Reforming Defense Acquisition: New Strategies Risk Addressing Outdated Challenges in Modern Warfare
Published on: 2026-03-31
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Solving Yesterdays Problems Will Kill You
1. BLUF (Bottom Line Up Front)
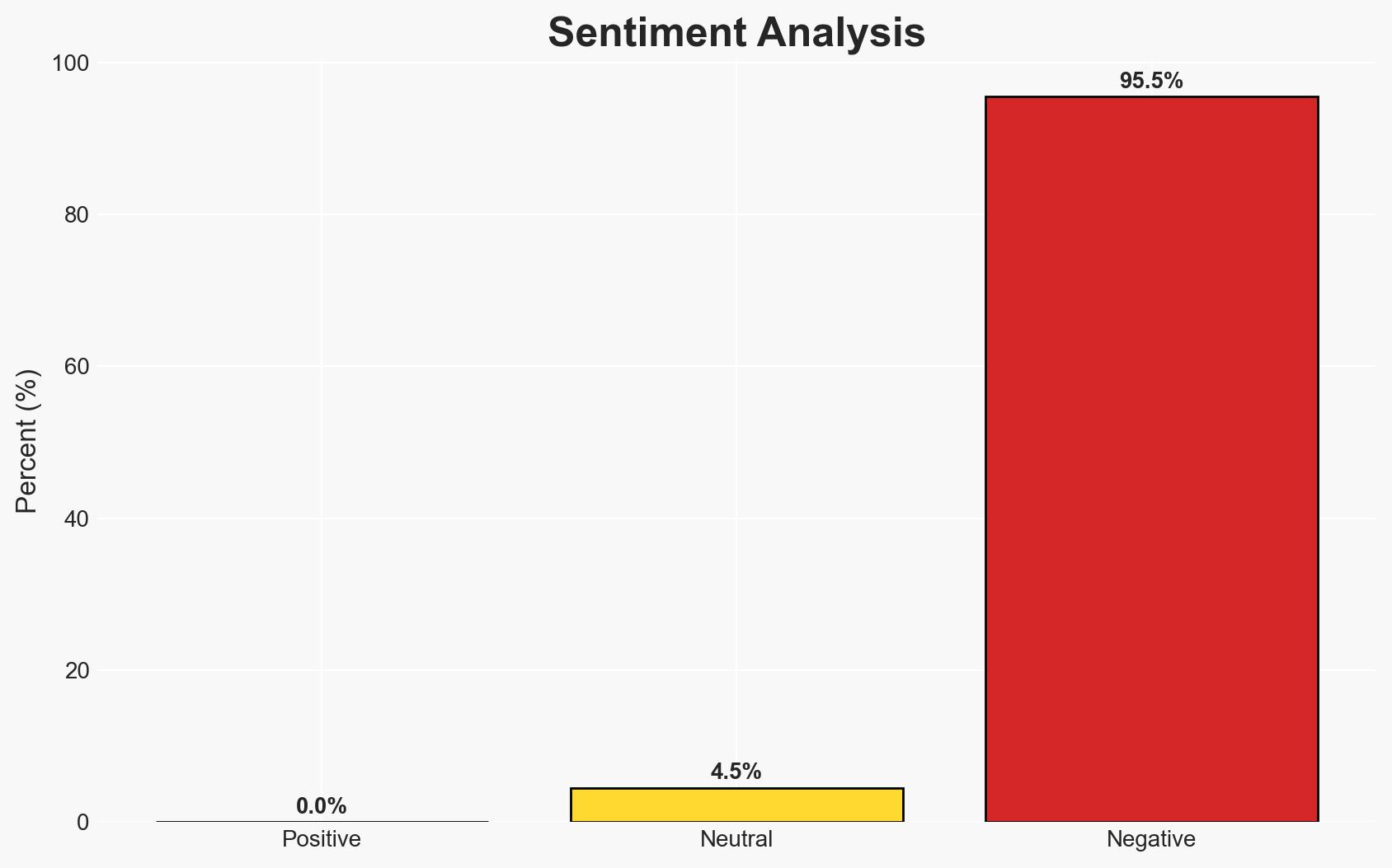
The Department of War’s acquisition reform aims to address modern warfare challenges, but risks focusing on outdated threats due to a lack of agile problem identification processes. The most likely hypothesis is that without significant changes, the reforms will inadequately address emerging threats. This affects defense strategy and operational effectiveness, with moderate confidence in this assessment.
2. Competing Hypotheses
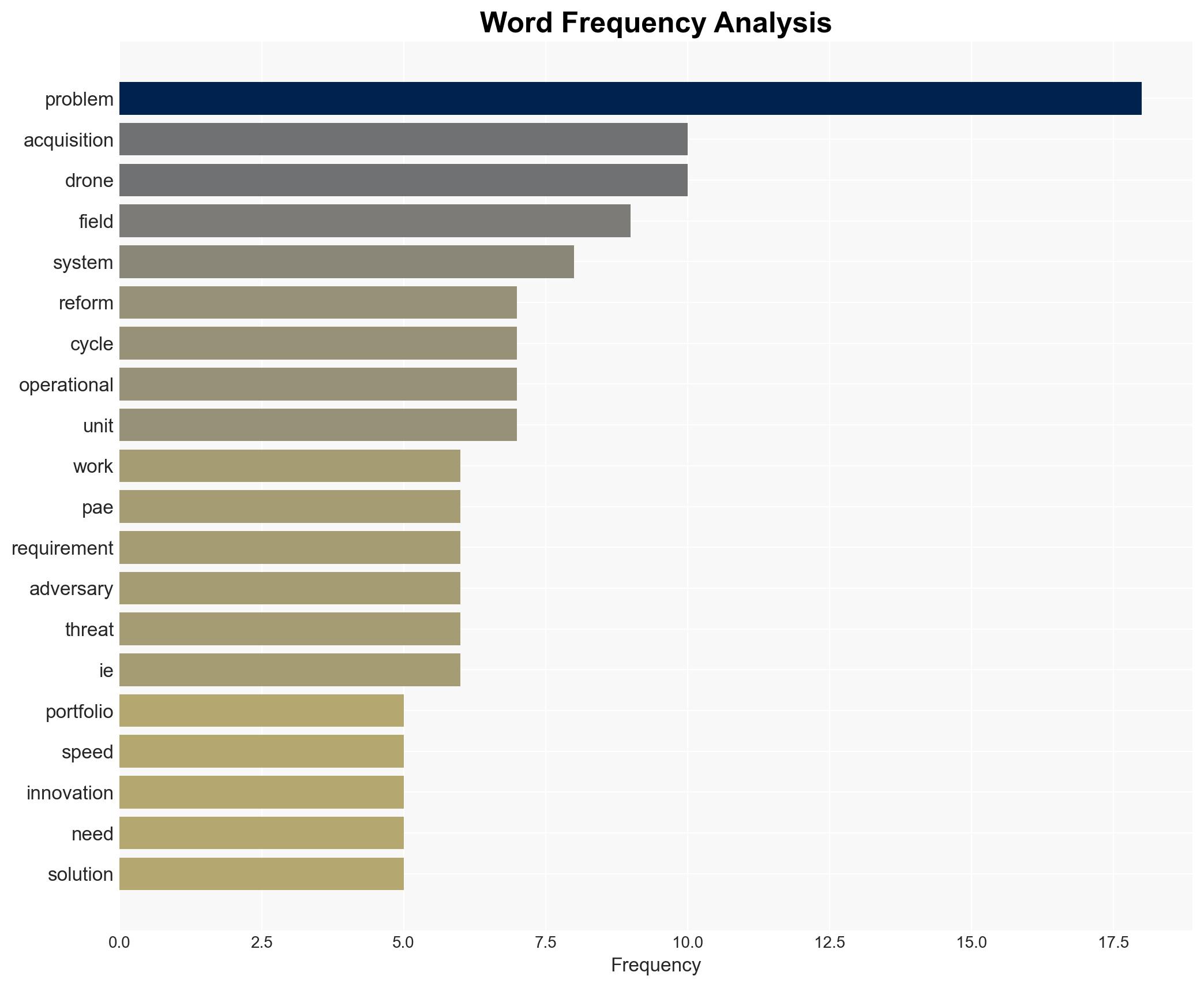
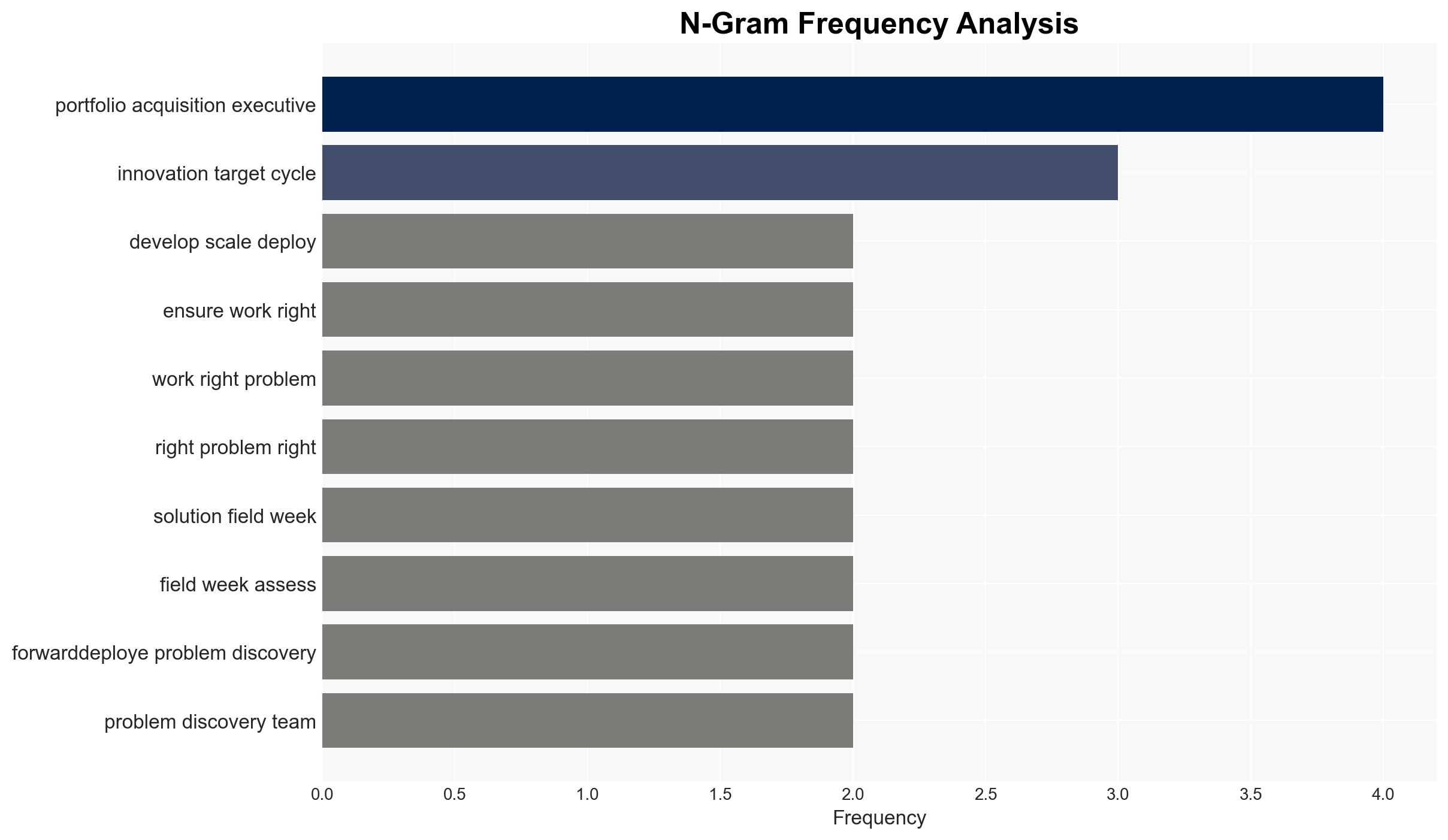
- Hypothesis A: The current reforms will effectively address modern warfare needs by implementing recommendations from the defense innovation community. Evidence includes the establishment of Portfolio Acquisition Executives and a focus on rapid delivery. However, uncertainties remain about the adaptability of these reforms to future threats.
- Hypothesis B: The reforms will fail to adequately address emerging threats due to a lack of forward-looking problem identification and a focus on existing solutions. This is supported by the absence of a rapid requirements process and forward-deployed problem discovery teams.
- Assessment: Hypothesis B is currently better supported due to the identified gaps in problem identification and adaptation processes. Indicators that could shift this judgment include the successful implementation of a rapid requirements process and evidence of effective problem discovery mechanisms.
3. Key Assumptions and Red Flags
- Assumptions: The Department of War’s reforms are based on accurate assessments of current and future threats; the defense innovation community’s recommendations are comprehensive and applicable; current acquisition processes are inadequate for modern warfare.
- Information Gaps: Specific details on how the new Warfighting Acquisition System will adapt to future threats; effectiveness data of current counter-UAS deployments; insights into adversaries’ adaptation strategies.
- Bias & Deception Risks: Potential bias in relying heavily on past recommendations without current threat analysis; risk of deception from adversaries adapting faster than anticipated.
4. Implications and Strategic Risks
The current trajectory of reforms may lead to a misalignment between defense capabilities and emerging threats, potentially undermining strategic objectives.
- Political / Geopolitical: Failure to address new threats could weaken alliances and embolden adversaries, altering geopolitical balances.
- Security / Counter-Terrorism: Inadequate counter-UAS capabilities may increase vulnerability to drone attacks, affecting operational security.
- Cyber / Information Space: Potential gaps in cyber defense if reforms do not integrate cyber threat considerations effectively.
- Economic / Social: Misallocation of resources could strain defense budgets and impact public perception of national security efficacy.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Establish forward-deployed problem discovery teams and initiate a rapid requirements process to address emerging threats.
- Medium-Term Posture (1–12 months): Develop partnerships with industry and allies to enhance adaptive capabilities and share threat intelligence.
- Scenario Outlook:
- Best: Successful adaptation of reforms leads to enhanced defense capabilities.
- Worst: Continued focus on outdated threats results in strategic vulnerabilities.
- Most-Likely: Partial adaptation with mixed results, requiring ongoing adjustments.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
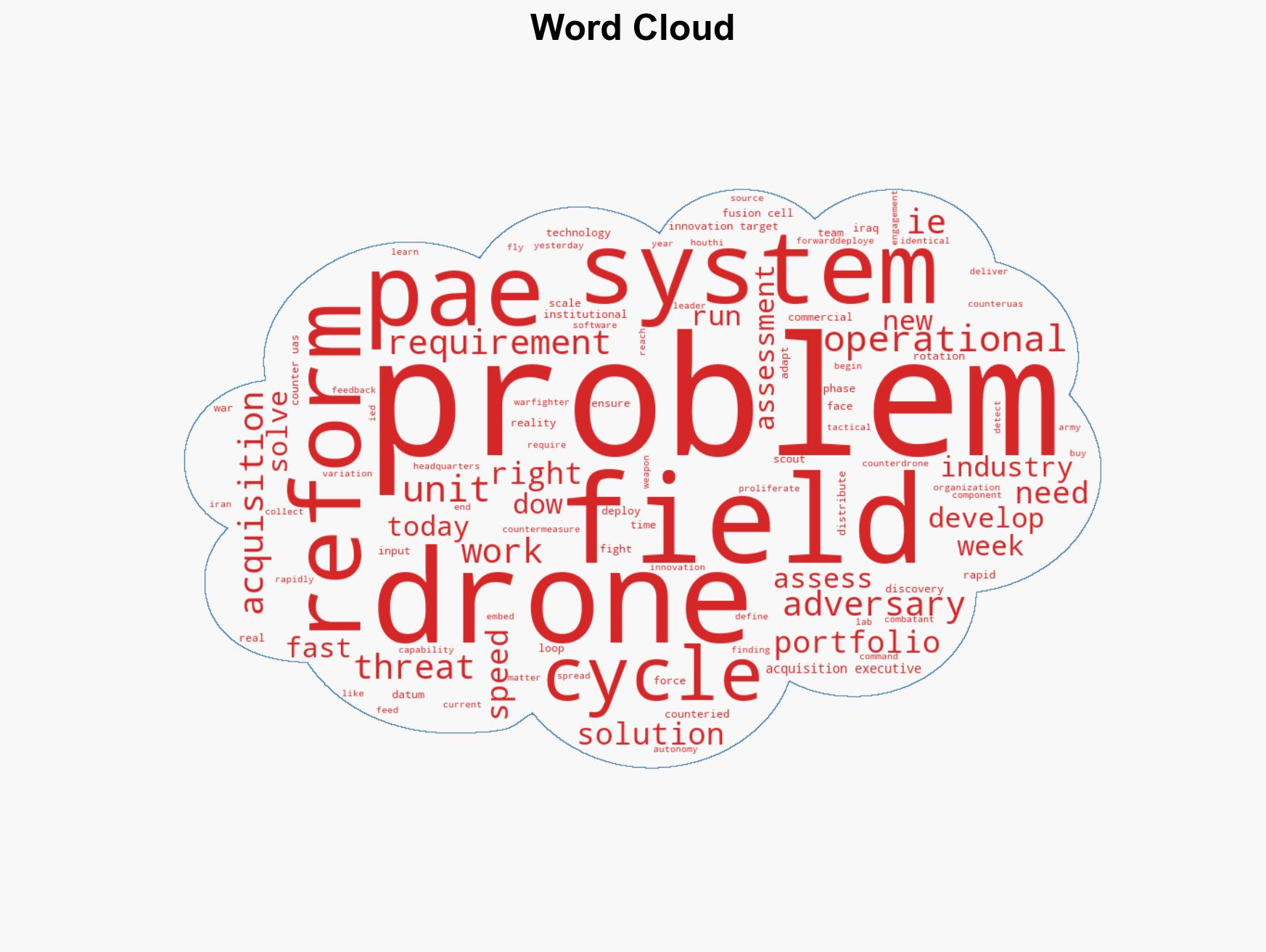
national security threats, defense acquisition, counter-UAS, military reform, innovation cycle, strategic risk, geopolitical dynamics, operational security
Structured Analytic Techniques Applied
- Cognitive Bias Stress Test: Expose and correct potential biases in assessments through red-teaming and structured challenge.
- Bayesian Scenario Modeling: Use probabilistic forecasting for conflict trajectories or escalation likelihood.
- Network Influence Mapping: Map influence relationships to assess actor impact.
- Cross-Impact Simulation: Simulate cascading interdependencies and system risks.
- Adversarial Threat Simulation: Model hostile behavior to identify vulnerabilities.
Explore more:
National Security Threats Briefs ·
Daily Summary ·
Support us