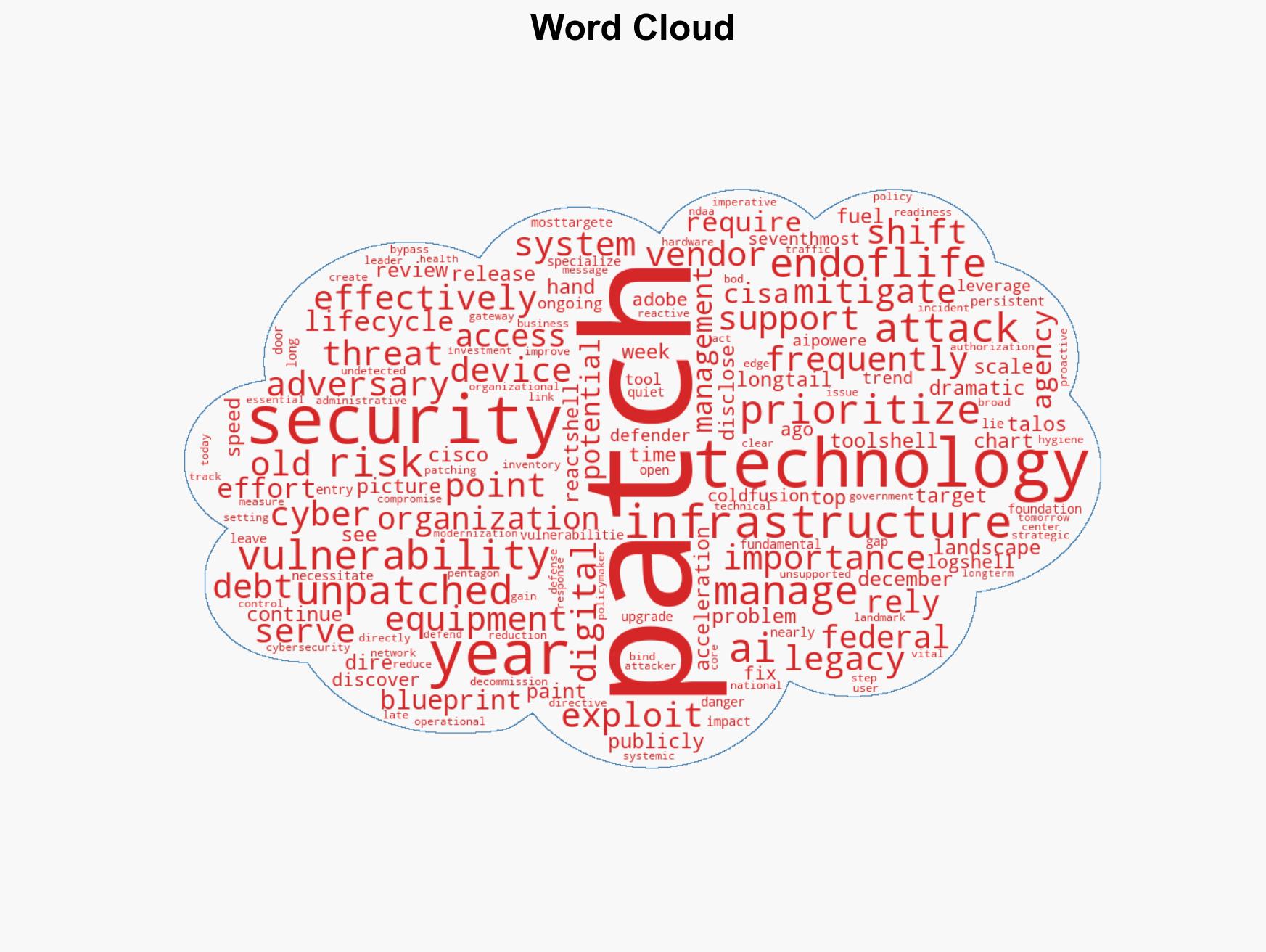
Revamping US Critical Infrastructure for AI: Enhancing Security Amid Rising Cyber Threats
Published on: 2026-03-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
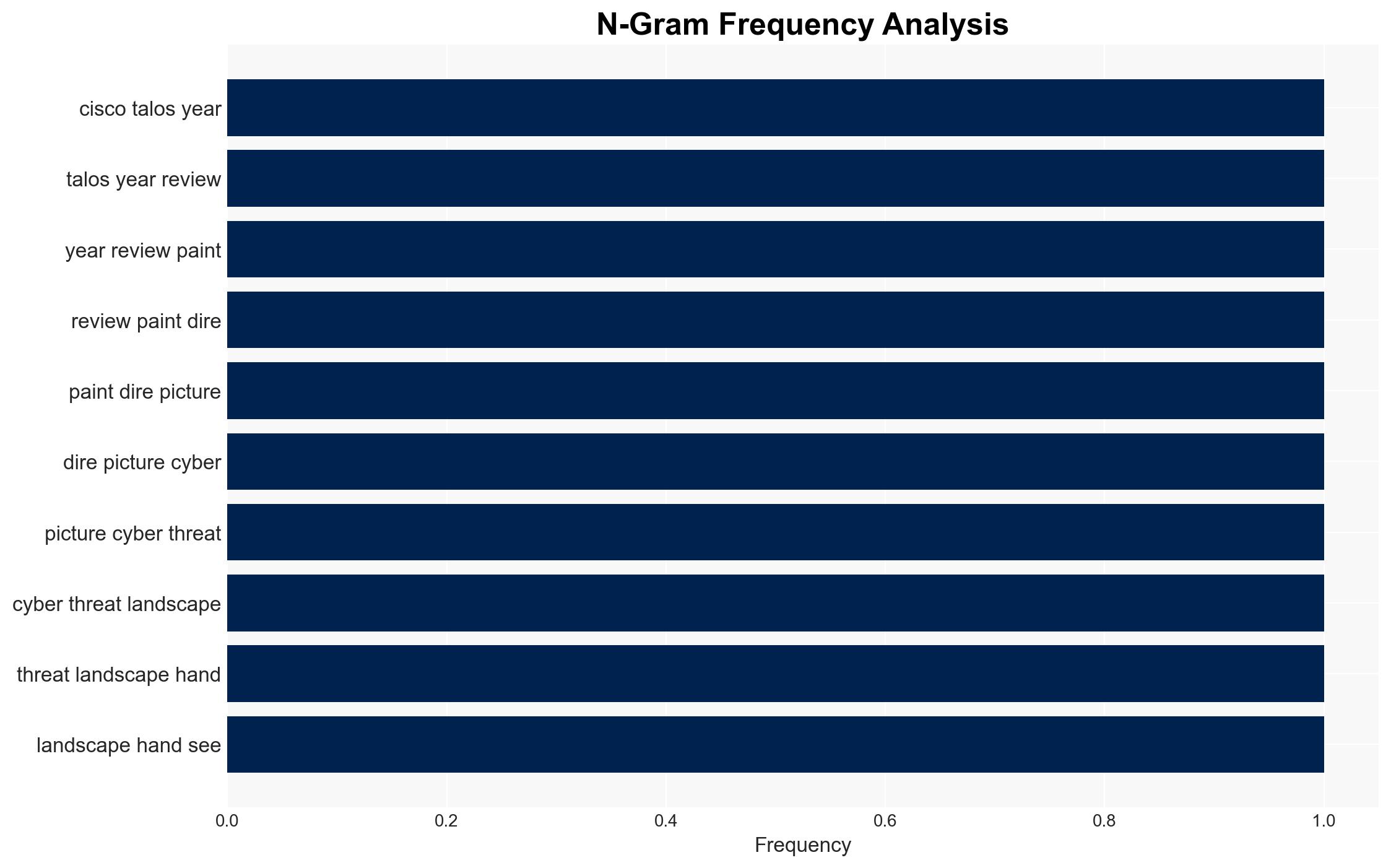
Intelligence Report: Modernizing US Critical Infrastructure for the AI Era Strengthening Security In an Evolving Threat Landscape
1. BLUF (Bottom Line Up Front)
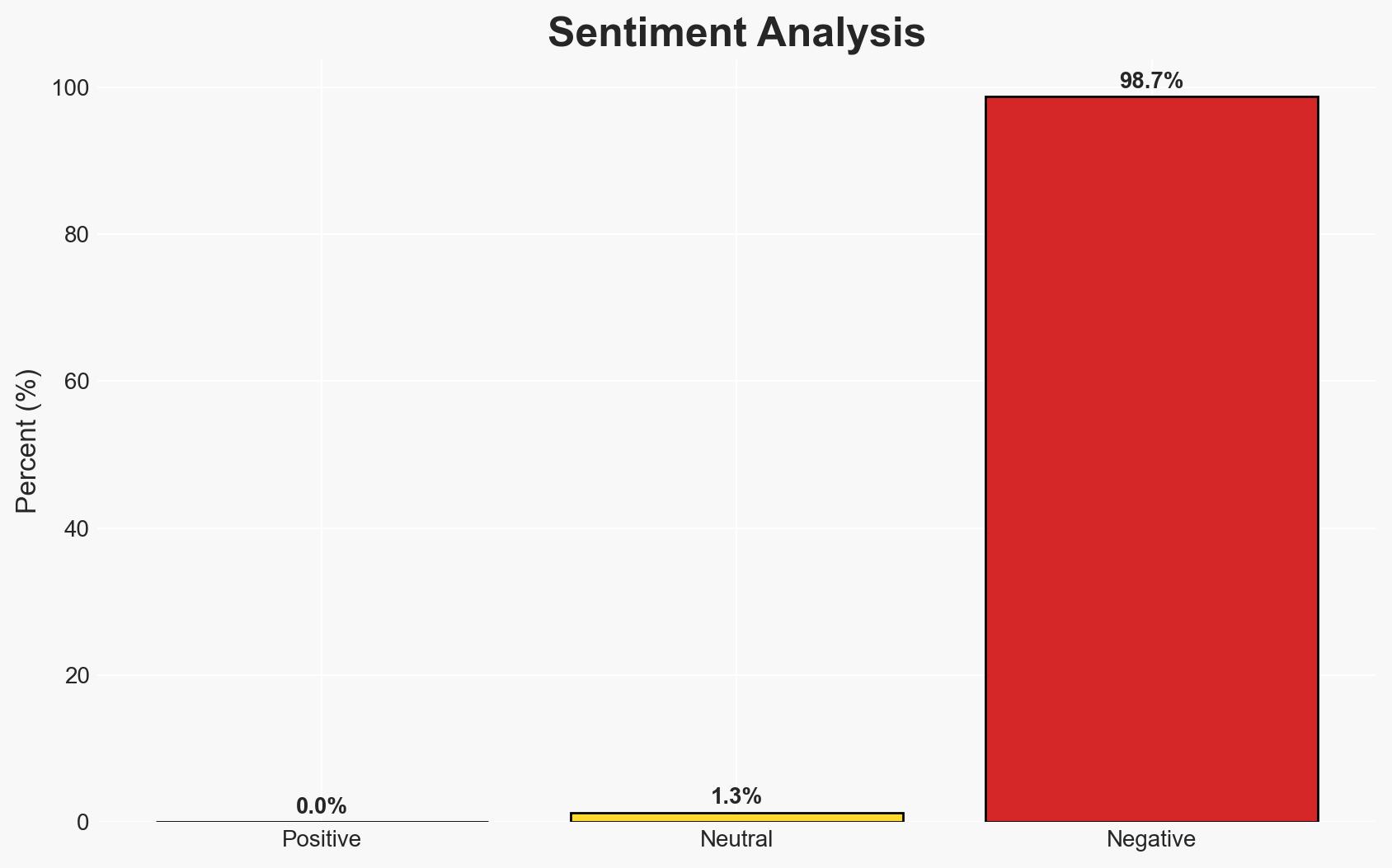
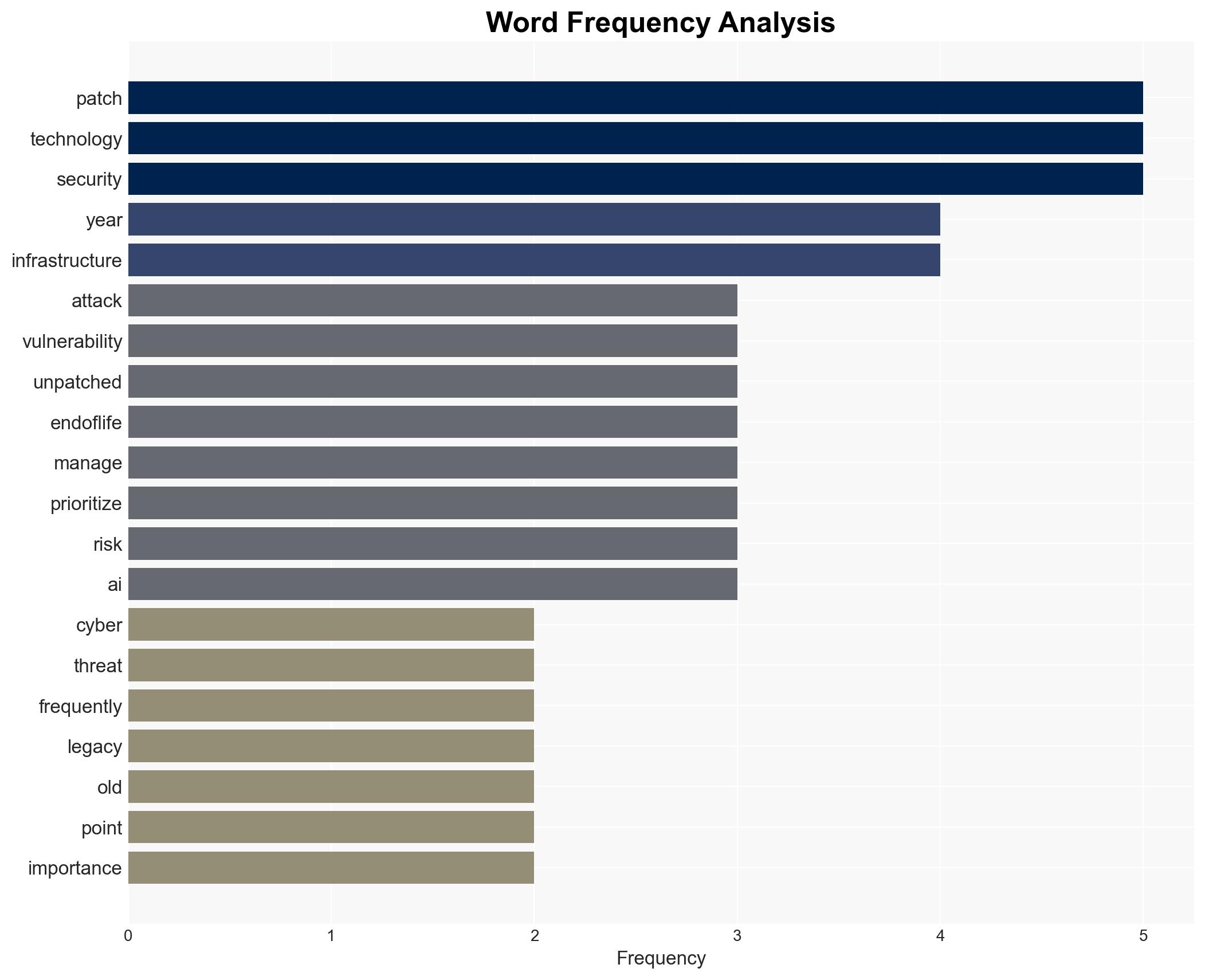
The current cyber threat landscape is characterized by an increase in both the speed and scale of attacks, with a significant focus on exploiting unpatched and end-of-life technologies. The most likely hypothesis is that modernization of infrastructure and lifecycle management will mitigate these risks, as evidenced by recent federal initiatives. This affects federal agencies and potentially all organizations reliant on outdated technology. Overall confidence in this judgment is moderate.
2. Competing Hypotheses
- Hypothesis A: Modernizing infrastructure and implementing lifecycle management will significantly reduce cyber risks. This is supported by federal initiatives like CISA’s BOD 26-02 and the NDAA’s focus on technical debt. However, uncertainties remain about the speed and effectiveness of these implementations across all sectors.
- Hypothesis B: Despite modernization efforts, adversaries will continue to exploit vulnerabilities due to the inherent lag in patching and decommissioning outdated systems. This is supported by the persistent targeting of long-known vulnerabilities like Log4shell and Adobe ColdFusion.
- Assessment: Hypothesis A is currently better supported due to proactive federal measures and policy shifts. Key indicators that could shift this judgment include the pace of technology upgrades and the emergence of new vulnerabilities.
3. Key Assumptions and Red Flags
- Assumptions: Organizations will comply with federal directives; AI tools will enhance vulnerability management; adversaries will continue to exploit known vulnerabilities.
- Information Gaps: Detailed timelines for infrastructure upgrades; specific organizational compliance levels; adversary capabilities and intentions.
- Bias & Deception Risks: Over-reliance on federal reports; potential underestimation of adversary adaptability; vendor bias in promoting new technologies.
4. Implications and Strategic Risks
The evolution of the cyber threat landscape necessitates a strategic shift towards proactive infrastructure management, with significant implications across multiple domains.
- Political / Geopolitical: Increased pressure on international partners to adopt similar modernization strategies.
- Security / Counter-Terrorism: Enhanced security posture may deter state and non-state actors, but could also lead to more sophisticated attack vectors.
- Cyber / Information Space: Potential for increased cyber resilience, but also a risk of adversaries developing new tactics to bypass enhanced defenses.
- Economic / Social: Short-term economic costs of modernization may be offset by long-term savings from reduced cyber incidents.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive inventory of current systems; prioritize patching of critical vulnerabilities; enhance monitoring of end-of-life technologies.
- Medium-Term Posture (1–12 months): Develop partnerships for technology sharing and threat intelligence; invest in AI-driven security solutions; establish a clear timeline for decommissioning obsolete systems.
- Scenario Outlook:
- Best: Rapid modernization leads to a significant reduction in cyber incidents.
- Worst: Slow implementation results in continued exploitation of vulnerabilities.
- Most-Likely: Gradual improvements in security posture with periodic setbacks due to emerging threats.
6. Key Individuals and Entities
- Cybersecurity and Infrastructure Security Agency (CISA)
- Department of Defense (DoD)
- Federal agencies subject to BOD 26-02
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, infrastructure modernization, AI readiness, federal policy, lifecycle management, vulnerability management, technical debt
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us