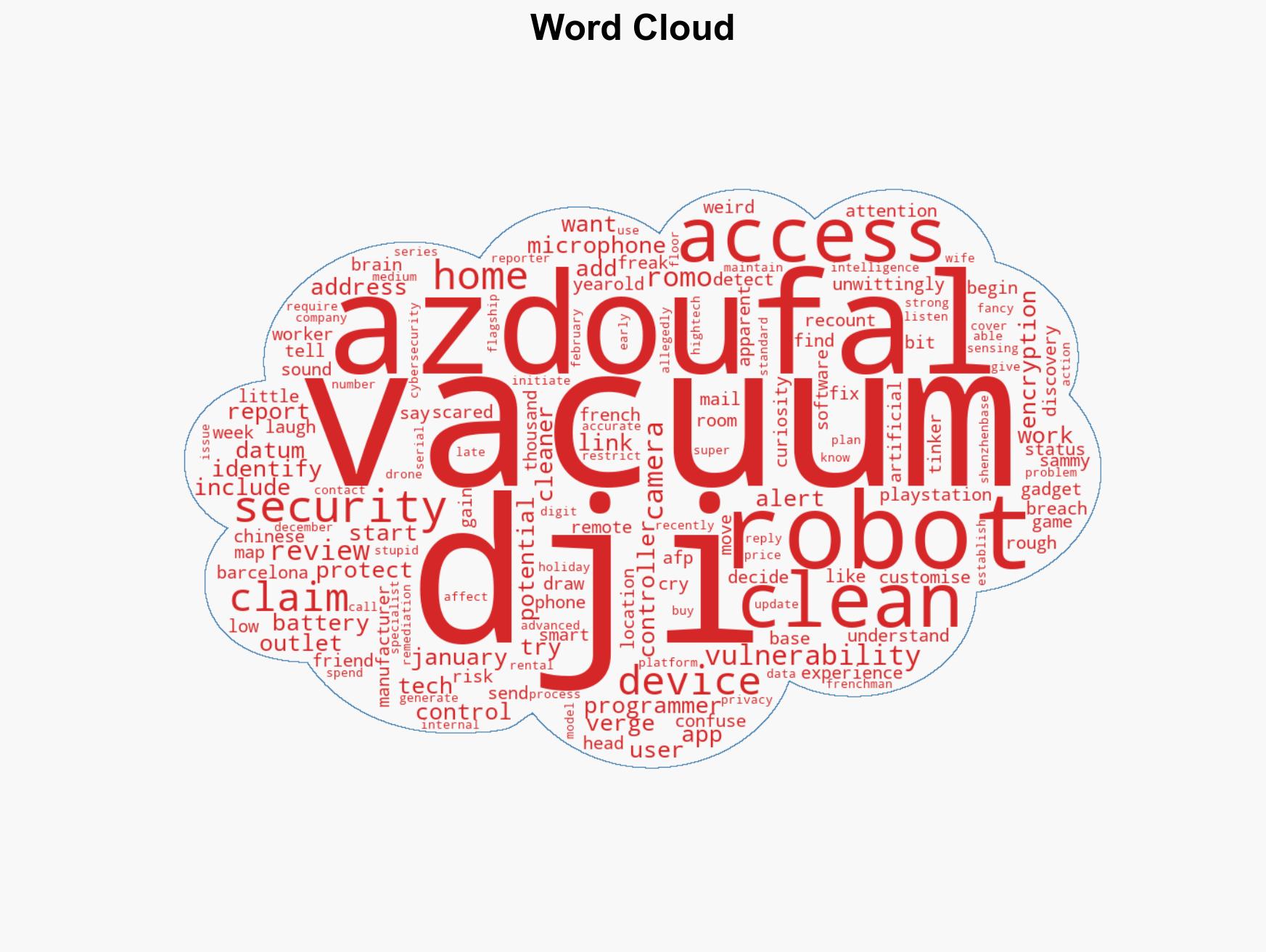
cybersecurity, IoT security, data privacy, cyber vulnerability, smart home technology, consumer electronics, regulatory scrutiny, Chinese tech industry
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us