Reliance Global Group Completes Acquisition of Enquantum to Strengthen Post-Quantum Cybersecurity Strategy
Published on: 2026-02-23
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Reliance Global Group Closes Enquantum Transaction Launching Path to Majority Control of Post-Quantum Cybersecurity Platform
1. BLUF (Bottom Line Up Front)
Reliance Global Group’s acquisition of Enquantum Ltd. positions it to become a leader in post-quantum cybersecurity, addressing vulnerabilities in current encryption standards. This move is likely to influence global cybersecurity strategies, especially as quantum computing capabilities advance. Overall, there is moderate confidence in this assessment due to the evolving nature of quantum technologies and encryption standards.
2. Competing Hypotheses
- Hypothesis A: Reliance Global Group’s acquisition of Enquantum will successfully establish it as a leader in post-quantum cybersecurity, leveraging Enquantum’s technology to secure critical infrastructure. This is supported by Enquantum’s existing patents and alignment with NIST standards. However, uncertainties remain regarding the pace of quantum computing advancements and market adoption.
- Hypothesis B: The acquisition may not significantly impact the cybersecurity landscape due to potential delays in quantum computing advancements or challenges in integrating Enquantum’s technology into existing systems. Contradicting evidence includes the current nascent stage of quantum computing and potential competitive responses from other cybersecurity firms.
- Assessment: Hypothesis A is currently better supported due to Enquantum’s technical capabilities and strategic alignment with emerging standards. Key indicators that could shift this judgment include breakthroughs in quantum computing or significant competitive advancements in post-quantum cryptography.
3. Key Assumptions and Red Flags
- Assumptions: Quantum computing will advance to a level that threatens current encryption standards; Enquantum’s technology will be effectively integrated into Reliance’s operations; global standards will continue to evolve in favor of post-quantum solutions.
- Information Gaps: Specific timelines for quantum computing advancements; detailed integration plans for Enquantum’s technology; competitive landscape analysis.
- Bias & Deception Risks: Potential overestimation of quantum computing threat timelines; reliance on company-reported capabilities without independent verification; market hype influencing strategic decisions.
4. Implications and Strategic Risks
This development could accelerate the transition to post-quantum cryptography, influencing global cybersecurity strategies and infrastructure investments.
- Political / Geopolitical: Countries may prioritize post-quantum cybersecurity in national security agendas, potentially leading to international collaborations or rivalries.
- Security / Counter-Terrorism: Enhanced encryption could complicate intelligence and law enforcement operations, necessitating new decryption capabilities.
- Cyber / Information Space: Increased focus on developing quantum-resilient systems may spur innovation but also create new attack vectors during the transition period.
- Economic / Social: Significant investments in post-quantum technologies could drive economic growth in the tech sector but may also lead to disparities in cybersecurity capabilities between nations.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor advancements in quantum computing and post-quantum cryptography; engage with industry and government stakeholders to assess integration challenges.
- Medium-Term Posture (1–12 months): Develop partnerships with leading post-quantum technology firms; invest in workforce training for post-quantum cybersecurity skills.
- Scenario Outlook:
- Best: Rapid integration of post-quantum solutions secures critical infrastructure globally.
- Worst: Delays in technology development lead to vulnerabilities and increased cyber threats.
- Most-Likely: Gradual adoption of post-quantum technologies with ongoing adjustments to standards and practices.
6. Key Individuals and Entities
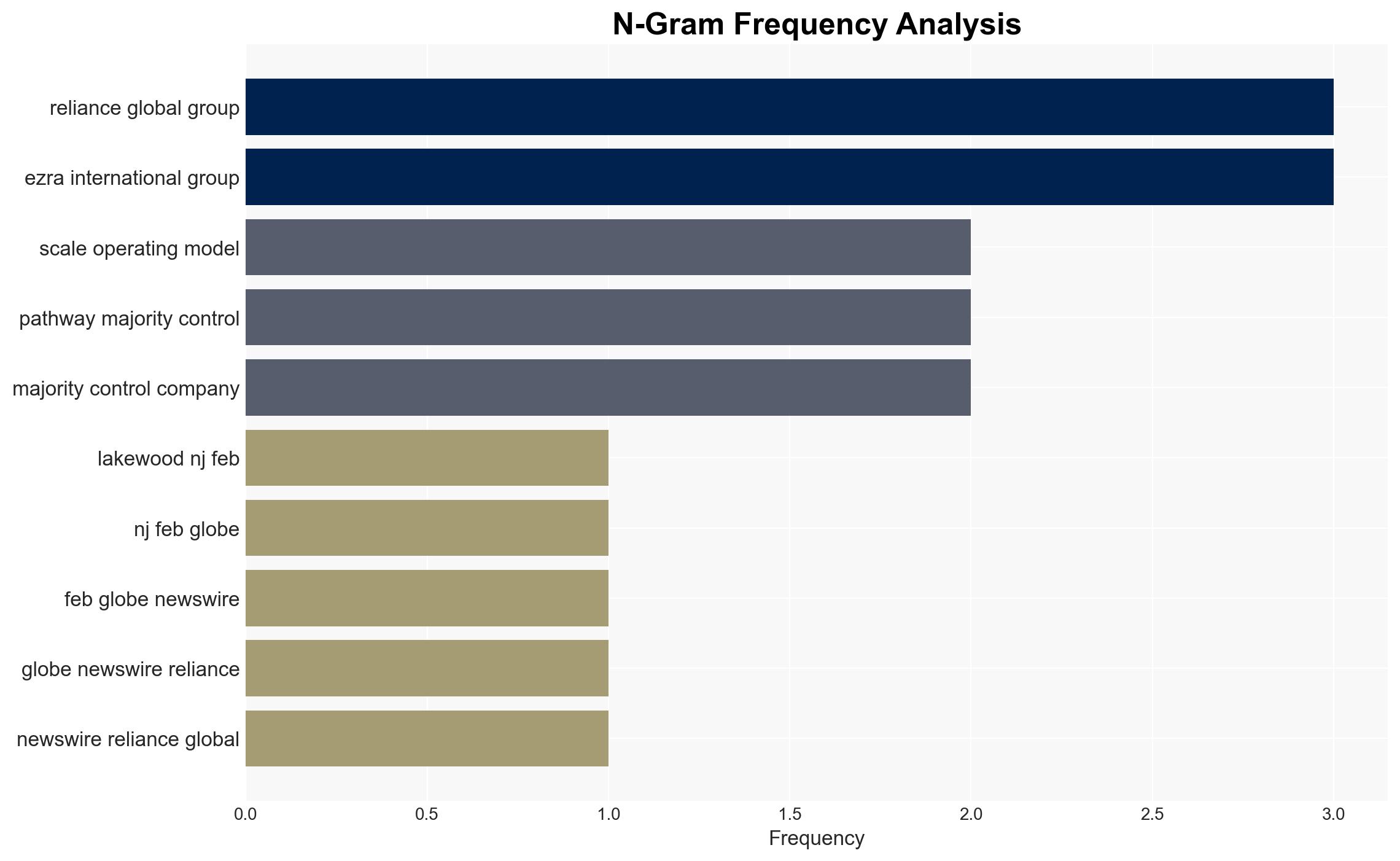
- Reliance Global Group
- Enquantum Ltd.
- U.S. National Institute of Standards and Technology (NIST)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, post-quantum cryptography, quantum computing, encryption standards, infrastructure security, technology acquisition, global cybersecurity strategy
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us