Rise in InstallFix Attacks: Users Misled by Counterfeit Claude Code Installation Pages
Published on: 2026-03-09
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Fake Claude Code install pages highlight rise of InstallFix attacks
1. BLUF (Bottom Line Up Front)
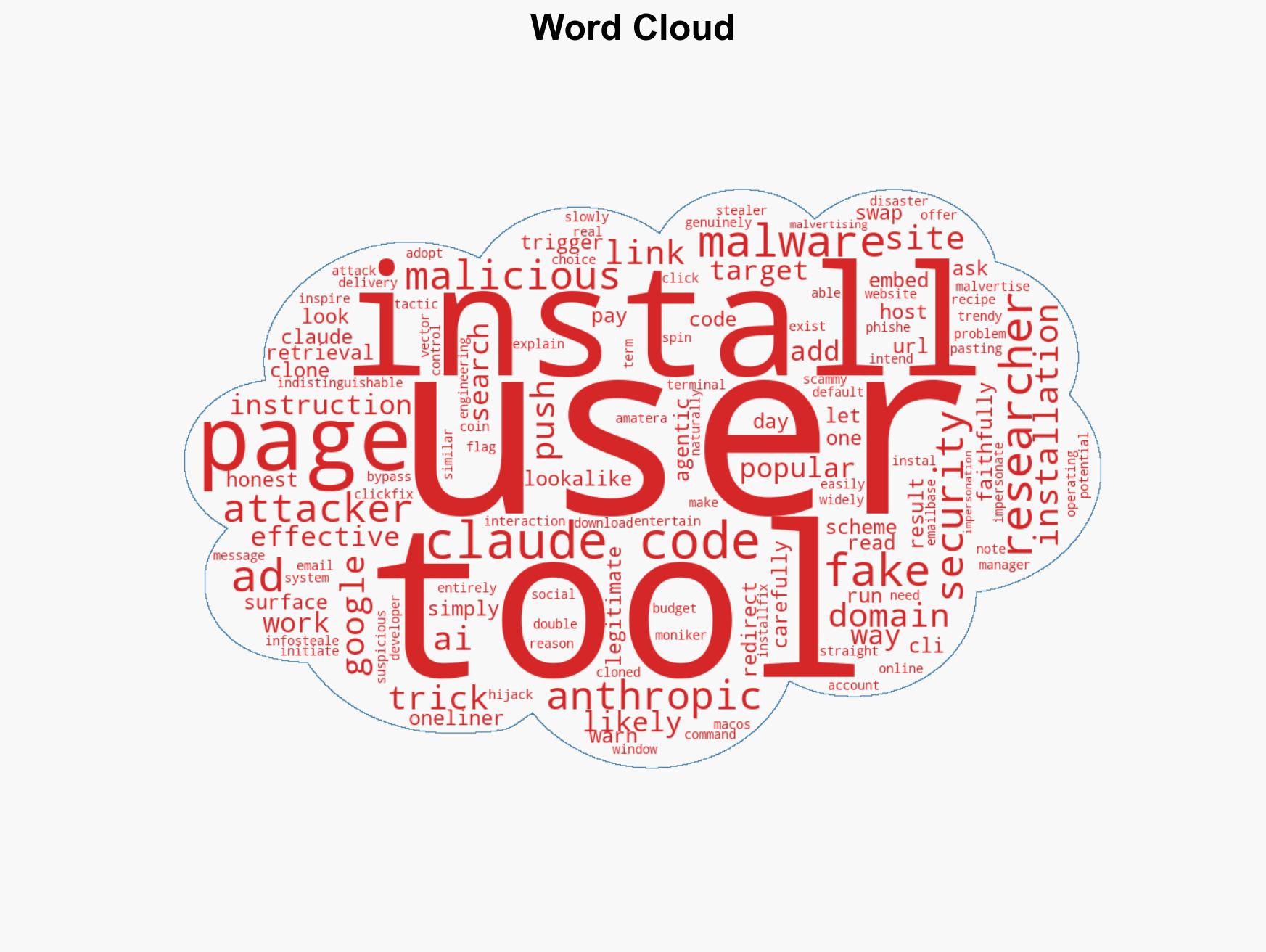
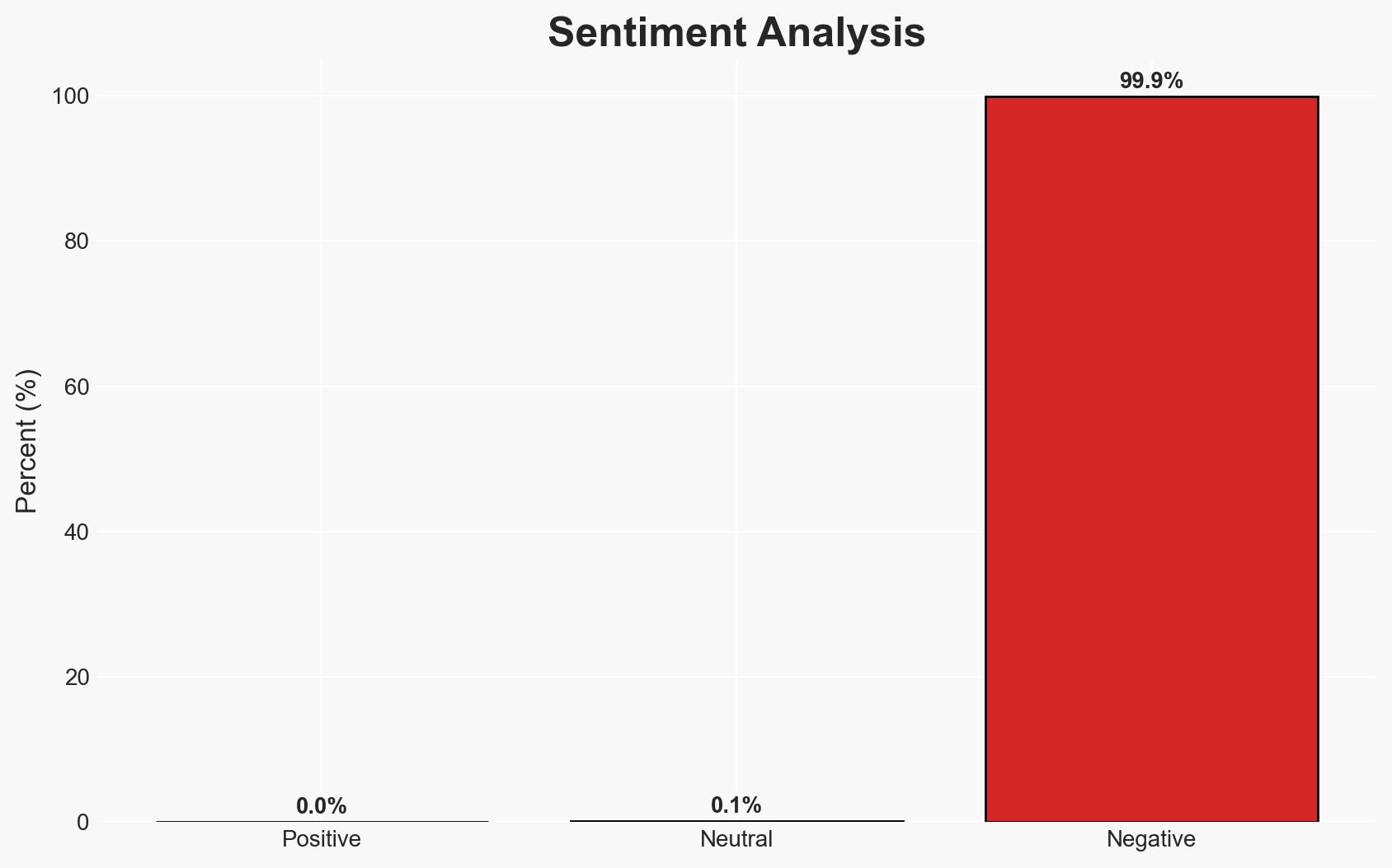
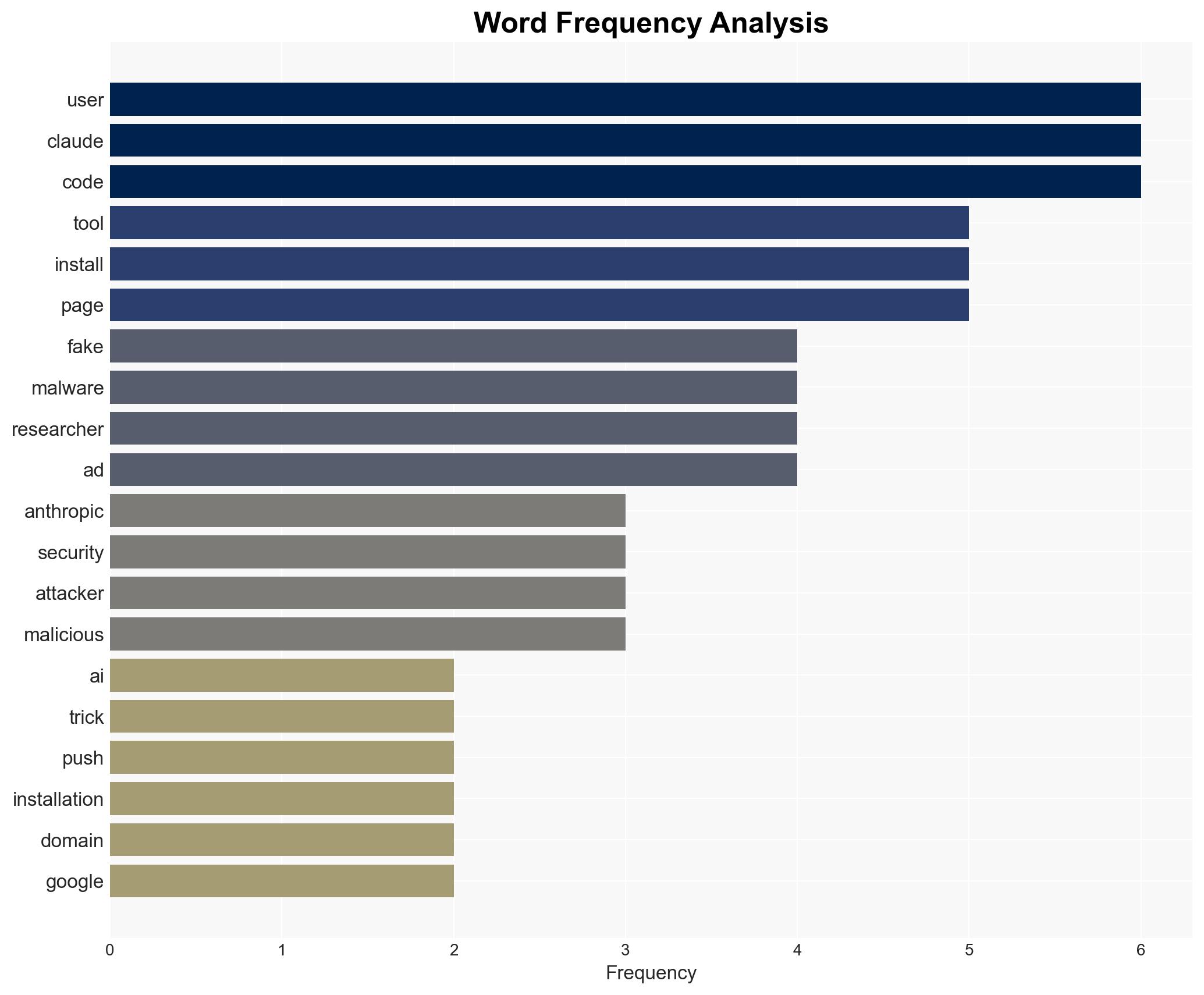
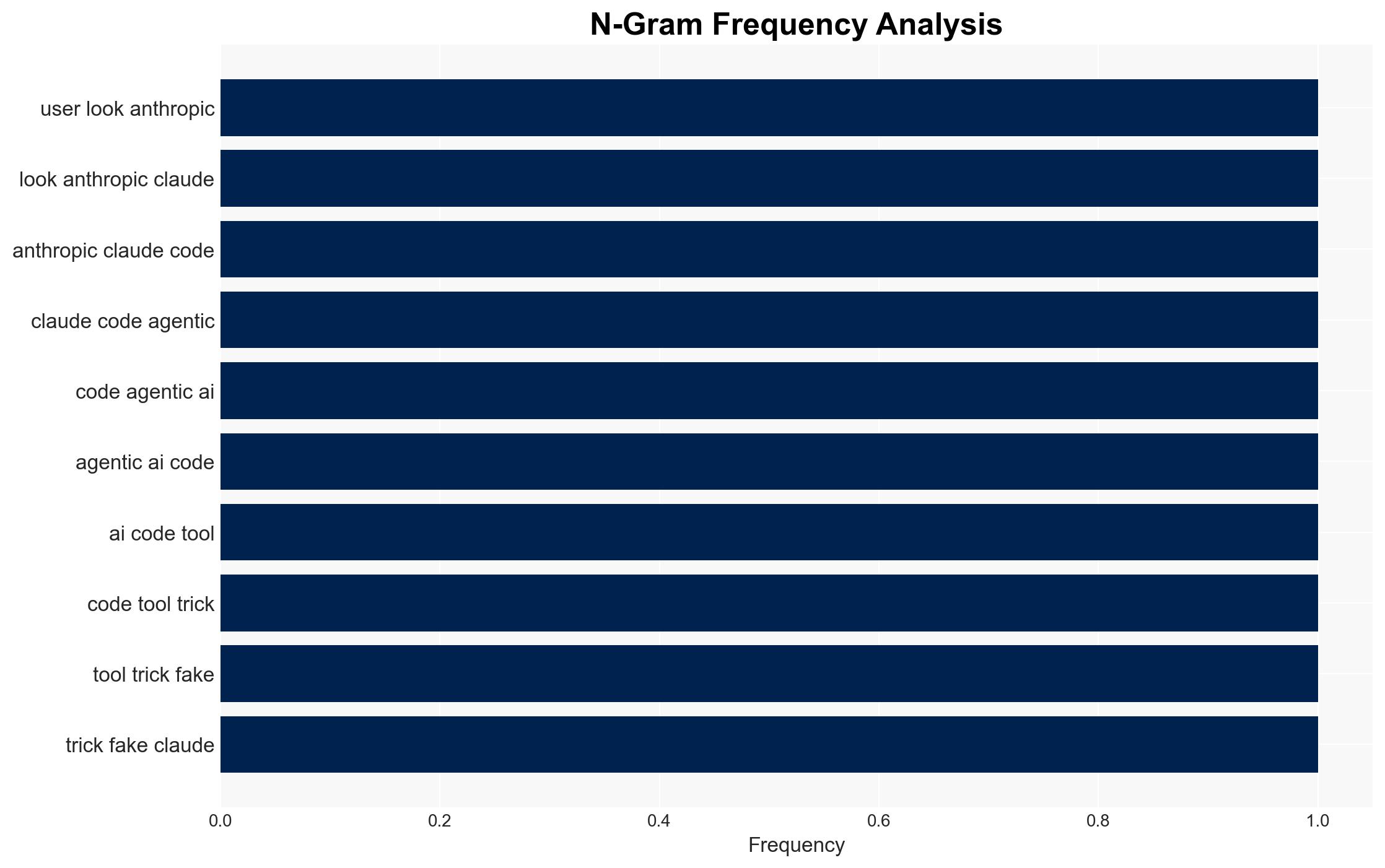
The emergence of fake Claude Code install pages exemplifies the increasing threat of “InstallFix” attacks, where attackers use malvertising to distribute malware. This affects users seeking AI tools, with moderate confidence that such tactics will proliferate due to their effectiveness and low detection rates. The primary targets are developers and tech-savvy users who rely on online searches for software installation guidance.
2. Competing Hypotheses
- Hypothesis A: The primary goal of the attackers is financial gain through the theft of sensitive information using malware like Amatera Stealer. This is supported by the use of info-stealing malware and the targeting of popular AI tools. However, the specific financial mechanisms (e.g., sale of data) remain unclear.
- Hypothesis B: The attackers aim to disrupt the operations of AI tool developers by undermining user trust and causing reputational damage. While plausible, there is less direct evidence of intent to harm the developers beyond opportunistic exploitation of their popularity.
- Assessment: Hypothesis A is currently better supported due to the direct financial incentives and the use of malware designed for data theft. Indicators such as increased targeting of other AI tools or shifts in malware type could alter this assessment.
3. Key Assumptions and Red Flags
- Assumptions: Attackers have the capability to clone websites effectively; Users do not scrutinize URLs closely; Malvertising will continue to bypass traditional security measures.
- Information Gaps: The identity and origin of the attackers; The full scope of the financial impact on victims; The potential for collaboration with other threat actors.
- Bias & Deception Risks: Confirmation bias in assuming all similar attacks have financial motives; Potential underestimation of the attackers’ strategic goals beyond immediate financial gain.
4. Implications and Strategic Risks
This development could lead to increased sophistication in malvertising tactics and broader targeting of AI and tech tools, potentially eroding trust in digital ecosystems.
- Political / Geopolitical: Potential for state actors to exploit similar tactics for espionage or disruption.
- Security / Counter-Terrorism: Increased risk of malware proliferation and exploitation of compromised systems for broader cyber operations.
- Cyber / Information Space: Heightened vulnerability of digital platforms to impersonation and malvertising, challenging cybersecurity frameworks.
- Economic / Social: Possible economic impact on AI tool developers due to reduced user trust and increased security costs.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of malvertising campaigns; Educate users on verifying URLs; Collaborate with ad platforms to identify and remove malicious ads.
- Medium-Term Posture (1–12 months): Develop partnerships with AI developers for shared threat intelligence; Invest in advanced detection technologies for malvertising.
- Scenario Outlook: Best: Decrease in malvertising through improved detection; Worst: Widespread adoption of InstallFix tactics across various sectors; Most-Likely: Continued targeting of popular tech tools with incremental improvements in attacker techniques.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, malvertising, AI tools, information theft, social engineering, malware distribution, digital trust
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us