Queensland cybersecurity audit reveals critical vulnerabilities in government systems and contract management…
Published on: 2026-03-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Cyber audit gains access to government systems in Qld exposing security gap
1. BLUF (Bottom Line Up Front)
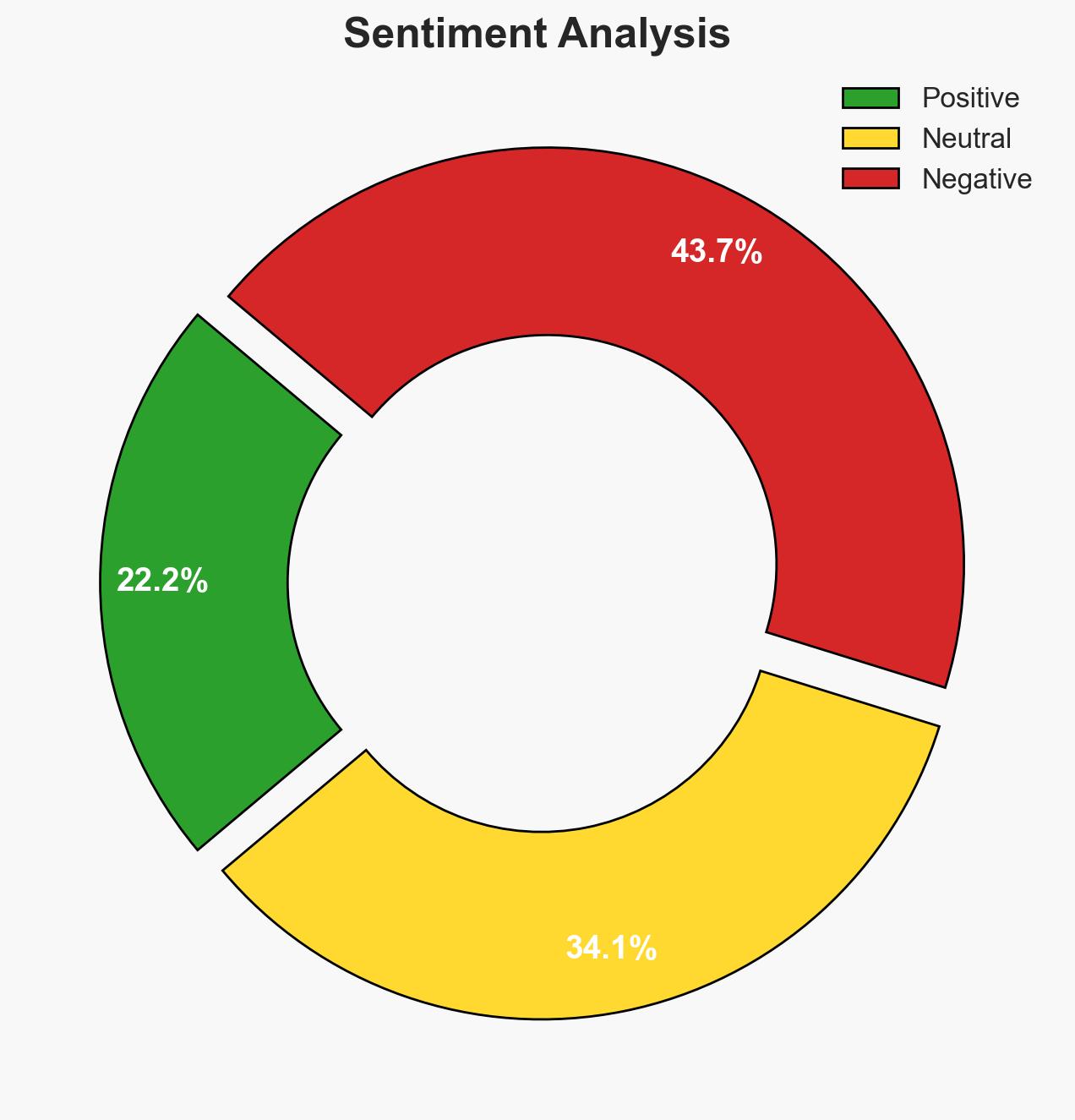
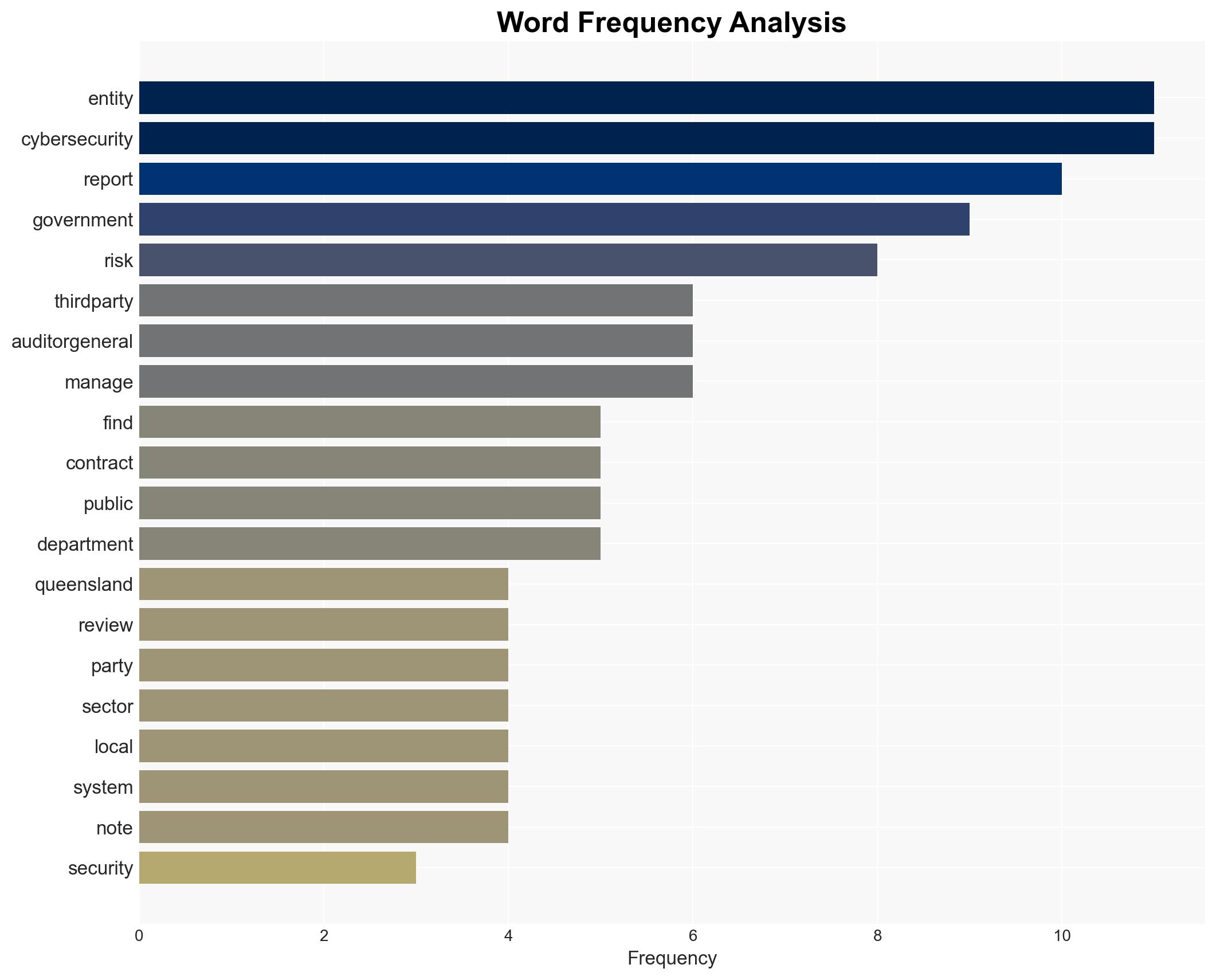
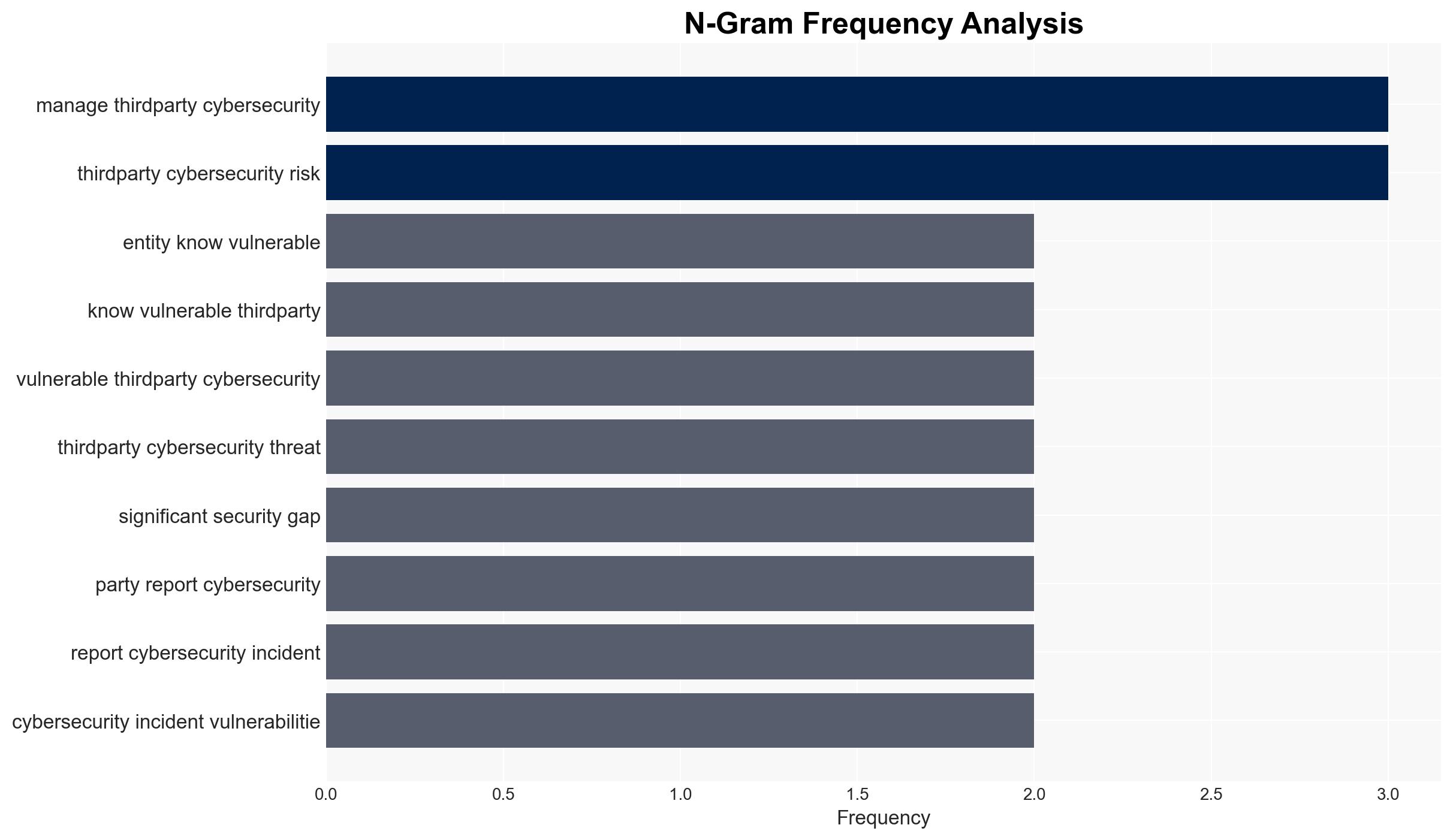
The Queensland Audit Office report reveals significant cybersecurity vulnerabilities in government systems, particularly concerning third-party risks. The audit’s findings indicate a lack of awareness and inadequate contract management, which could lead to severe security breaches. This affects multiple government entities, with moderate confidence in the assessment due to identified gaps and potential biases.
2. Competing Hypotheses
- Hypothesis A: The cybersecurity vulnerabilities are primarily due to inadequate contract management and lack of awareness about third-party risks. This is supported by the finding that only two of 36 contracts required third-party incident reporting. However, the extent of the vulnerabilities across all entities remains uncertain.
- Hypothesis B: The vulnerabilities are a result of systemic issues within the Queensland government’s cybersecurity framework, exacerbated by slow response to known risks. The report notes the government’s delayed development of a comprehensive risk management framework since 2021.
- Assessment: Hypothesis A is currently better supported due to specific evidence of contract management failures. Indicators such as improved contract requirements or increased awareness could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Government entities have not fully implemented recommended cybersecurity measures; third-party risks are not adequately monitored; contract management practices are outdated.
- Information Gaps: Detailed information on the specific entities affected and the nature of the vulnerabilities is lacking.
- Bias & Deception Risks: Potential bias in the report’s focus on contract management; risk of underreporting by entities due to reputational concerns.
4. Implications and Strategic Risks
The identified cybersecurity gaps could lead to increased vulnerability to cyber attacks, affecting governmental operations and public trust.
- Political / Geopolitical: Potential for increased scrutiny and pressure on government officials to enhance cybersecurity measures.
- Security / Counter-Terrorism: Increased risk of exploitation by malicious actors, potentially leading to data breaches or infrastructure disruptions.
- Cyber / Information Space: Heightened threat landscape with potential for sophisticated cyber attacks targeting weak points.
- Economic / Social: Possible financial losses and reputational damage to government entities, affecting public confidence.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive review of all contracts to ensure cybersecurity requirements are included; increase monitoring of third-party activities.
- Medium-Term Posture (1–12 months): Develop and implement a robust cybersecurity framework; enhance training and awareness programs for government staff.
- Scenario Outlook:
- Best: Rapid implementation of recommendations leads to strengthened cybersecurity posture.
- Worst: Continued vulnerabilities result in significant cyber incidents.
- Most-Likely: Gradual improvements with occasional setbacks as entities adapt to new requirements.
6. Key Individuals and Entities
- Queensland Audit Office
- Auditor-General
- Queensland government entities (specific entities not clearly identifiable from open sources in this snippet)
7. Thematic Tags
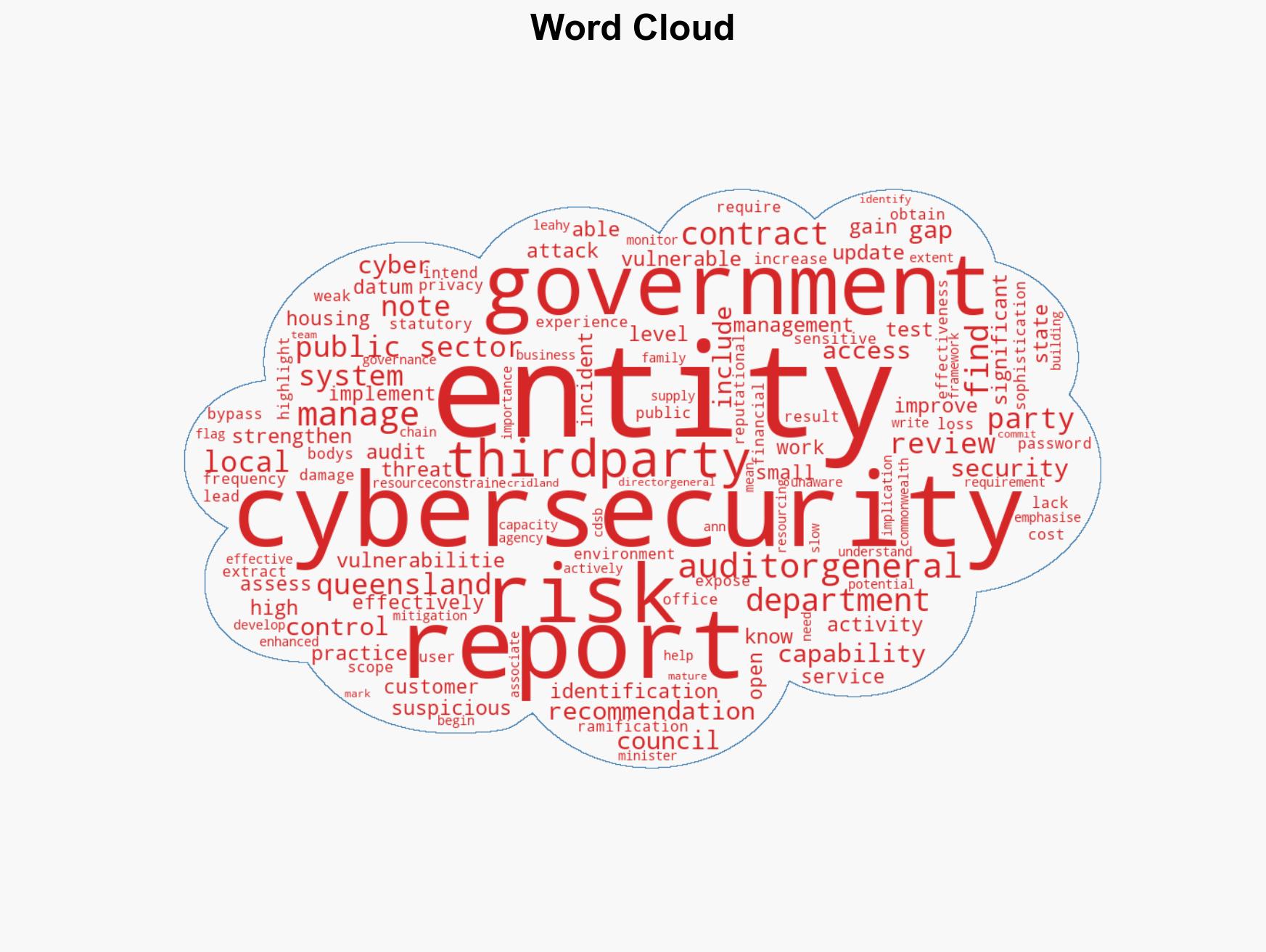
cybersecurity, third-party risk, government systems, contract management, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us