Rapid Exploitation of Vulnerabilities Demands Immediate Patching and Enhanced Security Measures
Published on: 2026-03-23
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Lightning-fast exploits make it essential to patch fast ask questions later
1. BLUF (Bottom Line Up Front)
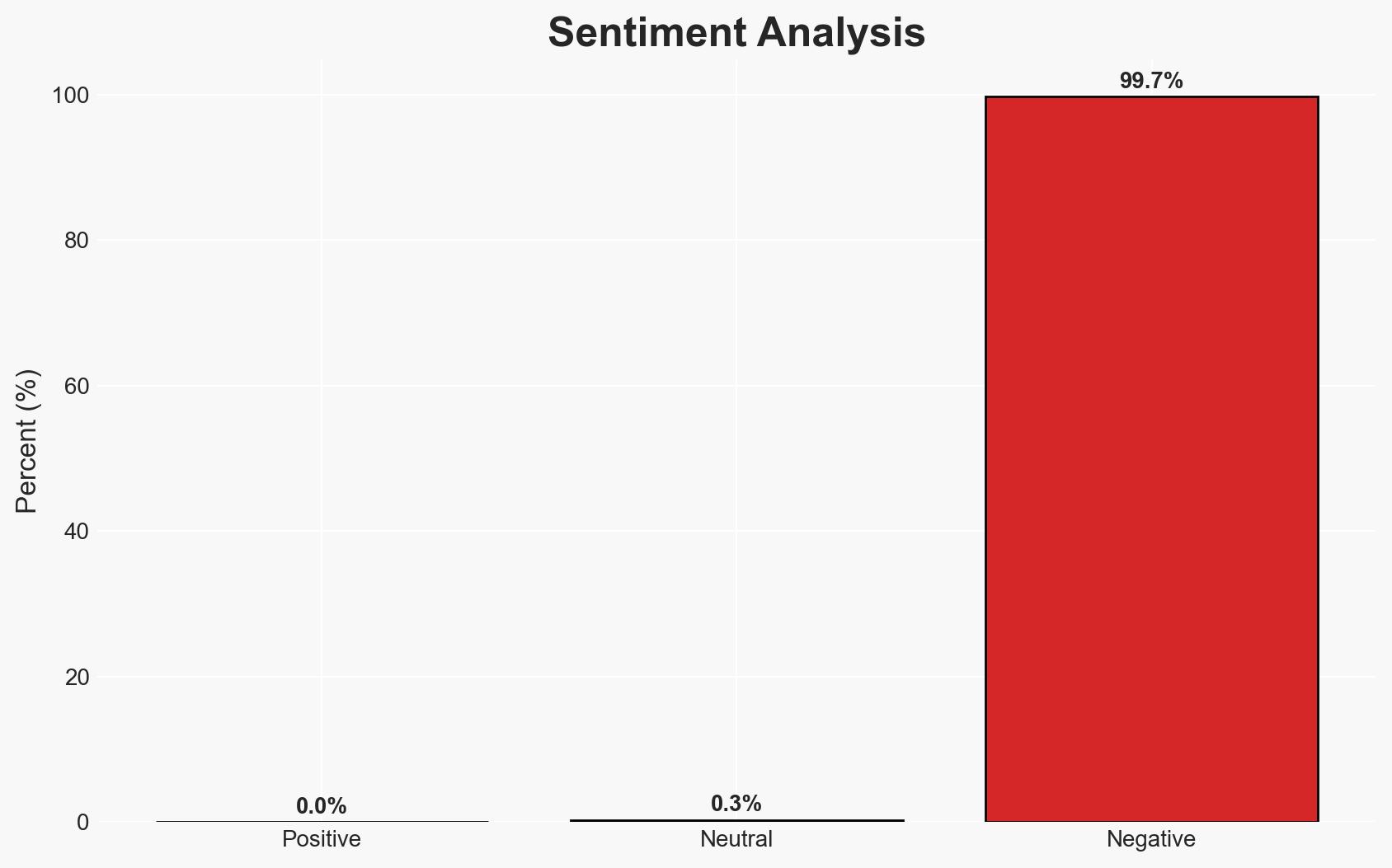
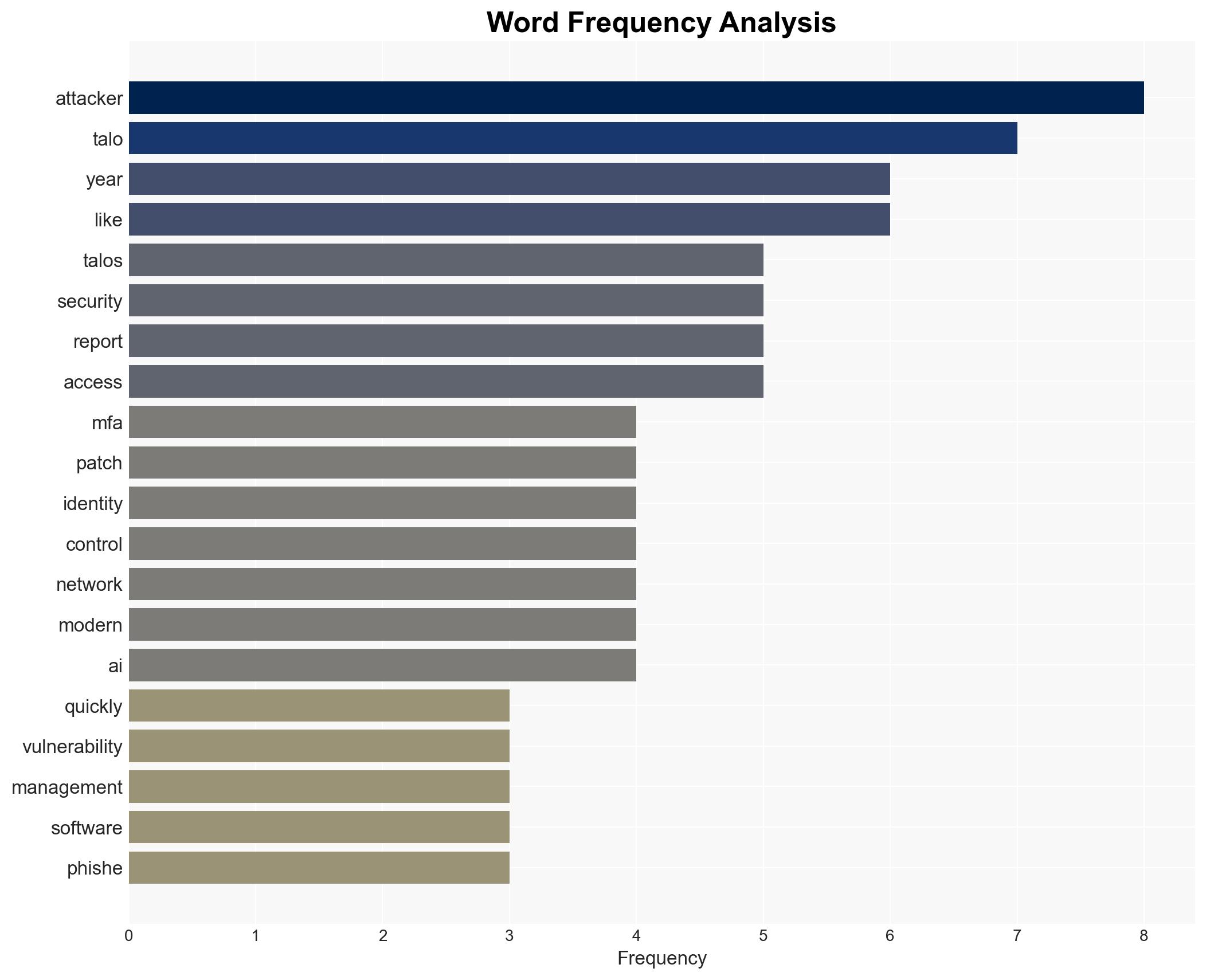
The rapid exploitation of vulnerabilities, driven by AI-enhanced cybercriminal tactics, poses a significant threat to global cybersecurity. The most likely hypothesis is that attackers will continue to exploit identity control points and leverage sophisticated phishing techniques, impacting organizations worldwide. Overall confidence in this assessment is moderate, given the evolving nature of cyber threats and the potential for rapid changes in tactics.
2. Competing Hypotheses
- Hypothesis A: Cyber attackers are primarily targeting identity control points and using AI to enhance phishing attacks, as evidenced by the rapid exploitation of vulnerabilities like React2Shell and the sophistication of phishing lures. Key uncertainties include the extent of AI’s role and the potential for new, unforeseen vulnerabilities.
- Hypothesis B: The primary driver of increased cyber threats is not AI-enhanced tactics but rather the sheer volume of vulnerabilities and the lack of timely patching by organizations. This hypothesis is supported by the persistent issue of unpatched systems but contradicted by the specific targeting of identity control points and the sophistication of phishing attacks.
- Assessment: Hypothesis A is currently better supported due to the specific targeting patterns and the role of AI in enhancing attack sophistication. Indicators that could shift this judgment include new evidence of vulnerabilities being exploited without AI involvement or a significant decrease in the sophistication of phishing attacks.
3. Key Assumptions and Red Flags
- Assumptions: Attackers will continue to prioritize identity control points; AI will remain a key tool in enhancing cyber attack sophistication; organizations will struggle to patch vulnerabilities promptly.
- Information Gaps: Detailed data on the specific AI tools used by attackers and the full scope of vulnerabilities exploited in 2025.
- Bias & Deception Risks: Potential bias in reporting from cybersecurity firms with vested interests; risk of deception in the sophistication of phishing attacks due to AI-generated content.
4. Implications and Strategic Risks
The rapid exploitation of vulnerabilities could lead to increased geopolitical tensions, as states may accuse each other of harboring or supporting cybercriminals. The evolving threat landscape requires adaptive security measures to prevent significant breaches.
- Political / Geopolitical: Potential for increased cyber attribution disputes and diplomatic tensions.
- Security / Counter-Terrorism: Enhanced threat environment with increased risk of critical infrastructure attacks.
- Cyber / Information Space: Greater need for robust cybersecurity frameworks and AI countermeasures.
- Economic / Social: Potential economic disruptions from successful cyber attacks, impacting business continuity and public trust.
5. Recommendations and Outlook
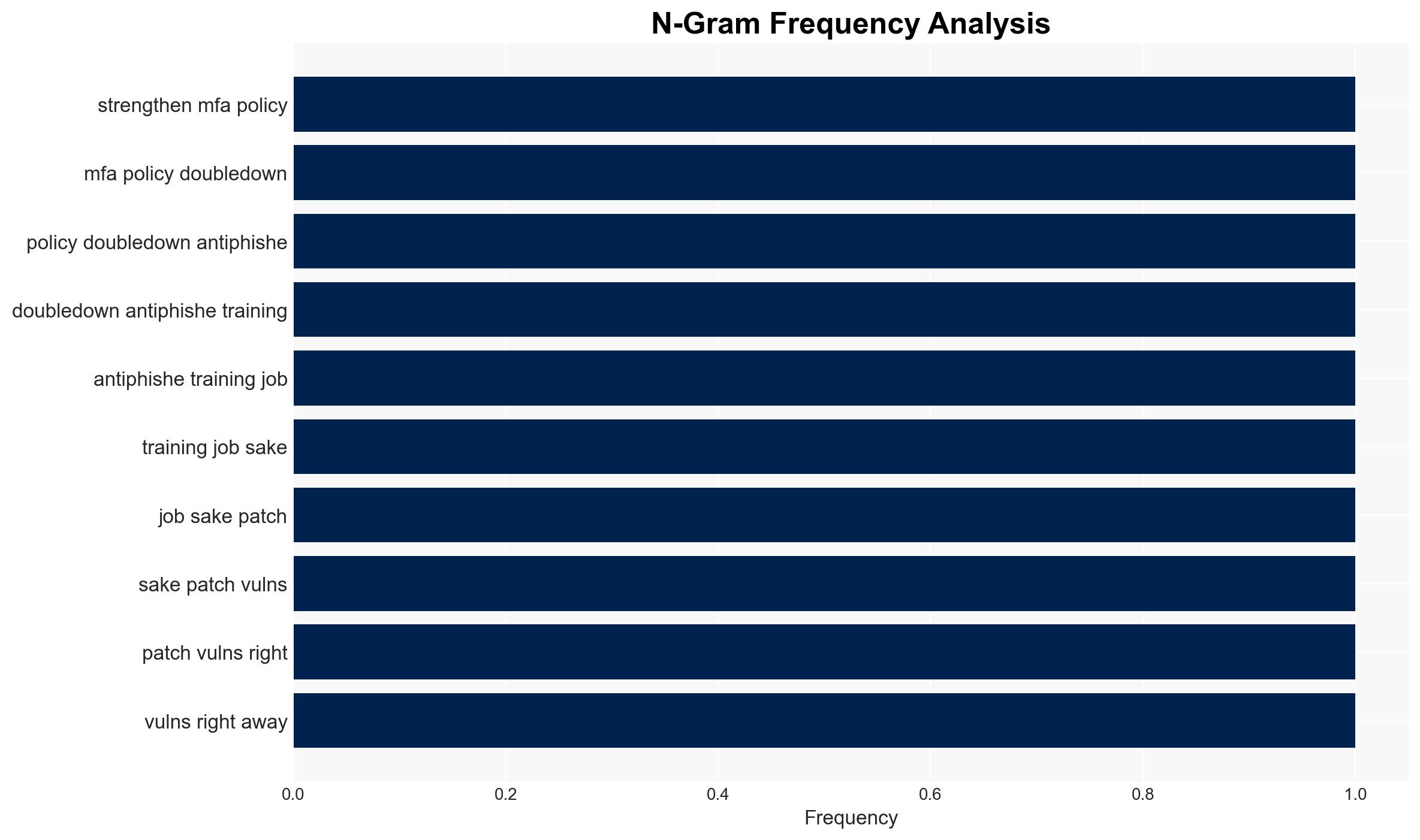
- Immediate Actions (0–30 days): Enhance monitoring of identity control points, implement rapid patching protocols, and conduct comprehensive phishing awareness training.
- Medium-Term Posture (1–12 months): Develop AI-based defensive tools, strengthen international cybersecurity partnerships, and invest in cybersecurity workforce development.
- Scenario Outlook:
- Best: Successful implementation of AI defenses reduces attack success rates.
- Worst: Major breaches in critical infrastructure lead to significant economic and social disruptions.
- Most-Likely: Continued adaptation by both attackers and defenders, with sporadic successful breaches.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
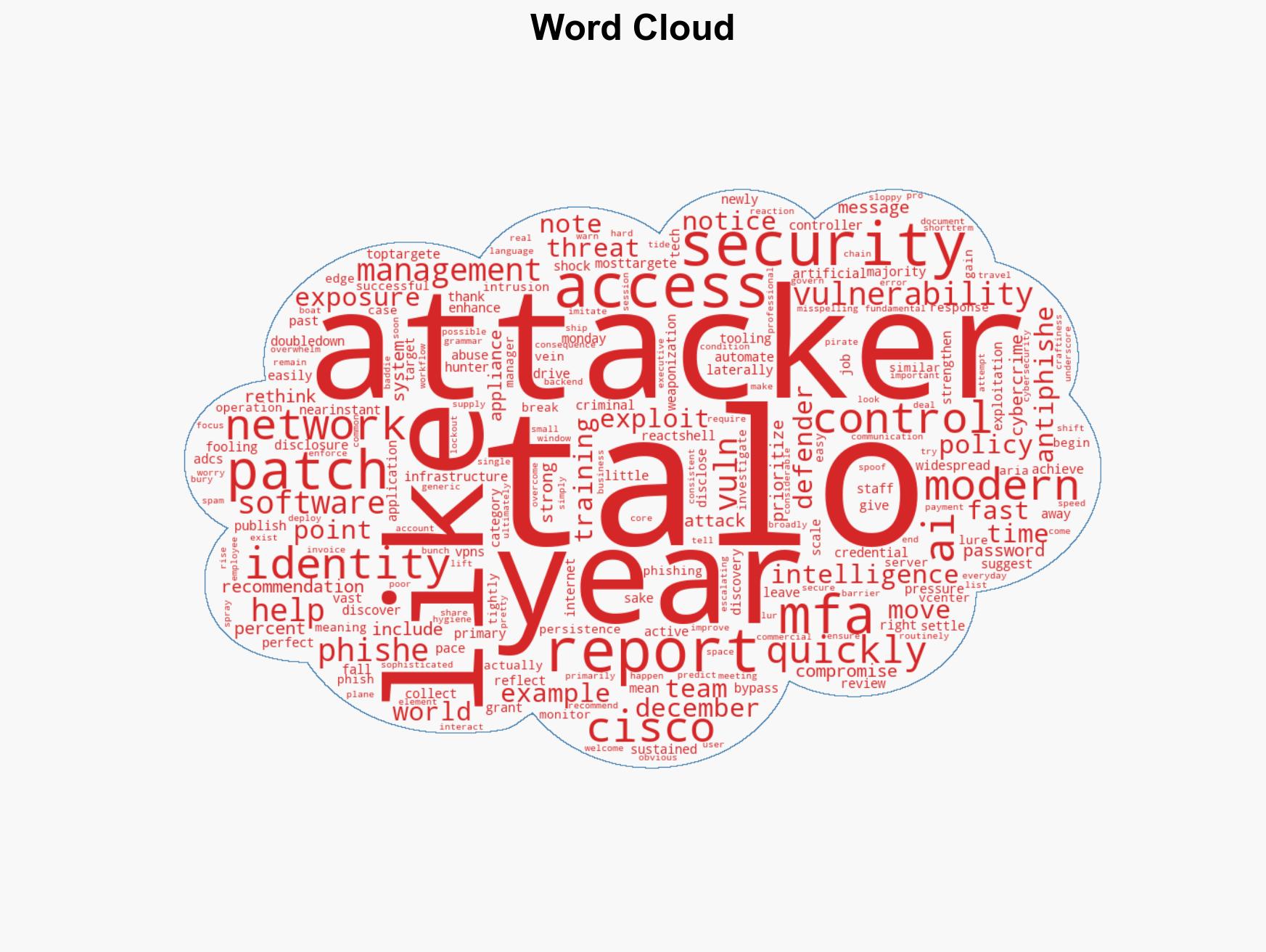
cybersecurity, AI-enhanced attacks, identity control points, phishing, vulnerability exploitation, cyber defense, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us