Ransomware Multi-Extortion Attacks Surge, Disrupting Healthcare and Financial Services Nationwide
Published on: 2026-04-03
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Evolution of Ransomware Multi-Extortion Ransomware Attacks
1. BLUF (Bottom Line Up Front)
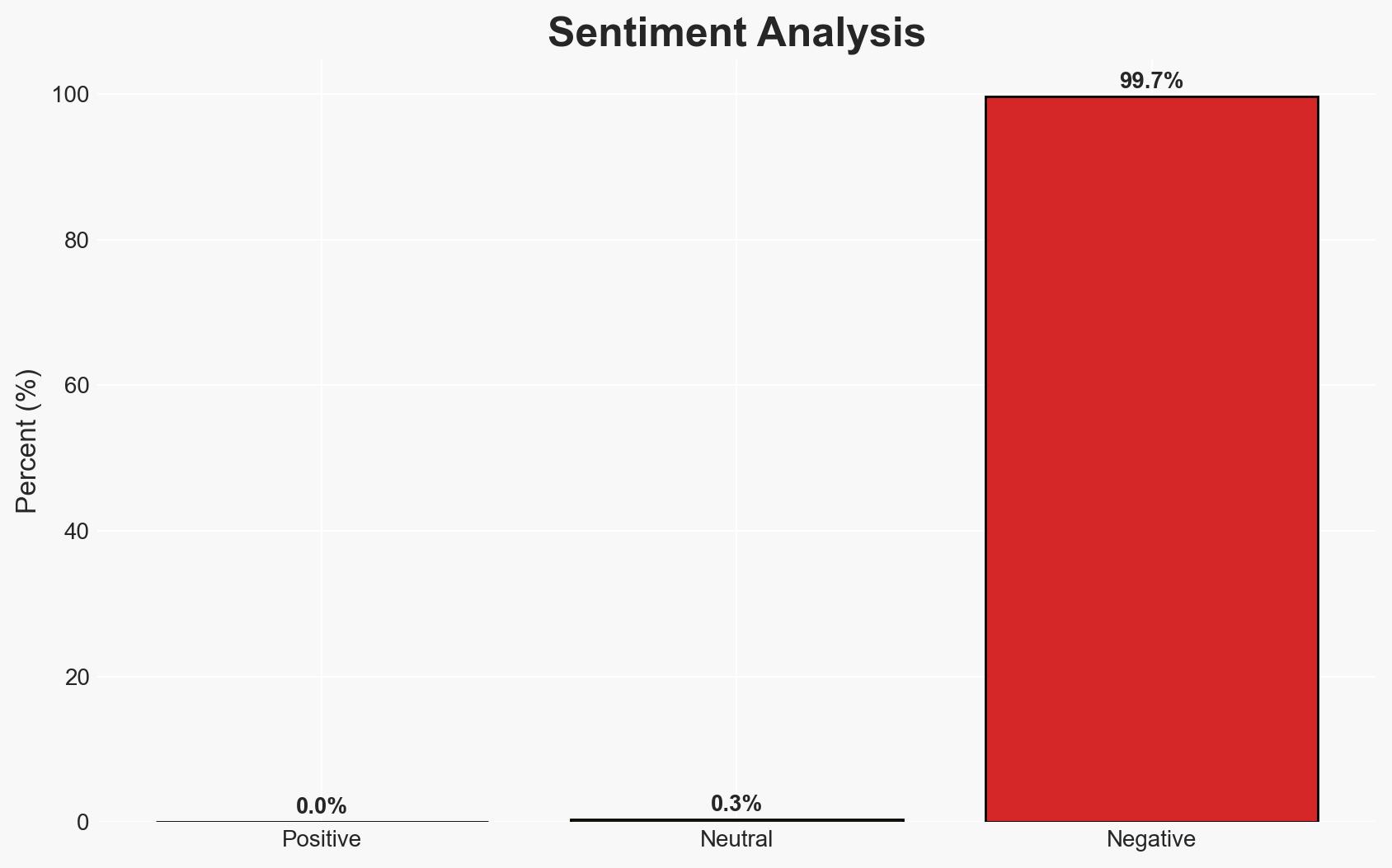
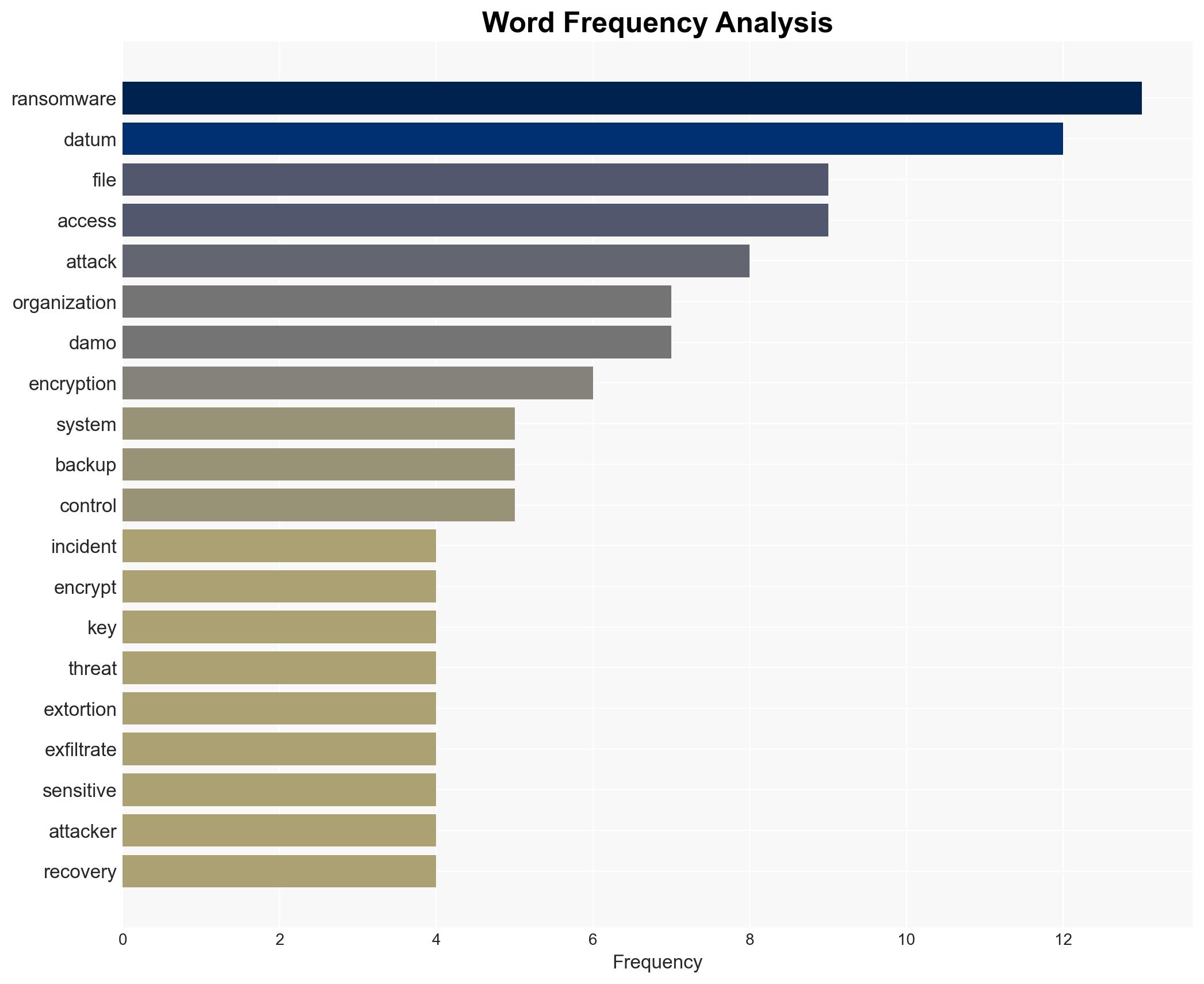
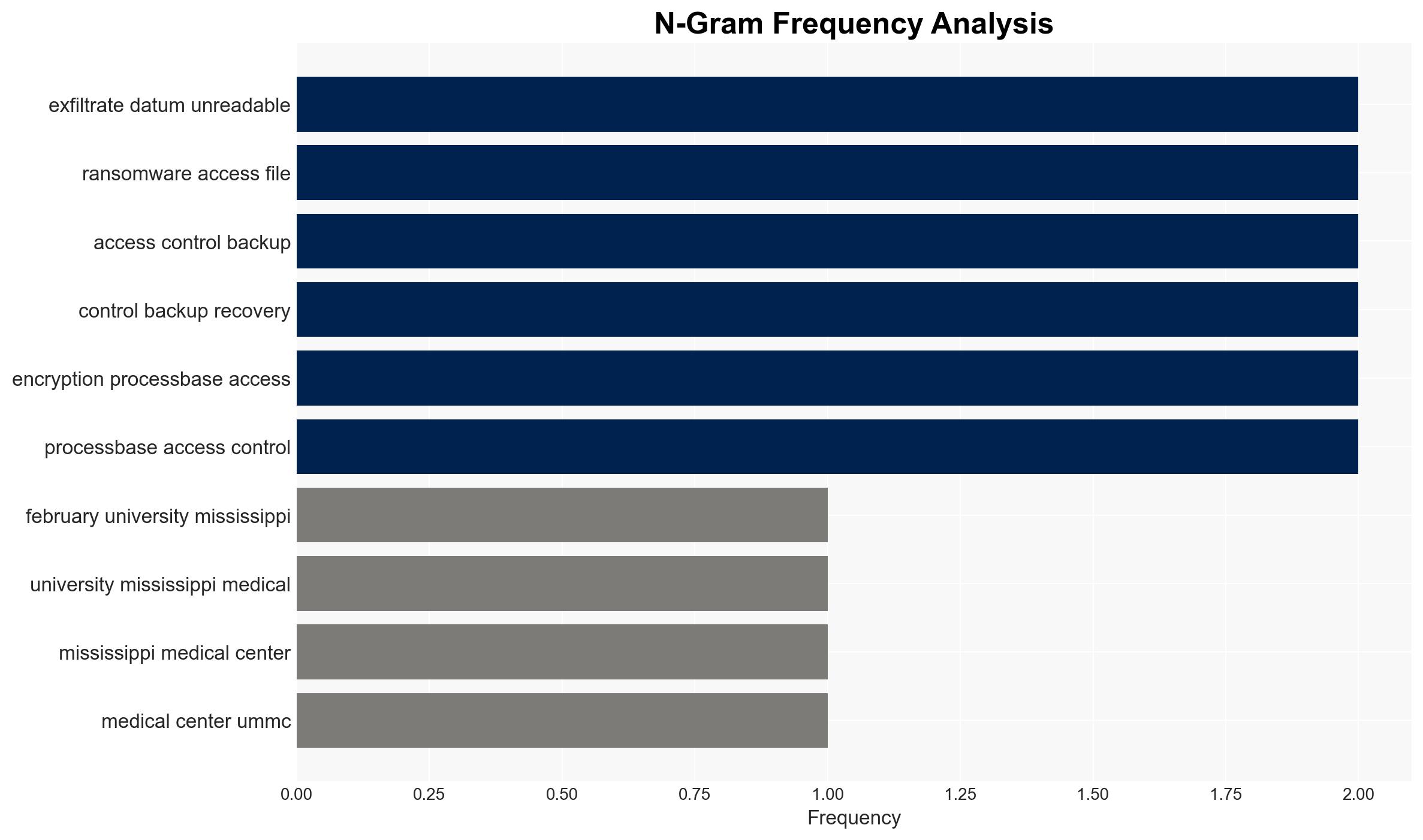
The evolution of ransomware into multi-extortion tactics poses a significant threat to critical sectors such as healthcare, finance, and manufacturing. The most likely hypothesis is that ransomware groups will continue to innovate and expand their tactics, increasing operational and regulatory risks for affected organizations. This assessment is made with moderate confidence due to the rapid proliferation of ransomware groups and the increasing accessibility of cybercrime tools.
2. Competing Hypotheses
- Hypothesis A: Ransomware attacks will continue to evolve in sophistication and frequency, driven by the proliferation of AI-powered tools and the emergence of new threat actors. This is supported by the increase in ransomware groups and the shift to multi-extortion tactics. However, the extent of AI’s impact on attack sophistication remains uncertain.
- Hypothesis B: The current surge in ransomware attacks will plateau as organizations improve their defenses and regulatory frameworks become more stringent. This is contradicted by the persistent increase in attack frequency and the adaptability of threat actors.
- Assessment: Hypothesis A is currently better supported due to the observed trends in attack frequency and sophistication. Key indicators that could shift this judgment include significant advancements in defensive technologies or international regulatory cooperation that effectively deters ransomware activities.
3. Key Assumptions and Red Flags
- Assumptions: Organizations will continue to struggle with implementing comprehensive cybersecurity measures; threat actors will maintain or increase their current level of sophistication; regulatory responses will lag behind the evolving threat landscape.
- Information Gaps: Detailed intelligence on the internal operations and motivations of emerging ransomware groups; effectiveness of current defensive measures across different sectors.
- Bias & Deception Risks: Potential over-reliance on publicly disclosed incidents, which may not represent the full scope of ransomware activities; possible underestimation of defensive capabilities due to lack of visibility into private sector innovations.
4. Implications and Strategic Risks
The continued evolution of ransomware tactics could significantly disrupt critical infrastructure and economic stability, with potential cascading effects on public trust and international relations.
- Political / Geopolitical: Increased tension between nations over cybersecurity responsibilities and potential attribution disputes.
- Security / Counter-Terrorism: Heightened threat environment as ransomware tactics could be adopted by terrorist groups to fund operations or cause disruption.
- Cyber / Information Space: Greater emphasis on cybersecurity resilience and the development of advanced threat detection and response capabilities.
- Economic / Social: Potential for significant economic losses and social disruption, particularly in sectors critical to public health and safety.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of ransomware group activities; increase awareness and training for potential targets; strengthen incident response protocols.
- Medium-Term Posture (1–12 months): Develop partnerships for information sharing; invest in advanced cybersecurity technologies; advocate for stronger regulatory frameworks.
- Scenario Outlook:
- Best Case: Effective international cooperation leads to a significant reduction in ransomware incidents.
- Worst Case: Ransomware attacks cause widespread disruption across critical sectors, leading to economic and social instability.
- Most-Likely: Continued increase in attack frequency and sophistication, with incremental improvements in defensive measures.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
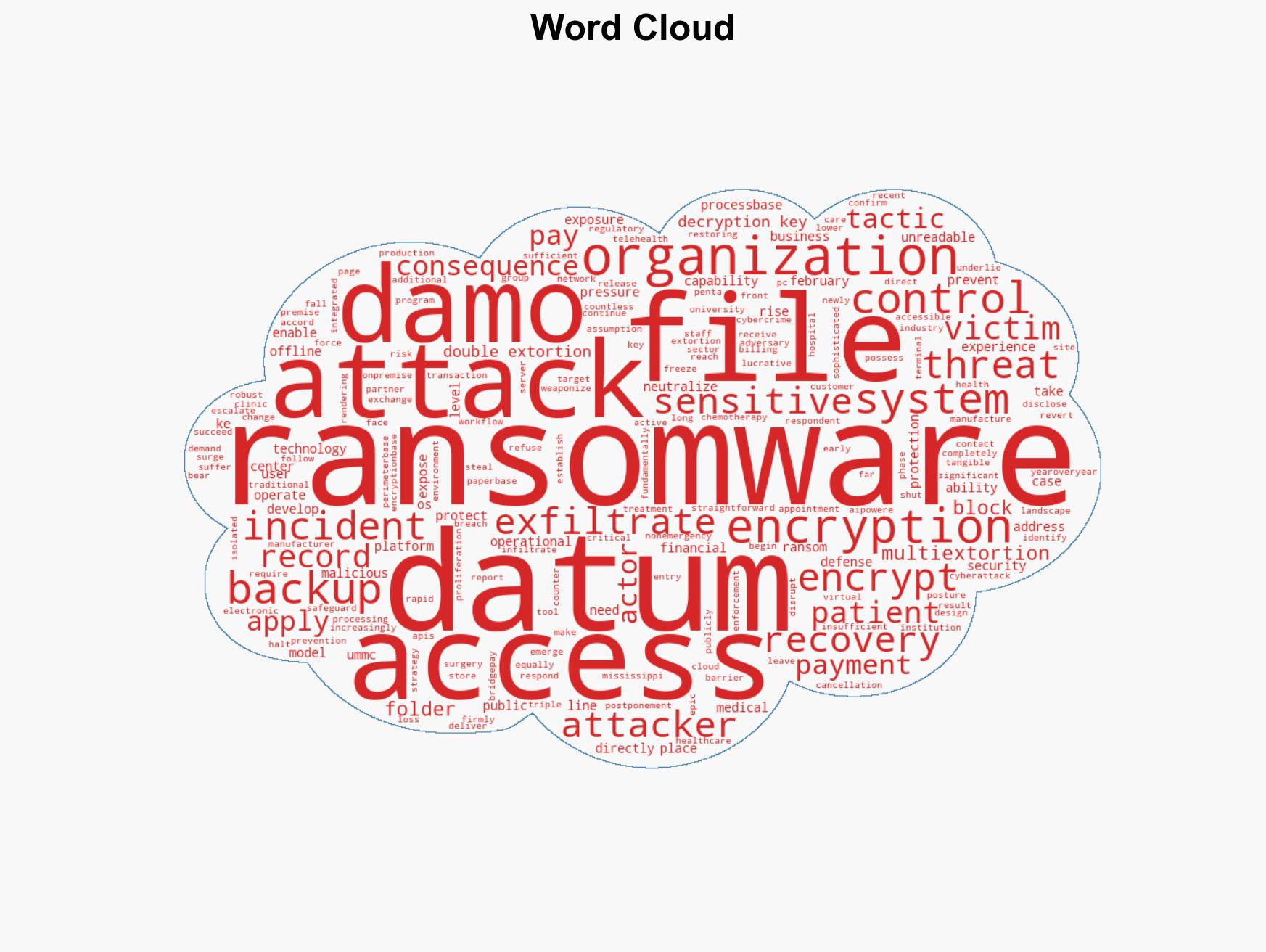
cybersecurity, ransomware, cybercrime, healthcare security, financial sector risk, multi-extortion, AI in cybercrime, regulatory challenges
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us